Cybersecurity operations center with analysts monitoring network threats
Red Team Cyber Security Guide
Organizations spend millions building firewalls, deploying endpoint protection, and training employees to spot phishing emails. Yet attackers still breach networks, exfiltrate data, and hold systems hostage. The disconnect? Most defenses are tested only against known threats or hypothetical scenarios. Red team cyber security closes that gap by simulating real adversaries who exploit every weakness—technical, procedural, and human—to achieve their objectives.
Unlike compliance-driven security audits that check boxes, red teaming mirrors how sophisticated threat actors actually operate: patient reconnaissance, creative exploitation, and persistent lateral movement. The result is an honest assessment of whether your defenses work when someone truly wants in.
What Is Red Team Cyber Security?
Red team cyber security is an adversarial assessment where skilled security professionals attempt to compromise an organization's assets using the same tactics, techniques, and procedures (TTPs) employed by real-world attackers. The goal is not simply to find vulnerabilities but to chain them together into successful attack paths that achieve specific objectives—stealing intellectual property, gaining domain administrator access, or disrupting critical operations.
Red teams operate under rules of engagement that define scope, authorized targets, and off-limit systems. But within those boundaries, they use any legal method: social engineering employees, picking locks to enter server rooms, exploiting zero-day vulnerabilities, or compromising third-party vendors. This unrestricted approach reveals blind spots that traditional security assessments miss.
Organizations invest in red teaming for several reasons. Mature security programs need validation that their layered defenses work as a system, not just in isolation. Regulatory frameworks in finance, healthcare, and critical infrastructure increasingly recommend adversarial testing. Executive leadership wants proof that security budgets translate into real resilience. Red teaming provides that evidence by attempting to accomplish what attackers actually want, not just finding individual flaws.
The professionals conducting these engagements typically come from offensive security backgrounds: former penetration testers, security researchers, or individuals with military or intelligence experience. They think like attackers because they understand attacker motivations, constraints, and decision-making processes. This mindset shift from defender to adversary is what makes red team cyber security basics fundamentally different from defensive security work.

Author: Daniel Prescott;
Source: williamalmonte.net
How Red Team Cyber Security Works
Red team engagements follow a structured methodology that mirrors the cyber kill chain used by advanced persistent threats. Each phase builds on the previous one, creating attack paths that demonstrate how initial access escalates into full compromise.
Planning and Reconnaissance
Every engagement begins with defining objectives and constraints. The organization specifies what the red team should attempt to achieve: access the CEO's email, exfiltrate customer databases, or disrupt manufacturing systems. These objectives align with real threat scenarios the organization faces based on industry, adversaries, and crown jewels.
Reconnaissance happens entirely outside the target's visibility. Red teamers gather intelligence from public sources: LinkedIn profiles revealing organizational structure and technologies, GitHub repositories containing hardcoded credentials, job postings describing security tools, and internet-facing assets mapped through passive DNS and certificate transparency logs. They identify acquisition history to find poorly integrated subsidiaries, locate remote offices with weaker security, and profile employees likely to have elevated access.
This phase often consumes weeks. Unlike penetration tests that announce their presence immediately with loud scanning, red teams move slowly to avoid detection. They build detailed target profiles, identify multiple potential entry points, and develop contingency plans. The reconnaissance dossier might include employee names and roles, technology stack details, physical security observations, and third-party relationships that could serve as pivot points.

Author: Daniel Prescott;
Source: williamalmonte.net
Attack Execution and Penetration
Initial access rarely comes from exploiting firewalls or VPNs. Red teams gain entry through paths defenders overlook: spear-phishing campaigns tailored to specific employees using reconnaissance data, exploiting unpatched internet-facing applications, or physically accessing facilities during business hours by impersonating vendors.
One common scenario involves calling the help desk impersonating an executive's assistant, claiming the executive is locked out before an important meeting. Social engineering exploits human nature—the desire to be helpful, fear of angering leadership, and trust in familiar contexts. The help desk resets the password, and the red team has valid credentials.
Once inside, lateral movement begins. Red teamers avoid triggering alerts by using living-off-the-land techniques: legitimate system administration tools like PowerShell, WMI, or remote desktop protocols. They harvest credentials from memory, exploit trust relationships between systems, and escalate privileges by finding misconfigurations. Each hop brings them closer to high-value targets.
