Cybersecurity incident response team monitoring systems in a security operations center
Cyber Security Incident Response Plan Guide
When a ransomware attack locks down your systems at 3 a.m., the difference between a contained incident and a company-ending disaster often comes down to one thing: whether you have a documented response plan that your team knows how to execute.
A cyber security incident response plan is your organization's playbook for handling security breaches, data leaks, malware infections, and other digital threats. Without one, teams scramble, critical evidence gets destroyed, and recovery costs skyrocket. With a solid plan in place, you can detect threats faster, minimize damage, and get back to business with less downtime and expense.
What Is a Cyber Security Incident Response Plan
A cyber security incident response plan is a structured set of procedures that defines how an organization detects, responds to, and recovers from security incidents. Think of it as a fire drill for digital threats—it documents who does what, when they do it, and how they communicate during a crisis.
The purpose extends beyond just reacting to breaches. A well-designed plan reduces response time, preserves forensic evidence, maintains compliance with regulations, and protects your organization's reputation. Companies with documented response plans contain breaches 54 days faster on average than those without, according to recent industry analysis.
Organizations need these plans because security incidents are no longer a question of "if" but "when." The average company faces dozens of security events each month, though only a fraction qualify as actual incidents requiring full response activation. Your plan helps teams distinguish between routine alerts and genuine threats that demand immediate action.
Many confuse incident response with disaster recovery, but they serve different purposes. Incident response focuses on addressing active security threats—stopping attackers, containing malware, and investigating breaches. Disaster recovery deals with restoring business operations after catastrophic events like natural disasters, hardware failures, or major outages. Your incident response plan handles the security crisis; disaster recovery gets your business running again afterward.
The cyber security incident response plan basics start with documentation. If your procedures exist only in someone's head, you don't have a plan—you have a single point of failure. Written procedures ensure consistency, enable training, and provide a reference during high-stress situations when memory fails.
How Cyber Security Incident Response Plans Work
Response plans operate on several core principles. First, speed matters—every minute an attacker remains in your systems increases potential damage. Second, coordination beats heroics—successful response requires multiple teams working together, not lone wolves. Third, documentation preserves options—detailed records support legal action, insurance claims, and regulatory compliance.
Plans activate when an incident meets predefined severity thresholds. Not every security alert triggers full response. A single phishing email caught by filters doesn't need the same response as ransomware spreading across your network. Your plan should define clear activation criteria based on factors like data sensitivity, system criticality, number of affected users, and potential business impact.
Multiple stakeholders participate in incident response. The core team typically includes IT security analysts who investigate threats, system administrators who implement containment measures, and an incident commander who coordinates activities. Depending on severity, you might also involve legal counsel, public relations, human resources, executive leadership, and external forensics specialists.
Response plans integrate with your broader security posture. They rely on existing security controls—your firewalls, endpoint protection, and monitoring tools provide the detection capabilities that trigger response. They complement your security policies by defining what happens when policies are violated or controls fail. A strong security posture prevents most incidents; your response plan handles the ones that slip through.
Understanding how cyber security incident response plan works means recognizing it as a living process, not a static document. Each incident teaches lessons that refine your procedures. Regular testing reveals gaps before real attackers exploit them. Updates incorporate new threats, technologies, and business changes.

Author: Vanessa Keaton;
Source: williamalmonte.net
Six Phases of Incident Response
The industry-standard framework divides incident response into six distinct phases, each with specific objectives and activities. This structure, widely adopted from NIST guidelines, provides a repeatable process that works across incident types.
Preparation
Preparation happens before incidents occur. This phase involves building your response team, documenting procedures, deploying detection tools, establishing communication channels, and conducting training exercises.
Concrete preparation steps include creating contact lists with after-hours phone numbers, setting up secure communication channels that function if email is compromised, pre-positioning forensic tools on a dedicated response workstation, and establishing relationships with external resources like forensics firms and legal counsel.
Many organizations skip tabletop exercises—simulated incidents where teams walk through response procedures. These low-cost exercises reveal confusion about roles, missing tools, and procedural gaps without the pressure of an actual breach. Run at least two per year, varying the scenario each time.

