API endpoint security dashboard with protected network connections
API Endpoint Security Guide
Every API endpoint you expose is a potential doorway into your system. Whether you're running a SaaS platform, a mobile app backend, or an internal microservices architecture, securing those endpoints determines whether you're building a fortress or leaving the gates wide open.
API endpoint security isn't just another checkbox on a compliance form. It's the difference between controlled access and data breaches that make headlines. This guide breaks down what you need to know, from basic concepts to real-world implementation strategies.
What Is API Endpoint Security
An API endpoint is a specific URL where your application programming interface can access the resources it needs. Think of it as a digital address—like https://api.yourapp.com/users/profile or https://payment.service.com/v2/transactions. Each endpoint represents a function: retrieving data, creating records, updating information, or deleting resources.
API endpoint security explained simply means protecting these digital addresses from unauthorized access, malicious attacks, and data theft. The challenge? Endpoints must be accessible enough for legitimate users while blocking everyone else. Unlike a traditional web application where a human logs in through a browser, APIs handle machine-to-machine communication. There's no CAPTCHA, no "Forgot Password?" link—just raw requests and responses.
Endpoints become vulnerable for several reasons. They're often documented publicly (or semi-publicly), making them easy to discover. They handle sensitive operations like payment processing, user authentication, and data retrieval. Many organizations expose dozens or hundreds of endpoints, and securing them all consistently proves difficult. A single misconfigured endpoint can expose your entire database.
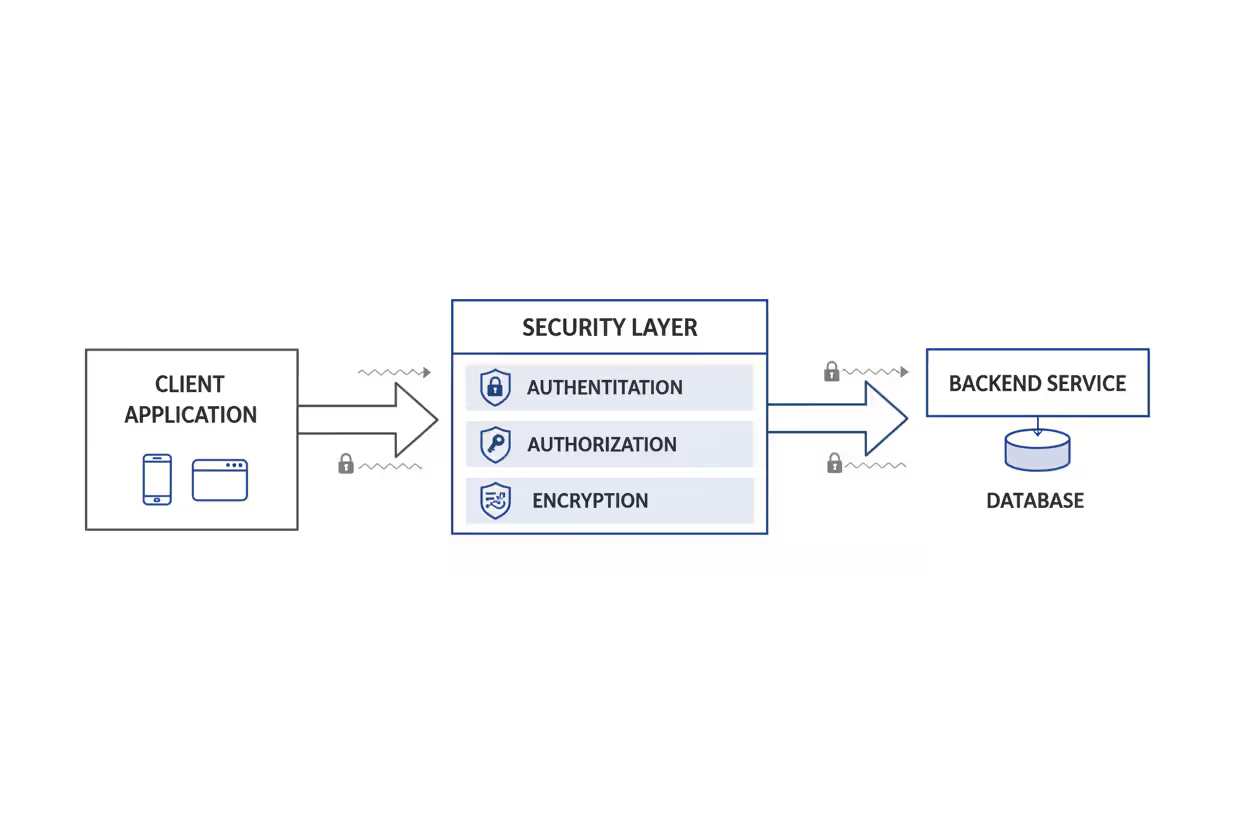
The core concept behind api endpoint security basics involves three pillars: verifying who's making the request (authentication), confirming they're allowed to perform that action (authorization), and protecting the data in transit (encryption). Miss any one of these, and you've created a vulnerability.
