Enterprise servers in a secure data center
Server Endpoint Protection Guide
Servers represent the backbone of enterprise IT infrastructure, housing critical applications, sensitive data, and authentication systems that keep organizations running. Yet many security teams treat server protection as an afterthought, applying the same endpoint security tools they use for employee laptops. This approach creates blind spots that attackers routinely exploit.
Server endpoint protection addresses these gaps with purpose-built security controls that account for server-specific threat models, operational constraints, and architectural differences. Understanding these distinctions matters whether you're securing on-premises data centers, cloud instances, or hybrid environments.
What Is Server Endpoint Protection
Server endpoint protection refers to security software and processes designed specifically to defend server systems from malware, unauthorized access, and exploitation attempts. While the term "endpoint" traditionally evoked images of desktops and laptops, servers qualify as endpoints in modern network architecture—they're discrete devices that communicate across networks and require individual protection.
The core distinction lies in how these tools operate. Desktop endpoint protection prioritizes user behavior monitoring and web-based threat prevention. Server endpoint protection focuses on process integrity, privilege escalation detection, and application-layer attacks that target services rather than human users.
Servers present unique security challenges. They run continuously without user intervention, host multiple concurrent sessions, and execute privileged operations that would trigger alerts on workstations. A web server handling 10,000 requests per minute generates vastly different behavioral patterns than a laptop running email and browsers. Protection mechanisms must distinguish between legitimate server activity and malicious behavior without introducing latency that degrades application performance.

Author: Marcus Halbrook;
Source: williamalmonte.net
Server endpoint protection basics include several foundational components: real-time file scanning optimized for server I/O patterns, memory protection against code injection, application whitelisting to prevent unauthorized executables, and integration with server management tools for centralized policy enforcement. These elements work together to create a defense-in-depth strategy tailored to server workloads.
The technology also accounts for server lifecycle differences. Servers often run legacy operating systems to support critical applications that can't be easily migrated. Protection solutions must support older platforms while defending against modern threats—a balancing act that desktop-focused tools rarely handle well.
The server layer is where adversaries establish persistence and exfiltrate crown jewel data. Generic endpoint tools weren't designed for the unique threat landscape servers face—they lack the granular control and performance optimization that production environments demand
— Chris Krebs
How Server Endpoint Protection Works
Server endpoint protection employs multiple overlapping security mechanisms that monitor different attack vectors simultaneously. The architecture differs significantly from desktop solutions because servers can't tolerate the performance overhead of aggressive scanning or frequent reboots.
Detection and Response Methods
Modern server protection relies on behavioral analysis rather than signature-based detection alone. The system establishes baselines for normal server activity—which processes typically run, what network connections they establish, which files they access, and what system calls they make. Deviations from these baselines trigger investigation.
Machine learning models trained on server-specific attack patterns identify anomalies that indicate compromise. For example, if a web server process suddenly begins reading database credential files or establishing outbound SSH connections, the protection system flags this as suspicious even if no known malware signature matches.
Memory scanning detects fileless malware that never touches disk. These attacks inject malicious code directly into running processes, bypassing traditional file-based scanners. Server protection tools monitor memory allocations, executable regions, and inter-process communication for signs of injection or process hollowing.
Exploit prevention mechanisms guard against common server attack techniques. Buffer overflow protection, return-oriented programming (ROP) mitigation, and data execution prevention (DEP) enforcement stop attackers from leveraging software vulnerabilities to gain code execution. These controls operate at the kernel level with minimal performance impact.
Integration with Server Infrastructure
Server endpoint protection integrates with existing infrastructure components rather than operating in isolation. The protection agent communicates with Security Information and Event Management (SIEM) systems, forwarding detailed telemetry about detected threats, policy violations, and system changes. This integration enables correlation with network security events and identity management logs.
Configuration management integration ensures protection policies align with server roles. A domain controller receives different security controls than a file server or database instance. The protection system queries configuration management databases (CMDBs) to automatically apply appropriate policies based on server function.
Patch management coordination prevents conflicts between security updates and endpoint protection. The system can defer scanning during maintenance windows, validate that patches don't introduce incompatibilities, and verify system integrity after updates complete. Some advanced solutions even prioritize patching based on active exploitation attempts detected across the server fleet.
