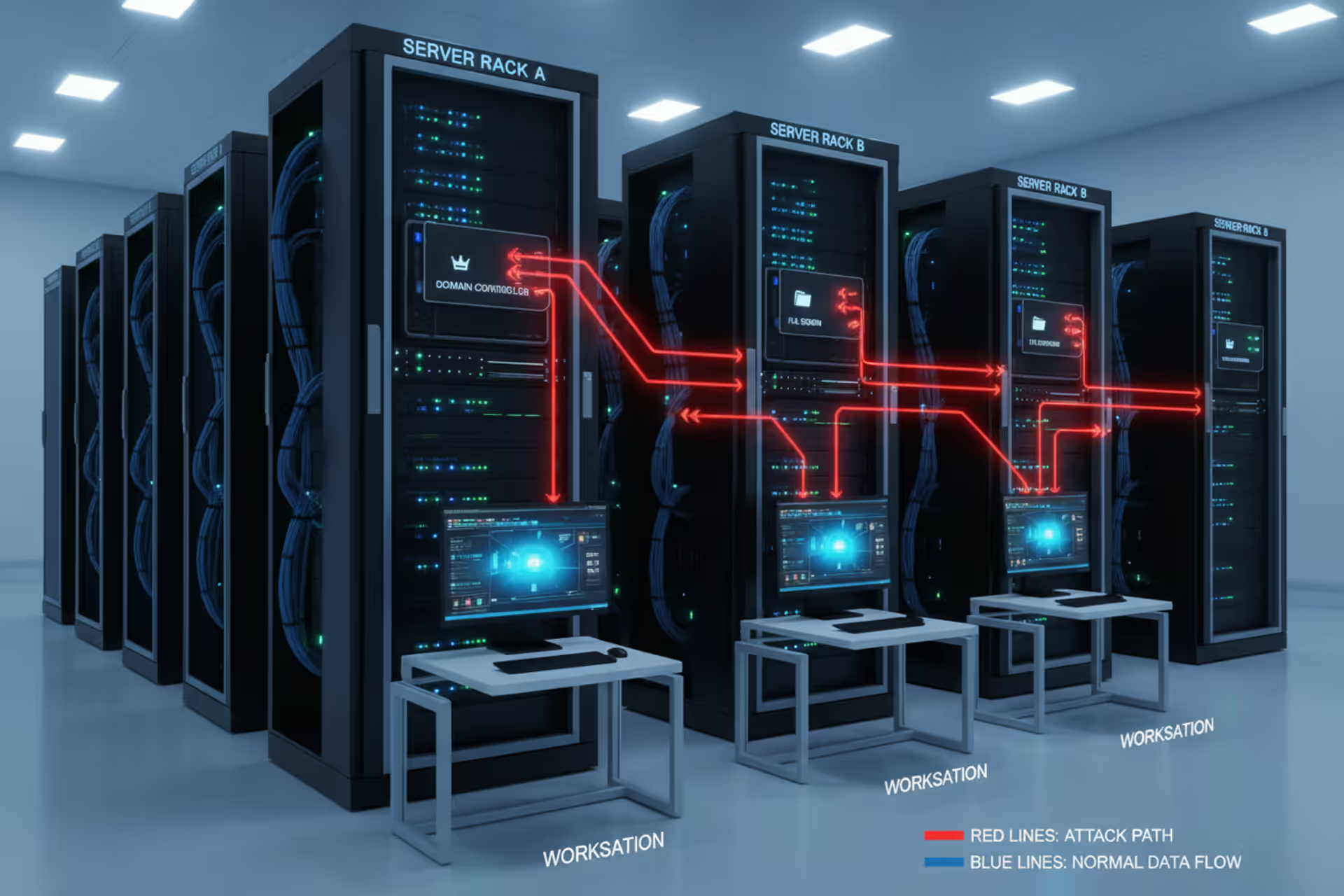
Lateral movement across an enterprise network diagram
Lateral Movement Cyber Security Guide
Lateral movement describes how attackers navigate horizontally across a network after gaining initial access to a single system. Rather than stopping at the entry point, adversaries move from device to device, escalating privileges and searching for high-value targets like domain controllers, database servers, or sensitive file shares.
