Cybersecurity audit workspace with security dashboards and network review screens
Cyber Security Audit Guide
Content
Content
Think of a cyber security audit as a financial audit, but for your digital assets. Instead of accountants examining your books, security professionals dissect your IT environment to verify you're actually protecting what you claim to protect.
Here's what makes audits different from other security activities. Penetration testers try breaking into your systems—they're the burglars testing your locks. Vulnerability scanners identify technical weak spots in software and configurations. Audits? They examine everything: technology, people, processes, policies, and whether what's written in your security manual actually happens in real life.
The examination covers your network setup, who gets access to what, how you handle sensitive information, whether employees know security protocols, your plans for responding to breaches, and even physical safeguards like locked server rooms. You're getting a complete picture, not just a technical snapshot.
Companies use these evaluations to figure out where they stand right now, spot the gap between their current reality and where they should be, then build practical plans to close those gaps. A retail chain might learn their point-of-sale systems are five years behind on patches—that's actionable intelligence worth having.
One massive misconception needs clearing up immediately. Passing an audit doesn't mean you're bulletproof. It means on that specific day, using that particular framework, you met certain requirements. Hackers evolve daily. Your security posture from March could be compromised by June. That's why smart organizations treat audits as recurring checkpoints, not finish lines.
The real value emerges when auditors find disconnects between policy and practice. Your documentation says all employees completed phishing training, but interviews reveal half your sales team still clicks suspicious links. That's gold—you've identified a concrete problem you can fix before attackers exploit it.
Author: Marcus Halbrook;
Source: williamalmonte.net
Why Businesses Need Cyber Security Audits
Federal and state regulations don't ask nicely—they require documented security reviews for anyone handling protected information. Medical practices face HIPAA scrutiny. Banks and payment processors answer to GLBA and PCI DSS. Companies with European customers must satisfy GDPR requirements regardless of where headquarters sits. Skip these mandates and you're looking at fines starting around $50,000, climbing into millions for serious violations, plus potential operating restrictions.
But let's talk about the scarier motivation: unknown risks. A mid-sized distributor operated for seven years before an audit revealed their wireless network—which delivery drivers used to update routes—had no encryption whatsoever. Anyone in the parking lot could intercept shipment data. They'd been lucky. Luck runs out.
Data breaches now average $4.8 million in total costs when you factor in notification expenses, legal fees, remediation, lost business, and reputation damage. Compare that to $15,000-$75,000 for a solid audit at most mid-sized companies. The math isn't complicated.

Author: Marcus Halbrook;
Source: williamalmonte.net
Insurance changed dramatically after 2024's ransomware surge. Underwriters now require recent audit documentation before issuing cyber liability policies. Companies without current reports face premium increases of 40-60% or outright denial. One manufacturing firm saw their renewal rejected because they couldn't produce audit records from the past 18 months—their coverage lapsed right before a network intrusion cost them $1.2 million.
Your customers care too, especially B2B clients conducting vendor assessments. A SaaS provider lost a $2 million enterprise deal during final negotiations when the buyer's risk team requested third-party audit verification and got crickets. Competitors with documentation won the contract. In tight markets, security proof becomes the tiebreaker.
Executive teams increasingly face personal liability exposure. Shareholders sued three different companies in 2025, alleging board members failed to implement reasonable safeguards. Regular audits demonstrate you took security seriously—critical evidence if litigation ever comes knocking.
How Cyber Security Audits Work
The process follows predictable phases, though details vary based on your industry, size, and what you're trying to accomplish.
Pre-Audit Preparation
You'll start planning 4-6 weeks ahead. Designate someone internally—usually from IT, compliance, or risk management—to coordinate everything. This person becomes the auditor's main contact and handles the avalanche of documentation requests.
What documentation? Network topology maps, security policy manuals, past audit reports if you've done this before, compliance certifications, employee training logs, incident response plans, disaster recovery procedures, and vendor contracts with security clauses. Start gathering early because finding everything takes longer than expected.
Initial meetings define what's actually getting examined. Full enterprise audits examining every system and control can stretch 3-4 weeks. Focused reviews targeting specific compliance requirements or particular systems finish faster. You're balancing thoroughness against cost and operational disruption.
