Cybersecurity team conducting a tabletop exercise in a conference room
Cybersecurity Tabletop Exercise Guide
A cybersecurity tabletop exercise is a structured, discussion-based session where key stakeholders simulate their response to a hypothetical security incident without actually deploying technical resources or activating emergency procedures. Think of it as a rehearsal for your incident response plan—participants walk through their roles, decisions, and communication protocols in a low-pressure environment.
The cybersecurity tabletop exercise explained simply: your team gathers around a table (or on a video call), a facilitator presents a realistic scenario such as a ransomware attack, and participants discuss how they would respond at each stage. No systems are taken offline, no actual containment happens, but the conversations reveal gaps in procedures, unclear responsibilities, and communication breakdowns before a real crisis hits.
Organizations conduct these exercises for several reasons. First, they validate whether incident response plans actually work in practice. A document sitting in SharePoint looks comprehensive until someone asks, "Who exactly calls our cyber insurance provider?" and three people give different answers. Second, tabletop exercises build muscle memory for decision-making under pressure. When executives have already debated whether to pay a ransom in a simulated scenario, they make faster, more confident decisions during an actual attack.
These exercises differ fundamentally from other security drills. A penetration test evaluates technical defenses by attempting to breach systems. A red team exercise involves simulated attackers trying to achieve specific objectives while defenders respond in real-time. A full-scale incident response drill activates actual procedures, potentially taking systems offline and mobilizing response teams. Tabletop exercises sit at the opposite end of the spectrum—purely discussion-based, designed for learning rather than testing, and intentionally low-stakes to encourage honest participation.
The most valuable outcome from tabletop exercises isn't finding the right answers—it's discovering which questions your team hasn't even thought to ask yet.We've run exercises where senior leaders realized they didn't know basic facts like where our backup data centers are located or who has authority to authorize emergency expenditures. Those gaps don't show up in audits, but they paralyze response during actual incidents
— Marcus Chen
The cybersecurity tabletop exercise basics come down to three elements: a realistic scenario, the right participants, and structured facilitation. Without realism, participants dismiss the exercise as irrelevant. Without the right people in the room, you can't identify cross-departmental coordination issues. Without skilled facilitation, discussions either stall or devolve into technical debates that miss strategic decision points.
How Cybersecurity Tabletop Exercises Work
Understanding how cybersecurity tabletop exercise works requires breaking down the process into distinct phases, each with specific objectives and deliverables.
Pre-Exercise Planning and Objectives
Planning begins four to six weeks before the actual exercise. The planning team—typically the security manager, a facilitator, and someone from organizational leadership—defines clear objectives. Weak objectives sound like "test our incident response plan." Strong objectives specify measurable outcomes: "Identify decision points requiring executive approval," "Validate communication protocols with legal counsel," or "Determine whether our documentation supports after-hours response."
Next comes scenario selection. The chosen scenario must align with your organization's actual risk profile. A healthcare provider should focus on ransomware targeting patient records, not industrial control system attacks. The scenario needs enough complexity to generate meaningful discussion but shouldn't overwhelm participants with technical minutiae. A 3-4 page scenario document works well—enough detail to feel real, concise enough that participants absorb it quickly.
Materials preparation includes the scenario document, a timeline of "injects" (new information revealed as the scenario progresses), discussion questions for each phase, and a participant guide explaining the exercise format. The facilitator prepares these injects carefully—they're the mechanism for introducing complications, time pressure, and decision points. An inject might read: "It's now 2:00 PM, four hours after initial detection. Your managed security provider reports the attackers have accessed the finance database. The CFO is asking whether to notify customers. What's your decision and rationale?"
Scheduling matters more than most organizations realize. Tuesday through Thursday mornings typically work best—Monday mornings bring weekend backlog, Friday afternoons lose attention to weekend plans. Block 2.5 to 3 hours minimum. Rushing through a tabletop exercise in 90 minutes defeats the purpose; meaningful discussion takes time. Send calendar invitations six weeks out with "required" status for critical participants.
