Team discussing cloud data security in a modern office
SOC 2 Cybersecurity Guide
Content
Content
Companies storing customer information in the cloud have a problem. Their prospects keep asking the same question during sales calls: "How do we know our data is actually safe with you?" Marketing decks with security buzzwords won't cut it anymore. Enterprise buyers want proof—the kind that comes from independent third-party audits.
That's exactly what SOC 2 delivers. It gives you a way to show (not just tell) customers that you've built solid security controls around their data. And unlike rigid compliance checklists, this framework lets you adapt controls to match how your business actually operates.
What Is SOC 2 Cybersecurity
The American Institute of Certified Public Accountants created this auditing standard to solve a specific problem: service companies needed a consistent way to prove they protect customer information. Think of it as a structured examination where independent CPAs verify that your security controls actually work.
Here's something that trips people up constantly—SOC 2 isn't something you "get certified" in. There's no certificate, no badge, no pass-or-fail grade. Instead, you receive an audit report that documents your controls in detail. Customers read that report and decide for themselves whether your security measures meet their standards.
The whole thing revolves around five trust principles called Trust Services Criteria. You've got Security (which everyone must include), plus Availability, Processing Integrity, Confidentiality, and Privacy. Companies pick whichever criteria match their business model. A video streaming service might choose Security and Availability since uptime matters most. A medical records platform would probably include all five given the sensitivity of health data.
Only service organizations need this—companies that handle data or run systems for other businesses. If you're manufacturing widgets in a factory, SOC 2 doesn't apply. But if you're hosting those widgets in a cloud database for customers? Now we're talking.
Why should you care? Because when you're asking potential customers to trust you with their most sensitive information, "we take security seriously" doesn't convince anyone. An audit report from an independent CPA firm carries actual weight during vendor evaluations.

Author: Ethan Caldwel;
Source: williamalmonte.net
How SOC 2 Cybersecurity Works
Getting audited doesn't start with calling an auditor. You need months of prep work first—building security controls, writing documentation, implementing monitoring systems. Companies with zero existing security infrastructure typically spend 6-12 months getting ready. Organizations that already have decent security practices might prepare in just a few months.
Once you're ready, a CPA firm comes in to examine everything. They'll interview your staff, test whether controls actually function, review logs and records, and generally poke around to verify that your documented procedures match reality. How long this takes depends entirely on which report type you're pursuing.
SOC 2 Type I vs Type II Reports
These two report types confuse people because they sound similar but measure completely different things.
| Report Type | What Gets Examined | How Long Auditors Spend | Who Should Get This | What You'll Pay | How Often to Update |
| Type I | Whether your controls are designed properly (snapshot in time) | 2-4 weeks | Early-stage companies, initial assessments, proving you're ready | $15,000-$50,000 | Optional, though most upgrade to Type II within a year |
| Type II | Whether your controls worked consistently over a period | At least 6 months, usually 12 months | Established businesses, customers who demand proof of sustained compliance | $30,000-$150,000+ | Every year or continuously |
Type I answers: "If we looked at your security controls today, would they theoretically work?" Auditors check that you've documented solid procedures and implemented appropriate technical safeguards. They don't verify whether you actually followed those procedures last month or last year.
Type II digs deeper: "Did your controls function properly over the past 6-12 months?" Auditors examine months of evidence—access review logs, vulnerability scan results, incident response records. They're confirming sustained compliance, not just a snapshot. You can't fake your way through Type II by implementing everything right before the audit.
Most mature companies go straight for Type II because sophisticated buyers recognize that point-in-time assessments prove very little. What stops a company from implementing perfect controls Monday, passing a Type I audit Tuesday, then abandoning everything Wednesday?

Author: Ethan Caldwel;
Source: williamalmonte.net
The SOC 2 Audit Process Step-by-Step
Here's what actually happens from start to finish:
Readiness Assessment (4-8 weeks): You figure out what's missing. Maybe you don't have a formal incident response plan. Perhaps access reviews happen sporadically instead of on a schedule. Maybe nobody's documented your encryption standards. This gap analysis shows exactly what needs fixing before an auditor arrives. Some companies hire consultants for this, others use internal security teams.
