Cybersecurity analyst monitoring a honeypot decoy inside a corporate network
Honeypot Cyber Security Guide
Content
Content
Most companies pour resources into firewalls and antivirus software, hoping to keep hackers out. But here's a twist: what if you could learn more by letting them in—sort of? That's exactly what honeypots do. They're fake systems that look vulnerable on purpose, sitting there waiting for attackers to take the bait. When someone does, you get a front-row seat to watch how they operate.
What Is Honeypot Cyber Security?
Think of honeypot cyber security as setting up a decoy in your network. You're deliberately placing systems that appear to contain valuable information but actually exist solely to monitor anyone who touches them. It's like leaving out a laptop that looks like it has executive emails, except everything on it is fake and you're recording every keystroke.
Why would organizations do this? Three main reasons stand out. You get an alarm bell that rings the moment someone starts poking around where they shouldn't. You collect real intelligence about what attackers want and how they work. And you keep them busy with fake targets while your actual assets stay protected.
Here's what the honeypot cyber security basics look like in practice. Let's say you run a bank. You might set up what appears to be a customer database server, complete with realistic-looking table names and folder structures. An energy company could deploy something that looks like it controls part of their power grid. The trick? Making it convincing enough that attackers can't tell it's a trap until it's too late.
This works because attackers scan networks looking for weak spots. They can't immediately tell which systems are real and which are decoys. The moment someone logs into your honeypot, you know something's wrong—your legitimate employees have zero reason to access these systems.
But detection is just the beginning. You're also gathering intelligence that traditional security tools simply can't provide. Which passwords do attackers try first? What malware do they install? How fast do they move through a network once they're in? You get answers to all these questions without risking your actual data.

Author: Marcus Halbrook;
Source: williamalmonte.net
How Honeypot Cyber Security Works
Getting how honeypot cyber security works starts with placement. You can't just dump a decoy in some isolated corner of your network and expect results. Smart placement means putting honeypots where an attacker would naturally stumble across them while exploring your environment.
Setup involves making your honeypot look vulnerable without being obviously fake. Maybe you run software that's three versions out of date with known security holes. Perhaps you set the admin password to "Admin123." You might expose services that should be behind a firewall. The goal? Look juicy enough to investigate.
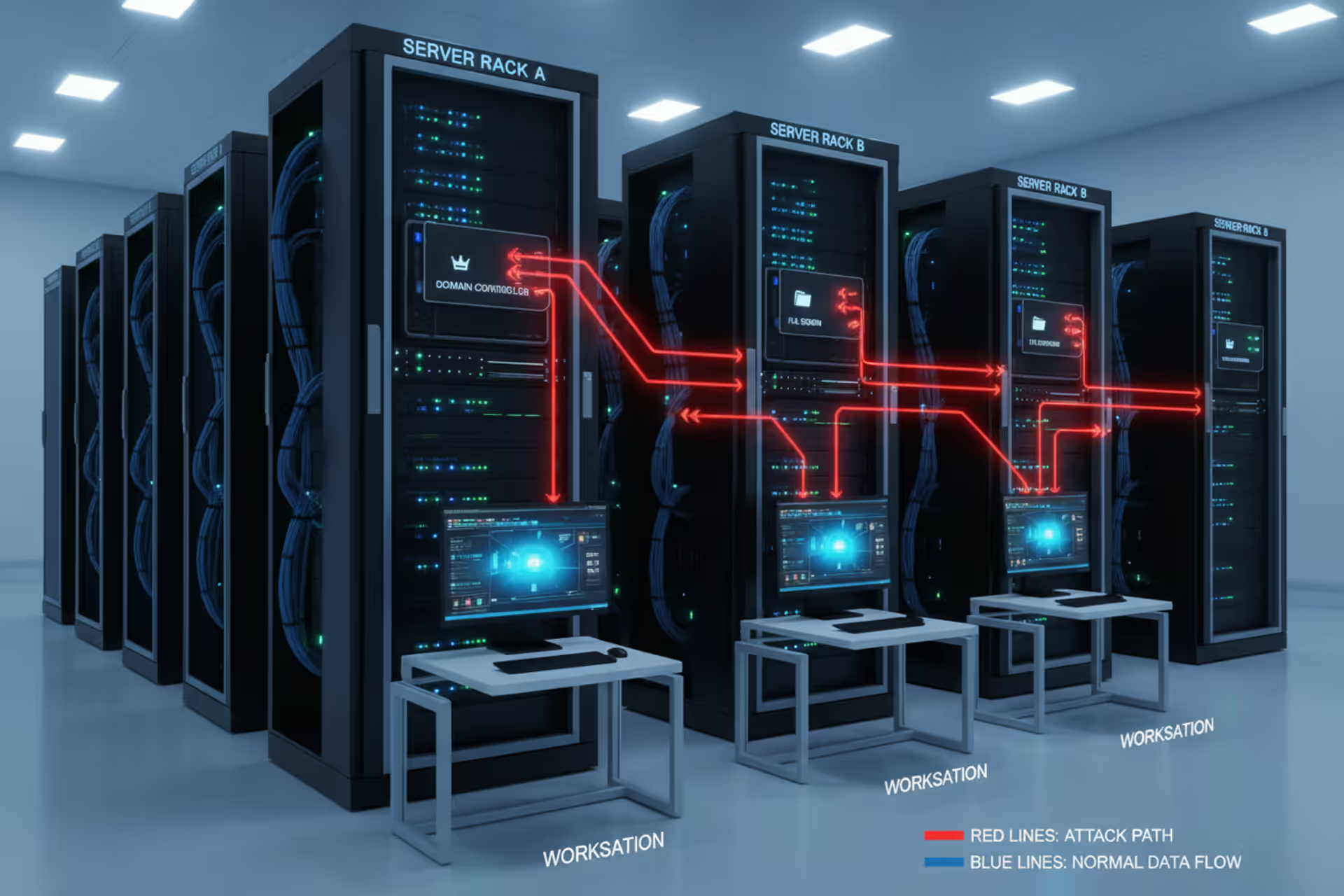
Once everything's running, the waiting game begins. Some security teams get creative here—they'll leave breadcrumbs throughout their network pointing toward the honeypot. Picture finding a config file on a compromised workstation that mentions a "backup_server_admin" with credentials. An attacker who discovers this will probably try those credentials, walking straight into your trap.