This phase sits squarely in the middle of the cyber kill chain, after initial compromise but before data exfiltration or destructive actions. The attacker already controls one machine—perhaps through a phishing email or unpatched vulnerability—but that foothold rarely contains the crown jewels. Lateral movement cyber security basics revolve around understanding that breaches don't end at the perimeter; they expand inward.
Initial access and lateral movement differ in purpose and scope. Initial access focuses on breaking into a single endpoint or account. Lateral movement exploits that beachhead to reach additional systems, often leveraging legitimate administrative tools and protocols to avoid detection. An attacker might spend weeks quietly mapping the network, harvesting credentials, and positioning themselves before triggering alarms.
Organizations often discover breaches only after lateral movement has progressed far enough to cause damage. A compromised workstation might go unnoticed, but when an attacker pivots to a file server and encrypts terabytes of data, the incident becomes impossible to ignore. Understanding lateral movement cyber security explained means recognizing that the real battle happens inside the network, not just at the firewall.
How Lateral Movement Cyber Security Works
The technical mechanics of lateral movement rely on credential theft, protocol abuse, and exploiting trust relationships built into enterprise networks. Once attackers control an initial system, they dump credentials from memory, registry hives, or cached authentication tokens. Tools like Mimikatz can extract plaintext passwords, NTLM hashes, or Kerberos tickets from a compromised Windows machine in seconds.

Author: Vanessa Keaton;
Source: williamalmonte.net
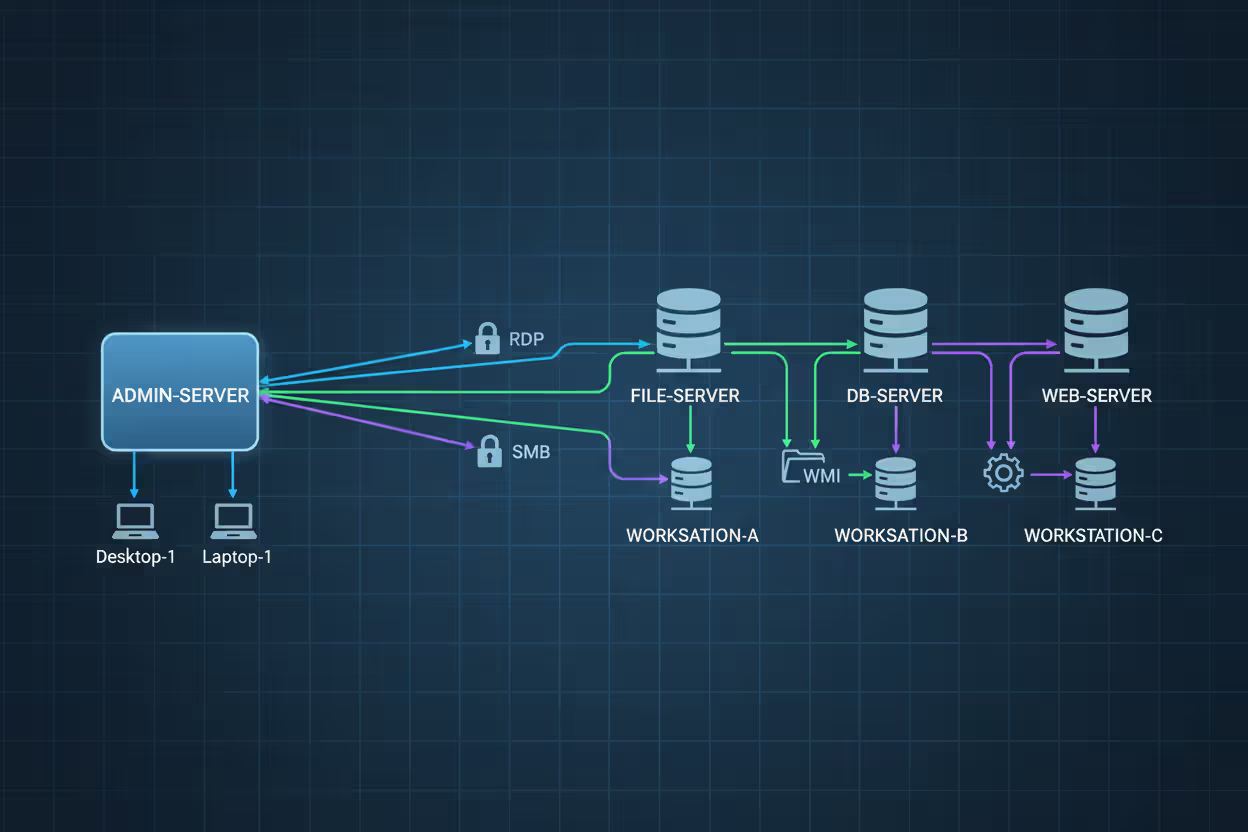
Armed with these credentials, adversaries authenticate to other systems using protocols designed for legitimate remote administration. Remote Desktop Protocol (RDP) allows graphical access to Windows machines. Server Message Block (SMB) enables file sharing and remote service execution. Windows Management Instrumentation (WMI) provides a scriptable interface for system management. Attackers abuse these same tools, blending their activity with normal administrative traffic.
