Linux endpoint security protecting enterprise servers
Endpoint Security for Linux Guide
Content
Content
Think of endpoint security for Linux as a dedicated bodyguard for each individual machine in your infrastructure—whether that's a server handling customer transactions, a developer workstation running containerized apps, or a virtual machine processing sensitive data. Unlike firewalls that guard your network perimeter, these security tools live directly on each Linux system, constantly watching what's happening at the operating system level.
Here's what surprises most people: Linux isn't magically immune to attacks. I still hear IT managers say "We run Linux, so we're fine" at conferences. That might've been reasonable thinking back in 2010 when Linux desktop market share was negligible. But today? Linux runs nearly half of all enterprise servers, dominates public cloud infrastructure, and powers the containerized applications driving modern businesses. Attackers know this. They've adapted.
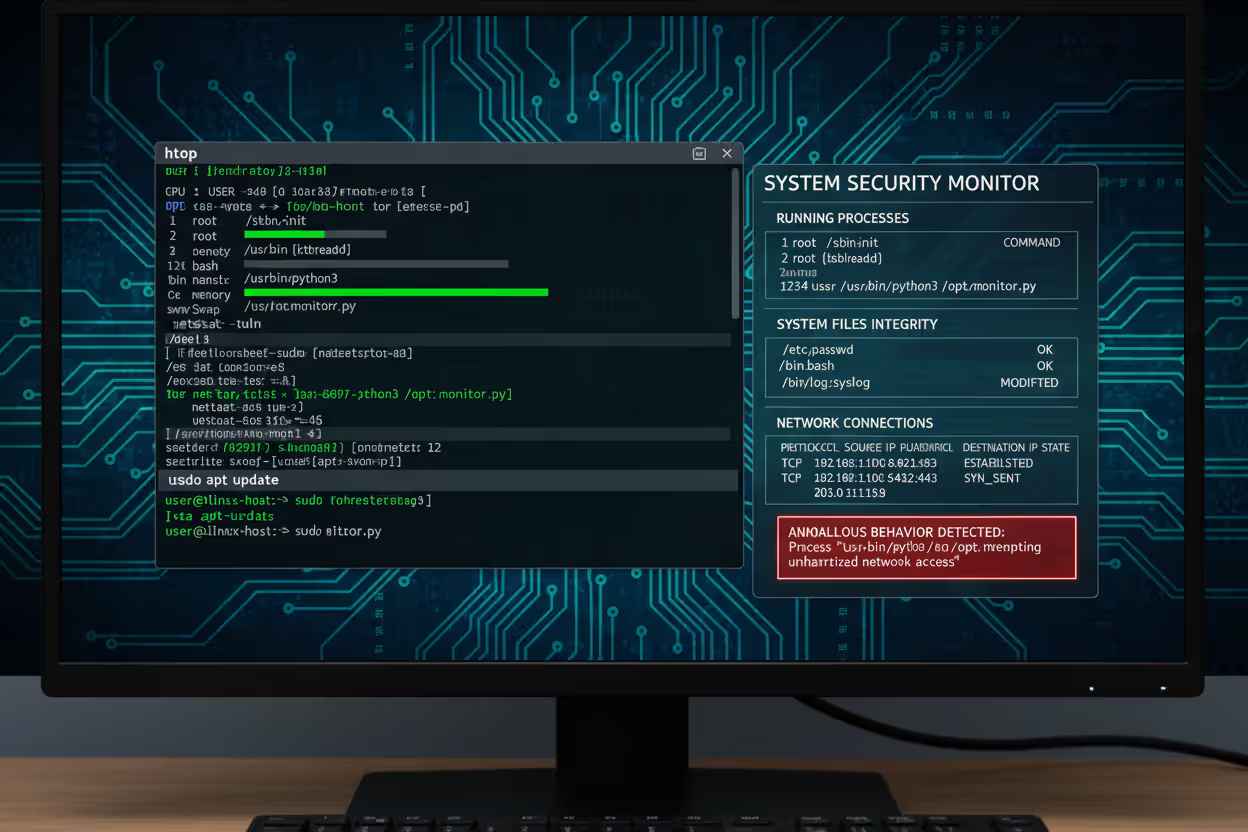
When we talk about endpoint security for linux basics, we're really discussing several protection layers working together. You've got real-time file monitoring that catches suspicious changes to system binaries. There's process behavior analysis that flags when your Apache web server suddenly tries spawning shell commands (a huge red flag). Network monitoring tracks which processes are making outbound connections and where they're going. Memory protection stops code injection attempts dead in their tracks.