Facilitating the Scenario Discussion
The exercise begins with the facilitator setting ground rules: this is a learning environment, not a performance evaluation. Participants should think out loud, challenge assumptions, and acknowledge uncertainty. The facilitator emphasizes that there are no "gotcha" moments—the goal is discovering gaps, not proving competence.
The facilitator presents the initial scenario, giving participants 5-10 minutes to read and absorb details. Then the discussion begins: "It's Monday morning, 9:30 AM. Your security analyst reports suspicious encrypted file activity on multiple workstations. What are your first three actions, and who takes them?"
Effective facilitation means controlling pace without stifling discussion. When conversations get too technical ("We'd check the EDR logs for process injection indicators"), the facilitator redirects: "Assume your technical team is doing that. Meanwhile, it's been 30 minutes. Does anyone need to be notified yet?" When participants rush to solutions, the facilitator introduces complications: "Before you can isolate those systems, the help desk reports 40 users calling about locked files."
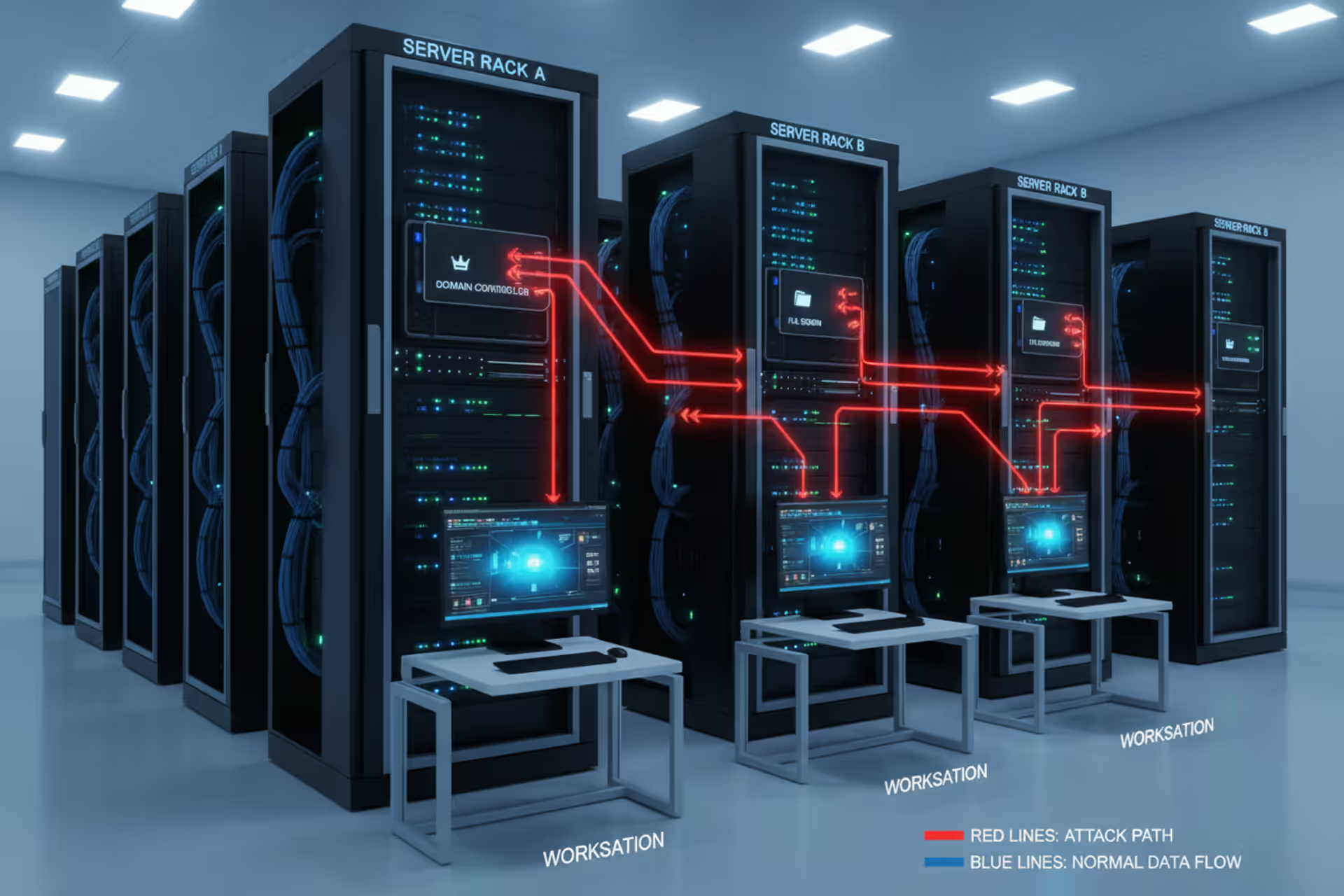
The facilitator uses injects to advance the scenario through phases: detection, containment, eradication, recovery, and post-incident activities. Each phase brings new decision points. During containment, participants might debate whether to shut down email servers. During recovery, they might discover their backup restoration process requires a vendor who doesn't offer weekend support. These discoveries are the exercise's value—better to learn about the vendor limitation in a tabletop than during an actual incident.
Note-taking is critical. A designated scribe captures key discussion points, identified gaps, unclear responsibilities, and action items. These notes become the foundation for the post-exercise report.

Author: Daniel Prescott;
Source: williamalmonte.net
Post-Exercise Analysis
The debrief happens immediately after the scenario concludes, while observations are fresh. The facilitator asks open-ended questions: "What surprised you?" "Where did our procedures work well?" "What would have stopped us from responding effectively?" Participants often identify issues they didn't notice during the heat of discussion.