Trust relationships amplify the problem. Domain-joined Windows environments authenticate users centrally, meaning a credential harvested from one machine often unlocks dozens of others. Service accounts with broad permissions create highways for lateral movement. An attacker who compromises a backup server with domain admin credentials can immediately access every system in the environment.
Author: Vanessa Keaton;
Source: williamalmonte.net
Common Techniques Attackers Use
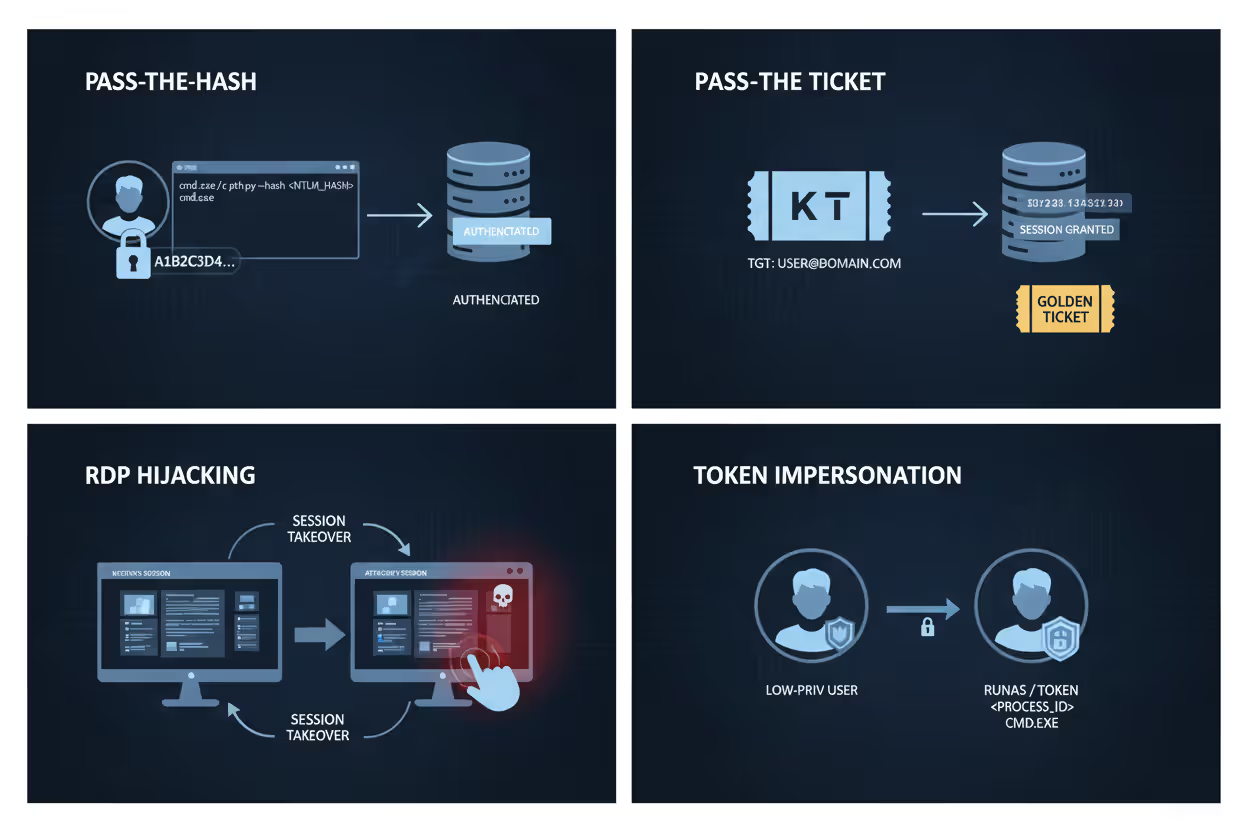
Pass-the-Hash lets attackers authenticate using stolen NTLM password hashes without cracking them to plaintext. Windows accepts the hash directly for network authentication, so adversaries bypass the need to recover actual passwords. This technique works because many organizations still allow legacy NTLM authentication alongside newer Kerberos protocols.
