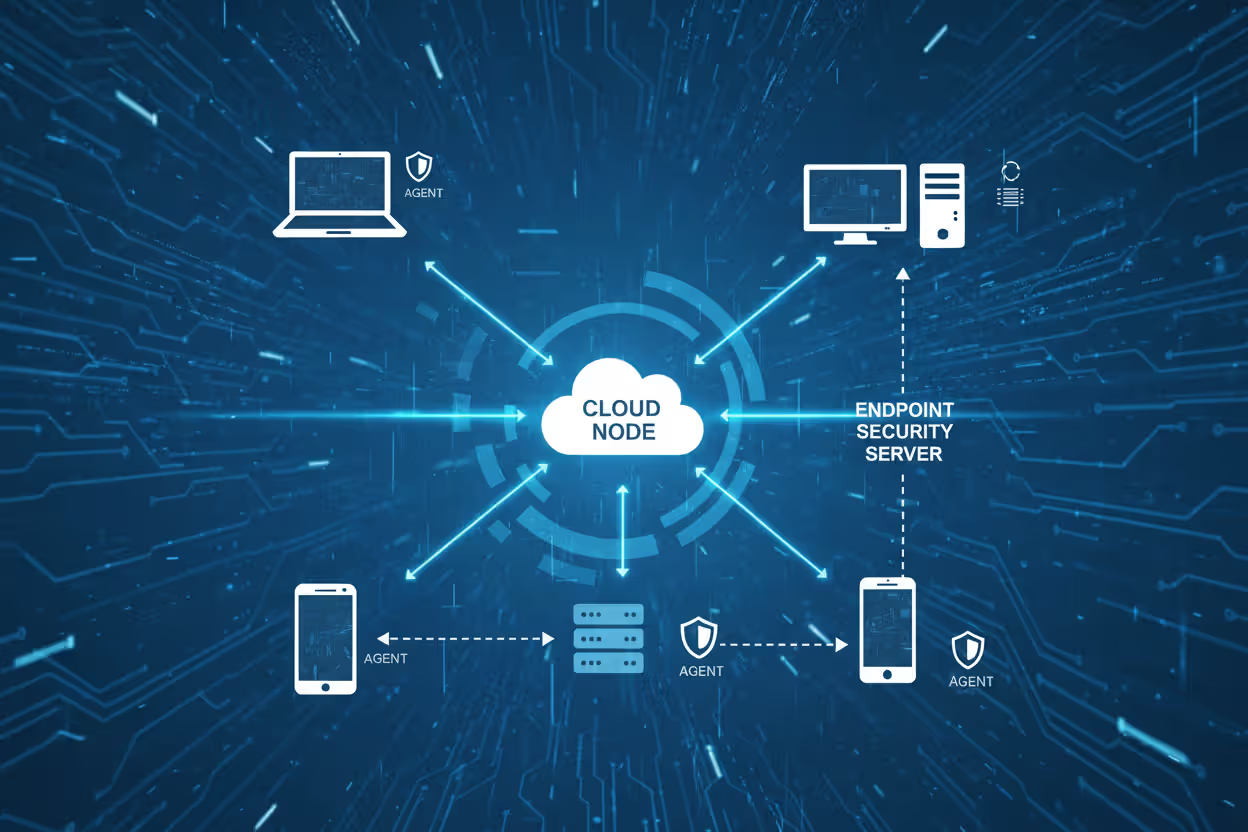
Endpoint security server monitoring multiple corporate devices
What Is an Endpoint Security Server?
Every laptop, smartphone, and workstation connected to your corporate network represents a potential entry point for attackers. An endpoint security server acts as the central command center that monitors, manages, and protects these devices from threats ranging from ransomware to credential theft.
Unlike standalone antivirus software that operates independently on each device, an endpoint security server coordinates protection across your entire infrastructure. It pushes security policies, collects threat data, and orchestrates responses from a single administrative interface—giving security teams visibility and control they can't achieve with disconnected tools.