Author: Marcus Halbrook;
Source: williamalmonte.net
How API Endpoint Security Works
Securing an endpoint means implementing multiple layers of protection. Each request travels through several checkpoints before reaching your application logic and returning a response.
Authentication Methods
Authentication answers one question: who are you? When a request hits your endpoint, you need proof of identity before proceeding.
API keys represent the simplest approach. You generate a unique string—something like ak_live_9x8f3j2k1m4n5p6q7r8s—and clients include it in their requests, typically as a header or query parameter. They're easy to implement but have limitations. If someone intercepts your API key, they can impersonate you until you revoke it. Many developers accidentally commit keys to public GitHub repositories, exposing them to automated scanners.
HTTP Basic Authentication sends a username and password with each request, encoded in Base64. It's straightforward but requires sending credentials repeatedly. Unless you're using HTTPS (which you absolutely should be), these credentials travel in plain text.
Bearer tokens improve on basic authentication by separating the login process from subsequent requests. A client authenticates once with credentials, receives a token, and includes that token in future requests. The token expires after a set period, limiting damage if it's compromised.
JSON Web Tokens (JWT) take bearer tokens further. A JWT contains encoded information about the user and their permissions, digitally signed to prevent tampering. Your server can verify a JWT without querying a database, making them efficient for distributed systems. The payload might include user ID, role, and expiration time—everything needed to make authorization decisions.
Certificate-based authentication uses SSL/TLS client certificates for high-security scenarios. The client proves identity with a cryptographic certificate rather than a password. Banks and government systems often require this approach, though it adds complexity to client setup.
Authorization and Access Control
Authentication tells you who someone is. Authorization determines what they can do.
Role-Based Access Control (RBAC) assigns permissions based on roles. An "admin" role might access all endpoints, while a "viewer" role only reads data. When a request arrives, you check the authenticated user's role against the required permissions for that endpoint.
Attribute-Based Access Control (ABAC) makes more granular decisions using attributes: user department, time of day, IP address, resource owner, and data sensitivity. You might allow a manager to approve expenses under $5,000 during business hours from office IP addresses, but require additional approval otherwise.
Scope-based authorization, common in OAuth 2.0, lets you grant specific permissions. Instead of "all or nothing" access, a mobile app might request read:profile and write:posts scopes but not delete:account. Users see exactly what they're granting.
The principle of least privilege should guide your authorization design. Grant the minimum permissions necessary for each role or client. A webhook that posts order confirmations doesn't need permission to delete user accounts.
Data Encryption and Transport Security
Even with perfect authentication and authorization, attackers can intercept data traveling between client and server. This is where how api endpoint security works becomes critical at the transport layer.
TLS (Transport Layer Security), the successor to SSL, encrypts all data in transit. When you use HTTPS instead of HTTP, you're using TLS. It prevents man-in-the-middle attacks where someone intercepts and reads your traffic. TLS 1.3, the current standard in 2026, offers improved performance and security over older versions.
Certificate pinning adds another layer for mobile apps. Instead of trusting any valid certificate, the app only accepts a specific certificate or public key. This prevents attacks using fraudulent certificates, though it requires updating your app when certificates rotate.
For extremely sensitive data, consider encrypting the payload itself before transmission. TLS protects data in transit, but payload encryption protects it even if TLS is somehow compromised. Financial institutions often encrypt account numbers and transaction details within an already-encrypted HTTPS connection.

Author: Marcus Halbrook;
Source: williamalmonte.net
Common API Endpoint Security Threats
Understanding threats helps you prioritize defenses. The OWASP API Security Top 10 project tracks the most critical vulnerabilities affecting APIs.
Injection attacks occur when an attacker sends malicious data that your application interprets as commands. SQL injection remains common: an endpoint accepting a username parameter might receive admin' OR '1'='1 instead, potentially exposing all users. NoSQL injection, XML injection, and command injection follow similar patterns. The fix? Never trust user input. Use parameterized queries and input validation.