Pass-the-Ticket targets Kerberos ticket-granting tickets (TGTs). Attackers extract valid TGTs from memory and inject them into their own sessions, impersonating legitimate users without touching passwords. Golden ticket attacks take this further by forging TGTs using the domain's Kerberos key, granting unlimited access for years if undetected.
RDP hijacking switches an attacker's session to an active RDP connection from another user without requiring credentials. The attacker assumes the victim's identity, inheriting all permissions and access. This technique leaves minimal logs since the connection already existed.
Token impersonation exploits Windows access tokens that represent user security contexts. Attackers running code on a compromised system can duplicate tokens from other logged-in users or services, then impersonate those identities to access additional resources.
Author: Vanessa Keaton;
Source: williamalmonte.net
Typical Attack Progression Stages
Reconnaissance comes first. Attackers enumerate network topology, identify domain controllers, locate file shares, and map user accounts. Built-in Windows commands like net view, nltest, and dsquery provide this intelligence without triggering alerts in many environments.
Credential harvesting follows. Attackers target systems where privileged users recently authenticated, scraping credentials from memory or disk. They prioritize IT workstations, jump servers, and systems running enterprise management software where admin credentials accumulate.
Privilege escalation establishes higher access levels. Attackers exploit misconfigured services, unpatched vulnerabilities, or weak Group Policy settings to gain local administrator rights, then leverage those rights to extract domain credentials.
Horizontal spread pushes outward to additional systems. Using stolen credentials and legitimate protocols, attackers authenticate to new machines, install persistence mechanisms, and repeat the harvesting process. Each compromised system becomes a new pivot point.
Objective completion ends the cycle. Once attackers reach domain controllers, database servers, or other targets, they execute their final goals: deploying ransomware, exfiltrating intellectual property, or establishing long-term espionage infrastructure.
Real-World Lateral Movement Cyber Security Examples
The 2013 Target breach demonstrates lateral movement's devastating potential. Attackers initially compromised a third-party HVAC vendor's credentials, gaining access to Target's network perimeter. Rather than stopping there, they moved laterally to point-of-sale systems across hundreds of stores, installing malware that captured 40 million credit card numbers. The initial foothold was minor; lateral movement transformed it into one of retail's worst breaches.
SolarWinds supply chain attacks in 2020 showcased sophisticated lateral movement by nation-state actors. After compromising SolarWinds' build system and distributing backdoored software updates, attackers used their initial access to customer networks as launching points. They moved laterally to cloud environments, email systems, and identity providers, establishing persistent access across thousands of organizations. The attacks demonstrated how lateral movement extends beyond on-premises networks into hybrid cloud infrastructure.
Ransomware campaigns routinely depend on lateral movement. The 2021 Colonial Pipeline attack began with a single compromised VPN password lacking multi-factor authentication. Attackers moved laterally through the corporate network, identifying critical systems and deploying ransomware across operational technology networks. The lateral movement phase determined which systems got encrypted, transforming a single credential compromise into a national fuel supply crisis.
