Healthcare data security in a medical office
HIPAA Cybersecurity Compliance Guide
Medical records, insurance claims, treatment histories, psychiatric evaluations—healthcare providers manage information that patients would never want exposed. Federal law recognizes this sensitivity. The Health Insurance Portability and Accountability Act mandates specific protections, and violating these rules carries serious consequences: hefty fines, legal liability, and devastating reputation damage.
HIPAA cybersecurity compliance represents how healthcare organizations actually secure electronic patient data against hackers, insider threats, and accidental breaches. It's the difference between storing patient files on password-protected encrypted servers versus leaving them accessible to anyone with internet access.
Smaller practices often struggle here. You're treating patients all day—when are you supposed to become a cybersecurity expert? This guide translates complex regulations into steps you can actually take, whether you're running a two-person clinic or managing IT for a hospital network.
What Is HIPAA Cybersecurity Compliance?
Think of HIPAA as having two main components. The Security Rule tells you how to lock down electronic patient information. The Privacy Rule covers who gets to see it and when. Different purposes, but they work hand-in-hand.
The Security Rule became enforceable in 2003 through the Department of Health and Human Services, specifically their Office for Civil Rights (OCR). It sets mandatory standards for protecting what regulators call ePHI—electronic protected health information. That's any patient data stored or transmitted digitally: EHR systems, email communications, billing databases, appointment scheduling software, and even text messages about patients.

Author: Ethan Caldwel;
Source: williamalmonte.net
Here's what confuses people: these rules target two distinct groups.
Covered entities operate in healthcare directly. Your primary care doctor's office? Covered entity. The insurance company processing your claims? Covered entity. This category includes any health plan, healthcare clearinghouse, or medical provider transmitting patient data electronically. Most hospitals, clinics, pharmacies, therapists, chiropractors, and insurance carriers fall here.
Business associates work behind the scenes. They're vendors and contractors who touch ePHI while providing services to covered entities. Medical billing services that process your claims, cloud companies storing your patient database, transcription companies converting your voice notes to text, IT consultants maintaining your servers, even shredding companies destroying old hard drives—all business associates. Since 2013, they face direct legal liability for security failures, not just the covered entities hiring them.
The stakes keep rising. In 2023 alone, healthcare breaches compromised over 133 million patient records. Ransomware gangs specifically target medical practices because they know hospitals can't function without access to patient data—they'll pay to get it back. Small dental offices, oncology centers, and mental health practices have all been hit. Nobody's too small to attack.
Core Requirements of HIPAA Cybersecurity Compliance
The Security Rule divides requirements into three buckets: administrative, physical, and technical. Within each bucket, you'll find "required" items (non-negotiable, implement them) and "addressable" items (implement them OR document why you chose an alternative approach).
Here's where organizations mess up constantly: addressable doesn't mean optional. It means flexible. Can't afford enterprise-grade encryption? Fine—explain why in writing and describe your alternative protection method. Just skipping it? That's a violation.
Administrative Safeguards
Your policies, procedures, and management processes live here. This is governance stuff—how you run your security program.
Security Management Process (Required): Run risk assessments regularly to spot weaknesses. Maybe your server room door doesn't lock. Maybe staff share passwords. Find these issues, fix them, and document what you did. You also need policies punishing employees who violate security rules and systems to review who's accessing what.
Security Officer (Required): One specific person owns security responsibility. In a solo practice, that's probably you. In a hospital, it's a dedicated role. Either way, someone's name goes on this job.
Workforce Security (Required): Control who gets system access from day one. New hire orientation should include account creation with appropriate permissions. Employee leaving? Terminate their access that same day—preferably before they know they're fired. Track all these authorization changes.
Information Access Management (Required): Your receptionist doesn't need to read psychiatric evaluations. Your billing clerk doesn't need full medical histories—just diagnosis codes and procedures. Limit access to what each role actually requires. This concept, called "least privilege," dramatically reduces breach risk.
Security Awareness and Training (Required): Everyone handling patient data needs training. Not just doctors and nurses—administrative staff, cleaning crews accessing computer areas, everyone. Cover password management, recognizing phishing emails, spotting suspicious USB drives left in the parking lot, and reporting weird system behavior. Run refresher sessions annually at minimum.
