
Endpoint security monitoring across laptop, server, and mobile device
What Is EDR in Cybersecurity?
Think of your organization's laptops, servers, and mobile devices as potential entry points for attackers. That's where Endpoint Detection and Response comes in—security technology that watches these devices around the clock, spots suspicious activity, and helps your team shut down threats fast.
EDR works differently than the antivirus programs you're probably familiar with. Instead of just checking files against a database of known malware, these tools track everything happening on your devices. They notice patterns. When a Microsoft Office document suddenly starts running PowerShell commands and connecting to a sketchy server overseas? That raises red flags, even if the specific malware variant has never been seen before.
Here's the reality: attackers have gotten smarter. They slip past firewalls, they use legitimate system tools to hide their tracks, and they can live quietly inside networks for months. Gartner came up with the term "endpoint detection and response" back in 2013 because organizations needed something beyond basic antivirus. They needed visibility.
The shift to remote work made this even more critical. Your employees' laptops aren't sitting safely behind your corporate firewall anymore—they're at coffee shops, home offices, and airports. EDR gives you eyes on those devices no matter where they are.
How EDR Technology Works
Let's walk through what actually happens when EDR protects your environment. It's a four-part process that runs continuously.
Data Collection and Monitoring
Small software agents sit on each device in your network. These agents are chatty—they're constantly recording what programs start and stop, what files get modified, which network connections open, what registry keys change, and dozens of other activities. We're talking hundreds of different event types per device.
The agents don't immediately send everything to a central location. They buffer data locally first. This matters because if someone rips out the network cable to cover their tracks, you still have a local record of what happened. Once connectivity returns, that data flows up to your central management system.
A typical laptop might generate 50,000+ events per day. That's way too much for humans to review manually, which is where the analysis piece comes in.

Author: Vanessa Keaton;
Source: williamalmonte.net
Behavioral Analysis and Detection
All that endpoint data feeds into analytics engines. Sure, these engines check file hashes against known malware signatures—but that's just the starting point.
The real power is behavioral detection. Let's say an Excel file launches PowerShell. PowerShell then downloads an executable from a domain registered two days ago. That executable creates scheduled tasks and starts scanning your internal network. Each individual step might look innocent. Together? Classic attack pattern.
Machine learning models help here. They learn what's normal for your specific environment. The sales team's laptops probably behave differently than the engineering team's workstations. One person accessing databases at 3 AM might be normal if they work night shifts. Someone else doing the same thing? Worth investigating.
False positives remain a challenge. No system is perfect. But good EDR platforms learn from your feedback—when you mark something as safe, the system adjusts.
Endpoint detection and response solutions record endpoint-system-level behaviors, use various data analytics techniques to detect suspicious system behavior, provide contextual information, block malicious activity, and suggest remediation actions to restore affected systems
— Anton Chuvakin
Investigation and Forensics
Alerts by themselves don't tell the whole story. Your security team needs context.
Say you get an alert about suspicious PowerShell activity. EDR lets your analyst click into that event and explore: What triggered this PowerShell instance? What's the parent process? Did this device contact any unusual domains in the past 24 hours? Are other devices showing similar behavior? Did any files get encrypted?
You can pivot through related events, build timelines, and reconstruct the entire attack chain. It's like having a DVR for your endpoints—you can rewind and see exactly what happened, even if the attack occurred three weeks ago.
This forensic capability is genuinely transformative. Without it, investigating an incident means taking systems offline, creating disk images, and spending days or weeks on manual analysis. With EDR, your analyst can examine a potentially compromised laptop in Boston while sitting at a desk in Seattle.

Author: Vanessa Keaton;
Source: williamalmonte.net
Automated and Manual Response
Speed matters during security incidents. Minutes can mean the difference between containing ransomware on one device versus watching it encrypt your entire file server.
EDR platforms can respond automatically based on rules you define. Detect ransomware behavior? Immediately isolate that device from the network. Malicious process detected? Kill it. Suspicious file? Quarantine it. These automated responses execute in seconds.
But you'll also want manual control. Maybe you need to remove specific registry keys without wiping the whole system. Or perhaps you want to leave a compromised system running to observe the attacker's techniques. EDR gives your analysts surgical tools for these situations.