NotPetya malware in 2017 automated lateral movement at unprecedented scale. After initial infection, the malware used multiple techniques—EternalBlue exploit, credential harvesting, and legitimate administrative tools—to spread across networks within minutes. Organizations found themselves completely encrypted before security teams could respond, with lateral movement happening faster than human reaction times.

Author: Vanessa Keaton;
Source: williamalmonte.net
How to Detect Lateral Movement in Your Network
Behavioral analytics identify deviations from normal patterns. A user account that typically accesses three servers suddenly authenticating to fifty systems within an hour signals potential compromise. Machine learning models establish baselines for each account and device, flagging anomalous lateral movement attempts.
Log analysis provides forensic evidence of lateral movement techniques. Windows Event ID 4624 (successful logon) combined with logon type 3 (network) or type 10 (RDP) shows remote authentication attempts. Unusual authentication times—service accounts logging in at 3 AM on weekends—warrant investigation. Correlating authentication logs across systems reveals movement patterns invisible when viewing single machines.
Network traffic analysis exposes protocol abuse. Legitimate RDP sessions typically involve sustained connections with interactive traffic patterns. Attackers using RDP for lateral movement often show brief connections focused on credential dumping or malware deployment. Monitoring SMB traffic for administrative share access (\target\C$) identifies potential lateral movement attempts.
Network segmentation limits visibility into lateral movement but creates detection opportunities at segment boundaries. When an attacker tries moving from a workstation VLAN to a server VLAN, the firewall or network access control system can flag the unusual cross-segment authentication. Micro-segmentation creates more boundaries, generating more detection opportunities.
Endpoint detection and response (EDR) tools monitor individual systems for lateral movement indicators. They detect credential dumping tools, unusual process execution patterns, and suspicious PowerShell commands. EDR visibility into process parent-child relationships helps identify attackers using legitimate tools like PsExec or WMI for malicious purposes.
Honeypot credentials planted throughout the network act as tripwires. These fake accounts with tempting names like "SQL_Admin" or "Backup_Service" have no legitimate use. Any authentication attempt using honeypot credentials indicates an attacker harvesting and testing credentials during lateral movement.

Author: Vanessa Keaton;
Source: williamalmonte.net