Within one week, the planning team produces a written report documenting findings, gaps, and recommendations. Strong reports organize findings by category: procedural gaps (missing documentation), technical gaps (tools or capabilities needed), communication gaps (unclear notification processes), and training gaps (skills or knowledge needed). Each finding includes specific, actionable recommendations with assigned owners and target completion dates.
The real test of a tabletop exercise isn't the discussion—it's whether identified gaps get fixed. Organizations that treat the report as a compliance checkbox waste their investment. Effective organizations assign gap remediation to specific people, track progress in regular security meetings, and verify completion before the next exercise.
Common Scenarios Used in Tabletop Exercises
Selecting the right scenario determines whether your exercise generates useful insights or wastes everyone's time. The scenario should reflect threats your organization actually faces, with complexity appropriate to participants' experience level.
| Scenario Name | Primary Threat | Key Stakeholders Involved | Typical Duration | Difficulty Level |
| Ransomware Attack | Encrypted systems, ransom demand, operational disruption | IT, executives, legal, communications, finance | 2.5-3 hours | Intermediate |
| Data Breach (Customer PII) | Unauthorized access to sensitive data, regulatory notification requirements | IT security, legal, compliance, PR, customer service | 2-3 hours | Intermediate |
| Insider Threat | Malicious employee exfiltrating intellectual property | IT security, HR, legal, affected business unit leaders | 2-2.5 hours | Advanced |
| DDoS Attack | Service unavailability, potential extortion | IT operations, security, communications, customer service | 2 hours | Beginner |
| Supply Chain Compromise | Third-party vendor breach affecting your systems | IT security, procurement, vendor management, legal | 2.5-3 hours | Advanced |
| Business Email Compromise | Executive impersonation leading to fraudulent wire transfer | Finance, IT security, legal, affected executives | 2 hours | Beginner |
Ransomware scenarios remain the most common choice, and for good reason—they're the threat most organizations will eventually face. A well-designed ransomware scenario includes decision points around system isolation (do you shut down the entire network or just affected segments?), ransom payment (who has authority to decide?), regulatory notification (what's the timeline?), and communication (what do you tell employees, customers, and media?). The scenario should introduce complications: backups that are also encrypted, attackers threatening to publish stolen data, or discovery that the initial infection happened weeks earlier.