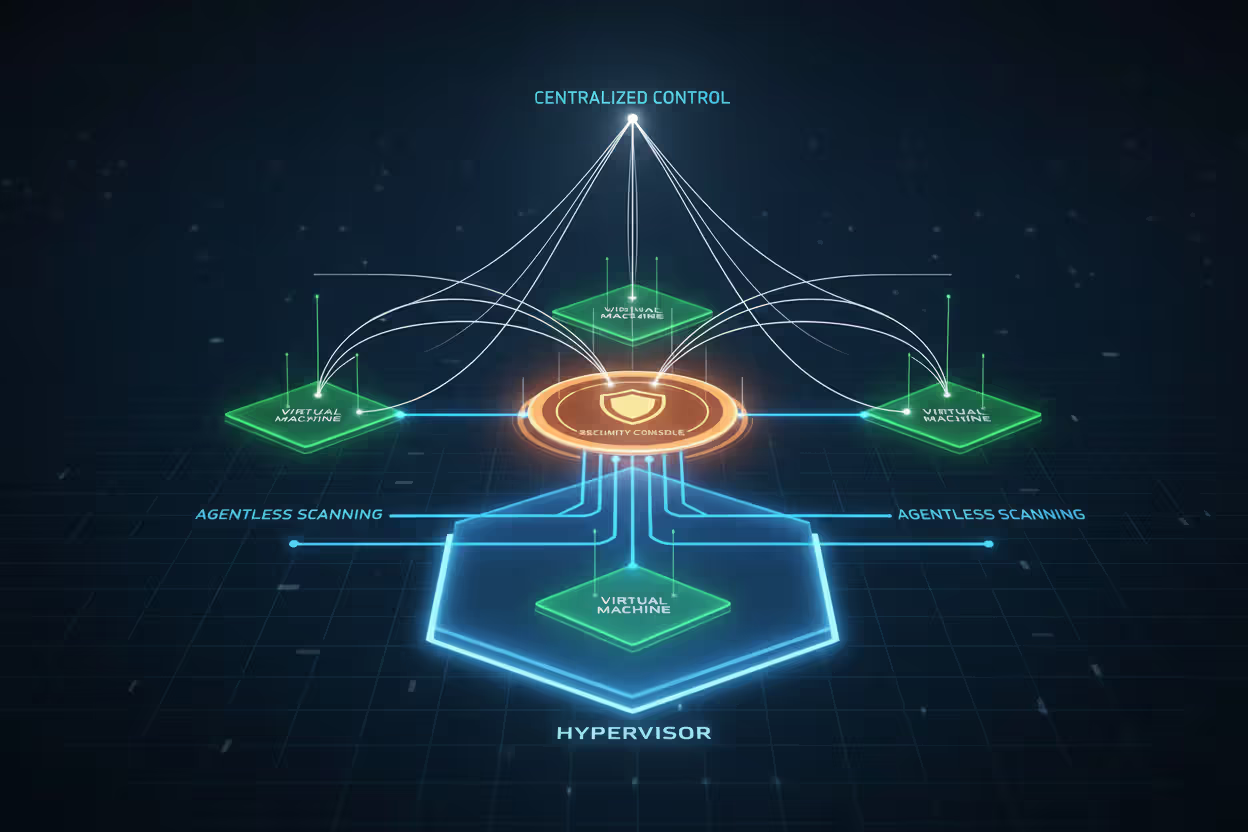
API-level integration with virtualization platforms enables agentless scanning for virtual machines. Rather than installing agents in every VM, the protection system can scan virtual disk files and memory from the hypervisor layer, reducing overhead and simplifying management in large-scale virtual environments.
Author: Marcus Halbrook;
Source: williamalmonte.net
Server vs Desktop Endpoint Protection
The architectural differences between servers and desktops necessitate fundamentally different protection approaches. While both defend against malware and unauthorized access, the implementation details diverge significantly.
| Feature | Desktop Endpoint Protection | Server Endpoint Protection |
| Primary threats | Phishing, browser exploits, removable media | Privilege escalation, lateral movement, service exploitation |
| Performance tolerance | Can pause for scans, tolerate brief slowdowns | Must maintain sub-millisecond response times, zero service interruption |
| Update frequency | Daily definitions, weekly patches acceptable | Real-time threat intelligence, immediate critical patches |
| Management complexity | Individual or small group policies | Role-based policies across hundreds of server types |
| Typical deployment scale | 1:1 per user device | Centralized management for thousands of instances |
Performance impact represents the most critical distinction. Desktop users tolerate occasional slowdowns during scans or updates. Servers supporting production applications cannot. A database server experiencing even 5% performance degradation during peak hours might violate service level agreements and impact revenue. Server protection tools use intelligent scheduling, incremental scanning, and hardware acceleration to minimize resource consumption.
Threat models differ substantially. Desktop users face social engineering attacks, drive-by downloads, and credential theft through phishing. Server threats center on exploitation of network-accessible services, privilege escalation through misconfigured permissions, and lateral movement after initial compromise. Attackers targeting servers aim for persistent access and data exfiltration rather than immediate financial gain through ransomware.