Persistence mechanisms ensure they maintain access even if initial entry points close. They might create hidden administrative accounts, install backdoors in legitimate software, or compromise certificate authorities to issue valid credentials. Advanced red teams establish multiple independent access paths so detection of one doesn't end the engagement.
Throughout execution, red teams document every action: timestamps, techniques used, credentials obtained, and systems compromised. This evidence trail proves what happened and helps defenders understand exactly how their environment was breached.
Reporting and Remediation
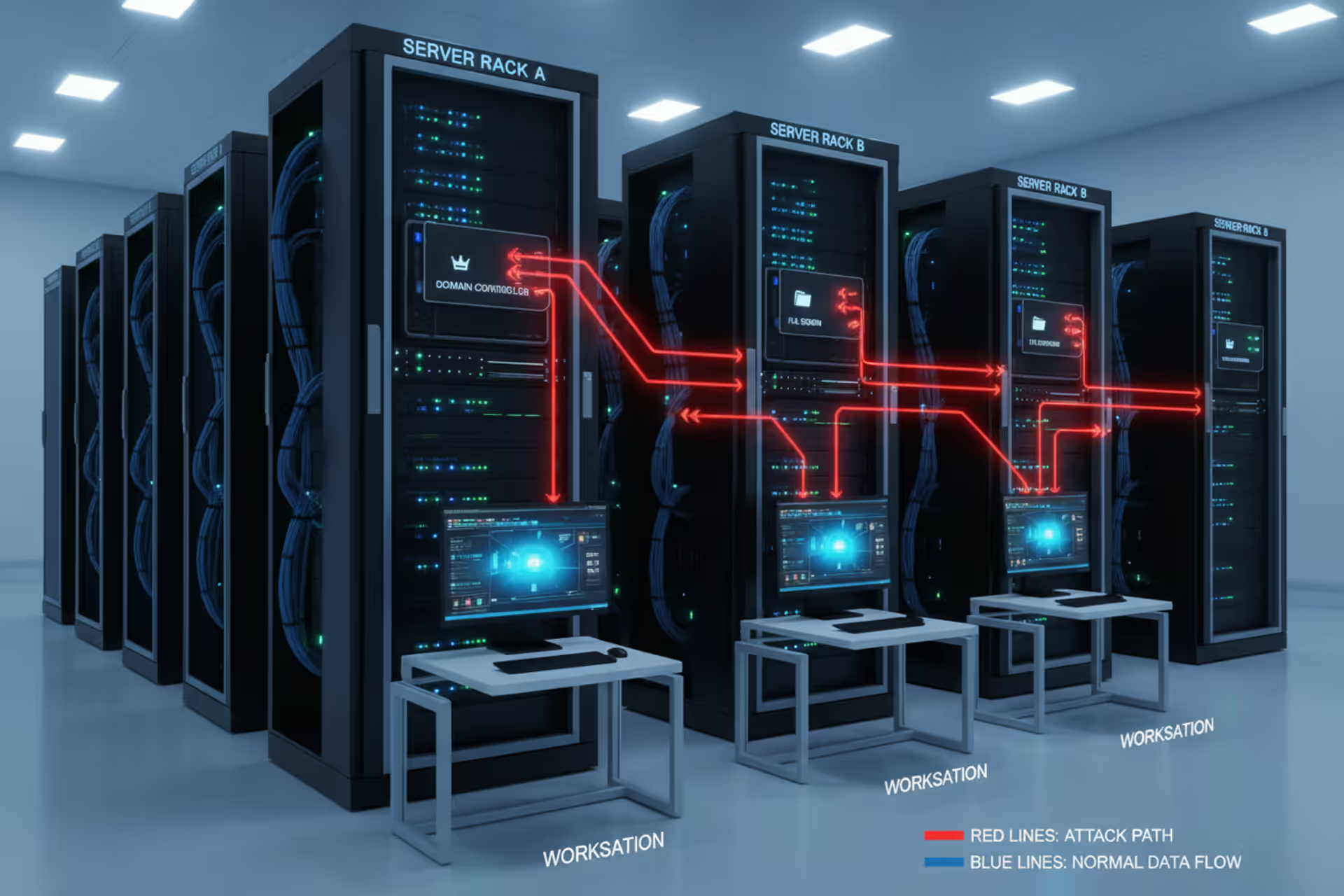
The engagement concludes with detailed reporting that goes beyond listing vulnerabilities. Red team reports map attack paths visually, showing how initial access chained through multiple weaknesses to achieve objectives. They explain why certain defenses failed and which security controls successfully detected or prevented actions.