Incident Response (Required): When (not if) something goes wrong, your team needs a playbook. Employee laptop stolen from their car? Follow step one, two, three. Suspicious email attachment opened? Here's the response protocol. Without documented procedures, people freeze or make reactive decisions that worsen the situation.
Contingency Planning (Required): Ransomware encrypts your entire patient database tomorrow morning. What now? Can you restore from backups? How quickly? Can you operate manually while systems recover? Document your backup strategy, disaster recovery steps, and emergency operation procedures. Then test them—an untested plan fails when you need it most.
Business Associate Contracts (Required): Every vendor touching ePHI signs a Business Associate Agreement before accessing anything. These contracts specify exactly how they'll protect data, how quickly they'll report breaches, and what happens if they violate the rules. No signed BAA? They don't get access. Period.

Author: Ethan Caldwel;
Source: williamalmonte.net
Physical Safeguards
Cybersecurity isn't purely digital. Physical access to servers, workstations, and storage media matters enormously.
Facility Access Controls (Required): Who can walk into your server room? Does your building have badge readers, security cameras, or at least locked doors to sensitive areas? Visitor logs help too. One clinic I worked with kept their server in an unlocked supply closet—anyone grabbing printer paper could access it.
Workstation Use (Required): Define where and how employees can view ePHI. Can nurses carry tablets into the public cafeteria where anyone can see the screen? Should billing staff work from coffee shops on public WiFi? Set clear boundaries.
Workstation Security (Required): Stop shoulder-surfing by positioning monitors away from hallways and waiting rooms. Use privacy screen filters that black out the display from side angles. Enable automatic screen locks after a few minutes of inactivity. These simple steps prevent casual snooping.
Device and Media Controls (Required): Upgrading computers? You can't just trash the old hard drives. Patient data persists even after deleting files—you need specialized wiping software or physical destruction. Maintain backup tapes securely. Track which devices contain ePHI and where they go. When equipment moves or gets disposed of, document it.
Technical Safeguards
Now we're into the technology itself—the systems and software protecting ePHI.
Access Control (Required): Every user gets unique login credentials. Shared passwords are prohibited—you can't track who did what if three people use "FrontDesk123." Implement automatic logoff when workstations sit idle (15 minutes is common). Set up emergency access procedures for urgent patient situations. Encryption for ePHI is technically addressable, but good luck justifying why you skipped it in 2024.
Audit Controls (Required): Your systems should log who accessed which patient records when. Dr. Smith viewed Jane Doe's chart at 2:47 PM from workstation 5. These audit trails help detect unauthorized snooping—like the famous cases where hospital employees looked up celebrity patient records. Review logs regularly, not just after suspected breaches.
Integrity Controls (Addressable): How do you know patient data hasn't been tampered with? Digital signatures, checksums, and version control systems verify records haven't been altered improperly. If someone changes a medication dosage in the system, you need evidence of who made that change and when.
Transmission Security (Addressable): When ePHI travels across networks—between offices, to business associates, from home workers to office servers—protect it. Encryption again. Virtual private networks (VPNs). Secure file transfer protocols. Otherwise, data crosses the internet in plain text, readable by anyone intercepting it.

Author: Ethan Caldwel;
Source: williamalmonte.net
How HIPAA Cybersecurity Compliance Works in Practice
Reading regulations is one thing. Actually implementing them in your practice requires a structured approach.
Step 1: Conduct a comprehensive risk assessment. Map where ePHI lives in your organization. Desktop computers, obviously. But also: mobile devices, backup tapes sitting in a storage unit, cloud servers, USB drives in someone's desk drawer, paper files waiting to be scanned, fax machine memory, copier hard drives. List every location.