Update strategies reflect these different risk profiles. Desktop protection can operate effectively with daily signature updates. Servers require real-time threat intelligence feeds because they're constantly exposed to automated scanning and exploitation attempts. A zero-day vulnerability announced publicly will face exploitation attempts within hours—servers need protection updates immediately, not during the next scheduled refresh.
Management complexity scales differently. An organization might manage desktop endpoints with broad policies applied to all users or departments. Server management requires granular control based on server roles, compliance requirements, network zones, and application dependencies. A payment processing server needs PCI-DSS-compliant controls, while a development server in an isolated network requires less restrictive policies.

Author: Marcus Halbrook;
Source: williamalmonte.net
Common Server Threats and Protection Examples
Server endpoint protection defends against a distinct threat landscape. Understanding common attack patterns helps illustrate how protection mechanisms respond to real-world scenarios.
Ransomware targeting backups: Attackers increasingly focus on server-based backup systems, knowing that encrypted backups force victims to pay ransoms. In a typical scenario, an attacker gains initial access through compromised credentials, then moves laterally to the backup server. Server endpoint protection detects the unusual authentication pattern—a service account suddenly accessing backup storage from a different system—and blocks the encryption attempt before it completes. Behavioral analysis identifies the rapid file modification pattern characteristic of ransomware, even if the malware variant is previously unknown.
Rootkit installation for persistence: After exploiting a web application vulnerability, an attacker attempts to install a kernel-mode rootkit to maintain access. The rootkit tries to modify system files and inject code into the operating system kernel. Server endpoint protection's integrity monitoring detects unauthorized changes to protected system files, while memory protection mechanisms prevent kernel code injection. The system quarantines the malicious files and alerts administrators to the compromise attempt.
Privilege escalation through misconfiguration: An attacker exploits a vulnerable web application to gain limited code execution as the web server user account. They attempt to escalate privileges by exploiting a local kernel vulnerability. Server protection monitors system calls for suspicious patterns—the web server process shouldn't be loading kernel modules or modifying user permissions. The protection system blocks the escalation attempt and isolates the compromised process before the attacker gains administrative access.
Lateral movement via stolen credentials: After compromising one server, attackers use credential dumping tools to extract authentication tokens from memory. They attempt to use these credentials to access other servers. Server endpoint protection detects the credential dumping tool through behavioral analysis—the suspicious process is reading memory regions belonging to authentication services. It also monitors for unusual authentication patterns, flagging when a server account suddenly authenticates to multiple systems in rapid succession.
Zero-day exploit against network service: Attackers exploit an unpatched vulnerability in a database service to execute arbitrary code. The exploit leverages a buffer overflow to inject shellcode. Server protection's exploit mitigation features detect the buffer overflow attempt and prevent code execution. Even though no signature exists for this specific exploit, the protection system recognizes the attack technique and blocks it at the exploit stage.
Cryptomining malware: An attacker deploys cryptocurrency mining software on compromised servers to monetize access. The mining process consumes CPU resources and generates unusual network traffic to mining pools. Server endpoint protection identifies the unauthorized executable through application whitelisting—only approved software should run on production servers. It also detects the abnormal resource consumption pattern and network behavior, flagging the mining activity even if the malware evades signature detection.

Author: Marcus Halbrook;
Source: williamalmonte.net
Choosing Server Endpoint Protection for Your Environment
Selecting appropriate server protection requires evaluating several technical and operational factors. The right solution depends on your specific infrastructure, compliance requirements, and risk tolerance.
Operating system compatibility tops the priority list. Verify that the protection solution supports all server operating systems in your environment, including legacy versions. Many organizations run Windows Server 2012 or older Linux distributions for specific applications. The protection vendor should provide agents for these platforms and commit to supporting them through your planned retirement timeline. Cloud-native environments running containers require protection tools that integrate with orchestration platforms like Kubernetes rather than traditional agent-based approaches.
Performance overhead demands careful evaluation through proof-of-concept testing. Deploy the protection solution on representative servers under realistic load conditions. Measure CPU utilization, memory consumption, disk I/O impact, and network latency before and after deployment. Application response times provide the most meaningful performance metric—protection that adds 10ms of latency to database queries might be unacceptable for latency-sensitive applications. Request performance benchmarks from vendors, but verify them in your environment.

Author: Marcus Halbrook;
Source: williamalmonte.net
Compliance alignment determines whether a solution meets regulatory requirements. PCI-DSS, HIPAA, and SOC 2 mandate specific endpoint protection capabilities. Verify that the solution provides required features like file integrity monitoring, audit logging, and access controls. Check whether the vendor maintains relevant certifications and provides compliance mapping documentation. Some industries require protection solutions validated under programs like FIPS 140-2 or Common Criteria.