Remediation and Implementation (3-12 months): Now you fix everything. Write missing policies. Deploy technical controls. Set up logging systems. Train employees. A startup building from scratch might need a full year. An enterprise with existing security programs might knock this out in three months.
Pre-audit Preparation (4-6 weeks): You gather evidence, organize documentation, select an auditing firm, and define what the audit will cover. Scope matters—you'll specify which systems, processes, and Trust Services Criteria the report addresses.
Fieldwork (2-4 weeks for Type I, 4-8 weeks for Type II): Auditors show up (virtually or in person) and start testing. They'll verify that encryption actually protects data, confirm that access reviews happened as documented, check whether intrusion detection triggers appropriately. They're collecting evidence to support their final report.
Report Issuance (2-3 weeks): The audit firm drafts their report, you review it for factual accuracy, and then they finalize everything. This document becomes what you share with customers and prospects moving forward.
The Five SOC 2 Trust Services Criteria
Each criterion targets specific risks. You prove compliance by implementing controls that achieve that criterion's objectives.
Security shows up in every single SOC 2 audit—it's non-negotiable. This criterion requires safeguards protecting your systems from unauthorized access. We're talking multi-factor authentication on administrative accounts, network segmentation keeping sensitive systems isolated, encryption covering data whether it's moving across networks or sitting in databases, intrusion detection watching for suspicious activity. Here's a real example: "Production database access requires hardware security key authentication through our SSO system. Every access attempt gets logged. Our security team reviews these logs every Monday morning."

Author: Ethan Caldwel;
Source: williamalmonte.net
Availability proves that your systems stay operational according to whatever uptime you've promised customers. Controls address redundancy, disaster recovery, incident management. A hosting company might run three geographically separated data centers with automatic failover. They test disaster recovery procedures every quarter to ensure they actually work. The criterion doesn't demand perfect uptime—it demands that actual availability matches your commitments and that you can recover when things break.
Processing Integrity verifies that your systems handle data correctly—completely, accurately, on time, as authorized. This matters tremendously for financial systems, data pipelines, automated workflows. Controls include input validation stopping bad data from entering systems, reconciliation processes confirming transaction accuracy, error handling that alerts staff when processing fails. Picture an automated invoicing system: controls ensure invoices don't get processed twice, amounts match what was approved, and failed transactions trigger alerts instead of disappearing silently.
Confidentiality focuses specifically on information you've designated as confidential, protecting it from unauthorized disclosure. Different from Security's broader scope, this criterion zeroes in on sensitive data handling. Controls include classification schemes tagging confidential information, access restrictions limiting who sees what, NDAs with staff and contractors, secure deletion procedures for confidential data you no longer need.
Privacy governs how you collect, use, store, share, and delete personal information—and it all has to align with your privacy notice. This criterion tracks with privacy regulations. Controls include consent mechanisms before collecting personal data, processes for handling data subject access requests, retention schedules preventing you from hoarding data indefinitely, vendor agreements ensuring third parties protect personal information properly.
Who Needs SOC 2 Compliance
Certain industries have turned SOC 2 into a de facto requirement. You'll struggle to compete without one if you fall into these categories.
SaaS Companies make up the biggest chunk of organizations pursuing these audits. Doesn't matter whether you're building CRM software, HR platforms, project management tools, or accounting systems—you're handling customer data. Enterprise buyers now routinely request SOC 2 reports during procurement. Many won't even consider vendors who can't produce current reports.

Author: Ethan Caldwel;
Source: williamalmonte.net
Cloud Service Providers offering infrastructure, platforms, or managed hosting face similar pressure. When customers run mission-critical applications on your infrastructure, they need assurance beyond marketing promises. A SOC 2 report delivers that third-party validation.
Data Centers and Colocation Facilities housing customer equipment must demonstrate physical and environmental controls. These organizations typically focus on Security and Availability—proving things like biometric access controls, environmental monitoring, redundant power and cooling, round-the-clock security monitoring.
Healthcare Technology Companies building EHR systems, telemedicine platforms, or health information exchanges deal with protected health information. HIPAA compliance is legally mandatory, but many also get SOC 2 reports to show comprehensive controls exceeding HIPAA's baseline requirements.