Broken authentication means weak or flawed identity verification. Examples include endpoints that don't require authentication at all, weak password policies, credential stuffing attacks (trying stolen username/password pairs from other breaches), and authentication tokens that never expire. One API gateway misconfiguration in 2025 exposed customer data for a major retailer because an internal endpoint was accidentally made public.
Excessive data exposure happens when endpoints return more information than necessary. An endpoint might return full user objects including password hashes, internal IDs, and personal details when the client only needs a name and email. Attackers analyze these responses to map your data structure and find sensitive information. Always filter responses to include only required fields.
Lack of rate limiting allows attackers to overwhelm your endpoints with requests. This enables brute-force attacks (trying thousands of passwords), denial-of-service attacks (making your API unavailable to legitimate users), and data scraping (downloading your entire database through repeated requests). Without rate limits, someone can make millions of requests in minutes.
Man-in-the-middle attacks intercept communication between client and server. Without HTTPS, attackers on the same WiFi network can read every request and response, stealing credentials and sensitive data. Even with HTTPS, certificate validation issues or downgrade attacks can create vulnerabilities.
Broken object-level authorization is particularly dangerous. An endpoint might check if you're authenticated but not whether you're authorized to access that specific resource. Consider GET /api/users/12345/orders. If the endpoint only verifies you're logged in but doesn't confirm user 12345 is you, an attacker can iterate through user IDs and access everyone's orders.
Security misconfiguration covers a range of issues: default passwords, unnecessary features enabled, verbose error messages revealing system details, unpatched software, and misconfigured CORS policies. A single misconfigured S3 bucket or database port can expose everything.

Author: Marcus Halbrook;
Source: williamalmonte.net
API Endpoint Security Methods and Tools
Protecting endpoints requires combining multiple techniques and tools into a cohesive security strategy.
API gateways sit between clients and your backend services, acting as a security checkpoint. They handle authentication, rate limiting, request validation, and logging in one place rather than implementing these in every service. Popular gateways include Kong, Amazon API Gateway, Azure API Management, and Apigee. A gateway lets you enforce security policies consistently across hundreds of endpoints without modifying each service's code.
OAuth 2.0 provides a framework for delegated authorization. Instead of sharing your password with third-party apps, OAuth lets you grant specific permissions through tokens. When you "Sign in with Google" on a website, that's OAuth 2.0. The website receives a token allowing limited access to your Google profile without ever seeing your password. OAuth 2.0 includes several flows (authorization code, client credentials, implicit) for different scenarios.
API keys work well for server-to-server communication and developer access. Generate unique keys for each client or integration, store them securely (never in code), and rotate them periodically. Include metadata with each key—creation date, last used, and associated permissions—so you can audit and revoke access quickly.
JWT tokens combine authentication and authorization in a single, self-contained token. After logging in, the client receives a JWT containing their user ID, roles, and expiration time. Each subsequent request includes this token. Your server validates the signature without database queries, making JWTs ideal for microservices and distributed systems. The trade-off? You can't instantly revoke a JWT—it remains valid until expiration.
Input validation and sanitization prevent injection attacks. Validate every parameter: type, length, format, and allowed values. An endpoint expecting an integer user ID should reject strings, negative numbers, or values exceeding reasonable limits. Use allowlists (accept only known-good inputs) rather than blocklists (reject known-bad inputs), since attackers constantly find new variations.
Web Application Firewalls (WAF) filter malicious requests before they reach your endpoints. They detect common attack patterns—SQL injection attempts, cross-site scripting, and known exploits—and block them automatically. Cloud WAFs from Cloudflare, AWS, and Azure provide protection without infrastructure management.
Rate Limiting and Throttling
Rate limiting controls how many requests a client can make within a time window. Without it, attackers can brute-force passwords, scrape data, or overwhelm your infrastructure.
Implement multiple rate limit tiers. A global limit might allow 10,000 requests per hour per IP address. Authentication endpoints might have stricter limits: 5 login attempts per minute. Expensive operations like report generation might allow only 10 requests per hour.
Token bucket and leaky bucket algorithms provide smooth rate limiting. Token bucket allows brief bursts—if you haven't used your allocation, you can make several rapid requests. Leaky bucket processes requests at a constant rate, queuing extras. Choose based on your use case: token bucket for human-driven traffic with natural bursts, leaky bucket for steady background processing.