Data breach scenarios focusing on customer or patient information force organizations to confront regulatory requirements under pressure. These exercises reveal whether teams understand notification timelines, who drafts customer communications, and how to coordinate with regulators. A realistic inject might introduce uncertainty: "Forensics suggests 50,000 to 200,000 records were accessed, but they can't be more specific. Your notification deadline is in 48 hours. What do you report?"
Insider threat scenarios work well for organizations with valuable intellectual property or sensitive operational data. These exercises surface uncomfortable questions: When does HR get involved? What evidence is needed before confronting an employee? How do you preserve evidence without tipping off the suspect? The scenario might involve an employee who's given notice and is now accessing unusual files, or a contractor whose behavior concerns coworkers.
DDoS attack scenarios serve as good introductory exercises for organizations new to tabletops. They're technically simpler than ransomware, with clearer response paths, but still generate valuable discussion around communication, vendor coordination (contacting your ISP or DDoS mitigation service), and business continuity.
Supply chain compromise scenarios have gained importance as organizations recognize third-party risk. These exercises explore questions like: How do you even detect that a vendor breach has affected you? Who has authority to suspend vendor access? What contractual obligations do you have to notify the vendor? The scenario might reveal that no one knows which vendors have access to what systems.

Author: Daniel Prescott;
Source: williamalmonte.net
Who Should Participate in a Tabletop Exercise
The participant list makes or breaks your exercise. Too narrow, and you miss critical perspectives. Too broad, and discussion becomes unwieldy.
The core team always includes IT security leadership—the CISO or security manager who owns incident response. These participants understand technical response capabilities and can answer questions about security tools, forensics capabilities, and technical procedures. However, an exercise with only IT security participants is a wasted opportunity.
Executive participation is non-negotiable for scenarios involving major business decisions. When the scenario reaches "Do we pay the ransom?" or "Do we take systems offline during business hours?" you need the people who would actually make those calls. This typically means the CEO, COO, or CFO. Their participation also signals organizational priority—when the CEO attends, everyone takes it seriously.
Legal counsel must participate in any scenario involving regulatory requirements, law enforcement notification, or contractual obligations. Attorneys identify legal implications that technical staff might miss: notification requirements under various state laws, attorney-client privilege considerations when discussing the incident, or contractual penalties for service disruptions. For organizations with in-house counsel, they should attend. For smaller organizations using outside counsel, consider inviting them or at least briefing them on findings afterward.
Human resources belongs in scenarios involving insider threats, but also in any scenario affecting employee communication or safety. HR can address questions about employee notification, remote work policies during an incident, or handling employees who might be impacted by compromised payroll systems.
Communications or public relations staff are critical for any scenario that might become public. They guide discussion on media statements, customer notification, social media monitoring, and stakeholder communication. The exercise often reveals that no one has thought about who monitors social media for customer complaints during an outage, or who's authorized to speak to reporters.
Finance participation matters for scenarios involving ransom payments, emergency expenditures, cyber insurance claims, or revenue impact. The CFO or controller can answer whether the organization has authority to make emergency purchases, how quickly insurance can be contacted, or what financial reporting obligations exist.
Business unit leaders should participate when the scenario affects their operations. A ransomware attack on manufacturing systems requires the plant manager's input. A breach of customer data needs the customer service director's perspective. These participants ground the exercise in operational reality—they're the ones who know that "just switch to manual processes" isn't feasible because no one under 50 knows the manual procedures.
External partners sometimes participate, particularly managed security service providers, incident response retainers, or critical vendors. Their participation clarifies what services they actually provide during an incident, response timeframes, and coordination procedures.
