
Endpoint security protecting laptops, tablets, and smartphones in a modern work environment
What Is Endpoint Antivirus?
Today's cybersecurity landscape moves at breakneck speed, often outpacing internal IT capabilities. The traditional model of installing standalone antivirus software on individual computers no longer matches how modern organizations operate. With employees working from coffee shops, accessing files from tablets, and connecting countless devices to corporate networks, security must extend everywhere data flows. Endpoint antivirus addresses this challenge by protecting every device that touches your network infrastructure.
Understanding Endpoint Antivirus Software
Endpoint antivirus delivers security protection to individual devices within a corporate network, defending against malware, ransomware, phishing attempts, and emerging cyber threats. The endpoint antivirus basics differ fundamentally from conventional antivirus because IT administrators control all security from one centralized dashboard rather than managing software installations separately on each machine.
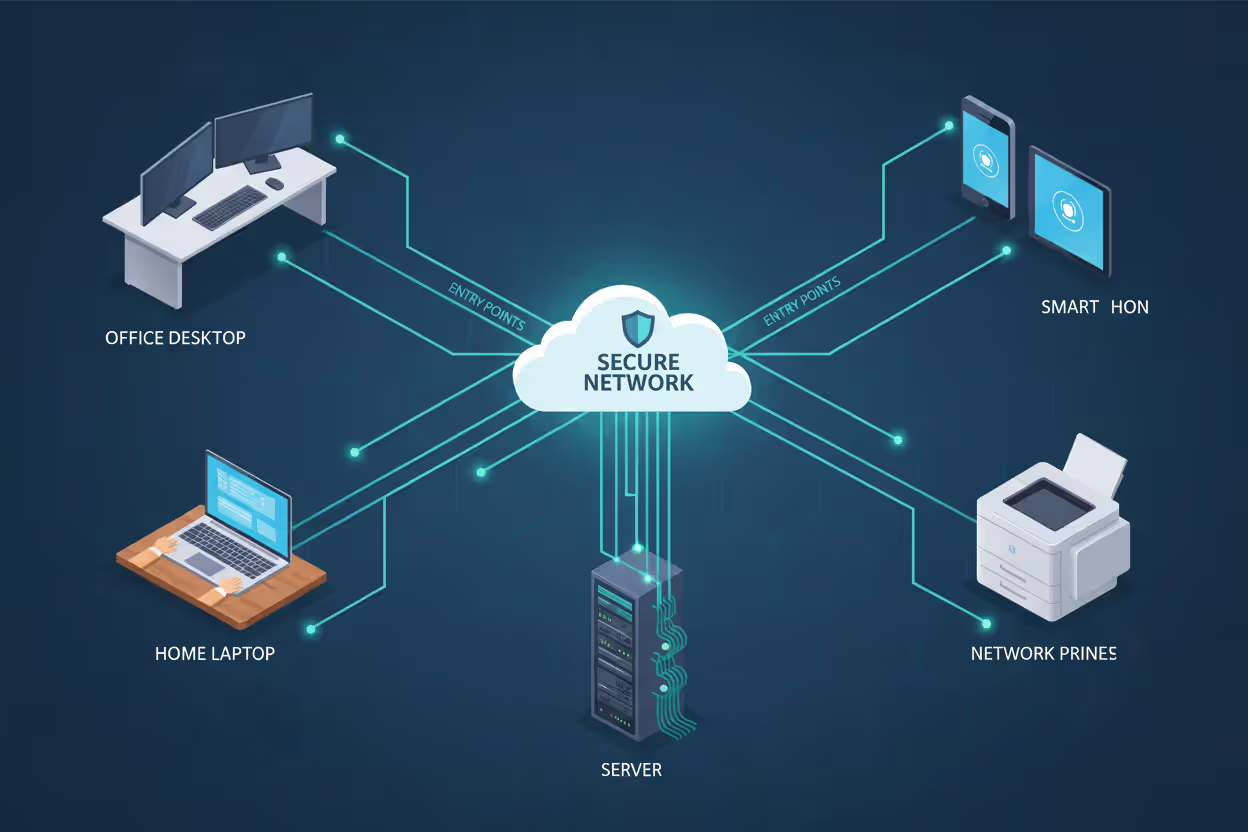
The term "endpoint" encompasses any hardware connecting to your network infrastructure: workstations at the office, employee laptops at home, mobile phones accessing corporate email, tablets used by field technicians, servers hosting applications, and even network-connected printers or retail terminals. These connection points create potential vulnerabilities where attackers probe for weaknesses. When someone clicks a malicious email link on their smartphone or plugs in a compromised thumb drive at their desk, endpoint antivirus identifies and stops threats before they can proliferate.