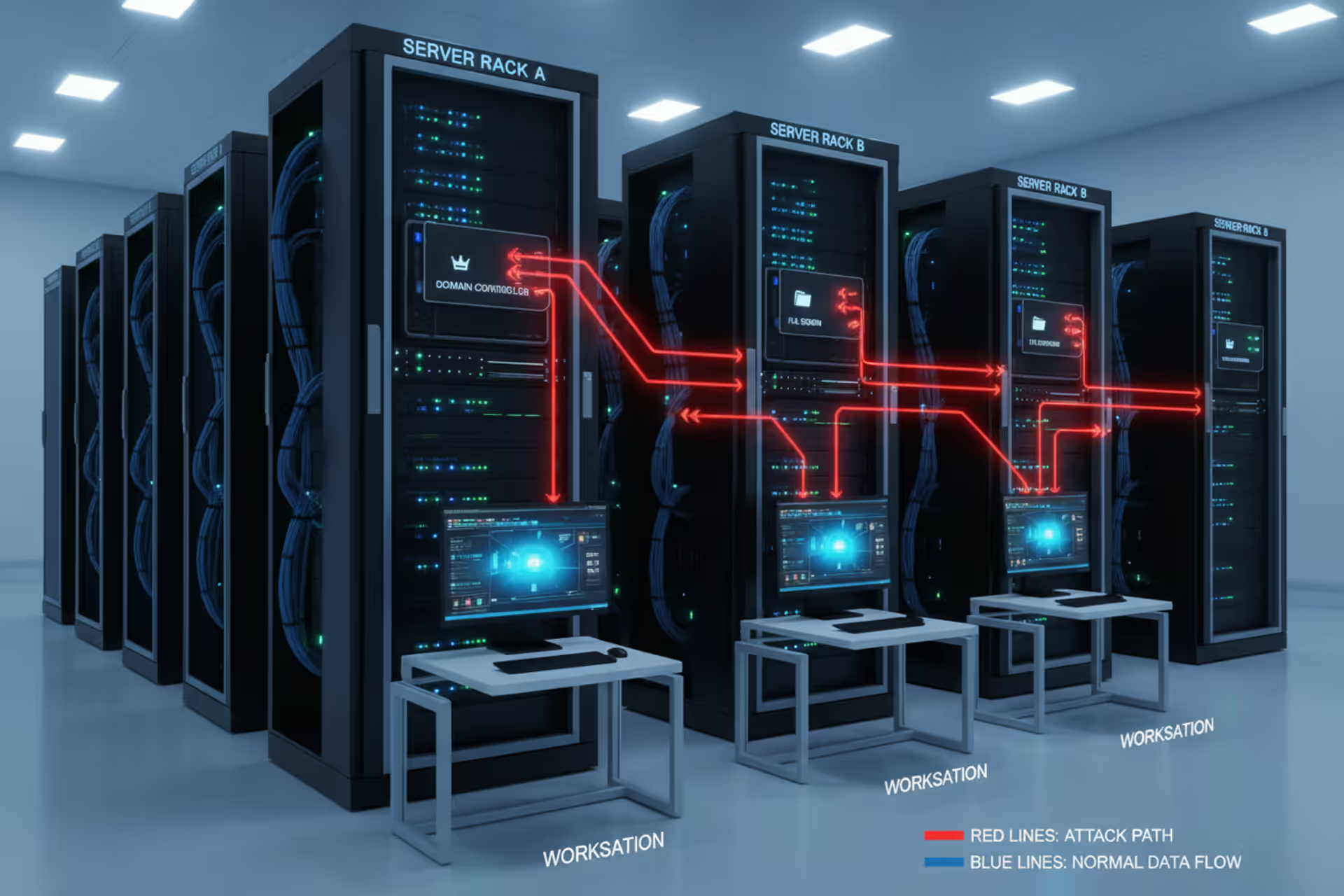
Next, identify realistic threats. Ransomware attacks targeting healthcare have exploded—that's a high-likelihood threat. A disgruntled employee copying patient files to sell? Less common but possible. Building fire destroying servers? Low probability but catastrophic impact. Weak passwords getting cracked? Happens constantly.
Now match threats against vulnerabilities. Your unencrypted laptops (vulnerability) meet the laptop-stolen-from-car threat. Your lack of offsite backups (vulnerability) meets the ransomware threat. Calculate likelihood and impact for each combination. This analysis drives your security decisions.
Step 2: Develop written policies and procedures. Based on those identified risks, create documented rules. Password requirements: minimum 12 characters, mix of uppercase, lowercase, numbers, symbols, changed every 90 days. Acceptable use policy: no storing ePHI on personal devices, no accessing patient data without business need, no sharing logins. Incident response: if you suspect a breach, notify the security officer within 2 hours, preserve evidence, don't delete anything.