Effective reports prioritize findings by business impact, not just technical severity. A low-severity vulnerability that provided initial access into a sensitive network segment matters more than a critical vulnerability on an isolated test system. The report includes specific remediation recommendations, detection signatures for the TTPs used, and guidance on improving security operations center (SOC) visibility.
Many organizations conduct hot-wash sessions where red and blue teams review the engagement together. These discussions reveal communication gaps, tool limitations, and process failures that enabled the compromise. The blue team learns attacker tradecraft, and the red team gains insight into defensive challenges.
Remediation tracking extends months beyond the engagement. Organizations fix vulnerabilities, tune detection rules, update playbooks, and retest controls. Some conduct purple team exercises where red and blue teams collaborate to validate that remediation efforts actually prevent the attack paths identified.
Red Team vs. Blue Team vs. Penetration Testing
Security assessments exist on a spectrum from compliance-focused to adversarial. Understanding the differences helps organizations choose appropriate testing methods for their maturity level and objectives.
| Aspect | Red Team | Blue Team | Penetration Testing |
| Objective | Achieve specific business objectives using any method | Detect, respond to, and prevent attacks | Identify and document vulnerabilities |
| Scope | Entire organization including physical, technical, and human elements | Defensive operations and monitoring | Defined systems or applications |
| Duration | Weeks to months of sustained activity | Continuous operations | Days to weeks |
| Approach | Stealthy, mimics real adversaries, avoids detection | Defensive monitoring and incident response | Methodical testing, often announced |
| Frequency | Annually or semi-annually | Ongoing | Quarterly or after major changes |
| Outcome Focus | Attack path narratives and security program validation | Improved detection and response capabilities | Vulnerability reports and remediation guidance |
Penetration testing provides a point-in-time snapshot of vulnerabilities in specific systems. Testers follow methodologies like OWASP or PTES, systematically checking for known vulnerability classes. Organizations typically know testing is happening and expect regular status updates. The deliverable is a prioritized list of findings with remediation steps.
Blue teams represent the defensive side: SOC analysts, incident responders, threat hunters, and security engineers. They monitor logs, investigate alerts, respond to incidents, and tune detection rules. Blue team success is measured by mean time to detect (MTTD) and mean time to respond (MTTR).
Red teams bridge the gap by testing whether blue teams actually detect sophisticated attacks. A successful red team engagement where the blue team never detected the intrusion reveals blind spots in monitoring, gaps in playbooks, or alert fatigue from too many false positives. Conversely, when blue teams quickly detect and contain red team activities, it validates that investments in people, processes, and technology are working.
Organizations often start with penetration testing to address basic vulnerabilities, mature into regular red team engagements to test detection capabilities, and eventually implement purple teaming where red and blue teams collaborate continuously to improve both offensive and defensive skills.
Real-World Red Team Cyber Security Examples
Real engagements demonstrate how red teams chain seemingly minor issues into major compromises. These red team cyber security examples illustrate common attack patterns.
Financial Services Compromise via Third-Party Access
A regional bank engaged a red team to test their fraud detection and data protection controls. The red team researched the bank's vendors and identified a small IT services firm that managed branch network equipment. They called the vendor's help desk claiming to be a bank employee who needed VPN credentials reset. The vendor, trying to provide good customer service, reset credentials without proper verification.
Using the vendor VPN, the red team accessed network management interfaces for branch routers. They pivoted into the bank's corporate network, harvested Active Directory credentials, and gained access to customer databases. Total time from initial call to data exfiltration: four days. The bank's SOC never detected the activity because it originated from a trusted vendor connection.
The engagement revealed gaps in third-party risk management, inadequate network segmentation between vendor and corporate networks, and insufficient monitoring of privileged access. The bank implemented vendor access controls, deployed additional network sensors, and created detection rules for unusual database queries.