Author: Vanessa Keaton;
Source: williamalmonte.net
Identification and Detection
Detection determines whether a security event qualifies as an incident requiring response. Your monitoring tools generate thousands of alerts; this phase separates signal from noise.
Analysts examine alerts, correlate data from multiple sources, and assess scope. Key questions include: Is this a false positive? What systems are affected? What data is at risk? Is the threat still active? Initial detection might take minutes, but thorough identification often requires hours as teams uncover the full extent of compromise.
Document everything from the start. Note who discovered the incident, what they observed, and what time detection occurred. These details become critical for forensics, compliance reporting, and legal proceedings.
Containment
Containment stops incident spread while preserving evidence for investigation. The goal is limiting damage without destroying forensic artifacts that reveal how attackers got in.
Short-term containment implements immediate measures like isolating infected systems, blocking malicious IP addresses, or disabling compromised user accounts. A server spreading ransomware gets disconnected from the network immediately, even if that causes temporary service disruption.
Long-term containment involves temporary fixes that allow some business operations to continue while you prepare for complete eradication. You might segment networks, implement additional monitoring, or deploy clean backup systems in parallel with investigating compromised ones.
Containment decisions involve trade-offs. Shutting down systems stops attackers but also halts business operations. Leaving systems running preserves business continuity but risks additional damage. Your plan should provide decision criteria based on incident severity and affected assets.
Eradication
Eradication removes the threat from your environment. This means deleting malware, closing vulnerabilities that allowed initial access, and eliminating attacker persistence mechanisms.
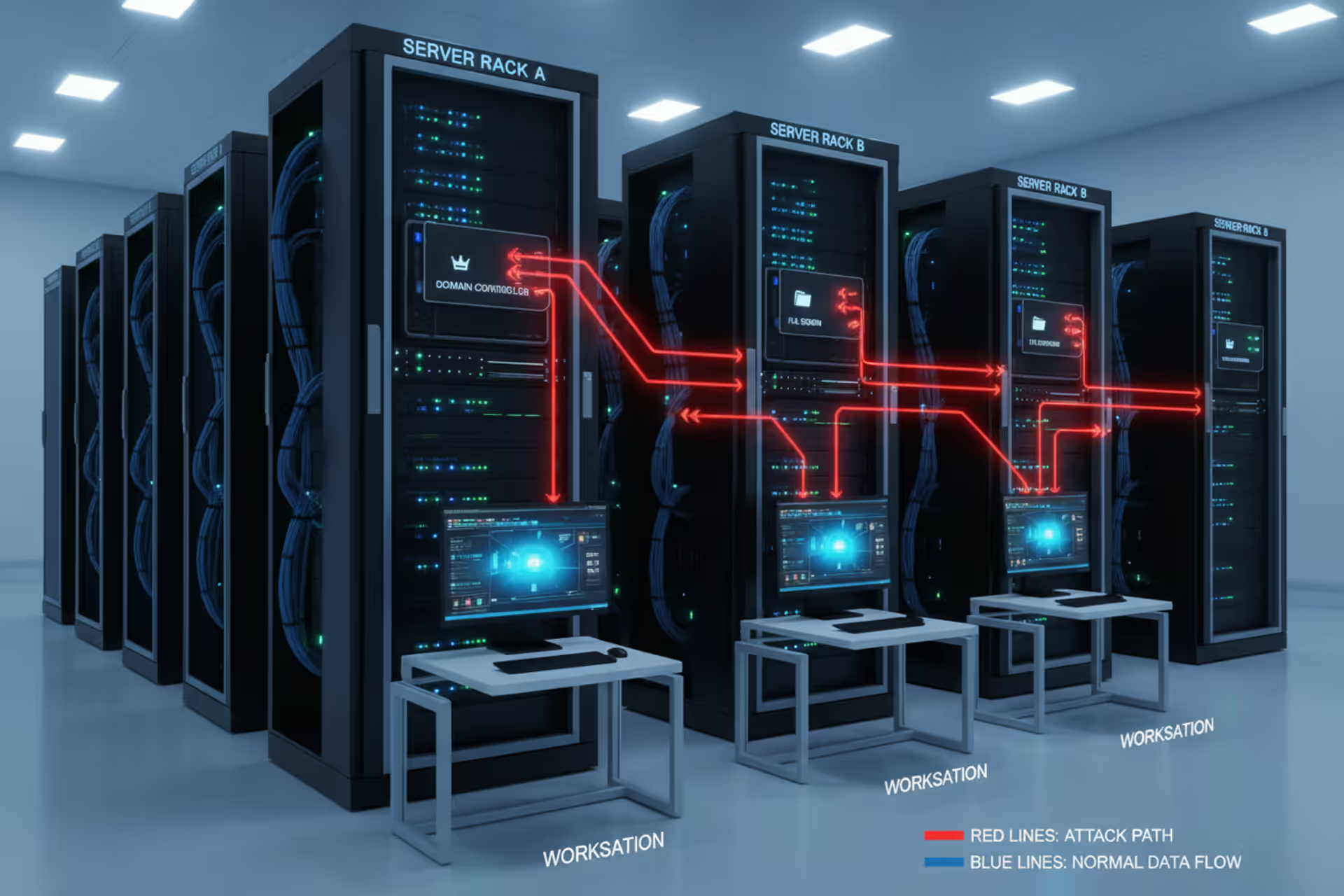
Thorough eradication requires understanding the full attack path. Attackers often establish multiple access points—removing obvious malware while missing a backdoor means they'll return. Forensic analysis identifies all compromised systems, malicious files, registry changes, and unauthorized accounts.
For sophisticated attacks, eradication might involve rebuilding systems from known-good backups or clean installations rather than attempting to clean infected systems. The cost of rebuilding often proves less than the risk of missing hidden malware.
Recovery
Recovery restores systems to normal operations while monitoring for signs that attackers return. This phase includes restoring data from backups, rebuilding compromised systems, resetting credentials, and implementing additional security controls.