Small practices need simpler policies than hospital systems, but everyone needs something in writing. Templates help, but customize them—generic copy-paste policies don't reflect your actual environment.
Step 3: Implement technical and physical controls. Now the hands-on work. Install and configure firewalls. Enable full-disk encryption on all devices. Deploy antivirus software with automatic updates. Set up multi-factor authentication (password plus phone code or biometric). Install physical locks on server room doors. Position cameras monitoring access points. Configure automatic security patches.
This step costs money. Budget for it. Licenses, hardware, maybe contractor help if you lack IT staff. Consider this insurance—spending $5,000 now beats a $50,000 breach notification and settlement later.
Step 4: Train your workforce. Schedule training sessions for all staff. Use real examples: "Last month, a clinic in Ohio clicked a fake Microsoft password reset email. Ransomware encrypted their entire database. Here's how to spot these scams..." Phishing simulations work well—send fake malicious emails and see who clicks. Those who fail get immediate remediation training.
Document everything. Attendance sheets, signed acknowledgments, quiz scores. When OCR audits you, training records demonstrate compliance.
Step 5: Execute business associate agreements. Before your EHR vendor, billing service, email host, or cloud backup provider touches ePHI, get a signed BAA. These contracts are non-negotiable. Vendors refusing to sign BAAs can't access your data—find different vendors.
Maintain a spreadsheet tracking all business associates, agreement dates, renewal schedules, and service descriptions. When associates change their data handling practices, agreements may need updates.
Step 6: Monitor and audit continuously. Schedule weekly or monthly audit log reviews. Look for patterns: after-hours access, employees viewing records of patients they're not treating, unusually high volumes of record access. Run quarterly access reviews—do former employees still have active accounts? Do current employees have more access than their jobs require?
Test your backups by actually restoring data. Many organizations discover their backups don't work during emergencies. Monthly restoration tests catch these failures early.
Step 7: Document everything. Create a compliance binder (physical or digital) containing: risk assessment reports with dates, all policy versions with approval dates, training rosters and materials, security incident reports and resolutions, business associate agreement copies, audit log review summaries, backup test results.
This documentation proves your compliance efforts during audits. No documentation equals no proof you did anything.
Step 8: Review and update regularly. Set annual calendar reminders for comprehensive risk assessment updates. When you adopt new technology (switching EHR systems, adding telehealth capabilities), conduct interim assessments. Update policies to address new workflows. Retrain staff when rules change.
Threats evolve constantly. Last year's security measures may not address this year's attacks. Continuous improvement isn't optional—it's how you stay ahead of criminals.

Author: Ethan Caldwel;
Source: williamalmonte.net
Common HIPAA Cybersecurity Compliance Examples
Abstract requirements make more sense with concrete scenarios showing how practices actually implement them.
Encryption implementation: Mountain View Physical Therapy sends therapists to patients' homes carrying tablets with treatment plans and progress notes. They enabled BitLocker encryption on all tablets, knowing devices might get stolen from vehicles. When a tablet did disappear from a therapist's car last fall, the encrypted data remained protected. The practice reported the theft to police but didn't trigger HIPAA breach notification requirements because encryption rendered the ePHI unreadable. They also switched from regular email to a HIPAA-compliant secure messaging platform after nearly sending patient information via unencrypted Gmail.
Role-based access controls: Riverside Medical Associates operates five specialties under one roof—cardiology, dermatology, orthopedics, primary care, and podiatry. Their IT administrator configured their EHR system with granular permission levels. Front desk staff see demographics, insurance information, and appointment calendars—nothing clinical. Medical assistants access charts for only the patients scheduled with their assigned physician that day. Nurses get broader access to clinical notes within their specialty. Billing specialists view diagnosis codes, procedures, and insurance details but can't read clinical narratives or lab results. Even the practice administrator, who has elevated permissions for oversight, must document business justification when accessing individual patient records.
Audit log monitoring: St. Catherine's Hospital employs a security analyst who reviews system logs every Tuesday morning. She runs reports showing unusual access patterns. When the report flagged a respiratory therapist who accessed 73 patient records in 14 minutes—impossible during normal patient care—she investigated. Turned out the therapist was looking up records of neighbors and acquaintances out of curiosity. The hospital terminated employment, reported the breach to affected patients, and implemented additional monitoring for similar patterns. Now the system automatically alerts security when any user accesses more than 20 records in 30 minutes.