Healthcare Data Breach Through Physical Access
A hospital system wanted to test protections for patient data. The red team sent members to the main hospital posing as biomedical equipment technicians. They wore polo shirts with a fake company logo and carried toolboxes. Security waved them through without checking credentials.
Once inside, they found unlocked server closets on multiple floors. They connected rogue wireless access points and keystroke loggers to workstations in nursing stations. Over two weeks, they captured login credentials for the electronic health record system, accessed patient data, and demonstrated they could modify medication orders.

Author: Daniel Prescott;
Source: williamalmonte.net
Physical security weaknesses—unlocked doors, lack of visitor badge verification, unescorted contractor access—combined with technical gaps like unencrypted wireless and shared workstation passwords. The hospital implemented badge verification procedures, locked network closets, deployed network access control, and required unique credentials for clinical systems.
Manufacturing Disruption via Supply Chain
A manufacturing company concerned about operational technology (OT) security hired a red team. Rather than attacking industrial control systems directly, the red team researched software used on the factory floor. They found a small vendor that provided custom production monitoring dashboards.
The red team compromised the vendor's software build environment and inserted a backdoor into a routine software update. When the manufacturer installed the update, the red team gained access to the OT network. They mapped the industrial control architecture, identified critical systems, and demonstrated they could modify production parameters.
This supply chain attack, similar to tactics used in real-world incidents, succeeded because the manufacturer trusted vendor software implicitly. They implemented software verification procedures, isolated OT networks from IT networks, and deployed anomaly detection on industrial systems.
Professional Services Intellectual Property Theft
A consulting firm engaged a red team after a competitor mysteriously won several bids with suspiciously similar proposals. The red team conducted reconnaissance and identified a recently departed employee who left on bad terms. They impersonated this employee in emails to current staff, claiming to need access to shared files for a client transition.
A helpful employee shared links to cloud storage containing proposal templates, client lists, and pricing strategies. The red team escalated access by exploiting weak cloud security configurations, accessed strategic planning documents, and exfiltrated data that would give competitors significant advantage.
The engagement revealed inadequate offboarding procedures, overly permissive cloud sharing settings, and lack of data loss prevention controls. The firm implemented automated access revocation, cloud access governance, and monitoring for unusual data downloads.
There are only two types of companies: those that have been hacked, and those that will be
— Robert Mueller
When Your Organization Needs Red Teaming
Not every organization is ready for red team cyber security. The assessment is most valuable when certain maturity indicators, compliance requirements, or risk factors align.
Security Program Maturity
Red teaming makes sense when your organization has already addressed basic security hygiene. If vulnerability scans regularly find critical issues, penetration tests reveal fundamental misconfigurations, or you lack security monitoring capabilities, red teaming is premature. Fix those foundations first.
Organizations ready for red teaming typically have established security operations centers, vulnerability management programs, incident response playbooks, security awareness training, and regular penetration testing. They want to validate that these investments work together against realistic threats.
A rule of thumb: if your last penetration test found fewer than ten high-severity issues, and your SOC can articulate clear detection use cases for common attack techniques, you're probably ready for adversarial testing.
Compliance and Regulatory Drivers
Several frameworks now recommend or require adversarial testing. The Threat-Led Penetration Testing guidelines from financial regulators describe red team-style assessments. The NIST Cybersecurity Framework suggests adversarial emulation for organizations at higher maturity levels. Critical infrastructure sectors face increasing pressure to validate resilience against sophisticated threats.
Organizations handling sensitive data—financial institutions, healthcare providers, defense contractors—often need to demonstrate security effectiveness to regulators, insurers, or customers. Red team reports provide evidence that security controls function against realistic attack scenarios.
High-Value Assets and Threat Landscape
Companies with intellectual property that competitors would value, infrastructure that nation-state actors might target, or customer data that organized crime seeks face elevated risk. Red teaming helps validate whether existing defenses can withstand adversaries with resources and motivation.
Consider red teaming if your organization has experienced previous breaches, operates in a targeted industry, undergoes frequent merger and acquisition activity that creates integration security gaps, or deploys new technologies like cloud infrastructure or OT systems without extensive security testing.
Organizational Readiness
Red teaming requires executive support and mature handling of findings. Leadership must understand that successful red team compromises don't indicate security failure—they reveal opportunities for improvement. Organizations that blame individuals or punish teams for red team successes will get defensive posturing instead of honest assessment.