Phased recovery reduces risk. Bring systems back online gradually, starting with the most critical and least compromised. Monitor restored systems intensively for several weeks—sophisticated attackers often attempt to regain access after initial ejection.
Validation confirms that systems are truly clean before returning to production. This might include vulnerability scans, integrity checks, and behavioral monitoring. Don't skip validation because business pressure demands immediate restoration; premature recovery often leads to reinfection.
Lessons Learned
The lessons learned phase happens within two weeks of incident closure while details remain fresh. The response team, along with affected business units, conducts a structured review of what happened, what worked, and what needs improvement.
Effective reviews focus on process improvement, not blame. Questions to address include: What was our detection time? Did we have the right tools and access? Were communication procedures effective? What would we do differently? What security controls should we add?
Document findings and assign specific action items with owners and deadlines. An incident that doesn't result in plan updates represents a missed learning opportunity. Track action item completion—recommendations that languish unimplemented won't help during the next incident.
Key Components Every Response Plan Must Include
Comprehensive response plans share several essential elements that enable effective action during crises.
Roles and responsibilities define who does what during response. Designate an incident commander who makes decisions and coordinates activities. Identify technical leads for investigation, containment, and recovery. Specify who communicates with executives, legal, public relations, and external parties. Include backup personnel for each role—incidents don't respect vacation schedules.
Communication protocols establish how teams share information during response. Define which communication channels to use for different scenarios—your primary email system won't work if it's compromised. Specify update frequency, who receives notifications, and what information to share. Create templates for common communications to save time during crises.
Escalation procedures clarify when to expand response efforts. Define severity levels with specific escalation triggers. A minor phishing incident might stay within the security team, while ransomware affecting production systems requires executive notification and external assistance. Include criteria for involving law enforcement, which varies based on incident type and jurisdiction.
Documentation requirements specify what information to record and how. Standard incident forms capture consistent data across events. Required details typically include incident timeline, affected systems and data, actions taken, personnel involved, and business impact. Proper documentation supports compliance, insurance claims, and potential legal action.