Return clear rate limit information in response headers:
X-RateLimit-Limit: 1000
X-RateLimit-Remaining: 437
X-RateLimit-Reset: 1735689600This lets clients manage their request rate proactively instead of hitting limits and failing.
Throttling temporarily slows down requests rather than blocking them entirely. When a client exceeds limits, you might add a delay before processing their requests rather than returning errors. This maintains service availability while discouraging abuse.
API Monitoring and Logging
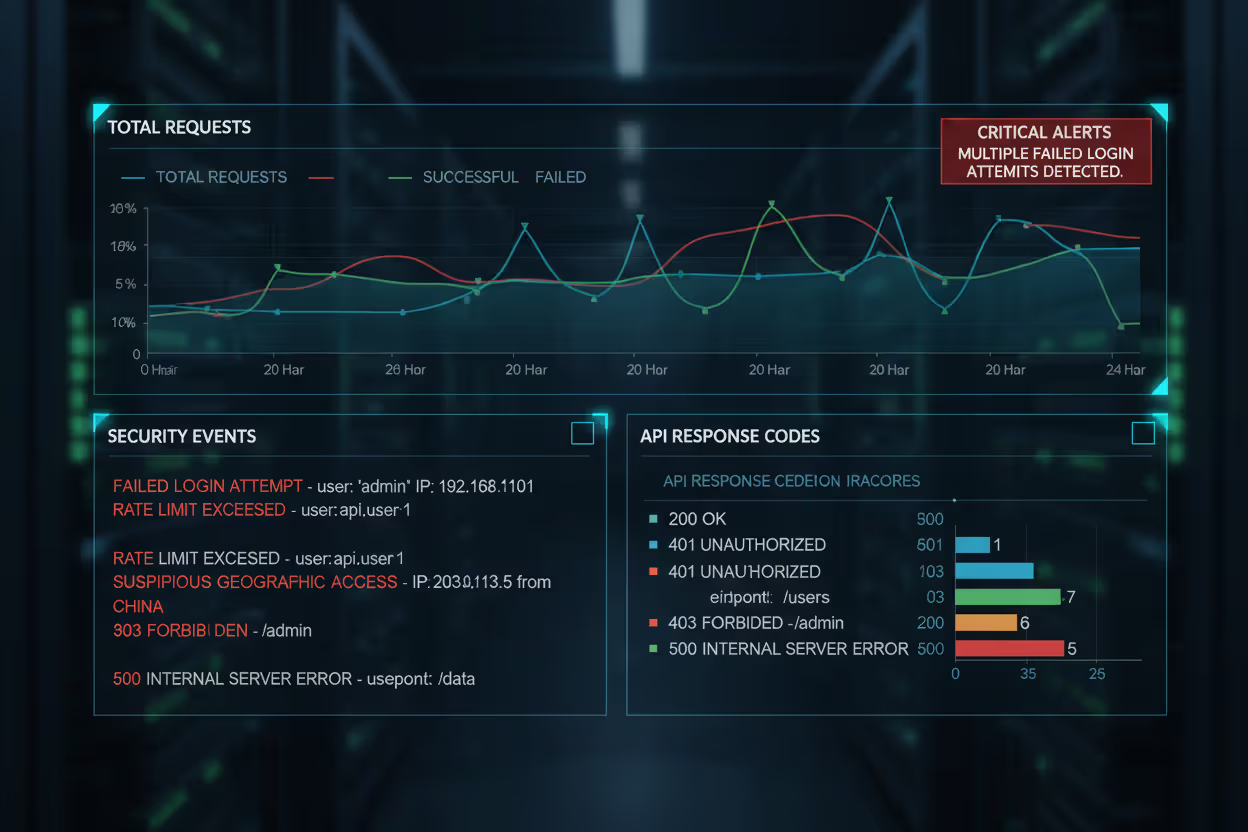
You can't secure what you can't see. Comprehensive monitoring and logging reveal attacks in progress, identify vulnerable endpoints, and provide evidence for incident response.
Log every request: timestamp, client IP, authentication status, endpoint accessed, HTTP method, response code, and response time. For failed authentication attempts, log the username tried (but never passwords). For authorization failures, log which resource was requested and why access was denied.
Monitor for suspicious patterns: repeated failed login attempts from one IP, unusual traffic spikes, requests for non-existent endpoints (scanning for vulnerabilities), access to sensitive endpoints outside business hours, and requests from unexpected geographic locations.