A solid Linux endpoint security solution doesn't just scan for known malware signatures—that's 2015 technology. Modern tools build behavioral profiles of your systems. They learn that your PostgreSQL database normally accesses certain files, communicates on specific ports, and runs with particular resource patterns. When something deviates—maybe a privilege escalation attempt or unauthorized configuration tampering—alerts fire immediately.
The endpoint security for linux explained concept boils down to this: continuous visibility into what's actually executing on your machines, combined with intelligent analysis that separates legitimate admin activities from potential threats. You want protection that works silently in the background until something genuinely dangerous happens.
Author: Daniel Prescott;
Source: williamalmonte.net
How Endpoint Security for Linux Works
Let's get technical about how endpoint security for linux works, because understanding the mechanics helps you choose and configure these tools effectively.
Core Protection Components
File integrity monitoring sits at the foundation. This component takes cryptographic checksums of critical system files—your kernel modules, shared libraries, configuration files in /etc, and essential binaries in /bin and /usr/bin. Every time something modifies these files, the monitoring system notices. Legitimate package updates? Expected. Mystery changes at 3 AM from an unknown process? That's when your phone should ring.
I've seen file integrity monitoring catch everything from clumsy malware that overwrites system utilities to sophisticated rootkits that carefully modify just a few bytes in kernel modules. The key is establishing your baseline before threats appear, not after.
Process monitoring examines every running task against what should be happening. Your endpoint agent maintains process genealogies—which parent process spawned which child processes. This matters because legitimate system updates follow predictable patterns, while malware often creates unusual process trees. When a web-facing service unexpectedly forks bash shells or wget processes, that's textbook compromise behavior.
Memory protection mechanisms have gotten incredibly sophisticated. They watch for return-oriented programming attacks, buffer overflows, and code injection attempts targeting running processes. Instead of just scanning files on disk, these components monitor actual execution flow in RAM. Attackers can't hide in memory anymore.
Network analysis at the endpoint reveals which specific processes generate traffic. Your centralized firewall might see encrypted HTTPS connections leaving your network, but endpoint security knows whether that traffic came from a legitimate update service or a cryptominer phoning home to its command server.

Author: Daniel Prescott;
Source: williamalmonte.net
Detection and Response Methods
Behavioral analysis has revolutionized Linux security. Rather than maintaining massive databases of malware signatures (which miss zero-day attacks), modern systems establish operational baselines. They learn normal patterns over days or weeks: typical CPU usage, standard network connections, expected file access patterns, routine authentication events.
Deviations trigger investigations. Maybe your normally quiet backup server suddenly starts CPU-intensive operations at unusual hours. Could be legitimate—or it could be cryptomining malware. The system flags it for review.
Threat intelligence feeds continuously pump updated indicators into your endpoint agents: malicious IP addresses from recent campaigns, file hashes of known Linux malware families, domain names associated with command-and-control infrastructure. When your systems encounter these indicators, responses happen automatically based on your configured policies.
Automated response capabilities range from passive alerting to aggressive isolation. Detecting confirmed ransomware? The agent might immediately kill the malicious process, quarantine affected files, and network-isolate the entire endpoint—all within seconds, before encryption spreads. You configure these responses based on threat severity and business impact tolerance.
Real-time scanning happens at multiple checkpoints throughout normal operations. Files get scanned when accessed, when modified, when executed. Network connections get analyzed when established. Process launches trigger behavioral checks. This creates continuous protection rather than periodic vulnerability windows.
Common Threats Targeting Linux Endpoints
Linux-focused threats have matured significantly. Attackers aren't just repurposing Windows malware anymore—they're building custom toolchains specifically for Linux environments.