Understanding Endpoint Security Servers
An endpoint security server is a centralized management platform that deploys, monitors, and controls security software across all endpoints in an organization's network. These endpoints include desktop computers, laptops, mobile devices, servers, and increasingly, Internet of Things (IoT) devices.
The architecture differs fundamentally from traditional antivirus solutions. Where conventional antivirus operates in isolation on individual machines with occasional signature updates, an endpoint security server maintains constant communication with lightweight agents installed on each device. This persistent connection enables real-time policy enforcement, immediate threat intelligence sharing, and coordinated incident response.
The server component typically runs on dedicated hardware or virtual machines within your data center, though cloud-hosted variants have gained significant traction. It houses the management console, threat detection engines, policy databases, and analytics platforms. Endpoint agents—small software programs installed on protected devices—execute security policies locally while reporting telemetry back to the server.
Author: Marcus Halbrook;
Source: williamalmonte.net
This centralized model solves practical problems that plague decentralized approaches. When a new malware variant emerges, the server can push updated detection signatures to thousands of endpoints within minutes rather than waiting for individual devices to check for updates. If an attack compromises one workstation, the server can immediately isolate that device from the network while scanning related endpoints for similar indicators of compromise.
The distinction from endpoint detection and response (EDR) tools matters here. While EDR focuses specifically on detecting and investigating threats that bypass preventive controls, a full endpoint security server encompasses prevention, detection, response, and policy management in a unified platform. Many modern solutions blur this line by incorporating EDR capabilities alongside traditional endpoint protection.
How Endpoint Security Servers Protect Your Network
The protection workflow begins with agent deployment. Administrators use the management console to push endpoint agents to devices across the network, either through automated discovery and installation or by integrating with existing deployment tools like Microsoft SCCM or mobile device management platforms. Once installed, agents establish encrypted communication channels with the server.
Centralized monitoring starts immediately. Agents continuously collect data about running processes, file system changes, network connections, user activities, and system configurations. This telemetry streams back to the server where it feeds into multiple analysis engines. The volume of data can be substantial—a typical enterprise endpoint might generate several megabytes of security telemetry daily.
Threat detection operates on multiple layers. Signature-based scanning catches known malware by comparing file hashes and code patterns against threat databases. Behavioral analysis identifies suspicious activities like unexpected registry modifications, unusual network traffic patterns, or attempts to disable security controls. Machine learning models trained on millions of malware samples flag anomalies that don't match known attack signatures but exhibit characteristics consistent with malicious behavior.
Policy enforcement happens both proactively and reactively. The server maintains security policies defining acceptable software, required configurations, permitted network connections, and access controls. Agents continuously enforce these policies—blocking unauthorized applications, encrypting sensitive data, restricting USB device usage, or preventing connections to known malicious domains. When policies change, the server pushes updates instantly across all managed endpoints.
Automated response capabilities distinguish modern endpoint security servers from passive monitoring tools. When the detection engine identifies a threat, the server can trigger predefined response workflows without human intervention. Common automated actions include isolating infected devices from the network, terminating malicious processes, quarantining suspicious files, rolling back unauthorized system changes, and alerting security personnel through integrated ticketing systems.
Consider a ransomware scenario: An employee opens a malicious email attachment. The endpoint agent detects abnormal file encryption activity and reports it to the server. Within seconds, the server cross-references this activity against threat intelligence feeds, confirms ransomware behavior, isolates the affected workstation from network shares, terminates the encryption process, and alerts the security team—all before the attack spreads to other systems.

Author: Marcus Halbrook;
Source: williamalmonte.net
Core Components of an Endpoint Security Server System
Management Console and Dashboard
The management console serves as the administrator's primary interface for configuring policies, monitoring security status, and investigating incidents. Modern consoles emphasize visual dashboards that surface critical information without requiring analysts to dig through logs.
Effective dashboards display real-time metrics: number of protected endpoints, active threats, policy compliance rates, and security posture scores. Drill-down capabilities let administrators investigate specific devices, users, or security events. Search functionality across all endpoint telemetry enables rapid incident investigation—finding every device that connected to a suspicious IP address or executed a particular file hash.