Set up alerts for critical events: successful authentication after multiple failures (potential breach), database connection errors (possible injection attack), sudden increase in 500 errors (system compromise or DoS), and disabled security features or modified configurations.
Security Information and Event Management (SIEM) systems aggregate logs from multiple sources, correlate events, and identify complex attack patterns. Tools like Splunk, ELK Stack (Elasticsearch, Logstash, Kibana), and cloud-native solutions help you spot threats across your entire API ecosystem.
Store logs securely and retain them long enough for forensic analysis. Regulations like GDPR and CCPA affect what you can log and how long you keep it, but security events typically warrant extended retention.
Author: Marcus Halbrook;
Source: williamalmonte.net
API Endpoint Security Implementation Examples
Theory matters, but implementation determines whether your endpoints are actually secure. Here are practical api endpoint security examples for common scenarios.
REST API security setup for a typical web application:
# Example: Securing a user profile endpoint GET /api/v1/users/{userId}/profile
Headers: Authorization: Bearer eyJhbGciOiJIUzI1NiIs... X-API-Key: ak_live_9x8f3j2k1m4n5p6q Security layers:
1. TLS 1.3 encryption (HTTPS)
2. API key validates the client application
3. Bearer token authenticates the user
4. Authorization check: token userId matches path userId
5. Rate limit: 100 requests/minute per user
6. Input validation: userId must be integer, 1-999999999
7. Response filtering: exclude sensitive fieldsThis endpoint requires both an API key (identifying the application) and a user token (identifying the person). The authorization logic verifies the authenticated user is requesting their own profile, not someone else's. Even if an attacker steals a valid token, rate limiting prevents bulk data scraping.
GraphQL endpoint protection requires different considerations. GraphQL's flexibility—letting clients request exactly what they need—also enables expensive queries that fetch deeply nested data:
# Vulnerable query
query { users { posts { comments { author { posts { comments { # Infinite depth possible } } } } } }
} # Security measures:
- Query depth limiting (max 5 levels)
- Query complexity scoring (assign cost to each field)
- Timeout enforcement (5 seconds max)
- Persistent query allowlist (only pre-approved queries)
- Field-level authorization (hide sensitive fields)
One e-commerce company in 2025 suffered an outage when attackers sent deeply nested GraphQL queries that overwhelmed their database. They implemented query complexity analysis, assigning each field a cost and rejecting queries exceeding a threshold.
Webhook security protects endpoints that receive data from external services. When Stripe sends payment notifications or GitHub posts repository events, you need to verify those requests are genuine:
# Webhook endpoint security POST /webhooks/payment-received
Headers: X-Webhook-Signature: sha256=5d41402abc4b2a76b9719d911017c592 Security implementation:
1. Signature verification using shared secret
2. Timestamp validation (reject old requests)
3. Idempotency (handle duplicate deliveries)
4. IP allowlist (only accept from known sources)
5. Separate authentication (webhook-specific credentials) # Signature verification pseudocode
received_signature = request.headers['X-Webhook-Signature']
payload = request.body
expected_signature = hmac_sha256(shared_secret, payload) if received_signature != expected_signature: return 401 Unauthorized
Webhooks can't use standard authentication since you're not initiating the request. Signature verification proves the sender knows a shared secret without transmitting it. Always validate timestamps to prevent replay attacks where someone captures and resends old webhook payloads.
Microservices internal API security matters even when endpoints aren't public. One compromised service shouldn't grant access to your entire system:
# Service-to-service authentication Service A calls Service B:
1. Mutual TLS (both services verify certificates)
2. Service mesh (Istio, Linkerd) handles authentication
3. JWT with service identity
4. Network segmentation (services can't directly access databases)
5. Zero-trust architecture (authenticate every request)
Many breaches exploit "soft centers"—strong perimeter security but weak internal controls. Once attackers compromise one service, they move laterally through the network. Treat internal APIs with the same security rigor as public ones.
API Endpoint Security Mistakes to Avoid
Expert perspective on layered security:
The most common mistake organizations make is relying on a single security control. Authentication alone doesn't protect you if authorization is broken. HTTPS doesn't help if you're logging credentials in plain text. Effective API security requires defense in depth—multiple overlapping controls so that when one fails, others still protect you. We're seeing attackers increasingly target the gaps between security layers rather than attacking the layers themselves
— Sarah Chen
Even experienced teams make preventable mistakes that compromise endpoint security. Here are the most common pitfalls and how to avoid them.