Cloud versus on-premises architecture influences deployment models. Cloud-native protection solutions integrate with AWS, Azure, and Google Cloud security services, leveraging cloud provider APIs for agentless scanning and automated policy enforcement. On-premises environments benefit from solutions that integrate with existing security infrastructure like SIEM systems and network security tools. Hybrid environments need protection platforms that provide consistent policies and centralized management across both deployment models.
Scalability and automation become critical at scale. Organizations managing hundreds or thousands of servers need protection platforms with robust automation capabilities. Look for solutions that integrate with infrastructure-as-code tools, support automated policy deployment, and provide APIs for custom integrations. The management console should handle large server fleets without performance degradation and provide efficient workflows for investigating alerts across many systems.
Vendor support and threat intelligence quality varies significantly. Evaluate the vendor's threat research capabilities, update frequency, and response time to emerging threats. Review their track record for detecting zero-day exploits and providing timely protection updates. Technical support quality matters when investigating complex security incidents—verify that the vendor provides access to senior security analysts rather than just tier-1 support.
Implementation Mistakes to Avoid
Deploying server endpoint protection involves common pitfalls that undermine security effectiveness or cause operational problems. Learning from these mistakes accelerates successful implementation.
Skipping pre-deployment testing causes the most frequent problems. Organizations sometimes rush deployment without adequate testing, only to discover that the protection agent conflicts with critical applications or degrades performance below acceptable levels. Always test in a non-production environment that mirrors production configurations. Run representative workloads and measure performance impact before deploying to production servers.
Using desktop protection policies on servers creates either security gaps or operational issues. Desktop-focused policies often include aggressive web filtering, USB device controls, and user behavior monitoring that don't apply to servers. Conversely, they may lack server-specific controls like service account monitoring and privilege escalation detection. Build server-specific policies based on server roles and threat models rather than adapting desktop policies.
Neglecting legacy and specialty servers leaves attack vectors unprotected. Organizations sometimes exclude older servers from endpoint protection because they assume legacy systems won't support modern security agents. Attackers specifically target these unprotected systems as easy entry points. Work with vendors to identify compatible protection options for legacy platforms, even if they require specialized deployment approaches.
Inadequate exclusion management causes both performance and security problems. Overly broad exclusions—like excluding entire directories or all files from a specific application—create security blind spots that attackers exploit. Too few exclusions cause performance problems or application failures. Document the specific reason for each exclusion, regularly review exclusions for continued necessity, and use the most specific exclusion possible (individual files rather than directories).
Ignoring alert tuning results in alert fatigue. Initial deployments often generate high volumes of false positives that overwhelm security teams. Rather than investigating and tuning policies to reduce noise, teams sometimes disable alerts or ignore them entirely. Invest time in baseline establishment and policy tuning during the first weeks after deployment. Work with the vendor to understand which alerts indicate genuine threats versus expected server behavior.
Failing to integrate with incident response limits protection effectiveness. Endpoint protection tools generate valuable forensic data during security incidents, but only if properly integrated with incident response processes. Ensure that security teams know how to query endpoint protection systems for indicators of compromise, extract forensic artifacts, and correlate endpoint data with network and identity logs.
Deploying without rollback plans creates risk during production deployment. If protection agents cause unexpected application failures or performance problems, you need the ability to quickly remove or disable them. Prepare rollback procedures, test them in advance, and ensure that operations teams can execute them without security team involvement if necessary.
Frequently Asked Questions About Server Endpoint Protection
Server endpoint protection addresses security requirements that generic endpoint tools cannot adequately fulfill. The unique operational characteristics of servers—continuous operation, high-performance demands, privileged access patterns, and exposure to sophisticated targeted attacks—require purpose-built protection mechanisms.
Effective server protection combines real-time threat detection, behavioral analysis, exploit prevention, and deep integration with server infrastructure. The technology must defend against server-specific threats like privilege escalation, lateral movement, and persistent access while maintaining the performance levels that production applications demand.
Successful implementation requires careful planning, thorough testing, and ongoing tuning. Organizations that treat server protection as a distinct security discipline—rather than simply extending desktop protection to servers—build more resilient infrastructure that can withstand contemporary attack techniques.
The investment in proper server endpoint protection pays dividends through reduced breach risk, faster incident response, and stronger compliance posture. As server infrastructure continues evolving toward cloud-native architectures and containerized workloads, protection strategies must evolve accordingly while maintaining focus on the fundamental principle: servers require security controls designed specifically for their unique role in enterprise infrastructure.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.