How to Prevent Lateral Movement Attacks
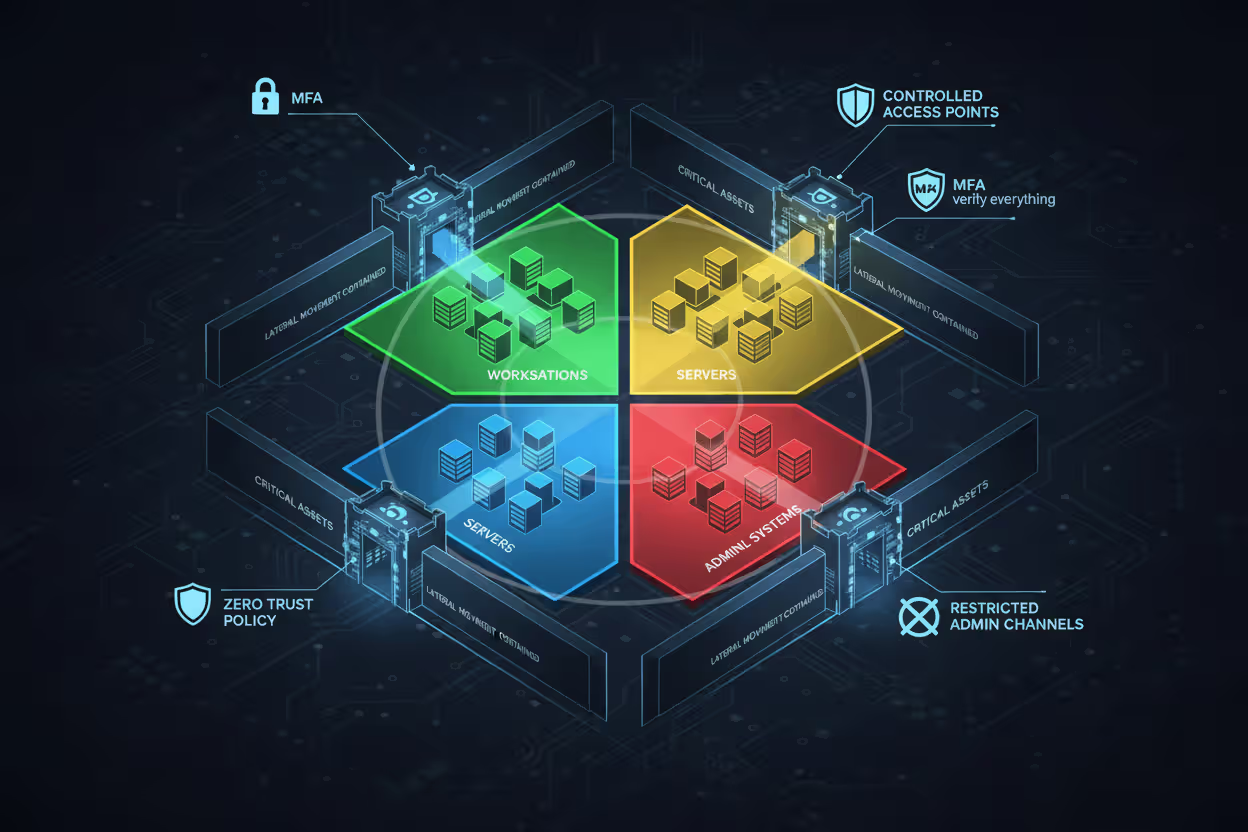
Least privilege access restricts each account to only necessary permissions. Service accounts shouldn't have domain admin rights. Users don't need local administrator access to workstations. Every excessive permission creates a lateral movement pathway. Regular access reviews identify and remove privilege creep before attackers exploit it.
Multi-factor authentication (MFA) blocks credential theft's effectiveness. Stolen passwords become worthless when attackers can't provide the second factor. Extend MFA beyond VPN and email to internal resources like RDP, administrative portals, and privileged access management systems. Phishing-resistant MFA using hardware tokens or biometrics defeats sophisticated attacks.
Network segmentation contains lateral movement by dividing networks into isolated zones. Place domain controllers in a separate VLAN from workstations. Isolate production servers from development environments. Require explicit firewall rules for cross-segment traffic rather than allowing unrestricted internal access. Zero trust network access (ZTNA) takes segmentation further by authenticating and authorizing every connection regardless of network location.
Credential hygiene prevents harvesting techniques. Disable NTLM authentication where possible, forcing Kerberos-only environments. Enable Credential Guard on Windows systems to protect credentials in virtualized containers. Configure LSASS protection to block memory dumping tools. Rotate local administrator passwords using tools like LAPS (Local Administrator Password Solution), ensuring compromised credentials expire quickly.
Privileged access workstations (PAWs) isolate administrative activities. Administrators perform privileged tasks only from hardened, restricted systems that don't browse the internet or check email. This prevents credential harvesting from phishing attacks or drive-by downloads that target admin workstations.
Author: Vanessa Keaton;
Source: williamalmonte.net
Application control whitelists prevent unauthorized tools from executing. Attackers rely on utilities like Mimikatz, PsExec, and PowerShell scripts for lateral movement. Restricting executable files to approved applications blocks these tools while allowing legitimate business software. PowerShell logging and constrained language mode limit script-based attacks.
Just-in-time (JIT) privileged access eliminates standing administrative permissions. Administrators request elevated access when needed, receive temporary credentials valid for specific tasks, then automatically lose privileges afterward. This time-boxing prevents attackers from finding and abusing persistent privileged accounts.