Tools and resources list the technical capabilities and external contacts needed for response. This includes forensic software, backup systems, communication platforms, and contact information for vendors, forensics firms, legal counsel, and law enforcement. Verify contact information quarterly—outdated phone numbers waste precious time during incidents.
Cyber Security Incident Response Plan Examples by Industry
Response plan specifics vary by industry due to different threats, regulatory requirements, and business models.
Healthcare organizations face unique challenges under HIPAA regulations. A response plan example might address a scenario where an employee's laptop containing patient records is stolen. The plan would specify immediate steps: remote wipe if possible, assess what data was exposed, notify the privacy officer within one hour, document the incident per HIPAA requirements, and determine if breach notification to patients and HHS is required. Healthcare plans often emphasize protecting patient privacy even during response activities.
Financial services firms deal with strict regulatory oversight and sophisticated attackers. A bank's plan might detail response to compromised online banking credentials. Procedures would include immediate account suspension, customer notification, transaction review for fraud, law enforcement notification if theft occurred, and regulatory reporting to agencies like the OCC or state banking regulators within required timeframes. Financial plans typically include detailed evidence preservation procedures for potential prosecution.
Retail and e-commerce companies prioritize protecting payment card data under PCI DSS requirements. An example scenario involves point-of-sale malware capturing card data. The response includes isolating affected terminals, notifying payment processors and card brands within specified timeframes, engaging a PCI forensic investigator, and potentially notifying affected customers. Retail plans often address the public relations aspects of breaches that affect customers directly.
Manufacturing firms increasingly face operational technology threats that can halt production. A plan might address ransomware affecting industrial control systems. Response procedures would include isolating affected production lines, switching to manual operations if possible, assessing safety implications, and determining whether to pay ransom or restore from backups. Manufacturing plans often include coordination with operational technology specialists, not just IT security.

Author: Vanessa Keaton;
Source: williamalmonte.net
Small businesses need simpler plans than enterprises but still require documented procedures. A small business plan might be 15 pages instead of 150, with fewer specialized roles and greater reliance on external assistance. The key difference is scalability—small business plans often emphasize when to call external help rather than attempting complex forensics internally. However, basic elements like communication procedures, escalation criteria, and backup restoration steps remain essential regardless of company size.
Common Mistakes When Building an Incident Response Plan
Several predictable mistakes undermine response effectiveness.
Lack of testing tops the list. Plans that look comprehensive on paper often fail during actual incidents because nobody has practiced the procedures. Untested communication channels don't work, assigned personnel have changed roles, documented tools aren't actually available, and procedures contain errors that only become apparent during execution. Test your plan at least annually through tabletop exercises and technical simulations.
Unclear roles create confusion about who has authority to make critical decisions. Multiple people think they're in charge, or worse, everyone waits for someone else to act. Define a clear command structure with decision-making authority. Specify who can authorize system shutdowns, approve external communications, and commit budget for response activities.
No communication plan leaves teams improvising how to coordinate during crises. This becomes critical when primary systems are compromised. Establish out-of-band communication channels—if your email is down, how does the team coordinate? Options include dedicated conference bridges, secure messaging apps on personal devices, or even a phone tree for critical notifications.
Ignoring compliance requirements creates legal and regulatory problems. Different regulations mandate specific response activities and timeframes. HIPAA requires breach assessment within 60 days. PCI DSS mandates forensic investigation for card data breaches. GDPR requires notification within 72 hours for certain incidents. Your plan must incorporate these requirements, not treat them as afterthoughts.
Failing to update regularly means plans become outdated as technology, personnel, and threats evolve. The contact list includes people who left the company, documented tools have been replaced, procedures reference systems that no longer exist. Review and update your plan at least annually, and immediately after significant organizational changes like mergers, major system upgrades, or leadership transitions.
How to Create Your Incident Response Plan
Building an effective plan follows a structured process that ensures comprehensive coverage while remaining practical for your organization.
Step 1: Assess risks and priorities. Identify your most critical assets—systems, data, and processes that matter most to business operations. Evaluate threats relevant to your industry and organization. Determine regulatory requirements that apply to your business. This assessment informs where to focus response capabilities.