What separates this from traditional antivirus comes down to architectural design. Conventional antivirus functions independently on single devices, demanding manual intervention for updates and providing zero insight into security events happening elsewhere in your organization. Endpoint solutions work collectively as an integrated defense network. After detecting a new threat on one laptop, the central management system instantly distributes updated protection parameters to every other monitored device. This synchronized approach proves dramatically more effective against coordinated attacks that simultaneously probe multiple network entry points.
Author: Vanessa Keaton;
Source: williamalmonte.net
Endpoint antivirus platforms typically consist of three components: lightweight agent software running on each protected device, browser-accessible management dashboards for administrators, and cloud-connected threat intelligence systems that refresh continuously. The agent tracks file operations, network traffic, and system behaviors while administrators view consolidated security dashboards showing real-time protection status across their complete device inventory.
How Endpoint Antivirus Protects Your Network
Grasping how endpoint antivirus works means examining the multiple defensive techniques these platforms deploy simultaneously. Contemporary endpoint protection layers several detection approaches rather than depending on any single methodology.
Detection Methods Explained
When endpoint antivirus explained in technical detail, signature-based detection forms the fundamental layer. This approach maintains databases containing known malware "signatures"—distinctive code patterns or file attributes linked to specific threats. As files get accessed, the agent generates their signature and cross-references it against the database. Positive matches trigger immediate isolation or removal. This technique excels at blocking recognized threats but proves useless against brand-new exploits or morphing malware that alters its signature with every infection cycle.
Heuristic analysis studies file architecture and execution patterns to spot suspicious traits without requiring exact signature matches. The technology searches for code characteristics commonly found in malicious software: attempts at modifying critical system files, abnormal network communication sequences, or encryption algorithms typical of ransomware variants. Heuristics successfully catch mutations of existing threats and occasional novel malware, although they produce more incorrect threat identifications than pure signature matching.
Behavioral monitoring observes program actions after they start running. Instead of examining static files, this method tracks active processes for hostile operations: unauthorized attempts to access protected data, efforts to escalate system privileges, or communications with identified criminal command servers. A document appearing legitimate during initial scans gets flagged by behavioral monitoring when its embedded scripts try downloading additional malicious payloads.
Machine learning algorithms process millions of threat specimens to discover relationships human analysts might overlook. These computational models simultaneously evaluate hundreds of file characteristics—creation timestamps, structural composition, system calls, communication behaviors—calculating probability scores for malicious intent. Machine learning particularly excels at recognizing novel malware families and complex attacks designed to bypass conventional detection. Attackers respond by developing adversarial methods to deceive these models, creating continuous technological competition.
Sandboxing runs questionable files inside isolated virtual containers to monitor their behavior without endangering production systems. When a file demonstrates malicious activities within the sandbox—encrypting documents, harvesting credentials, or establishing persistent backdoors—the endpoint agent prevents it from executing on actual devices. This approach catches sophisticated threats but introduces delays since suspicious files must complete sandbox evaluation before users can access them.