Cryptominers dominate the threat landscape by volume. Attackers scan the internet for exposed Redis instances, misconfigured Docker APIs, or servers running outdated SSH implementations. Once they breach a system, they deploy mining software that quietly consumes 80-90% of available CPU cycles generating Monero or other cryptocurrencies. Organizations sometimes run these infections for months, paying inflated cloud bills while attackers profit. One retail company I consulted for discovered cryptominers on 47 EC2 instances, costing them roughly $15,000 monthly in unnecessary compute charges.
Ransomware targeting Linux accelerated dramatically after 2023. Groups like LockBit developed Linux-native variants specifically designed for VMware ESXi hosts and Linux file servers. These attacks typically target backup repositories first—encrypt your backups, then encrypt production systems, and suddenly recovery becomes nearly impossible. Ransom demands for mid-sized companies often start at $500,000 and escalate quickly.
Rootkits achieve persistent stealth access by compromising the kernel itself or critical system components. Modern variants hook system calls, hide processes from ps output, and conceal network connections from standard monitoring tools. You might be running netstat and seeing clean results while a rootkit-hidden backdoor siphons data continuously. Detection requires specialized forensic tools that compare kernel memory structures against expected values.
Privilege escalation exploits turn limited user access into root control. Attackers discover vulnerabilities in SUID binaries, misconfigured sudo rules, or kernel bugs that allow privilege elevation. The 2022 Dirty Pipe vulnerability (CVE-2022-0847) affected Linux kernels since 5.8, allowing any user to overwrite read-only files and gain root. Thousands of systems got compromised before patches deployed.
Supply chain compromises exploit trust in software repositories and open-source packages. Attackers inject malicious code into popular npm packages, PyPI libraries, or even compromise official distribution repositories. The 2024 XZ Utils backdoor attempt showed how close we came to a massive supply chain breach—malicious code nearly made it into production SSH implementations across major Linux distributions.
Container escape vulnerabilities let attackers break out of containerized isolation. They compromise an application running inside Docker or Kubernetes, then exploit kernel vulnerabilities or container runtime bugs to access the host system. From there, they can compromise every container on that host and potentially pivot throughout your infrastructure.

Author: Daniel Prescott;
Source: williamalmonte.net
Endpoint Security Solutions for Linux
Looking at endpoint security for linux examples available today, you'll find options spanning fully-managed commercial platforms to community-driven open-source projects.
CrowdStrike Falcon for Linux delivers cloud-native protection with a lightweight agent that monitors processes, files, and network activity. Their threat intelligence comes from analyzing millions of endpoints globally. Management happens through a unified cloud console covering Windows, Mac, and Linux systems. They support major distributions—RHEL, Ubuntu, Amazon Linux, SUSE—with agents that typically consume under 3% CPU during normal operations.
Microsoft Defender for Endpoint expanded Linux support substantially since 2023. It integrates tightly with Azure infrastructure and Microsoft's threat intelligence network. Organizations already using Microsoft security tools often choose this for simplified management. Licensing runs per-user rather than per-endpoint, which can benefit or hurt depending on your user-to-server ratio.
SentinelOne approaches detection differently, using AI models trained on behavioral patterns rather than signature matching. Their agents can roll back ransomware encryption automatically, restoring affected files to pre-attack states. This rollback capability has saved several customers I've worked with from catastrophic data loss.
Open-source alternatives like Wazuh provide comprehensive security monitoring without licensing costs. Wazuh combines intrusion detection, log analysis, file integrity monitoring, and compliance reporting. You host the management infrastructure yourself—typically a central manager coordinating multiple agents. Configuration requires more technical expertise than commercial platforms, but you gain complete transparency and customization flexibility.
OSSEC pioneered open-source host intrusion detection for Linux. It's mature, stable, and supports virtually every Linux distribution. Many organizations run OSSEC as their primary detection layer, then add commercial tools for specific advanced capabilities.
Cloud-native platforms like Aqua Security and Sysdig Secure focus specifically on containerized workloads. They understand Kubernetes deployments, monitor container runtime behavior, and enforce policy controls appropriate for ephemeral infrastructure. Traditional endpoint tools often struggle with containers that exist for minutes rather than months.