Step 2: Assemble your response team. Identify personnel to fill key roles: incident commander, technical investigators, system administrators, communications lead, legal liaison. Include representatives from IT, security, legal, HR, and executive leadership. For small organizations, individuals might fill multiple roles, but document who handles each function. Establish relationships with external resources you'll need—forensics firms, legal specialists, public relations consultants.
Step 3: Document procedures. Write step-by-step procedures for each response phase. Use clear, specific language—"disconnect the network cable" not "isolate the system." Include decision trees for common scenarios. Create templates for incident forms, communication messages, and status reports. Keep procedures concise; responders won't read 200-page documents during crises.
Step 4: Establish communication channels. Set up secure communication methods that function if primary systems are compromised. This might include a dedicated conference bridge, encrypted messaging app, or emergency contact list. Define who receives notifications at different severity levels and what information to share. Create communication templates to speed message creation during incidents.
Step 5: Test and refine. Conduct a tabletop exercise where team members walk through responding to a simulated incident. Note what works, what causes confusion, and what's missing. Update procedures based on findings. Run technical tests of specific capabilities like backup restoration or forensic data collection. Schedule regular testing—quarterly for high-risk organizations, at least annually for others.
Additional considerations include integrating your plan with existing security operations, obtaining executive support and budget, arranging training for response team members, and establishing metrics to measure response effectiveness.
Key Components Across Compliance Frameworks
Different regulatory frameworks mandate specific incident response capabilities. Understanding these requirements ensures your plan meets applicable compliance obligations.
| Framework | Detection Requirements | Response Timeframe | Documentation | Notification Requirements |
| NIST CSF | Continuous monitoring, anomaly detection | Immediate containment | Incident tracking, lessons learned | Based on organizational policy |
| ISO 27001 | Security event logging, incident criteria | Defined in procedures | Incident records, evidence preservation | Per organizational requirements |
| HIPAA | Audit controls, access monitoring | Immediate risk assessment | Incident documentation, breach analysis | 60 days for breach determination, notification if required |
| PCI DSS | Intrusion detection, file integrity monitoring | Immediate response | Detailed incident logs, forensic reports | Immediate notification to payment brands for card data breaches |
| SOC 2 | Security monitoring, incident detection | Timely response per policy | Incident records, remediation tracking | Customer notification per agreements |
This comparison shows that while specific requirements vary, all frameworks expect documented procedures, timely response, thorough documentation, and appropriate notifications. Your plan should address the most stringent requirements applicable to your organization.
The organizations that weather incidents best are those that prepared before the crisis hit. You cannot develop an effective response plan while systems are burning. The time to build relationships with forensics teams, establish communication procedures, and train your staff is now, when you have the luxury of thoughtful planning rather than the pressure of an active breach
— Kevin Mandia
This perspective from one of the industry's most respected incident response leaders emphasizes that preparation determines outcome. Organizations that invest in planning, testing, and training before incidents occur consistently achieve better results—faster detection, more effective containment, and lower overall costs.
Frequently Asked Questions
A cyber security incident response plan transforms panic into process. When incidents occur—and they will—your documented procedures guide teams through detection, containment, eradication, and recovery. The difference between organizations that survive incidents and those that suffer catastrophic damage often comes down to preparation.
Start building your plan now if you haven't already. Begin with the basics: define your team, document procedures for the most likely scenarios, establish communication channels, and conduct your first tabletop exercise. Your plan doesn't need to be perfect initially—it needs to exist and provide guidance that's better than improvising during a crisis.
For organizations with existing plans, schedule your next test and review. Plans that sit on shelves without regular testing and updates provide false confidence. Verify that contact information is current, procedures reflect your current environment, and team members understand their roles.
Remember that incident response planning is an investment, not an expense. The costs of plan development, testing, and training are minimal compared to the potential losses from a poorly handled incident. Organizations with mature response capabilities consistently report lower breach costs, faster recovery times, and better regulatory outcomes.
Your response plan represents insurance against digital threats. Like any insurance, you hope never to need it, but you'll be grateful to have it when incidents occur. The question isn't whether you can afford to invest in incident response planning—it's whether you can afford not to.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.