Financial Technology Firms handling payments, managing investments, or providing banking services get intense scrutiny. SOC 2 reports supplement PCI DSS compliance and regulatory requirements, giving financial institution partners and customers extra assurance.
Startup founders always ask: when's the right time to pursue this? That depends on your sales pipeline. If you're consistently losing enterprise deals because prospects request SOC 2 reports and you can't provide them, it's time. If you're selling to small businesses with minimal security requirements, you can probably wait until you've found product-market fit. General rule: consider SOC 2 when it's blocking revenue or when a major customer makes it contractually mandatory.
SOC 2 Cybersecurity Implementation Examples
Abstract frameworks make more sense with concrete scenarios showing real implementation.
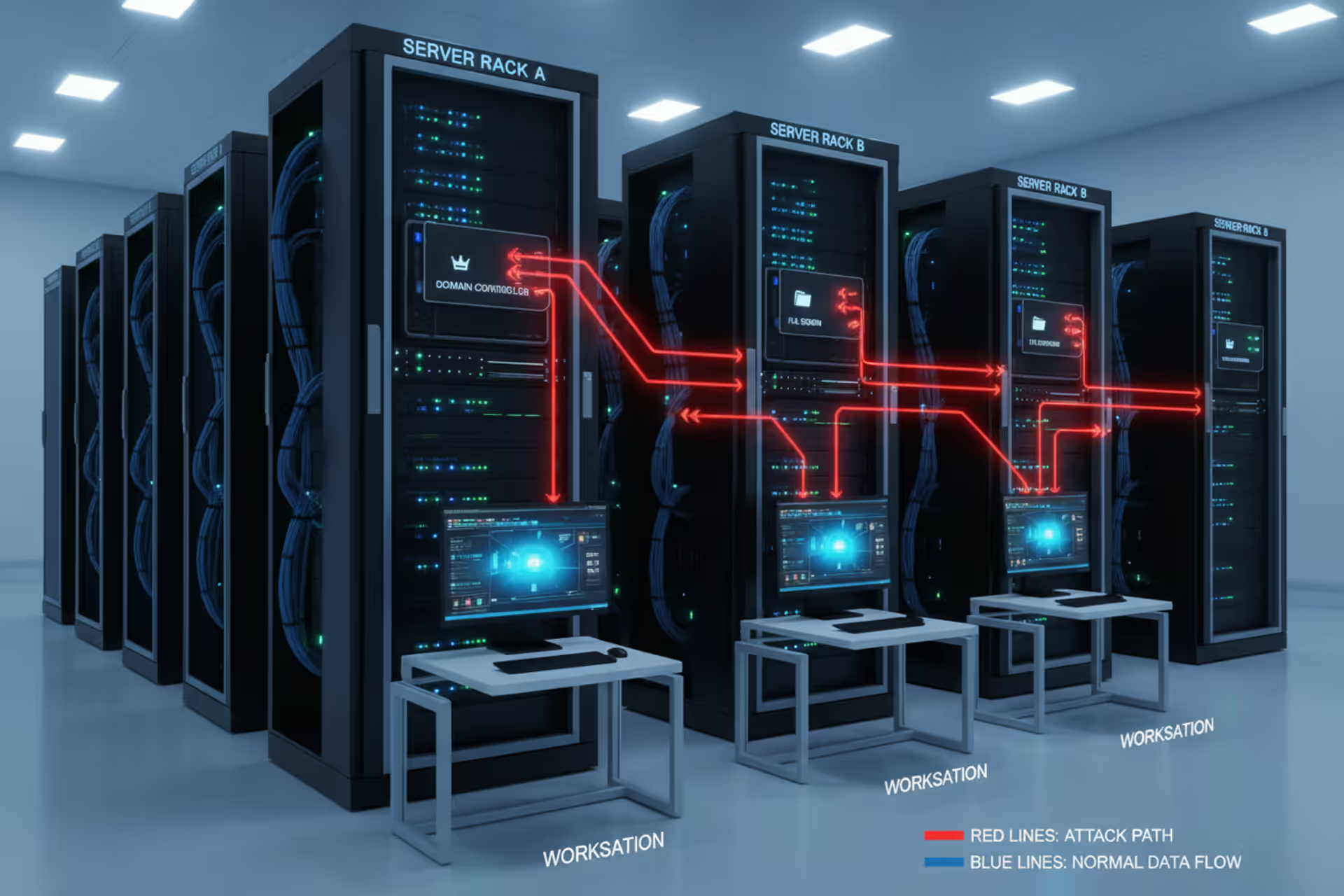
SaaS Company Access Controls: A project management platform with 50 employees needed role-based access control for their Security criterion. Developers got staging environment access but couldn't touch production. Support staff could view customer data but couldn't modify system configurations. Database administrators needed CTO approval for schema changes—tracked through a ticketing system auditors later examined. They implemented SSO with multi-factor authentication so compromised passwords alone couldn't grant system access. Managers reviewed team permissions quarterly, confirming everyone still needed their current access levels.