The magic happens when someone interacts with your honeypot. Every command they type gets logged. Every file they open, every network connection they attempt, every bit of data they try to steal—all recorded. Production systems can't log this comprehensively because it would slow everything down, but honeypots don't have real users to worry about.
Modern honeypot cyber security explained includes tight integration with your existing security stack. When your honeypot detects activity, it can automatically alert your security team through your SIEM platform. Some setups go further, triggering automated responses like isolating network segments or blacklisting IP addresses.
Analyzing what you capture requires dedicated effort. A single honeypot interaction might reveal a zero-day exploit, a new ransomware variant, or a coordinated campaign targeting your industry. One security team discovered attackers were specifically searching for API keys in configuration files—information that helped them better protect their real systems.
You can also run active deception campaigns. When attackers compromise your honeypot, you might feed them false information about your network layout. Watch how they use that information. Follow them back to their command servers. This approach turns defense into offense, giving you leverage against adversaries.
Types of Honeypots Used in Cyber Defense
Different honeypots serve different purposes. Your choice depends on how much risk you'll tolerate, what resources you can spare, and what kind of intelligence you're after.
Low-Interaction Honeypots
These honeypots fake it. They'll respond to network requests and pretend to be vulnerable services, but they don't let attackers actually break in. When someone tries to exploit a supposed vulnerability, the honeypot generates realistic-looking responses without running any malicious code.
Where do these shine? Catching automated attacks and mass scanning. They're cheap to run (one server can pretend to be dozens of different systems), and they're incredibly safe since attackers never touch a real operating system.
Companies with small security teams often start here. Setup takes a few hours, not weeks. Maintenance is minimal. The downside? Limited insight. You'll see that someone tried to exploit your fake web server, but you won't learn what they planned to do after getting in.

Author: Marcus Halbrook;
Source: williamalmonte.net
High-Interaction Honeypots
Now we're talking about the real deal—actual servers running genuine operating systems and applications. When attackers compromise these, they get full access. They can install rootkits, steal files, encrypt drives, whatever they want. Except you're watching the entire time.
The intelligence quality jumps dramatically. You observe sophisticated attackers' actual workflows. What tools do they download? How do they escalate privileges from a basic user to an administrator? Which files do they consider valuable enough to exfiltrate? This visibility is impossible with simpler alternatives.
But the risks escalate too. Even with careful isolation, a skilled attacker might use your honeypot as a launching pad for attacks against your real infrastructure. You need dedicated hardware, bulletproof network segmentation, and constant monitoring. Each honeypot consumes resources equivalent to a production server.