Key Capabilities of EDR Solutions
What does "EDR" actually mean in practical terms? Let's break down the core capabilities that define these platforms.
Continuous Endpoint Visibility
EDR creates a searchable database of everything happening across your endpoints. This visibility extends backward in time—you can investigate incidents that happened weeks or months ago.
Need to know which devices accessed a particular shared folder last quarter? EDR can answer that. Wondering when a specific vulnerability first appeared in your environment? Check the EDR logs. This retrospective analysis is impossible with traditional antivirus.
Threat Intelligence Integration
EDR platforms consume external threat intelligence feeds constantly. When security researchers discover a new ransomware variant and publish indicators of compromise, your EDR system can immediately search all endpoint data for those indicators.
This works both ways. Your EDR also contributes to collective threat intelligence. When your system detects a novel attack technique, anonymized data about that technique can be shared with the broader security community (if you enable this feature).
Automated Threat Hunting
Besides responding to alerts, EDR enables proactive searches for hidden threats. Your security team can write queries like "show me any process that accessed LSASS memory"—a common technique for stealing credentials.
Some EDR platforms include pre-built hunting queries designed by security researchers. These queries run continuously in the background, looking for subtle indicators of compromise that wouldn't trigger high-confidence alerts on their own.
One financial services company used threat hunting to discover an attacker who'd been quietly present in their environment for eight months. No alerts had fired because the attacker was extremely careful. But a hunting query looking for unusual remote desktop patterns caught them.
Incident Response Orchestration
During a widespread incident, you need to coordinate responses across many devices simultaneously. EDR provides a central command console where your team can manage dozens or hundreds of affected endpoints at once.
This orchestration capability proves its value during ransomware outbreaks. Instead of manually isolating each infected device, you can execute network isolation across all affected systems with a few clicks.
Forensic Analysis Tools
EDR platforms include built-in forensic capabilities that used to require specialized tools. You can examine memory dumps, review file execution histories, analyze network traffic patterns, and reconstruct attacker activities—all remotely.
This eliminates the need for physical access to compromised devices. Your security team can conduct thorough investigations without shipping laptops to a forensics lab or flying technicians to remote offices.
EDR vs Antivirus vs XDR
People often ask how EDR relates to traditional antivirus and the newer XDR (Extended Detection and Response) platforms. Here's how these technologies compare:
| Technology Type | Primary Function | Threat Scope | Response Capability | Best For |
| Antivirus | Blocks known malware using signature databases | Known malware with existing fingerprints | Removes or quarantines detected files automatically | Basic protection; meeting baseline compliance; personal computers |
| EDR | Identifies suspicious endpoint behaviors and enables investigation | Unknown malware, sophisticated techniques, behavioral anomalies | Device isolation, process killing, detailed forensics, targeted remediation | Organizations targeted by advanced threats; teams with security analysts |
| XDR | Links threats across endpoints, networks, email, cloud services, and identity systems | Multi-stage attacks crossing different security boundaries | Orchestrated responses across all connected security tools | Large enterprises with complex IT environments; mature security operations |
Traditional antivirus still has a role. It blocks common malware effectively and meets basic compliance requirements. But attackers bypass antivirus routinely using encryption, polymorphic code, or simply avoiding files altogether with fileless techniques.
EDR tackles these limitations by watching behavior instead of just scanning files. However, EDR only sees what happens on endpoints. An attacker might compromise someone's email, pivot to a cloud application, and exfiltrate data through network channels—activities happening outside EDR's field of view.
That's where XDR enters the picture. XDR platforms pull data from endpoints, network security tools, email gateways, cloud access security brokers, and identity systems. By correlating events across these different layers, XDR reveals attack patterns that would look like disconnected events when viewed separately.
For example, XDR might connect a phishing email to suspicious endpoint behavior to anomalous cloud storage uploads to unusual authentication patterns. Together, these reveal a coordinated attack. Separately, each piece might not warrant high-priority attention.
Most organizations layer these technologies rather than picking just one. You'd typically deploy antivirus for baseline protection, add EDR for behavioral detection and investigation, then implement XDR when your environment complexity demands unified visibility across security domains.