Role-based access controls ensure appropriate segregation of duties. Help desk staff might view endpoint status and initiate basic remediation actions while lacking permission to modify security policies. Security analysts access investigation tools and threat intelligence. Senior administrators control policy configuration and system settings.
Integration capabilities matter significantly. The console should connect with SIEM platforms, threat intelligence feeds, ticketing systems, and vulnerability scanners. API access enables automation—scripting routine tasks, integrating with orchestration platforms, or feeding endpoint data into custom analytics tools.

Author: Marcus Halbrook;
Source: williamalmonte.net
Endpoint Agents and Client Software
Agents represent the server's presence on each protected device. These lightweight programs must balance comprehensive security capabilities against performance impact. Poorly optimized agents that consume excessive CPU, memory, or disk I/O frustrate users and face removal by frustrated employees.
Modern agents employ several techniques to minimize resource consumption. They leverage hardware-based security features like Intel Threat Detection Technology or AMD Secure Processor. They cache frequently accessed threat signatures locally rather than constantly querying the server. They schedule resource-intensive scans during idle periods.
Agent resilience matters when devices operate offline or outside the corporate network. Agents maintain local policy enforcement even when disconnected from the server, applying the last-received configuration until connectivity resumes. Upon reconnection, they synchronize accumulated telemetry and receive policy updates.
Tamper protection prevents attackers from disabling or manipulating agents. Techniques include kernel-level drivers that resist termination, self-healing mechanisms that restore deleted agent files, and integrity checks that detect unauthorized modifications. Some agents implement "safe mode" protections that maintain security even when Windows boots into safe mode—a common attacker tactic for evading security software.
Threat Intelligence and Detection Engine
The detection engine analyzes telemetry from all endpoints to identify security threats. It combines multiple detection methodologies because no single approach catches everything.
Static analysis examines files without executing them—analyzing code structure, embedded resources, digital signatures, and metadata. Dynamic analysis runs suspicious files in isolated sandbox environments, observing their behavior before allowing them onto production systems. Memory scanning detects fileless malware that operates entirely in RAM without touching the disk.
Threat intelligence integration enhances detection accuracy. The server consumes feeds from commercial providers, open-source communities, and industry sharing groups. These feeds provide indicators of compromise (file hashes, domain names, IP addresses, URL patterns) associated with known threat actors. When an endpoint contacts a domain linked to a specific ransomware gang, the server recognizes the connection immediately.
Machine learning models continuously improve detection capabilities. Supervised learning algorithms trained on labeled malware samples identify new variants of existing threat families. Unsupervised learning detects anomalies—unusual patterns that don't match known threats but warrant investigation. Behavioral models establish baseline activity for each endpoint, flagging deviations like a file server suddenly initiating outbound connections or a workstation executing PowerShell scripts at 3 AM.
False positive management remains challenging. Aggressive detection settings catch more threats but generate alerts for legitimate activities. Conservative settings reduce alert fatigue but risk missing genuine attacks. Effective engines provide tuning mechanisms—whitelisting trusted applications, creating exceptions for specific business processes, and adjusting sensitivity thresholds based on endpoint risk profiles.
Common Endpoint Security Server Deployment Models
Organizations choose between three primary deployment architectures based on their infrastructure, compliance requirements, and operational preferences.