Organizations typically deploy high-interaction honeypots when investigating specific threat actors. Maybe you've seen indicators that someone's targeting your company specifically. Setting up a high-fidelity trap lets you study their methods without risking actual assets. Researchers use these to document new malware families and share findings with the broader security community.
Production honeypots protect specific organizations, while research honeypots contribute to collective threat intelligence. Production deployments prioritize keeping your environment safe. Research deployments prioritize data collection and often publish findings publicly.
| Honeypot Category | Setup Difficulty | Infrastructure Needed | Safety Level | Intelligence Value | Best Situations |
| Simulated Services | Simple | One server runs many decoys | Extremely safe | Shows scanning patterns and basic exploits | Detecting automated attacks, limited security budgets, getting started |
| Full Systems | Complex | Each decoy needs dedicated hardware | Requires careful isolation | Captures complete attacker behavior after compromise | Studying advanced threats, malware analysis, targeted investigations |
| Operational Defense | Medium difficulty | Depends on approach | Relatively safe with proper setup | Threats specifically targeting your organization | Internal threat hunting, perimeter monitoring, meeting compliance requirements |
| Academic Study | Very complex | Significant hardware commitment | Moderate risk level | Insights into broader attack trends | University research, sharing community intelligence, tracking emerging tactics |
Real-World Honeypot Cyber Security Examples
A major bank deployed honeypots resembling their ATM management infrastructure back in 2023. Within six weeks, attackers had compromised one and installed malware designed to make machines dispense cash. The security team captured this malware before it ever reached their actual ATM fleet, potentially preventing millions in losses.
Healthcare networks face constant targeting for patient data. One hospital system created honeypot cyber security examples by setting up fake electronic health record servers. They populated these with fabricated records that looked real—names, addresses, diagnoses, insurance information. An insider employee accessed a honeypot containing supposed celebrity patient records. That employee had no legitimate reason to view those files. Investigation revealed they planned to sell the information.
The energy sector deals with nation-state threats. Several power companies have deployed honeypots mimicking industrial control systems—the computers that actually manage power generation and distribution. These honeypots have detected reconnaissance activity from advanced persistent threat groups, providing weeks or months of advance warning before actual attacks materialized.
E-commerce platforms create fake customer databases filled with realistic but invented information. When attackers steal this data, security teams track its journey. Does it appear on dark web forums within days? Does someone try using the credentials in credential-stuffing attacks? Which underground marketplaces sell it? This intelligence reveals how stolen data gets monetized.
Major cloud providers run honeypot networks across their global infrastructure. These detect compromised accounts, identify misconfigurations that customers might be using, and catch attacks targeting specific cloud services. Microsoft, Amazon, and Google all operate these systems, though they don't publicize details. When a new exploitation technique emerges, their honeypots often detect it before it affects paying customers.
University researchers documented an entire ransomware attack from start to finish using honeypots in 2024. They watched attackers move from initial compromise through privilege escalation, lateral movement, data exfiltration, and finally encryption—all in just four hours. That research revealed how little time defenders have to respond once attackers get in.

Author: Marcus Halbrook;
Source: williamalmonte.net
Benefits and Limitations of Honeypot Deployment
The biggest advantage of honeypot cyber security explained comes down to signal versus noise. Traditional intrusion detection systems generate thousands of alerts daily, most of them false positives. Honeypots generate almost zero false positives because legitimate users never touch them. Any activity means trouble.
You catch threats early. Attackers typically spend time in reconnaissance before hitting high-value targets. Honeypots often detect them during this exploration phase, before they've found anything important. That head start lets you lock things down, hunt for other compromises, and prepare your response.
The threat intelligence you collect is immediately relevant. Generic threat feeds tell you about attacks happening somewhere in the world. Honeypots tell you about attacks happening in your network right now. That contextual specificity helps prioritize defenses and allocate resources effectively.
Resource efficiency surprises people. Unlike intrusion detection systems that need constant tuning and rule updates, honeypots mostly run themselves. Deploy them, check logs periodically, done. One analyst can monitor several honeypots without drowning in false alarms.
But limitations exist, and they're significant. Skilled attackers sometimes recognize honeypots. Systems that look too vulnerable, networks that feel suspiciously empty, services that respond just slightly wrong—these can give away the deception. Attackers who spot your honeypot will simply avoid it.
Legal questions get murky. What happens if an attacker uses your honeypot to launch attacks against other companies? Some courts have held organizations liable for facilitating attacks, even unintentionally. You need rock-solid network isolation and careful monitoring. Even then, legal frameworks around deception-based security remain unclear in many jurisdictions.