Cloud Storage Provider Availability: A file hosting service promised 99.9% uptime in customer contracts, making Availability critical. They built redundant storage spanning three geographically separated data centers with automated replication keeping files in multiple locations. When one data center lost power, traffic automatically rerouted to the others—customers never noticed. They ran disaster recovery drills quarterly, simulating complete data center failures to verify recovery procedures worked as documented. Monitoring tracked uptime constantly, with monthly reports comparing actual versus promised availability.
Healthcare Platform Confidentiality: A telemedicine platform handling patient consultations tackled Confidentiality by classifying and protecting data appropriately. Patient health information got tagged as confidential, with access restricted to authorized medical staff and the specific patient. Video consultations used end-to-end encryption—even the company couldn't view session content. Audit logs tracked every patient record access, with anomaly detection flagging weird patterns like a provider accessing hundreds of records rapidly. When employees departed, access got revoked within an hour and all devices were remotely wiped.
Controls appearing across most implementations include: AES-256 encryption for stored data and TLS 1.2+ for data in transit, multi-factor authentication required for admin access and optionally for users, centralized logging capturing security events with retention matching audit requirements, incident response procedures defining detection and response processes, vendor management ensuring third-party providers implement appropriate controls.
Common SOC 2 Compliance Mistakes to Avoid
First-time organizations stumble over predictable obstacles. Learn from their mistakes to move faster and spend less.
Treating SOC 2 as a One-Time Project: Some companies view this as checkbox compliance—implement controls, pass the audit, go back to business as usual. This fails spectacularly with Type II reports or renewals. Controls must operate continuously. Auditors reviewing 12 months will notice if access reviews stopped after month three or vulnerability scanning paused for half the year. Build controls into standard operations instead of creating audit theater.
Inadequate Documentation: Auditors require evidence. Verbal explanations don't work—you need policies, procedures, screenshots, logs, records. Common failure: organizations implement strong technical controls but can't prove it during audits because they didn't document configurations or retain logs. Start documentation early and ensure systems generate required evidence.
Scope Creep: Sometimes companies define audit scope too broadly, including irrelevant systems or processes. This increases costs and complexity without adding value. Conversely, too-narrow scope might exclude critical systems, reducing report usefulness. Work with your auditor to define scope covering systems that handle customer data while excluding internal-only systems not affecting service delivery.
Choosing the Wrong Report Type: Startups sometimes pursue expensive Type II reports when Type I would satisfy current customers, wasting resources. Others choose Type I when major prospects demand Type II, forcing a second audit within months. Assess customer requirements before selecting report types. Remember that Type II requires minimum six months of control operation before fieldwork begins.
Neglecting Employee Training: Perfect technical controls fail if employees don't understand their security role. Staff need training on policies, procedures, and specific responsibilities. Auditors interview employees during fieldwork—inconsistent answers or confusion about procedures raises red flags. Regular training ensures everyone understands not just what controls exist, but why they matter.
Poor Vendor Management: Organizations overlook that third-party vendors impact SOC 2 compliance. If you use cloud infrastructure providers, email services, or payment processors, their security controls affect your environment. SOC 2 requires vendor security assessment—often by reviewing their SOC 2 reports—and contracts including appropriate security requirements. Failing to manage vendor risk creates control environment gaps.