Aim for 8-15 participants. Fewer than eight limits perspective; more than fifteen makes discussion difficult to manage. For larger organizations needing broader participation, consider running multiple exercises for different audiences or creating observer roles for people who attend but don't actively participate.

Author: Daniel Prescott;
Source: williamalmonte.net
Planning Your First Tabletop Exercise
Organizations planning their first tabletop exercise face a chicken-and-egg problem: you need experience to plan a good exercise, but you need to run an exercise to gain experience. This cybersecurity tabletop exercise guide provides a practical roadmap.
Start with modest objectives. Your first exercise should focus on basic response procedures and communication, not complex technical decisions or advanced threat scenarios. Choose a straightforward scenario—ransomware or DDoS work well—that participants can grasp quickly. Save insider threats and supply chain compromises for later exercises after your team has experience with the format.
Select an experienced facilitator. The facilitator guides discussion, introduces injects at appropriate times, redirects unproductive tangents, and ensures all participants contribute. For first exercises, consider hiring an external facilitator with tabletop experience. They bring objectivity, established credibility, and practiced skills at managing group dynamics. Budget $3,000-$8,000 for an external facilitator who will also help with scenario development and produce the after-action report. If budget doesn't allow external help, designate your most experienced security professional who has strong meeting facilitation skills and won't be defensive when gaps emerge.
Build your scenario from real incidents, but adapt them to your environment. Start with a published incident report from a similar organization—the Verizon Data Breach Investigations Report and US-CERT alerts provide good source material. Modify the scenario to match your technology environment, business model, and risk profile. A scenario involving compromised point-of-sale systems makes sense for retail, not for a law firm.
Create a detailed timeline. Your scenario document should specify when events occur: "Monday, 6:45 AM: Night shift security analyst notices unusual encrypted file activity." The timeline creates urgency and forces discussion of after-hours response, escalation delays, and resource availability at different times.
Prepare 5-7 injects that introduce complications at natural break points. Injects might reveal that backups are corrupted, that attackers are demanding ransom, that a reporter has called asking about service disruptions, or that a key vendor is unreachable. Write injects as short, factual statements: "It is now 11:30 AM. Your managed security provider reports that the attackers have accessed the HR database containing employee personal information including Social Security numbers. What actions do you take?"
Schedule the exercise at least six weeks out, and send reminders two weeks before and three days before. Include the participant guide with your invitation so people know what to expect. The guide should explain that this is a discussion exercise, not a test, and that the goal is learning and improvement.
Arrange logistics thoughtfully. A conference room with a large table where everyone can see each other works better than a classroom-style setup. Provide name tents—in the stress of discussion, people forget names. Have printed copies of the scenario for everyone; don't rely on everyone reading on laptops. Eliminate distractions: no side conversations, minimal laptop use, phones on silent.
Plan for 2.5-3 hours. A typical timeline: 15 minutes for introductions and ground rules, 10 minutes for scenario reading, 90-120 minutes for scenario discussion with injects, 30 minutes for debrief. Don't try to compress this into 90 minutes—you'll rush through valuable discussion.
Assign a scribe who won't actively participate in the scenario. This person captures key discussion points, identified gaps, action items, and notable quotes. Their notes form the basis for your after-action report.
Set expectations beforehand. Tell participants this is a learning exercise where honest discussion is valued more than having all the answers. Emphasize that identifying gaps is success, not failure—every gap found in the exercise is a problem that won't surprise you during a real incident.

Author: Daniel Prescott;
Source: williamalmonte.net
Mistakes to Avoid During Tabletop Exercises
Organizations waste time and money on poorly executed tabletop exercises. These common mistakes undermine the exercise's value.
Creating unrealistic scenarios is the most frequent error. A scenario where attackers breach your network, encrypt all systems, and demand ransom within 30 minutes isn't realistic—real attacks unfold over days or weeks. Unrealistic scenarios lead participants to dismiss the exercise: "That would never happen here." Ground scenarios in actual threat intelligence for your industry. If you're a small accounting firm, don't build a scenario around nation-state attackers targeting your industrial control systems.