| Deployment Model | Infrastructure Requirements | Maintenance Responsibility | Scalability | Typical Cost Structure | Best Use Cases |
| On-Premises | Dedicated servers, storage, network capacity, backup systems | Internal IT team handles updates, patches, hardware maintenance | Limited by purchased capacity; scaling requires hardware procurement | High upfront capital expenditure; ongoing hardware, licensing, personnel costs | Regulated industries with data residency requirements; organizations with existing data center investments; air-gapped networks |
| Cloud-Based | Internet connectivity only; no local infrastructure | Vendor manages all infrastructure, updates, and maintenance | Elastic scaling on-demand; vendor handles capacity planning | Subscription-based per-endpoint pricing; predictable monthly/annual costs | Distributed workforces; rapid deployment needs; organizations minimizing capital expenditure; companies lacking security expertise |
| Hybrid | Limited on-premises infrastructure plus cloud connectivity | Shared between vendor (cloud components) and internal team (local components) | Flexible; scale cloud components while maintaining local presence | Mixed capital and operational expenditure | Large enterprises with both on-premises and remote workers; organizations transitioning to cloud; compliance scenarios requiring local data processing |
On-premises deployments appeal to organizations with strict data sovereignty requirements. Financial institutions, government agencies, and healthcare providers often mandate that security telemetry never leaves their controlled infrastructure. This model provides maximum control over data handling, network traffic, and integration with existing security tools. However, it demands significant IT resources—procuring and maintaining server hardware, managing database performance, applying security patches, and ensuring high availability.
Cloud-based solutions eliminate infrastructure overhead. The vendor hosts management servers in their data centers, handles capacity planning, and maintains system availability. Administrators access the management console through web browsers from anywhere. This model accelerates deployment—organizations can protect endpoints within hours rather than weeks spent provisioning on-premises infrastructure. The subscription pricing model converts capital expenditure into predictable operational costs.
Cloud deployments raise data privacy considerations. Endpoint telemetry—which may include file hashes, process names, user activities, and network connections—transmits to vendor-controlled servers. Organizations must evaluate vendor security practices, data encryption methods, and compliance certifications. Most enterprise-grade cloud solutions offer regional data residency options, letting customers specify geographic locations for data storage.
Hybrid architectures combine both approaches. A local management server handles endpoints within corporate facilities while cloud components protect remote workers and branch offices. This model suits large enterprises with complex requirements—keeping sensitive data on-premises while leveraging cloud scalability for distributed users. The complexity trade-off involves managing two interconnected systems and ensuring consistent policy enforcement across both environments.
Real-World Endpoint Security Server Examples
Several platforms dominate the enterprise endpoint security market, each with distinct architectural approaches and capability emphases.
Microsoft Defender for Endpoint integrates tightly with Windows operating systems and the broader Microsoft security ecosystem. Its server-side components run entirely in Azure cloud infrastructure. The platform leverages Windows security features like Attack Surface Reduction rules, Controlled Folder Access, and hardware-based isolation. Organizations already invested in Microsoft 365 benefit from unified licensing and seamless integration with Azure Sentinel SIEM, Microsoft Intune device management, and Microsoft Threat Intelligence. The platform supports Windows, macOS, Linux, Android, and iOS endpoints, though Windows protection remains most mature.

Author: Marcus Halbrook;
Source: williamalmonte.net
CrowdStrike Falcon pioneered the cloud-native endpoint security architecture. Its lightweight agent (typically under 5MB) maintains minimal local footprint while streaming telemetry to CrowdStrike's cloud infrastructure for analysis. The platform emphasizes threat hunting capabilities—providing security analysts with detailed visibility into endpoint activities and attack timelines. CrowdStrike's threat intelligence team actively tracks specific adversary groups, attributing attacks to particular threat actors. The platform's indicator-of-attack approach focuses on identifying attacker behaviors rather than relying solely on malware signatures.
VMware Carbon Black (formerly Carbon Black Response and Defense) offers both cloud and on-premises deployment options. The platform records comprehensive endpoint activity data, creating searchable archives of process executions, file modifications, network connections, and registry changes. This "DVR for endpoints" approach enables retrospective investigation—analysts can query historical data to determine when an attacker first compromised a system or identify all endpoints that executed a specific file. The platform integrates with VMware's broader security portfolio, including network security and workload protection products.
Symantec Endpoint Protection (now part of Broadcom) represents the evolution of traditional antivirus into comprehensive endpoint security. The platform supports both on-premises and cloud management models. Its multi-layered protection combines signature-based detection, machine learning classification, behavioral analysis, and exploit prevention. Symantec's Global Intelligence Network aggregates threat telemetry from millions of endpoints worldwide, feeding detection engines with current threat data. The platform particularly appeals to large enterprises with complex, heterogeneous environments requiring support for legacy operating systems.