Breach notification procedures: Oakwood Dental discovered their office manager's email account was compromised when patients started receiving suspicious messages. Following their incident response playbook, they immediately reset the password and forced a logout on all devices. The IT contractor reviewed email logs to determine what was accessed—appointment confirmations containing patient names and dates, but no clinical information. Since 847 patients were potentially affected (over the 500-person threshold), they notified HHS within 60 days, sent individual notification letters, and posted a notice on their website. They also implemented multi-factor authentication to prevent similar compromises.
Vendor management: Specialty Pharmacy Network vets all software vendors before signing contracts. Their evaluation checklist requires: documentation of the vendor's security practices, willingness to sign a BAA, confirmation that data is encrypted at rest and in transit, evidence of regular security audits, and references from other healthcare clients. When considering a new e-prescribing platform, they rejected the lowest-cost option because the vendor couldn't provide SOC 2 compliance documentation. They paid 30% more for a vendor meeting their security standards—worth it to avoid breach liability.
Remote work security: When Midwest Medical Billing shifted 40 employees to home offices in 2020, they didn't just send people home with laptops. They issued company-owned devices with pre-configured encryption and security software. They required VPN connections for any system access. They implemented two-factor authentication using mobile phone codes. They prohibited downloading or storing ePHI on personal devices. They conducted virtual home office inspections via video calls, verifying employees had private workspaces with lockable doors, weren't working from coffee shops, and used password-protected home WiFi (not the default router password). Employees received written remote work security policies and signed acknowledgments.

Author: Ethan Caldwel;
Source: williamalmonte.net
HIPAA Cybersecurity Compliance Checklist
The Security Rule's three safeguard categories translate into specific actions organizations must take:
| Safeguard Type | Purpose | Key Requirements | Implementation Examples |
| Administrative | Create management frameworks and documented procedures | Risk analysis completion, designated security official, workforce training programs, incident response protocols, business associate contracts | Annual third-party risk assessment ($3,000-$15,000), appointed Chief Privacy Officer, mandatory quarterly training with completion tracking, documented incident response runbook with 24-hour notification timeline, signed BAA library with 25+ vendors |
| Physical | Secure buildings, equipment, and hardware housing ePHI | Controlled facility entry, protected workstation environments, secure device disposal | Keyfob access system limiting server room entry to 3 authorized staff, 3M privacy filters on all monitors facing public areas, certified hard drive shredding service with certificates of destruction, security camera coverage of all equipment areas |
| Technical | Deploy technology controls protecting data and system access | Unique user identification, automatic session timeouts, data encryption, activity logging, secure transmission | Microsoft Authenticator two-factor authentication for all users, 10-minute idle timeout before automatic logout, AES-256 encryption on all devices, Splunk SIEM tool aggregating logs from all systems, Cisco AnyConnect VPN required for remote access |
Beyond comparing these categories, build a detailed checklist tailored to your specific environment:
- Risk assessment completed and documented within past 12 months with remediation plan (High Priority)
- Named security officer with written job description and training (High Priority)
- Complete written security policies covering all Security Rule requirements (High Priority)
- Signed business associate agreements filed for every vendor accessing ePHI (High Priority)
- Full-disk encryption enabled and verified on all laptops, tablets, and mobile devices (High Priority)
- Unique username and password assigned to each system user with no sharing (High Priority)
- Multi-factor authentication implemented for all remote access and privileged accounts (High Priority)
- Automatic workstation lockout after 10 minutes of inactivity (Medium Priority)
- Monthly audit log reviews documented with findings and actions taken (Medium Priority)
- Annual security awareness training completed by 100% of workforce with records (High Priority)
- Incident response plan tested through tabletop exercise within past 12 months (Medium Priority)
- Data backup restoration tested monthly with documented success rate (High Priority)
- Physical access controls implemented for server rooms and medical record storage (Medium Priority)
- Documented device disposal procedures with certificates of destruction maintained (Medium Priority)
- Access termination checklist ensuring departing employees lose all system access within 24 hours (High Priority)
- Encryption configured for email communications containing patient information (High Priority)
- Firewall and antivirus software installed on all systems with automatic updates (High Priority)
- Password complexity requirements enforced through technical controls (minimum 12 characters, expiration every 90 days) (Medium Priority)
Common Compliance Mistakes and How to Avoid Them
Organizations repeatedly stumble on the same compliance pitfalls. Learning from others' mistakes saves money and headaches.