Hardcoded credentials appear in code more often than you'd expect. Developers write api_key = "sk_live_abc123" during testing and forget to remove it. Those credentials end up in version control, public repositories, and compiled binaries. Use environment variables, secret management services (AWS Secrets Manager, HashiCorp Vault, Azure Key Vault), and automated scanning to detect secrets in code.
Lack of HTTPS still occurs, especially for internal APIs or development environments. The reasoning goes: "It's only internal traffic" or "We'll add HTTPS later." Later never comes, or the API gets exposed accidentally. Certificate management is easier than ever with Let's Encrypt and cloud provider tools. There's no excuse for HTTP in 2026.
Missing rate limits on authentication endpoints enable brute-force attacks. An attacker can try thousands of passwords per second without rate limiting. Even a simple limit—5 attempts per minute per IP—stops most automated attacks. Implement progressive delays: after 3 failures, wait 5 seconds; after 5 failures, wait 60 seconds.
Verbose error messages help developers debug but also help attackers. An endpoint returning "Invalid password for user admin@company.com" confirms that email exists and the password was wrong. Return generic messages to clients: "Invalid credentials." Log detailed errors internally for debugging.
No logging or monitoring means you won't notice breaches until customers complain. One API served malware for three months before someone reported it. The company had no logs showing when the compromise occurred or which endpoints were affected. Implement logging from day one, not after an incident.
Outdated dependencies contain known vulnerabilities. The Log4j vulnerability in late 2021 affected millions of systems. Automated dependency scanning (Dependabot, Snyk, OWASP Dependency-Check) alerts you to vulnerable libraries. Update regularly and test thoroughly.
Ignoring the principle of least privilege grants excessive permissions. A service that reads user profiles doesn't need database write access. An API key for mobile apps doesn't need admin privileges. When something goes wrong—a compromised key or buggy code—limited permissions contain the damage.
Accepting any content type enables attacks. If your endpoint expects JSON but also processes XML, attackers might exploit XML External Entity (XXE) vulnerabilities. Explicitly validate content type headers and reject unexpected formats.
Trusting client-side validation alone leaves you vulnerable. JavaScript validation improves user experience but doesn't secure your endpoint. Attackers bypass client-side checks easily. Always validate and sanitize on the server.
Exposing internal identifiers leaks information about your system. Auto-incrementing database IDs reveal how many records you have and enable enumeration attacks. Use UUIDs or random strings for public-facing identifiers.
Comparison of API Authentication Methods
Different authentication methods suit different scenarios. Choose based on your security requirements, client types, and operational constraints.
| Method | Security Level | Use Case | Pros | Cons |
| API Keys | Low-Medium | Server-to-server, developer access, low-risk operations | Simple to implement; easy to generate and revoke; good for identifying applications | No user context; if leaked, valid until revoked; often accidentally exposed; limited authorization granularity |
| OAuth 2.0 | High | Third-party integrations, delegated access, user-authorized actions | Industry standard; separates authentication from authorization; supports granular scopes; token refresh capability | Complex to implement correctly; multiple flows to understand; requires secure token storage; overhead for simple use cases |
| JWT Tokens | Medium-High | Microservices, mobile apps, distributed systems, stateless authentication | Self-contained (no database lookup); efficient for distributed systems; includes claims for authorization; standardized format | Cannot revoke before expiration; payload size increases request overhead; requires secure secret management; vulnerable if algorithm set to "none" |
This quote emphasizes why api endpoint security guide recommendations always include multiple techniques. No single method provides complete protection.
Frequently Asked Questions About API Endpoint Security
API endpoint security isn't optional anymore. Every breach makes headlines, regulations impose penalties, and customers expect their data protected. The good news? Most attacks exploit basic mistakes—missing authentication, lack of HTTPS, poor authorization—that are straightforward to fix.
Start with fundamentals: require authentication on every endpoint, use HTTPS everywhere, implement rate limiting, validate all inputs, and log security events. Build from there with OAuth 2.0 for third-party access, API gateways for centralized control, and monitoring for threat detection.
Security isn't a one-time project. New vulnerabilities emerge, attack techniques evolve, and your API changes. Regular security reviews, dependency updates, and penetration testing keep your defenses current. The investment in proper API endpoint security pays dividends in prevented breaches, maintained customer trust, and avoided regulatory penalties.
Your endpoints are the front door to your data. Lock them properly.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.