Deployment approaches vary significantly. Agent-based installations put software directly on each endpoint, providing deep visibility but requiring ongoing maintenance. Agentless scanning leverages hypervisor APIs or cloud provider integrations to monitor systems without installed software, reducing operational overhead but potentially missing certain threat categories or introducing detection delays.
Implementing Endpoint Security on Linux Systems
Here's where theory meets reality. I've seen endpoint security for linux implementations succeed brilliantly and fail spectacularly, usually based on planning quality rather than product selection.
Start with complete asset discovery. You need accurate inventory of every Linux system requiring protection: physical servers in data centers, virtual machines across environments, cloud instances spanning multiple regions, containers running in orchestration platforms, even embedded Linux devices. Document each system's role, criticality, current security controls, and network connectivity. This inventory drives your deployment priorities—protect internet-facing systems first, then work inward.
Measure baseline performance before installing anything. Record CPU utilization, memory consumption, disk I/O rates, and network latency under typical workloads. You'll need these numbers later when someone claims "endpoint security is killing performance." Objective baselines prevent blame games and help identify genuine performance issues requiring configuration tuning.
Run pilot deployments in non-production environments first. I recommend selecting systems that mirror your production architecture—same distributions, same kernel versions, same application stacks. Operate the pilot for at least two weeks, monitoring for compatibility issues, false positives, and performance impacts. One financial services client discovered their endpoint agent conflicted with a custom kernel module they'd compiled for database optimization. Finding that in testing rather than production saved them a weekend outage.
Common implementation mistakes happen repeatedly across organizations. Don't deploy agents during peak business hours—schedule rollouts during maintenance windows. Don't enable aggressive blocking policies until you've tuned detection thresholds through weeks of monitoring. Don't apply identical policies across all systems—a web server needs different controls than a database server or developer workstation.
Configure role-based policies reflecting actual system purposes. Your DMZ web servers warrant strict network monitoring and aggressive response policies. Internal development systems might allow more latitude for unusual activities. Database servers need exclusions for high-I/O data directories. One-size-fits-all policies generate either excessive false positives or insufficient protection.
Exclude high-traffic directories from real-time scanning to prevent performance bottlenecks. Database file directories that handle thousands of operations per second don't need continuous on-access scanning—schedule periodic scans during off-hours instead. Application log directories accumulating gigabytes daily can overwhelm real-time scanners. Temporary file locations used by compilation processes create scanning overhead without meaningful security benefit.
Centralize logging immediately. Feed endpoint security events into your SIEM platform, log aggregation system, or cloud logging service. Centralized visibility enables correlation between endpoint events, network traffic, authentication logs, and application activities. Sophisticated attacks spanning multiple systems only become visible when you can analyze events holistically.
Document incident response procedures before incidents occur. Who receives critical alerts? Who investigates anomalies? Who authorizes containment actions? Who coordinates recovery? Define escalation paths, communication protocols, and remediation workflows for different threat categories. Running your first incident response during an actual compromise creates chaos.
Schedule monthly tuning sessions reviewing false positives, updating exclusion lists, and refining detection policies. Endpoint security requires ongoing optimization—your threat landscape evolves, your applications change, your business requirements shift. I've seen organizations abandon effective security tools simply because they never invested in tuning, leading to alert fatigue and eventual disablement.

Author: Daniel Prescott;
Source: williamalmonte.net
Choosing the Right Endpoint Security for Your Linux Environment
Selecting Linux endpoint protection requires matching capabilities against your specific requirements. What works for a 50-person startup won't necessarily suit a multinational bank.
Verify distribution support meticulously. Some vendors only officially support RHEL, Ubuntu LTS, and SUSE Enterprise. Others extend coverage to Debian, CentOS Stream, Amazon Linux, Oracle Linux, and more specialized distributions. Check specific kernel version compatibility—running a slightly older kernel for stability? Make sure it's supported. Using ARM64 architecture in some environments? Confirm support beyond standard x86_64.