Common Use Cases for EDR
EDR shines in specific scenarios where traditional security tools leave you exposed. Here are the situations where organizations get the most value.

Author: Vanessa Keaton;
Source: williamalmonte.net
Ransomware Detection and Containment
Ransomware attacks have gotten more damaging and more common. EDR spots ransomware behavior—rapid file encryption, deletion of backup copies, shadow copy removal—even when the specific ransomware family is brand new.
A manufacturing company experienced this firsthand. An employee opened a malicious attachment on Friday afternoon. Within seconds, EDR detected unusual file modification patterns and automatically isolated the infected laptop. The attack stopped at one device instead of spreading to production systems over the weekend when minimal IT staff was available.
Without EDR? That company would likely have discovered the ransomware Monday morning when dozens or hundreds of systems were encrypted.
Insider Threat Detection
Malicious or careless insiders present unique challenges. They have legitimate credentials and authorized access. Traditional security tools struggle to differentiate between normal work and data theft.
EDR helps by identifying anomalous behavior from authorized users. Maybe someone suddenly accesses records far beyond their job requirements. Or they copy thousands of files to a USB drive. Or they upload sensitive documents to personal Dropbox accounts.
One financial services firm caught an employee accessing customer records they had no business viewing. The employee then copied thousands of files to an external drive. EDR flagged the unusual access patterns and mass file transfers, enabling investigation before sensitive information left the building.
Compliance and Audit Requirements
Regulations like PCI DSS, HIPAA, and GDPR require organizations to detect and respond to security incidents affecting sensitive data. EDR provides the monitoring, logging, and response capabilities that auditors expect to see.
The detailed endpoint activity records serve as evidence that you can detect unauthorized access to protected data. When auditors ask "how do you know if someone accessed this patient database?" you can demonstrate EDR's monitoring capabilities.
Healthcare organizations particularly value EDR's ability to track access to systems containing protected health information. Those audit trails help demonstrate HIPAA compliance.
Incident Response and Forensics
When breaches happen, understanding the scope determines your response. What did the attacker access? What data left the network? How long were they present? Which systems are compromised?
EDR accelerates incident response dramatically. A technology company faced a suspected data breach and needed answers fast. Using EDR forensic tools, their security team reconstructed attacker activities across multiple compromised systems, identified exfiltrated files, and built a detailed timeline—all within 48 hours. Traditional forensic investigations would have taken weeks and required physical access to affected systems.
Advanced Persistent Threat (APT) Detection
Sophisticated attackers use stealthy techniques to maintain long-term access. They move slowly, use legitimate system tools, and carefully avoid triggering alerts. EDR's behavioral detection and hunting capabilities help identify subtle indicators of APT activity.
Security teams can hunt for specific tactics documented in the MITRE ATT&CK framework, searching endpoint data for evidence even when no automatic alerts fired. Maybe you're looking for unusual scheduled tasks, persistence mechanisms in obscure registry locations, or low-and-slow data exfiltration patterns.
When Organizations Need EDR
EDR isn't necessary for everyone immediately. Several factors determine when this investment makes sense for your organization.
Organization Size and Complexity
Small businesses with 20-30 endpoints and one part-time IT person probably don't need full EDR. The cost and complexity outweigh the benefits relative to risk exposure. These organizations often do better with managed detection and response services that include EDR technology but outsource the monitoring and analysis.
Mid-size organizations with 50-500 endpoints hit an inflection point. Manual security monitoring becomes impractical at this scale. A single successful ransomware attack often costs more than five years of EDR licensing. This is typically when investing in EDR starts making economic sense.
Enterprises with thousands of endpoints absolutely require EDR. There's no practical alternative for maintaining visibility across distributed environments. Relying solely on antivirus and quarterly vulnerability scans leaves massive blind spots.
Industry and Threat Profile
Healthcare organizations handle valuable patient data and face constant targeting by ransomware operators. Financial institutions deal with money and face both cybercriminals and nation-state actors. Critical infrastructure companies are targets for disruptive attacks. Government agencies handle sensitive information attractive to foreign intelligence services.