The security team should be prepared to learn from findings without taking them personally. The goal is organizational improvement, not demonstrating who is smarter. Effective red teaming requires collaboration, transparency, and commitment to fixing identified issues.

Author: Daniel Prescott;
Source: williamalmonte.net
Common Red Team Techniques and Tools
Red teams employ a diverse toolkit spanning social engineering, physical security, network exploitation, and custom malware. Understanding these techniques helps organizations recognize attack patterns and improve defenses.
Social Engineering
Human vulnerabilities remain the easiest entry point. Red teams craft pretexts—believable scenarios that manipulate targets into taking desired actions. Common approaches include phishing emails with malicious attachments, vishing (voice phishing) calls to help desks or executives, smishing (SMS phishing) with urgent requests, and physical impersonation of vendors or employees.
Advanced social engineering combines multiple channels. A red teamer might send a calendar invitation for a fake meeting, call claiming to be IT support troubleshooting the meeting connection, and request credentials to "fix the issue." The multi-channel approach builds credibility and urgency.
Tools like SET (Social Engineering Toolkit) automate phishing campaigns, Gophish tracks email open rates and link clicks, and Evilginx2 proxies authentication to bypass multi-factor authentication. But the most effective social engineering relies on research and psychological manipulation, not tools.
Physical Security Testing
Digital security means nothing if attackers can walk into server rooms. Red teams test physical controls through tailgating (following authorized personnel through doors), badge cloning, lock picking, and social engineering security guards or receptionists.
Once inside, they deploy rogue access points for network access, install hardware keyloggers or USB drop devices, photograph sensitive documents or whiteboards, and access unlocked workstations. Physical access often provides easier paths to objectives than remote exploitation.
Physical security tools are surprisingly simple: lock pick sets, badge cloners, hidden cameras, and USB devices that emulate keyboards to execute commands when plugged in. The challenge is operational security—acting naturally, having plausible stories if questioned, and avoiding actual trespassing charges through proper legal agreements.
Network Exploitation
Once red teams gain initial access, they need to move laterally and escalate privileges. They exploit weak passwords using tools like Hashcat or John the Ripper, abuse trust relationships between systems, exploit unpatched vulnerabilities, and leverage misconfigurations in Active Directory.
Common tools include Metasploit for exploitation, Cobalt Strike for command and control, Mimikatz for credential harvesting, and BloodHound for mapping Active Directory attack paths. PowerShell Empire and similar frameworks enable "living off the land" attacks using built-in Windows tools that blend with legitimate activity.
Red teams increasingly use custom malware or heavily modified open-source tools to avoid signature-based detection. They employ anti-forensics techniques to remove evidence, encrypt communications to evade network monitoring, and time activities during high-traffic periods to blend with normal operations.
Operational Security
The most critical red team skill is avoiding detection. Red teams use operational security (OPSEC) practices: rotating infrastructure to prevent IP blacklisting, mimicking normal user behavior patterns, limiting tool usage to avoid triggering alerts, and establishing covert communication channels.
They monitor the target's security posture during engagements, watching for signs their activities triggered investigations. If the blue team starts hunting, red teams may pause, switch tactics, or activate backup access methods. This cat-and-mouse dynamic mirrors real adversary behavior.
Frequently Asked Questions About Red Team Cyber Security
Red team cyber security transforms abstract security investments into concrete evidence of resilience. By simulating real adversaries who exploit every available weakness, organizations discover whether their defenses actually work under pressure. The findings are rarely comfortable—successful red team compromises reveal gaps in technology, process, and human awareness. But this discomfort drives improvement in ways that compliance audits and vulnerability scans cannot.
The value extends beyond fixing specific vulnerabilities. Red team engagements teach defenders how attackers think, validate that security operations centers can detect sophisticated threats, and provide executives with honest assessments of security posture. Organizations that embrace adversarial testing mature faster than those that rely solely on defensive assessments.
Start by ensuring your security fundamentals are solid. Address basic vulnerabilities, establish monitoring capabilities, and develop incident response processes. When you're ready to test whether those investments work together against realistic threats, red teaming provides the answer. The question is not whether you'll find gaps—you will. The question is whether you'll discover them through controlled testing or actual breaches.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.