Management scalability matters enormously as endpoint counts grow. Cloud-based consoles generally scale effortlessly from hundreds to hundreds of thousands of endpoints. On-premises management servers hit practical limits—database performance degrades, web interface responsiveness suffers, backup windows extend. One manufacturing company managing 12,000 Linux endpoints discovered their on-premises console couldn't handle real-time updates at that scale. They migrated to a cloud-managed solution within three months.
Performance overhead varies dramatically between products. Request detailed benchmarks showing CPU, memory, and I/O impact under realistic workloads. Some agents consume 1-2% CPU during normal operations and spike to 8-10% during scheduled scans. Others maintain 5% baseline consumption and spike to 20% when scanning. For latency-sensitive trading systems or resource-constrained IoT devices, these differences determine viability.

Author: Daniel Prescott;
Source: williamalmonte.net
Detection sophistication separates basic from advanced solutions. Can the platform detect fileless malware executing purely in memory? Does it identify container escape attempts? Will it catch supply chain compromises in software updates? Request proof-of-concept testing using realistic attack scenarios—watch vendors attempt detection against modern Linux-specific threats, not outdated sample malware.
Integration capabilities determine how smoothly endpoint security fits your existing infrastructure. Native SIEM integration? API availability for automation? Webhook support for security orchestration? Compatibility with your vulnerability management platform? Rich integrations reduce implementation complexity and accelerate incident response. One retail customer required endpoint security integration with their ServiceNow ticketing system—automatic ticket creation for certain threat types, with context and remediation guidance pre-populated.
Compliance support becomes critical in regulated industries. Financial services, healthcare, and government organizations need audit trails, compliance dashboards, and configuration baselines aligned with specific frameworks. PCI DSS requires file integrity monitoring for cardholder data environments. HIPAA mandates access logging and integrity controls for protected health information systems. Some endpoint platforms include pre-built compliance reports that transform audit preparation from weeks of manual evidence collection to automated report generation.
Budget considerations extend well beyond license costs. Calculate total ownership costs including deployment effort (internal staff time or professional services), ongoing management overhead, infrastructure requirements for management servers (if self-hosted), training expenses, and opportunity costs. Open-source solutions eliminate licensing fees but demand skilled personnel for deployment, integration, and maintenance. Commercial platforms charge recurring fees scaling with endpoint counts but include vendor support, automatic updates, and managed threat intelligence.
Vendor viability and strategic alignment influence long-term success. Evaluate financial stability—you don't want your security vendor acquired and dismantled mid-contract. Assess product development velocity through release notes and roadmap transparency. Consider strategic direction—vendors committed to Linux and cloud-native technologies will likely evolve more favorably than those treating Linux as secondary to Windows-focused platforms.
Anyone still believing Linux systems don't need serious endpoint protection is living dangerously in the past.We're watching adversaries build sophisticated toolchains specifically targeting Linux environments. Container adoption created entirely new attack surfaces requiring runtime monitoring and behavioral analysis. Organizations treating Linux security casually typically discover their mistakes during incident response—usually after significant damage. Effective protection demands multiple defensive layers: endpoint monitoring, network security, and configuration management, all informed by current threat intelligence. The question isn't whether you need Linux endpoint security—it's whether you can afford the consequences of skipping it
— Sarah Chen
Frequently Asked Questions About Linux Endpoint Security
Linux endpoint security has shifted from "nice to have" to operational requirement. The expanding attack surface from cloud migration, containerization, and Linux's dominant enterprise presence demands protection beyond outdated assumptions about operating system immunity. Current threats—from targeted ransomware to supply chain compromises—require detection combining behavioral analysis, threat intelligence, and rapid response.
Effective implementation balances protection depth against operational efficiency. Evaluate solutions based on your specific distributions, workload characteristics, and security maturity. Whether choosing commercial platforms with integrated management or building protection from open-source components, success requires careful planning, phased deployment, and continuous optimization.
Investing in Linux endpoint security reduces breach risk, improves compliance posture, and provides visibility into system activities that would otherwise remain opaque. As attackers continue developing Linux-specific techniques, organizations deploying comprehensive endpoint protection maintain operational resilience while those relying on outdated security assumptions face escalating risks and eventual compromise.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.