Inviting the wrong participants wastes everyone's time. An exercise full of technical staff will produce detailed technical discussion but miss strategic and communication issues. An exercise with only executives will stall when technical questions arise. Match participants to the scenario and objectives. If your objective is testing executive decision-making, you need executives. If you're testing technical coordination, you need technical staff.
Treating the exercise as a test rather than a learning opportunity kills honest participation. When the facilitator acts like a teacher grading students, participants become defensive and hide gaps rather than acknowledging them. The facilitator must create psychological safety: "We're here to find problems with our procedures, not with people." Avoid language like "You should have known..." or "The correct answer is..." Instead use "What information would help you make that decision?" or "What would need to be in place for that to work?"
Skipping the debrief is like leaving a meeting without action items. The debrief is where participants reflect on what they learned, identify patterns in the gaps that emerged, and commit to improvements. Without a debrief, everyone leaves with different takeaways and nothing changes.
Failing to follow up on identified gaps is perhaps the most damaging mistake. When participants see that nothing changed after the last exercise, they view future exercises as checkbox compliance activities. The after-action report must include specific, assigned, time-bound action items: "Legal will draft incident notification templates by March 15" not "Improve notification procedures." Track these items to completion.
Making scenarios too complex for participants' experience level frustrates everyone. If your organization has never run a tabletop exercise, don't start with a sophisticated supply chain compromise involving multiple vendors and international regulatory requirements. Build complexity gradually as participants develop familiarity with the format.
Poor time management ruins exercises. A facilitator who spends 45 minutes on the initial detection phase leaves no time for containment, recovery, and post-incident activities. The facilitator must watch the clock and move discussion forward: "We could discuss detection methods for another hour, but let's assume detection is complete and move to containment decisions."
Allowing technical rabbit holes to derail strategic discussion is common when technical staff dominate participation. Someone asks "How would the attackers have bypassed our EDR?" and suddenly everyone is debating technical controls instead of discussing business decisions. The facilitator must redirect: "That's a great question for post-exercise analysis. For now, assume the breach happened. What's your containment strategy?"
Ignoring organizational politics creates unrealistic discussion. If your actual organization requires three levels of approval for emergency expenditures, don't handwave that away during the exercise. Confronting these bureaucratic realities in the exercise helps build the case for streamlined emergency procedures.
Frequently Asked Questions
Cybersecurity tabletop exercises represent one of the highest-return investments in incident preparedness. For a modest commitment of time and resources, organizations discover critical gaps in procedures, clarify responsibilities, and build decision-making confidence among response teams—all before facing a real crisis.
The most successful exercises share common characteristics: realistic scenarios grounded in actual threats, the right mix of participants from across the organization, skilled facilitation that keeps discussion productive, and rigorous follow-up that converts identified gaps into concrete improvements. Organizations that treat exercises as learning opportunities rather than compliance checkboxes see the greatest value.
Start simple if you're new to tabletop exercises. Choose a straightforward ransomware or DDoS scenario, invite 8-12 key stakeholders, and focus on basic response procedures and communication. As your organization gains experience, increase complexity with insider threats, supply chain compromises, or scenarios combining multiple threat types.
The after-action report determines whether your exercise investment pays dividends. Assign specific owners to each identified gap, set realistic completion dates, and track remediation progress in regular security meetings. An exercise that identifies ten gaps but fixes eight is infinitely more valuable than an exercise that identifies twenty gaps and fixes none.
Remember that incident response is fundamentally a team sport requiring coordination across technical, legal, communications, and business functions. Tabletop exercises are where these diverse stakeholders learn to work together under pressure, develop shared understanding of priorities and trade-offs, and build the relationships that enable effective response when a real incident strikes.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.