One healthcare network made a critical mistake: they announced the upcoming audit in a panicked email without context. Staff immediately started deleting old files, assuming clutter would look bad. This file purging itself became an audit finding—they'd violated data retention policies. Communicate calmly about what's happening and why.
Audit Execution Phase
Auditors deploy automated scanning tools that probe your network for vulnerabilities, misconfigured systems, and devices that shouldn't be there. These typically run overnight or during slow periods to avoid performance hits. Simultaneously, they're reviewing your documentation and comparing written policies against actual system configurations.
Interviews matter enormously. Auditors talk with IT administrators, department managers, frontline employees, and executives to understand how security actually works versus how it's documented. A credit union discovered during these conversations that tellers routinely shared login credentials during shift changes to avoid the "hassle" of logging in and out—a practice management never knew existed.
Technical testing includes examining firewall rule sets, attempting access with different permission levels, reviewing system logs for gaps or anomalies, and verifying encryption is configured correctly. They'll check whether access controls match job requirements or if people have excessive permissions "just in case."
Physical security gets assessed too. Are server rooms actually locked? Who has access badges? What happens to visitors? Do workstations auto-lock after inactivity? How are old hard drives destroyed? An accounting firm learned their backup tapes sat in an unlocked storage closet accessible to cleaning contractors after hours—a gap nobody had considered.

Author: Marcus Halbrook;
Source: williamalmonte.net
Post-Audit Actions
Findings get compiled into formal reports with severity ratings. Critical issues need immediate attention—like exposed databases or default passwords on admin accounts. High-priority items get 30-day deadlines. Medium-priority improvements might have 90-day windows. Low-priority recommendations are "nice to haves" for future consideration.
Report delivery involves a walkthrough meeting where auditors explain each finding with context. Quality auditors don't just point out problems—they explain business impact and suggest realistic fixes given your budget and resources.
Here's where many companies stumble: they file the report and forget it. Real remediation tracking extends 6-12 months post-audit. Assign owners to every finding. Set concrete deadlines. Monitor progress weekly. Some auditors offer follow-up assessments verifying critical issues were actually resolved, not just marked complete in a spreadsheet.
The audit finishes when vulnerabilities get fixed, not when the report arrives.
Types of Cyber Security Audits
Different audit flavors serve different needs. You'll likely need multiple types over your company's lifetime.
Compliance audits verify you're meeting specific regulatory requirements or certification standards. SOC 2 for service organizations, PCI DSS for anyone processing credit cards, HIPAA for healthcare entities—these follow prescribed checklists and result in official certifications or attestation letters. If you operate in regulated industries or need specific certifications to win business, expect these annually or every six months.
Risk-based audits prioritize threats specific to your situation rather than checking generic boxes. A logistics company with GPS tracking across 200 trucks would emphasize IoT device security. A marketing agency handling campaign data for Fortune 500 clients would focus on intellectual property protection and client data segregation. The audit adapts to your actual risk profile.
Technical audits go deep on infrastructure, applications, and systems. Expect detailed examination of network architecture, server hardening, database security configurations, application code quality, and cloud environment settings. These work well after major infrastructure migrations, following security incidents, or when preparing for mergers where acquirers demand technical due diligence.
Third-party audits evaluate vendors, suppliers, and partners who touch your systems or data. Supply chain attacks jumped 68% between 2024 and 2026—making vendor security critical. These assess whether third parties maintain adequate controls and honor contractual security obligations. Organizations with dozens of vendors often establish rolling audit programs, examining several vendors quarterly.