Author: Vanessa Keaton;
Source: williamalmonte.net
Real-Time Monitoring and Response
Endpoint antivirus maintains constant vigilance rather than operating only during scheduled scanning windows. The agent inspects every file access attempt, program launch, and network connection as events occur. When someone downloads an email attachment, the agent intercepts and analyzes it before permitting the file to open. If an application initiates unexpected network communications, the agent determines whether this represents normal operation or signals compromise.
Response actions scale with threat severity. Minor detections might generate administrator notifications for manual review. Confirmed malware triggers automatic isolation, relocating infected files into quarantined storage where they cannot execute or propagate. Critical threats can launch automated defensive sequences: severing the device's network connection, killing malicious processes, reversing unauthorized system modifications, and alerting security personnel through integrated security information and event management platforms.
Centralized oversight enables coordinated responses spanning all endpoints. Upon detecting ransomware on one computer, administrators can instantly scan the entire device fleet for compromise indicators, block the malware's network signatures organization-wide, and deploy emergency patches closing exploited vulnerabilities—executing all actions from the management console without accessing individual machines.
Common Endpoint Antivirus Solutions
Endpoint antivirus examples available in 2026 span comprehensive enterprise systems to specialized solutions targeting particular industries or implementation scenarios.
CrowdStrike Falcon runs completely cloud-based with minimal agent footprints that barely impact system resources. Its threat intelligence network processes billions of security events daily, leveraging this information to protect all subscribers simultaneously. Falcon prioritizes behavioral detection and proactive threat hunting, making it favored by organizations confronting advanced persistent threats. The platform incorporates endpoint detection and response (EDR) features extending well beyond basic antivirus functions.
Microsoft Defender for Endpoint delivers seamless integration within Windows ecosystems while extending coverage to macOS, Linux, iOS, and Android platforms. Companies already utilizing Microsoft 365 gain unified security administration across email systems, identity management, and endpoint devices. Defender taps into Microsoft's vast threat intelligence operations and provides exceptional protection against Windows-targeted attacks. The solution fits mid-market companies wanting consolidated security oversight.
Symantec Endpoint Protection (now under Broadcom ownership) merges traditional signature scanning with machine learning and behavioral evaluation. Its established platform delivers extensive customization options and granular policy management. Organizations facing complex regulatory compliance often select Symantec for its thorough logging and audit reporting features. The solution manages large-scale deployments efficiently but demands more administrator expertise than cloud-native competitors.
McAfee Endpoint Security offers modular protection where businesses choose specific components—antivirus, firewall, web filtering, data loss prevention—matching their particular requirements. This adaptability suits enterprises with diverse security needs across different business units. McAfee's ePO management platform consolidates oversight across multiple security technologies beyond endpoint antivirus alone.
Trend Micro Apex One highlights automated threat responses and coordination with network security infrastructure. Its XGen detection system combines multiple methodologies to optimize security without sacrificing performance. Apex One performs well in heterogeneous environments running mixed operating systems and incorporates specialized server and virtual environment protection.
SentinelOne Singularity employs AI-powered autonomous responses to isolate threats without human intervention. Upon detecting ransomware, the platform automatically restores encrypted files, terminates malicious processes, and disconnects affected devices—frequently within seconds of initial detection. This response speed makes SentinelOne attractive to organizations operating without extensive security teams.
Smaller organizations might evaluate Bitdefender GravityZone or Kaspersky Endpoint Security, delivering solid protection at accessible pricing with streamlined management designed for generalist administrators.
Endpoint Antivirus vs Traditional Antivirus
| Feature | Traditional Antivirus | Endpoint Antivirus |
| Coverage scope | Individual device protection operating independently | Coordinated network-wide defense spanning all connected hardware |
| Management method | Manual configuration required on every machine | Centralized dashboard controlling all endpoints remotely |
| Threat detection | Mainly signature matching with limited heuristics | Layered approach: signatures, behavioral analysis, machine learning, sandboxing |
| Update frequency | Manual or scheduled periodic updates | Continuous cloud-driven updates in real-time |
| Remote device support | Minimal or no protection for off-network hardware | Complete coverage for remote workers and mobile devices |
| Cost structure | Per-device licensing with lower individual costs | Per-device subscriptions including management infrastructure |
The management distinction becomes mission-critical as organizations expand. Using traditional antivirus, IT staff must physically access or remotely connect to individual computers for policy updates, log reviews, or threat responses. This methodology collapses beyond several dozen devices. Endpoint antivirus scales seamlessly to thousands of devices because all administration flows through the central console.