These examples illustrate different architectural philosophies. Microsoft emphasizes integration within its ecosystem. CrowdStrike prioritizes cloud-native architecture and threat intelligence. Carbon Black focuses on forensic investigation capabilities. Symantec balances comprehensive protection with deployment flexibility. Organizations evaluate these differences against their specific requirements, existing infrastructure, and security team capabilities.
Choosing the Right Endpoint Security Server for Your Organization
Company size significantly influences appropriate solutions. Small businesses with 50-200 endpoints typically lack dedicated security teams and benefit from cloud-based platforms with strong automation and minimal management overhead. Mid-sized organizations (200-2,000 endpoints) often require more granular policy controls and integration with existing IT management tools. Large enterprises (2,000+ endpoints) demand scalability, multi-tenancy for business units, and extensive customization capabilities.
Compliance requirements constrain deployment options. Healthcare organizations must ensure HIPAA compliance—protecting patient data, maintaining audit logs, and implementing access controls. Financial institutions face PCI DSS requirements for cardholder data protection. Government contractors need solutions with FedRAMP authorization. Each regulatory framework imposes specific technical controls, data handling requirements, and audit capabilities that endpoint security servers must support.
Integration needs extend beyond security tools. The endpoint security server should connect with identity providers (Active Directory, Okta, Azure AD) for user context, asset management systems for inventory correlation, and patch management platforms for vulnerability coordination. API quality matters—well-documented REST APIs enable custom integrations and automation workflows.
Budget considerations encompass more than license costs. On-premises deployments require server hardware, storage infrastructure, database licensing, and ongoing maintenance. Cloud solutions convert these capital costs into per-endpoint subscriptions but may accumulate higher total costs over extended periods. Calculate total cost of ownership including personnel time for administration, training expenses, and potential costs of security incidents.
Scalability planning should account for growth and seasonal fluctuations. Can the platform handle your current endpoint count plus 30-50% growth? Does licensing accommodate temporary workers or contractors? Cloud platforms typically scale elastically, while on-premises solutions require capacity planning and hardware procurement lead times.
Performance requirements vary by industry. Organizations with high-performance computing workloads or latency-sensitive applications need agents with minimal performance impact. Healthcare imaging workstations, financial trading systems, and manufacturing control systems tolerate little resource consumption from security software. Request performance benchmarks and conduct proof-of-concept testing with representative workloads.
Vendor evaluation should assess company stability, support quality, and development roadmap. How frequently does the vendor release updates? What's their track record for detecting emerging threats? Do they provide 24/7 support? Can they demonstrate customer references in your industry? The endpoint security market consolidates regularly—consider acquisition risk and product roadmap continuity.
Organizations shifting to hybrid work models need endpoint security platforms that provide consistent protection regardless of device location. The traditional perimeter has dissolved, making the endpoint the new security boundary. Centralized management becomes critical when you can't rely on network-based controls
— Peter Firstbrook
Frequently Asked Questions About Endpoint Security Servers
Endpoint security servers transformed from simple antivirus management consoles into comprehensive platforms that protect, detect, investigate, and respond to threats across distributed device populations. The centralized architecture provides security teams with visibility and control impossible with standalone tools, enabling rapid response to emerging threats and consistent policy enforcement across thousands of devices.
Selecting an appropriate platform requires balancing technical capabilities against operational constraints. Cloud-based solutions offer rapid deployment and minimal infrastructure overhead but raise data residency considerations. On-premises deployments provide maximum control at the cost of infrastructure complexity. Hybrid models accommodate complex requirements but demand expertise managing interconnected systems.
The threat landscape continues evolving—ransomware gangs refine their techniques, nation-state actors develop sophisticated exploits, and attack surfaces expand with remote work and IoT proliferation. Endpoint security servers provide the centralized command and control necessary to defend distributed organizations against these persistent threats. Organizations that treat endpoint security as a strategic investment rather than a compliance checkbox position themselves to detect breaches quickly, respond effectively, and minimize damage when attacks inevitably occur.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.