These sectors face persistent, sophisticated threats that make EDR practically mandatory—regardless of organization size.
Retailers processing payment cards need EDR to meet PCI DSS monitoring and incident response requirements. Manufacturing companies increasingly deploy EDR as industrial control systems become attack targets.
Regulatory and Compliance Drivers
Compliance frameworks increasingly expect endpoint monitoring capabilities. CMMC requirements for defense contractors explicitly include continuous monitoring and incident response. The SEC's cybersecurity disclosure rules pressure public companies to demonstrate robust security controls.
Organizations operating across multiple jurisdictions face overlapping requirements from GDPR, CCPA, and other privacy regulations. These frameworks expect timely breach detection and response—capabilities that EDR delivers.
Existing Security Gaps
Organizations that have experienced security incidents often identify EDR as a missing piece. Ask yourself: can your security team see what's happening on endpoints right now? Can you investigate incidents without reimaging systems? Can you determine breach scope quickly?
If those questions make you uncomfortable, EDR would provide immediate value.
Similarly, organizations with heavily remote workforces need EDR. Traditional network security controls don't protect laptops operating from home offices and coffee shops. EDR provides protection that follows devices wherever they go.
Choosing an EDR Platform
Author: Vanessa Keaton;
Source: williamalmonte.net
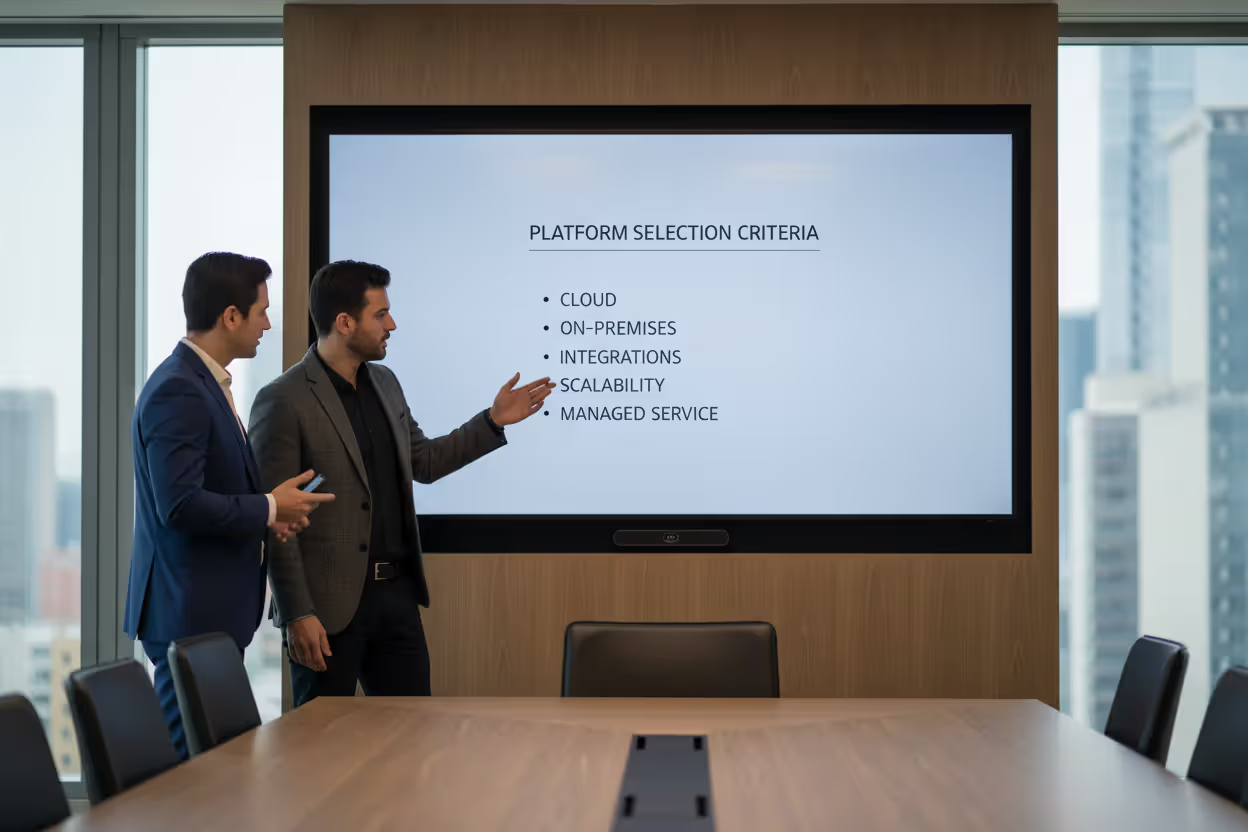
Selecting an EDR solution means evaluating technical capabilities, deployment options, and organizational fit. Here's what to consider.