| Audit Category | What Gets Examined | Works Best For | How Long It Takes |
| Compliance | Adherence to regulations and standards | Industries with legal requirements, certification candidates | 2-4 weeks |
| Risk-Based | Threats unique to your environment | Organizations wanting practical improvements over checkbox exercises | 3-5 weeks |
| Technical | Infrastructure and application security | Companies after major changes or security incidents | 2-6 weeks |
| Third-Party | Vendor and supplier controls | Businesses with complex supply chains | 1-2 weeks each vendor |
What Auditors Examine During a Cyber Security Audit
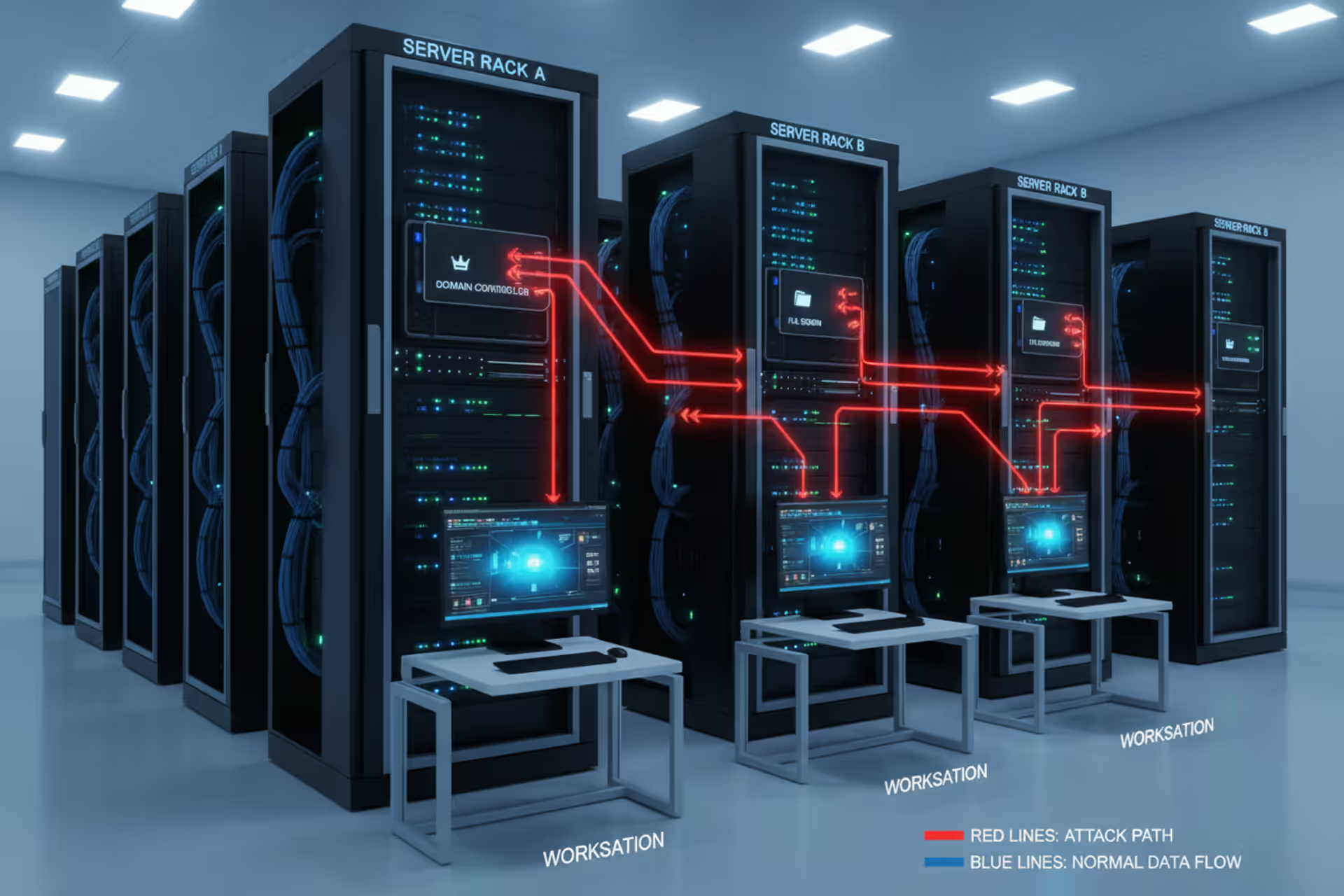
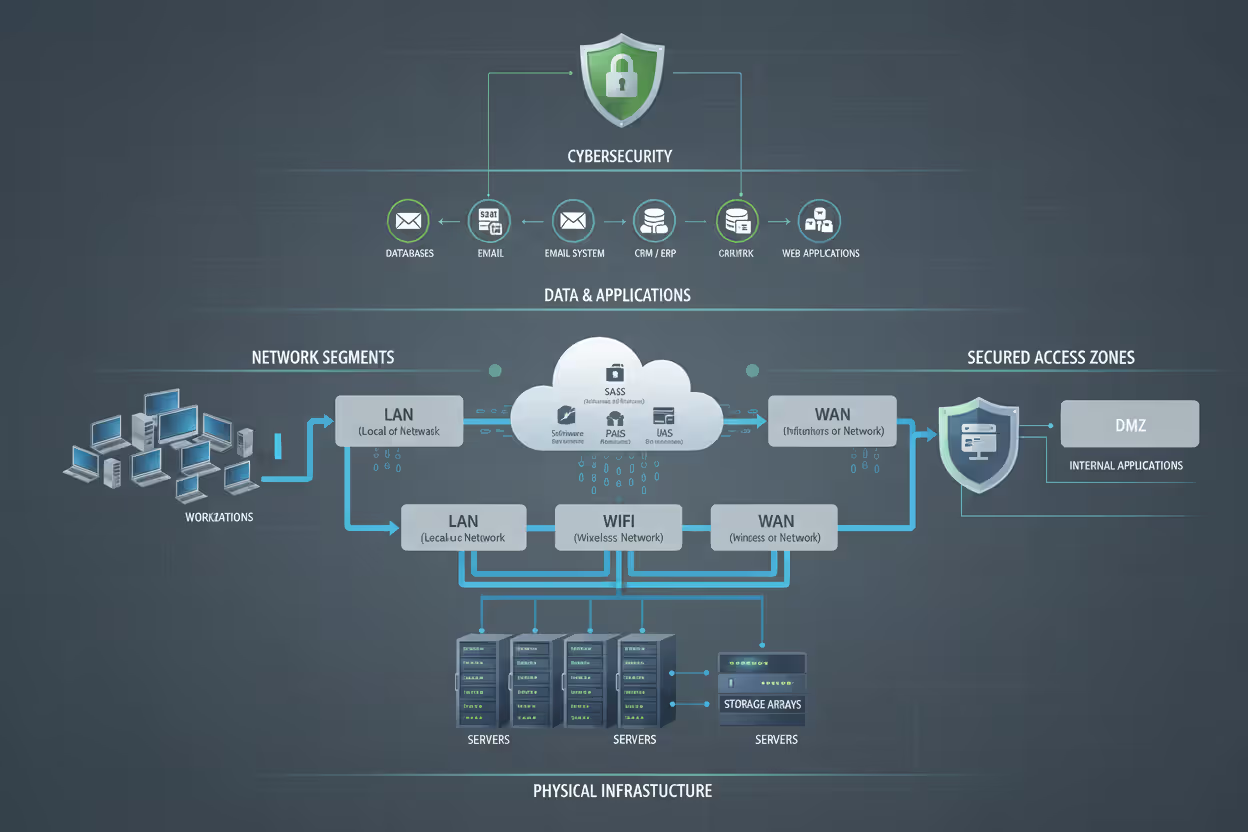
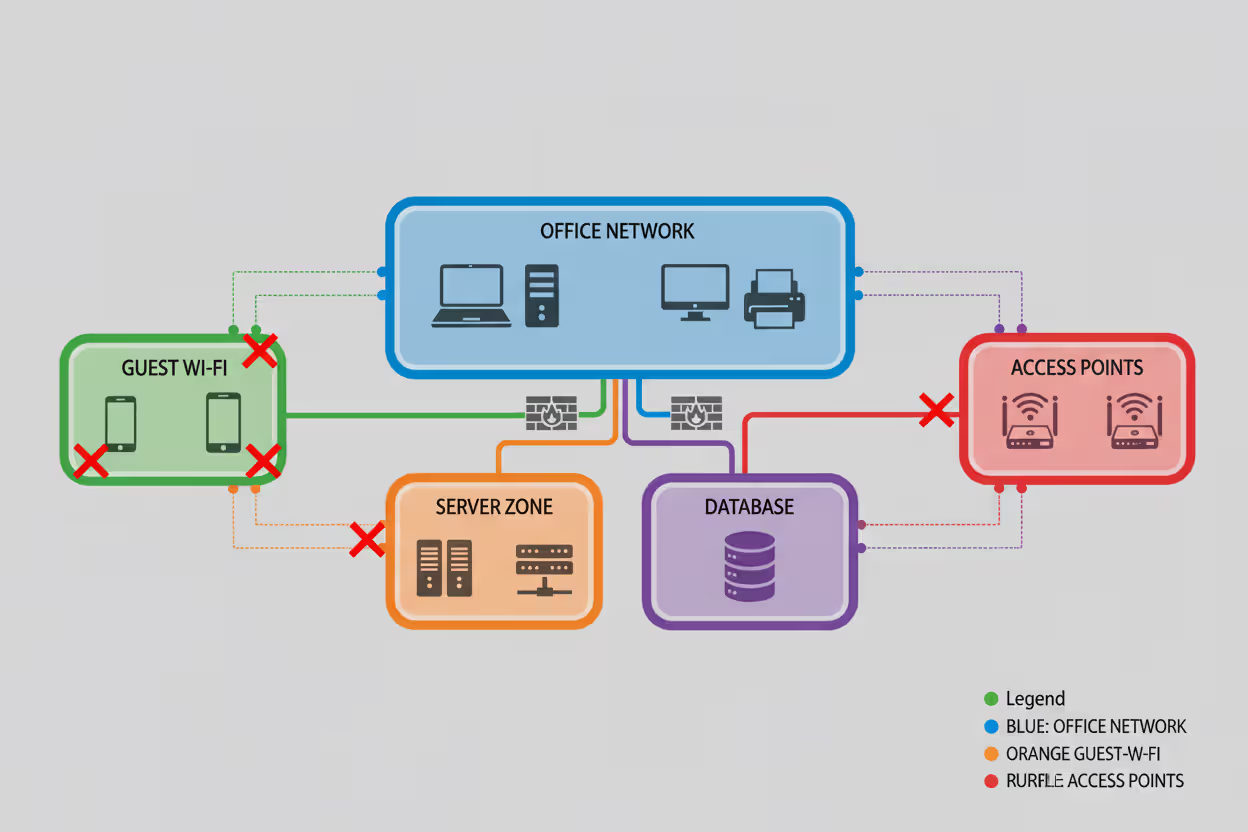
Your network infrastructure gets mapped and tested. Auditors diagram network topology, catalog every connected device (including that forgotten printer in the basement), examine how you've segmented networks, and verify firewall configurations. Proper segmentation means compromising one system doesn't grant access to everything. A law office discovered their guest WiFi—used by clients in the waiting room—had direct access to case management databases. That exposure existed for three years before an audit caught it.