Traditional antivirus typically concentrates on malware prevention and cleanup. Endpoint platforms incorporate additional capabilities including application whitelisting (permitting only approved software), device restrictions (blocking unauthorized USB storage), content filtering, and firewall administration. These supplementary controls shrink your attack surface beyond merely detecting malware.
Understanding true expenses requires looking at complete ownership economics. Traditional antivirus costs $30-60 annually per device with negligible infrastructure requirements. Endpoint antivirus runs $40-150 per device depending on capabilities, plus management server expenses if not cloud-hosted. However, endpoint solutions dramatically reduce administrative overhead—one administrator can oversee 5,000 endpoints versus perhaps 500 with traditional antivirus—frequently making them more economical for organizations exceeding 25-30 devices.
When Your Organization Needs Endpoint Protection
Extremely small businesses operating fewer than ten computers running simple applications might function adequately with traditional antivirus, assuming they maintain rigorous update discipline and employ no remote workers. This scenario becomes increasingly uncommon.
Endpoint antivirus becomes necessary when these circumstances exist:
Remote or hybrid workforce models: Staff connecting from residential networks, public venues, or travel accommodations require identical protection as office-based colleagues. Endpoint antivirus projects corporate security policies to devices wherever they operate. The centralized administration ensures remote laptops receive updates and policy modifications instantly without requiring VPN connections or user actions.
Distributed office locations: Businesses with satellite offices encounter identical management obstacles as remote work arrangements. Endpoint antivirus eliminates requirements to station IT personnel at every location or depend on non-technical employees maintaining security.
Regulatory compliance mandates: HIPAA, PCI-DSS, GDPR, and comparable regulations frequently require specific security implementations including centralized security oversight, comprehensive audit trails, and rapid incident containment. Endpoint antivirus platforms deliver the documentation and enforcement mechanisms compliance auditors demand. Traditional antivirus rarely satisfies these standards because it lacks unified reporting and policy application.
Sensitive data processing: Financial records, customer databases, proprietary research, and regulated information demand protection exceeding endpoint antivirus basics. The sophisticated detection techniques and automated containment features in endpoint platforms substantially minimize breach probability.
Beyond 20-25 devices: Administrative burden managing traditional antivirus becomes prohibitive around this threshold. One IT generalist can effectively administer endpoint security for 100-200 devices using modern platforms, while managing traditional antivirus across equivalent fleets would consume multiple full-time positions.
Prior security breaches: Organizations having suffered ransomware, data theft, or other compromises should deploy endpoint protection during remediation. The behavioral monitoring and automated containment features help prevent recurring incidents.
Bring-your-own-device programs: Permitting personal smartphones or tablets to access corporate communications and documents demands endpoint protection functioning across operating systems while respecting user privacy alongside securing business data.
Organizations frequently make the mistake of postponing endpoint protection until after experiencing incidents. The typical ransomware attack costs small businesses $100,000-500,000 in operational disruption, recovery expenses, and lost revenue—vastly exceeding multiple years of endpoint antivirus subscriptions. Proactive implementation costs a fraction of incident remediation.

Author: Vanessa Keaton;
Source: williamalmonte.net
Choosing the Right Endpoint Antivirus Solution
Assessing endpoint antivirus platforms means weighing security performance, operational effects, and complete ownership costs.