Lateral Movement vs. Other Attack Phases
| Attack Phase | Primary Goal | Typical Duration | Network Position | Detection Difficulty |
| Initial Access | Establish foothold on single system | Minutes to hours | Perimeter/endpoint | Medium (signature-based detection works) |
| Lateral Movement | Spread across network to reach targets | Days to weeks | Internal network | High (uses legitimate tools and protocols) |
| Privilege Escalation | Gain higher permissions on compromised systems | Hours to days | Individual systems | Medium (exploit-based, behavioral anomalies) |
| Data Exfiltration | Extract sensitive information | Hours to months | Outbound network | Medium (large transfers, unusual destinations) |
Lateral movement differs from privilege escalation in scope and direction. Privilege escalation happens vertically on a single system, moving from standard user to administrator. Lateral movement spreads horizontally across systems, potentially without elevating privileges on each machine. An attacker might move laterally using standard user credentials that happen to work on multiple systems.
Initial access focuses on breaching the perimeter or compromising an endpoint through phishing, vulnerabilities, or stolen credentials. Success means controlling one system. Lateral movement begins after initial access succeeds, using that foothold to expand access. The two phases require different defensive strategies—initial access prevention emphasizes perimeter security and endpoint protection, while lateral movement prevention focuses on internal segmentation and identity management.
Data exfiltration represents the attacker's end goal, while lateral movement is the means to reach exfiltration targets. Attackers move laterally to locate valuable data, then exfiltrate it. However, lateral movement can serve other objectives like deploying ransomware or establishing persistent backdoors. Not every lateral movement campaign ends with exfiltration.
Adversaries rarely stay on one system. Once inside, they move laterally to expand access, locate valuable assets, and achieve their objectives
— Eric S. Raymond
How to Prevent Lateral Movement Attacks
Zero trust architecture fundamentally rethinks network security by eliminating implicit trust. Traditional perimeter-focused security assumes anything inside the network is trustworthy. Zero trust verifies every access request regardless of origin, treating internal and external connections identically. This prevents lateral movement by requiring authentication and authorization at each step.
Identity and access management (IAM) becomes the new perimeter. Strong identity verification, continuous authentication, and granular authorization policies replace network location as the primary security control. Attackers who compromise one system can't automatically pivot to others without repeatedly proving identity and need-to-know.
Endpoint detection and response (EDR) deployments across all systems provide visibility into lateral movement attempts. EDR agents monitor process execution, network connections, and file modifications, correlating events across endpoints to identify attack patterns. Automated response capabilities can isolate compromised systems before lateral movement progresses.
Security information and event management (SIEM) systems aggregate logs from across the infrastructure, correlating authentication events, network traffic, and endpoint telemetry. Custom detection rules identify lateral movement patterns like multiple failed authentication attempts followed by success, or service accounts authenticating from unusual locations.
Regular vulnerability patching eliminates exploitation paths. Attackers often use unpatched vulnerabilities for privilege escalation during lateral movement. Prioritize patches for remote code execution vulnerabilities and those affecting authentication systems. Automated patch management ensures timely deployment across large environments.
Disable unnecessary services and protocols. If systems don't require RDP, disable it. If NTLM authentication isn't needed, block it. Each disabled service removes a potential lateral movement vector. Audit enabled protocols regularly, questioning whether business needs justify the security risk.
Frequently Asked Questions About Lateral Movement
Lateral movement represents the critical phase where initial compromises transform into major breaches. Attackers who gain a single foothold can spread across entire networks, reaching sensitive data and critical systems through credential theft and protocol abuse. The techniques aren't exotic—they exploit the same remote administration tools and authentication protocols that IT teams use daily.
Detection requires visibility into authentication patterns, network traffic, and endpoint behavior across the entire infrastructure. Prevention demands architectural changes: network segmentation, zero trust principles, privileged access management, and credential hygiene. Organizations that treat lateral movement as an inevitable post-compromise phase and design defenses accordingly fare better than those relying solely on perimeter security.
The most effective defense combines technical controls with operational discipline. Least privilege access limits what compromised credentials can access. Multi-factor authentication blocks credential theft attacks. Network segmentation contains spread. Behavioral analytics detect anomalies. No single control stops lateral movement, but layered defenses force attackers to make noise, creating detection opportunities before they reach critical assets.
Understanding how lateral movement cyber security works empowers security teams to design appropriate defenses, prioritize detection capabilities, and respond effectively when prevention fails. The battle against sophisticated attackers happens inside the network, making lateral movement detection and prevention essential components of modern cybersecurity programs.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.