Access controls reveal who can reach which systems and data. Auditors review how new users get provisioned, check permission assignments against job roles, examine privileged account management, and verify departed employees actually get deprovisioned. The principle of least privilege says people should have minimum access needed to do their jobs. Most organizations grant access liberally but rarely revoke it. Findings commonly include former employees with active accounts six months after termination, contractors with admin rights, and teams sharing passwords "for convenience."
Author: Marcus Halbrook;
Source: williamalmonte.net
Data encryption practices cover information both sitting in storage and moving across networks. Are databases encrypted? What about backup files? Are you using current TLS protocols for web traffic, or outdated SSL that's trivially breakable? Key management matters too—how do you generate, store, rotate, and retire encryption keys? Weak implementations create false confidence, making you think data is protected when it's actually vulnerable.
Incident response plans get tested for completeness and realism. Auditors review documented procedures, interview team members about their roles, and sometimes run tabletop exercises simulating breaches. Contact lists must be current, escalation procedures clear, and communication templates ready. Plans gathering dust on SharePoint since 2019 typically reference employees who left years ago and phone numbers that no longer work.
Employee training programs show whether staff actually understand security responsibilities or just click through mandatory videos. Auditors examine training content, review attendance logs, check testing results, and conduct informal interviews. Some run simulated phishing campaigns to gauge real-world awareness. A bank with 100% training completion discovered through audit interviews that employees treated the annual module as a coffee break—they'd click through slides without reading them, then guess on the quiz until passing.