Resource demands, particularly for realistic honeypots, add up quickly. Each system needs monitoring. Someone must analyze captured data and translate findings into defensive actions. Updates keep honeypots looking authentic as your real environment evolves. Organizations often underestimate the staff time required.
Honeypots introduce risk themselves. Poor configuration or weak isolation might give attackers a stepping stone into production networks. Your decoy systems need the same security rigor as real ones—ironic, considering their purpose.
Coverage has inherent limitations. Honeypots only detect attackers who interact with them. Someone who successfully compromises production systems without encountering your decoys stays invisible. Think of honeypots as sensors that enhance rather than replace comprehensive security programs.
We've watched honeypots mature from academic experiments to critical intelligence infrastructure. Organizations extracting real value aren't just collecting data—they're feeding honeypot insights directly into architectural decisions, budget planning, and response procedures. The difference between success and failure comes down to treating honeypots as intelligence platforms rather than standalone defenses
— Sarah Chen
Implementing Honeypots in Your Security Strategy
Start by defining what you want to achieve. Are you primarily seeking early warning when attackers probe your network? Building threat intelligence about techniques targeting your industry? Researching specific attack types? Your answers shape everything else—where you place honeypots, how interactive they should be, how you'll monitor them.
Planning requires understanding your network architecture. Where would honeypots make sense from an attacker's perspective? Sticking them in an isolated subnet that nobody ever accesses is pointless and obvious. Instead, position them among production systems where attackers would naturally encounter them while moving laterally.
Begin with simulated-service honeypots to gain experience with minimal risk. Set up several instances pretending to be commonly targeted services—web servers, databases, file shares, remote desktop. Monitor what happens. You'll quickly learn what attacks target your network and develop workflows for analyzing interactions.
Integration with existing tools amplifies value exponentially. Configure your honeypots to send alerts into your SIEM platform. Security operations center staff see honeypot events alongside everything else, enabling correlation. Did that IP address that just hit your honeypot also scan production systems? That's valuable context.
Credential management gets interesting. Some teams deliberately place documents on production systems that mention honeypot credentials. When attackers compromise a real server, find those documents, and try the credentials, they walk straight into the trap. Bonus: you now know which production system was compromised based on which credentials got used.
Maintenance can't be neglected. Update honeypot configurations periodically to match your current production environment. Upgrading to a new database version in production? Update your database honeypots too. Attackers who discover your honeypots run outdated software that doesn't match your actual infrastructure might smell a rat.
Documentation proves critical for legal and operational reasons. Maintain detailed records of honeypot locations, purposes, and configurations. Document your isolation measures and monitoring procedures. This paperwork becomes essential during security audits or if you ever face legal questions about your security practices.
Consider expanding gradually based on results. Maybe simulated-service honeypots prove valuable, so you deploy full-system honeypots for deeper analysis of sophisticated threats. Companies facing targeted attacks might create highly customized honeypots that perfectly mimic their crown jewel assets.
Avoid rookie mistakes like insufficient isolation. That's how attackers pivot from your honeypot into production systems. Honeypots need separate network segments with strict controls preventing them from initiating connections to real infrastructure or external systems.
Another common error? Deploying honeypots without allocating analyst time. Honeypots generate data that requires human interpretation. Someone must review logs, identify patterns, and translate findings into actionable defenses. Deploying more honeypots than you can effectively monitor wastes money and effort.
How honeypot cyber security works in practice scales with organizational maturity. Small companies might deploy one simulated-service honeypot and review logs weekly. Enterprises might operate dozens across multiple network segments, with automated analysis and real-time alerting. Match your implementation to available resources rather than overcommitting.

Author: Marcus Halbrook;
Source: williamalmonte.net
Frequently Asked Questions About Honeypot Cyber Security
Honeypot cyber security fundamentally changes how organizations think about defense. Instead of only blocking threats, you're actively gathering intelligence about adversary tactics. The insights from honeypot interactions inform defensive strategies, expose emerging threats, and provide advance warning of compromise attempts that might otherwise go unnoticed.
Success requires thoughtful planning, adequate resources, and proper integration with broader security operations. Start with manageable deployments—typically simulated-service honeypots monitoring common threats—then expand based on results and capacity. The objective isn't building the most elaborate honeypot network possible but deploying systems that generate actionable intelligence aligned with your security goals.
Attack techniques keep evolving, and adversaries keep getting better. Honeypots will continue providing value because they flip the script—attackers must execute perfectly while defenders only need to catch one mistake. In an environment where breaches seem inevitable, honeypots deliver the early warning and detailed intelligence necessary for effective response and damage minimization.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.