Deployment Models
Cloud-native EDR hosts the management console and analytics infrastructure in the vendor's environment. These solutions deploy quickly, scale effortlessly, and eliminate data center infrastructure requirements. Cloud deployment works well for distributed workforces and organizations lacking on-premises resources.
On-premises EDR keeps all data within your infrastructure, addressing data sovereignty concerns and regulatory requirements around endpoint telemetry. This model requires more IT resources to maintain but provides maximum control.
Hybrid deployments combine local data collection with cloud-based analytics. Some organizations use hybrid approaches to keep sensitive data on-premises while leveraging cloud-based threat intelligence and machine learning.
Integration Requirements
EDR should integrate with your existing security stack rather than creating another silo. Look for solutions that share threat intelligence with firewalls, email security gateways, and SIEM platforms. Robust APIs enable custom integrations and workflow automation.
If you use specific identity providers, cloud platforms, or ticketing systems, verify smooth integration with EDR candidates. Poor integration creates manual work and undermines automation benefits.
Scalability Considerations
EDR platforms must handle current endpoint counts and accommodate growth. Evaluate licensing models carefully—some vendors charge per endpoint, others use tiered pricing that becomes economical at scale.
Performance impact matters, especially for resource-constrained systems like point-of-sale terminals or manufacturing equipment. EDR agents consume CPU cycles, memory, and network bandwidth. Request performance benchmarks and run proof-of-concept tests on representative systems before committing.
Vendor Evaluation Factors
Assess vendor stability, support quality, and product roadmap. EDR represents a multi-year commitment. Review customer references from similar organizations.
Evaluate the vendor's threat research capabilities. Leading EDR vendors maintain security research teams that discover emerging threats and develop new detection techniques. This research translates into better protection for customers.
Consider the vendor's approach to false positives. Some platforms generate overwhelming alert volumes that create analyst fatigue and burnout. Look for solutions with high-fidelity detections and tuning options to reduce noise.
Managed vs. Self-Operated
Organizations with limited security staff should consider managed EDR services. A security operations center monitors alerts, conducts investigations, and executes responses on your behalf. This provides EDR capabilities without requiring internal expertise.
Self-operated EDR gives complete control but demands skilled analysts who understand threat hunting, incident response, and the platform's capabilities. Honestly assess whether your team has bandwidth and expertise to operate EDR effectively.
Frequently Asked Questions About EDR
EDR has transformed from a specialized security tool into a core component of cybersecurity programs for organizations facing today's threat landscape. By delivering continuous endpoint visibility, behavioral threat detection, investigation tools, and response capabilities, EDR addresses gaps that traditional security solutions can't close.
Whether your organization needs EDR depends on size, threat profile, regulatory requirements, and security maturity. Not every organization requires enterprise-grade EDR today, but trends toward targeted ransomware, supply chain attacks, and persistent threats make these capabilities increasingly relevant across organization types and industries.
Successful EDR implementation goes beyond purchasing software. Organizations need appropriate skills to operate the platform effectively—whether through internal security teams or managed service providers. Integration with existing security tools, proper tuning to minimize false positives, and regular threat hunting activities determine whether EDR delivers its potential value.
Threat actors continue developing techniques to evade traditional defenses. The behavioral detection and forensic capabilities that define EDR will remain essential for organizations needing to detect, investigate, and respond to security incidents before they cause catastrophic damage. If you're serious about cybersecurity, EDR belongs in the conversation about your security strategy.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.