Detection performance: Obtain independent testing data from AV-TEST or AV-Comparatives documenting detection percentages against known and zero-day threats. Monitor false positive frequencies—overly aggressive detection blocking legitimate applications creates workflow disruptions. Most vendors provide proof-of-concept trials where you can validate detection against your particular environment and business processes.
System performance: Endpoint agents utilize CPU cycles, memory, and storage capacity. Lightweight cloud-connected agents typically affect performance less than traditional on-premise solutions maintaining extensive local signature libraries. Validate solutions on representative hardware, especially older equipment and resource-limited systems like point-of-sale terminals. Workers will bypass security that visibly degrades their productivity.
Administrative simplicity: Assess the management interface for intuitive design and workflow efficiency. Can you remotely deploy agents to new hardware? How quickly can you build and distribute new policies? Does the dashboard surface actionable insights or overwhelming data volumes? Organizations lacking specialized security personnel should emphasize solutions with simplified interfaces and autonomous response features.
Platform coverage: Confirm the solution protects all device types in your infrastructure: Windows, macOS, Linux, iOS, Android, and specialized systems. Some vendors bill separately for mobile protection or deliver reduced functionality on non-Windows platforms.
Integration options: Endpoint antivirus should connect with your current security tools. Verify compatibility with SIEM platforms, help desk ticketing, network access controls, and identity systems. Application programming interfaces support customized connections and workflow automation.
Growth capacity: Select platforms accommodating expansion without architectural redesigns. Cloud-managed solutions scale more readily than on-premise management servers requiring capacity planning and hardware additions.
Vendor reliability and assistance: Endpoint security demands continuous updates and occasional emergency support. Research vendor financial health, update cadence, and support responsiveness. Investigate how rapidly vendors deployed protections for recent major threats.
Implementation choices: Cloud-managed solutions minimize infrastructure requirements and simplify administration but depend on internet availability. On-premise management servers provide greater control and function in air-gapped environments but increase administrative complexity. Hybrid designs balance these considerations.
Pricing models: Analyze complete expenses including subscriptions, management infrastructure, staff training, and ongoing administration. Some vendors charge separately for premium capabilities like EDR, sandboxing, or mobile support. Clarify what base pricing includes versus advanced tiers.
A sensible evaluation approach: identify three solutions meeting your requirements, then conduct proof-of-concept trials with 20-50 devices representing your environment's diversity. Measure detection success, performance effects, and administrative workflows before committing to organization-wide rollout.
Thinking of endpoint protection as simply 'improved antivirus' means missing its strategic significance. Contemporary endpoint platforms deliver visibility into device patterns, user behaviors, and threat trends that shape broader security planning. The real question isn't whether endpoint protection fits your budget—it's whether you can accept the operational blind spots that exist without it
— Sarah Chen
Frequently Asked Questions About Endpoint Antivirus
Endpoint antivirus marks the progression of malware defense from isolated device protection to synchronized network-wide security. The centralized oversight, sophisticated detection techniques, and automated containment capabilities address threat environments where attacks simultaneously target multiple devices and exploit your security chain's weakest point.
Choosing appropriate solutions demands understanding your particular needs: device quantities and types, remote work arrangements, compliance responsibilities, and available IT capabilities. Organizations operating dedicated security teams benefit from comprehensive platforms delivering EDR functions and advanced threat hunting. Smaller businesses should emphasize solutions with streamlined management and robust automated responses compensating for limited security specialization.
Migrating from traditional to endpoint antivirus involves more than software procurement. Successful deployment requires planning rollout processes, training administrators on management consoles, establishing alert response procedures, and educating users about their security responsibilities. Begin with pilot implementations on representative devices, confirm detection effectiveness and performance characteristics, then expand methodically across your device population.
Cyber threats will continue advancing, but endpoint antivirus delivers the visibility and authority necessary to protect your network's most vulnerable locations—the devices where people interact with information and attackers pursue access. The expense of comprehensive endpoint protection remains substantially below recovering from successful attacks that proper protection would have stopped.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.