Treating "addressable" as "optional": I've reviewed dozens of practices that completely skipped addressable specifications without any documentation. They assumed "addressable" meant "we can ignore this." Wrong. When you decide not to implement an addressable requirement, write down why it's not reasonable for your situation and what alternative you're using instead. Example: "We chose not to encrypt internal email communications between staff because our email server remains entirely within our secured internal network with no internet access. As an alternative, we implemented strict access controls limiting email system access to authorized personnel only." That documentation protects you during audits.
Neglecting business associate agreements: Some organizations believe vendor claims like "We're HIPAA compliant!" or "We have enterprise security!" substitute for signed agreements. They don't. Every vendor touching ePHI requires a signed BAA, regardless of their marketing materials or certifications. This includes obvious vendors (EHR systems, billing companies) and less obvious ones (email hosting services, cloud backup providers, IT support contractors, even voicemail transcription services if they access messages containing patient information). Maintain a BAA for each relationship.
Insufficient access controls: Giving every employee full access to all patient records represents unnecessary risk exposure. A receptionist who can view psychiatric evaluations, HIV test results, and substance abuse treatment records creates privacy risks that serve no business purpose. Implement role-based access matching job functions. Receptionists access scheduling and demographics. Medical assistants access charts for their assigned patients. Physicians access clinical information for patients under their care. Billing staff access financial and insurance data. Review these access levels quarterly—people change roles, and permissions should change with them.
Outdated risk assessments: Completing a risk assessment in 2019 and filing it away doesn't satisfy ongoing compliance. Technology has changed drastically since 2019. You've probably added telehealth, maybe switched EHR systems, perhaps moved to cloud storage. Each change introduces new risks requiring assessment. Schedule comprehensive risk assessments annually at minimum. Conduct targeted assessments when implementing new systems or significantly modifying workflows. A current risk assessment reflects your actual environment, not what existed years ago.
Inadequate training: Onboarding training during someone's first week, then nothing for years, fails to maintain security awareness. Threats evolve constantly—phishing tactics that didn't exist three years ago now fool experienced users daily. Schedule comprehensive annual refresher training covering password hygiene, physical security, recognizing social engineering, mobile device security, and reporting procedures. Send quarterly security awareness tips via email. When policies change, train immediately. Run simulated phishing exercises to identify who needs additional coaching.
Poor password practices: Despite endless warnings, "Password123" and "Summer2024!" still appear in healthcare environments. Shared credentials like "nursestation" used by multiple staff members make individual accountability impossible. Require genuinely strong passwords: minimum 12 characters (better 15+), combination of character types, no dictionary words or personal information, changed every 90 days. Implement multi-factor authentication adding a second verification layer. Provide password managers helping employees maintain unique passwords across systems—people can actually remember one strong master password protecting a vault of complex passwords.
Ignoring mobile devices: Smartphones and tablets accessing ePHI need identical protection to desktop computers. Yet many practices overlook mobile security entirely. Physicians checking patient charts on personal phones, nurses using tablets without encryption, therapists carrying unprotected devices to home visits—all create breach risks. Require device encryption (both iOS and Android support this natively). Enforce strong passcodes or biometric authentication. Implement mobile device management (MDM) software enabling remote wipe if devices are lost. Prohibit storing ePHI on personal devices—use secure remote access instead.
Lack of encryption: While technically addressable, encryption has become the de facto standard given its widespread availability and reasonable cost. Choosing not to encrypt ePHI in 2024 requires extraordinary justification. Modern devices include built-in encryption requiring minimal effort to enable. Cloud services offer encryption as standard features. Network traffic encryption costs almost nothing. If you're not encrypting ePHI, document compelling reasons why and describe robust alternative protections you've implemented instead. Be prepared to defend this decision during audits.