Author: Ethan Caldwel;
Source: williamalmonte.net
SOC 2 vs Other Security Frameworks
Multiple security frameworks exist, each serving different purposes. Understanding when to pursue SOC 2 versus alternatives helps allocate resources effectively.
SOC 2 vs ISO 27001: Both address information security management but differ significantly. ISO 27001 is an international standard with prescriptive control requirements. Organizations receive certification after proving compliance—that certification carries global recognition. SOC 2, built for US markets, offers control selection flexibility but provides reports rather than certificates. ISO 27001 suits organizations serving international markets or preferring structured frameworks. SOC 2 better serves US-based service organizations whose customers want detailed audit reports. Many enterprises pursue both—ISO 27001 for international credibility, SOC 2 for US customer assurance.
SOC 2 vs HIPAA: HIPAA is legally mandatory for covered entities and business associates handling protected health information. SOC 2 is voluntary. HIPAA defines minimum security and privacy requirements that organizations must meet to avoid penalties. SOC 2 demonstrates comprehensive controls often exceeding HIPAA minimums. Healthcare organizations typically need HIPAA compliance and may add SOC 2 to differentiate themselves or satisfy customers wanting assurance beyond regulatory requirements.
SOC 2 vs PCI DSS: The Payment Card Industry standard applies specifically to organizations touching credit card data—processing, storing, or transmitting it. Like HIPAA, it's effectively mandatory for anyone handling payment cards. PCI DSS provides granular technical requirements focused narrowly on payment data. SOC 2 addresses broader operational security. Payment processors and fintech companies often maintain both—PCI DSS satisfies card brand requirements while SOC 2 addresses broader customer security concerns.
SOC 2 vs FedRAMP: The Federal Risk and Authorization Management Program is mandatory for cloud providers serving federal agencies. It's dramatically more rigorous and expensive than SOC 2, with detailed technical requirements and continuous monitoring obligations. Organizations serving government need FedRAMP. Those serving commercial customers typically choose SOC 2. Some companies pursue both—SOC 2 for commercial customers, FedRAMP for government contracts.
Many organizations maintain multiple frameworks simultaneously. A healthcare SaaS company might pursue HIPAA (legally required), SOC 2 (customer expectation), and ISO 27001 (international credibility). While this requires investment, frameworks overlap significantly. Implementing multi-factor authentication satisfies requirements across all frameworks—you're not completely duplicating effort, just documenting and auditing the same controls through different lenses.
SOC 2 reports have become the common language of trust in the service provider ecosystem. They transform abstract security promises into concrete, audited evidence that customers can evaluate and compare. Organizations that view SOC 2 as merely checking a compliance box miss the real value—it's an opportunity to build a security program that actually protects your business and your customers
— Melissa Bischoping
Frequently Asked Questions About SOC 2 Cybersecurity
SOC 2 has shifted from competitive differentiator to baseline expectation for service organizations handling customer data. The framework provides structured methodology for implementing, documenting, and verifying security controls protecting sensitive information and ensuring service reliability.
The investment—both financial and operational—can seem intimidating, particularly for smaller organizations. Yet the alternative often proves costlier: lost sales opportunities, customer hesitation, security incidents that proper SOC 2 controls might have prevented. The framework forces systematic security approaches rather than reactive firefighting, building resilience extending beyond audit requirements.
Success requires treating SOC 2 as continuous program rather than point-in-time project. Controls must embed into daily operations with regular monitoring, testing, improvement. Documentation needs ongoing maintenance. Staff require periodic training maintaining awareness and compliance.
Organizations beginning SOC 2 journeys should start with honest capability assessment, realistic timelines, clear understanding of customer requirements. Engage experienced auditors early for scope and approach guidance. Invest in tools and processes serving you beyond initial audit. Most importantly, build culture where security and compliance aren't burdens imposed by auditors but fundamental operational aspects.
The path demands effort, but the destination—verified security programs protecting customer data and building market trust—justifies the journey.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.