Physical security protects hardware and facilities. Auditors inspect server rooms, test badge access systems, review how you manage visitors, and verify workstations are secured when unattended. Equipment disposal matters too—how do you handle old computers and drives? One company threw decommissioned hard drives in regular dumpsters without wiping data. Anyone could have retrieved customer information from their trash.
Common Cyber Security Audit Findings and How to Address Them
Weak password policies show up in 6 out of 10 audits. Organizations allow 6-character passwords, don't require complexity, permit password reuse across systems, or never enforce rotation. Fix this by implementing 12-character minimums, requiring password managers for employees, enabling multi-factor authentication everywhere possible, and rotating privileged account passwords quarterly. A distribution company cut unauthorized access attempts 89% within three months after tightening password requirements following an audit.
Outdated software and missing patches create immediate risks. Auditors routinely find servers running unsupported operating systems, applications several versions behind current releases, and security patches from 2023 still not installed in 2026. A healthcare provider discovered 47 Windows Server 2012 instances—support ended in 2023—because nobody maintained a complete server inventory. Remediation requires establishing patch management processes with regular vulnerability scanning, testing protocols for updates, and deployment schedules. You can't patch what you don't know exists, so maintain current asset inventories.
Insufficient logging and monitoring means you can't detect breaches or investigate incidents. Companies either don't collect logs, don't keep them long enough, or never review them. The average breach in 2026 takes 207 days to detect—comprehensive logging and active monitoring dramatically shrink that window. Address this by implementing centralized log collection, establishing retention policies meeting regulatory requirements (90 days to 7 years depending on industry), and configuring automated alerts for suspicious activity patterns.
Missing documentation or policy-practice gaps create compliance headaches and operational confusion. Auditors find companies operating without formal security policies, or with policies copied from templates but never customized or implemented. A tech startup had a comprehensive security manual downloaded from the internet—employees didn't know it existed. Create practical, organization-specific policies. Train people on them. Review and update them annually. Security policies should evolve as your business evolves, not sit static for five years.
Inadequate backup and recovery capabilities leave you vulnerable when ransomware hits. Common findings include infrequent backups, untested restoration procedures, backups stored on the same network as production systems (so ransomware encrypts them too), and missing documentation. A manufacturer learned during their audit that backup jobs had been failing silently for six months—they had no viable backups at all. Follow 3-2-1 rules: three copies of data, two different media types, one copy offsite. Test restorations quarterly. Isolate backup infrastructure from production networks.

Author: Marcus Halbrook;
Source: williamalmonte.net
Weak vendor management creates supply chain exposure. Organizations don't assess vendor security before signing contracts, lack security requirements in agreements, or never audit vendor compliance. After a major 2025 breach caused by a compromised third-party provider, scrutiny intensified in this area. Address it by establishing vendor risk assessment procedures before engagement, incorporating specific security requirements into contracts, maintaining vendor inventories with risk ratings, and conducting periodic vendor security reviews.
The audits that actually move the needle don't just catalog vulnerabilities—they shift how organizations think about security. When leadership treats findings as intelligence rather than criticism, and commits resources to fix problems, audits become turning points that strengthen security culture for years
— Marcus Chen
Frequently Asked Questions About Cyber Security Audits
Cyber security audits give organizations honest assessments of their security posture, revealing vulnerabilities before attackers exploit them. The structured examination of systems, policies, and controls exposes gaps between security intentions and messy reality, creating specific action plans for improvement.
Yes, audits require investments of time and money. But audit costs pale against breach consequences: financial losses, regulatory penalties, reputation damage, customer defection, and litigation exposure. The question isn't whether you can afford regular audits—it's whether you can afford to skip them.
Organizations treating audits as compliance checkboxes waste the opportunity. Better approach: view audits as intelligence gathering that strengthens defenses, validates security investments, and builds cultures where security becomes everyone's job. Select appropriate audit types for your situation. Prepare thoroughly. Engage constructively with auditors. Commit to actual remediation, not just documentation.
Whether you're scheduling your first audit or refining an established program, remember security is continuous work, not a destination. Regular audits provide checkpoints on that journey, helping navigate evolving threats, changing regulations, and growing business complexity. Organizations embracing this perspective—treating audits as partners rather than obstacles—build more resilient, secure, and trustworthy operations that customers and partners value.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.