Failing to test backups and disaster recovery: Writing a backup plan sounds great until ransomware strikes and you discover backups haven't worked for six months. Test backup restoration monthly—actually restore a sample of data and verify integrity. Run disaster recovery exercises annually simulating various scenarios: ransomware attack, server failure, natural disaster, malicious insider. These drills reveal gaps invisible in written plans. Maybe your backup restoration takes 72 hours, but your practice can't operate that long without patient data. Better to learn this during a drill than during a real emergency.
Missing documentation: HIPAA compliance lives or dies on documentation. Excellent security measures that aren't documented might as well not exist during OCR audits. Document risk assessments with dates, identified vulnerabilities, and remediation actions. Document policy decisions and the reasoning behind them. Document training sessions with attendance rosters. Document security incidents and response steps taken. Document business associate agreements. Document everything. Create a compliance file organization system making documents easily retrievable when auditors ask for them. I've seen organizations with genuinely good security fail audits because they couldn't prove their efforts through documentation.
The biggest mistake I see is organizations treating HIPAA cybersecurity as a checkbox exercise they complete once and forget about. They'll hire a consultant, generate a pile of policies, maybe do some initial training, then consider themselves done. Compliance isn't a destination you reach and forget about—it's a continuous process of assessment, improvement, and adaptation to new threats. Organizations that embrace this mindset not only avoid penalties but also build stronger, more resilient security programs that genuinely protect their patients. The question isn't whether you'll face a security challenge—it's whether you'll be prepared when it happens
— Jennifer Martinez
Frequently Asked Questions About HIPAA Cybersecurity Compliance
Patient trust forms healthcare's foundation. When people share their mental health struggles, chronic conditions, substance abuse histories, and reproductive choices, they're trusting you to protect that information from prying eyes. HIPAA cybersecurity compliance represents how you honor that trust through concrete security measures, not just good intentions.
Meeting Security Rule requirements demands organization-wide commitment. Leadership must prioritize security by allocating sufficient budget and resources. IT staff or managed service providers must implement and maintain technical controls. Clinical staff must follow security policies during patient care. Administrative employees must protect data while scheduling appointments and processing billing. Everyone contributes to the security posture.
Start with honest assessment of your current state. Where does ePHI exist throughout your environment? What threatens it—ransomware, insider snooping, lost devices, natural disasters? Which vulnerabilities create exploitable weaknesses—unpatched software, weak passwords, missing encryption, unlocked doors? This foundation drives everything else.
Build comprehensive policies addressing administrative, physical, and technical safeguard requirements. Don't copy generic templates verbatim—customize them to reflect your actual environment, technology, workflows, and risks. Policies you can't actually follow don't protect anyone.
Implement appropriate controls matching your risk assessment findings and policy requirements. Encryption, access controls, firewalls, training programs, physical security measures, backup systems—the specific tools matter less than whether they effectively address your identified risks.
Train everyone repeatedly. Once isn't enough. Security awareness requires constant reinforcement through annual comprehensive training, quarterly reminders, simulated phishing tests, and immediate updates when policies change or new threats emerge.
Document relentlessly. Risk assessments with dates and findings, policies with version numbers and approval dates, training rosters with signatures, security incidents with response actions, business associate agreements with renewal schedules, audit log reviews with follow-up actions. This documentation proves your compliance efforts when auditors come calling.
The threat landscape never stops evolving. Ransomware gangs develop new attack methods. Phishing schemes grow more sophisticated and harder to recognize. Software vulnerabilities emerge in previously secure systems. Yesterday's adequate protection may fail against tomorrow's threats. HIPAA cybersecurity compliance isn't a project you complete and forget—it's an ongoing process of continuous assessment, adaptation, and improvement.
Whether you're a solo practitioner beginning your compliance journey or a large healthcare system refining sophisticated security programs, the core principles remain constant: assess your risks honestly, implement appropriate safeguards matching those risks, train your people thoroughly, monitor your systems continuously, and document everything comprehensively.
The investment in HIPAA cybersecurity compliance pays dividends beyond avoided penalties. You protect patient privacy, maintain the trust enabling therapeutic relationships, prevent devastating breaches damaging reputations and finances, and demonstrate professionalism in an era where healthcare data security makes headlines regularly. Your patients deserve protection. HIPAA provides the framework. Implementation is up to you.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.