
Endpoint security protection across multiple connected devices
Endpoint Security Threat Prevention Guide
Cyber threats continue to evolve at an alarming pace. According to recent security reports, endpoint-related attacks account for over 70% of successful data breaches in enterprise environments. Every laptop, smartphone, server, and IoT device connected to your network represents a potential entry point for attackers. Endpoint security threat prevention addresses this challenge by stopping malicious activity before it can compromise systems, steal data, or disrupt operations.
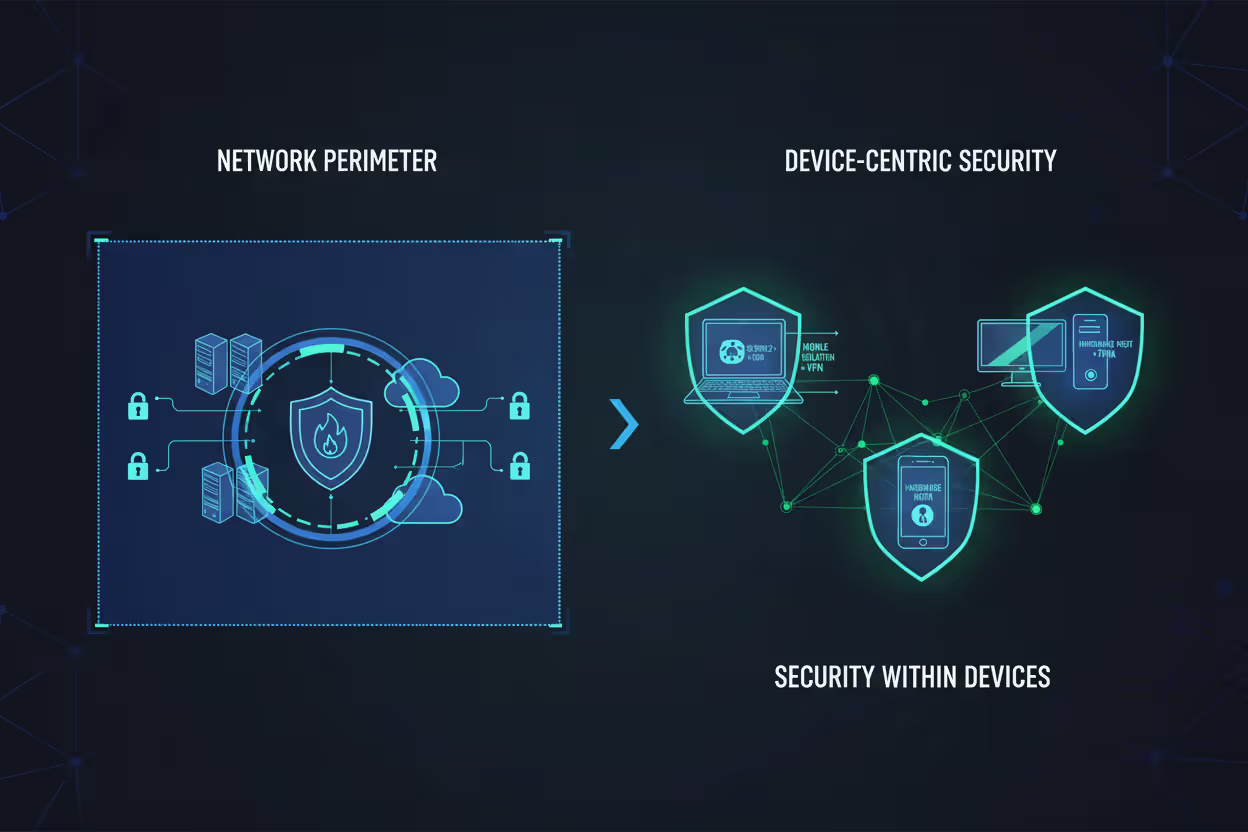
Unlike traditional security approaches that focus on network perimeters, endpoint threat prevention operates directly on devices themselves. This shift reflects a fundamental change in how organizations operate—with remote work, cloud services, and mobile devices making the old "castle-and-moat" security model obsolete. Understanding how endpoint security threat prevention works and implementing it effectively has become essential for organizations of all sizes.
What Is Endpoint Security Threat Prevention?
Endpoint security threat prevention is a proactive security approach that identifies and blocks cyber threats directly on endpoint devices before they can execute malicious actions. An endpoint refers to any device that connects to your network: workstations, laptops, mobile phones, tablets, servers, point-of-sale systems, and increasingly, IoT devices like smart sensors and cameras.
The term "threat prevention" distinguishes this approach from traditional antivirus software or detection-based systems. While detection identifies threats after they've entered a system, prevention stops them at the point of entry. Rather than waiting to discover a breach and then responding, prevention-focused solutions analyze files, processes, network connections, and user behaviors in real-time to block malicious activity before it executes.
Endpoints represent the largest attack surface in modern networks. A single compromised laptop can provide attackers with network access, credential theft opportunities, and lateral movement capabilities. Endpoint security threat prevention basics involve creating multiple layers of protection at the device level: analyzing incoming files for malware signatures, monitoring process behavior for anomalies, controlling which applications can run, and enforcing security policies regardless of network location.
This approach differs fundamentally from perimeter-based security. A firewall protects network boundaries, but once a threat passes through—via a phishing email, infected USB drive, or compromised web download—perimeter defenses offer no protection. Endpoint threat prevention continues protecting devices even when they're off the corporate network, addressing the reality of remote work and mobile computing.
Author: Vanessa Keaton;
Source: williamalmonte.net
The distinction between prevention, detection, and response matters for practical reasons. Detection-based systems like traditional SIEM (Security Information and Event Management) platforms collect logs and alert security teams to suspicious activity. Response capabilities help contain and remediate incidents after they occur. Prevention stops threats before they cause damage, reducing the workload on security teams and minimizing the window of exposure.
How Endpoint Security Threat Prevention Works
Endpoint security threat prevention explained begins with understanding that modern solutions operate through continuous monitoring and real-time decision-making. When a user downloads a file, launches an application, or connects to a network resource, the endpoint security agent intercepts that action and evaluates it against multiple criteria before allowing it to proceed.
The process typically follows this sequence: First, the agent captures the event (file execution, network connection, registry modification, etc.). Second, it analyzes the event using multiple detection engines—signature matching, heuristic analysis, behavioral monitoring, and machine learning models. Third, based on this analysis, it makes an immediate decision: allow, block, or quarantine. Fourth, it logs the event and communicates relevant information to the central management console.
This happens in milliseconds, transparent to the user when legitimate activity occurs, but instantly blocking malicious actions. The sophistication lies in making accurate decisions without generating excessive false positives that disrupt productivity.
Core Technologies Used in Threat Prevention
Several complementary technologies work together in endpoint threat prevention systems:
Signature-based detection remains valuable for identifying known threats. The agent maintains a database of malware signatures—unique identifiers for specific malicious files—and blocks exact matches. While attackers can evade signature detection through polymorphic malware, it still catches a significant volume of commodity threats with minimal processing overhead.
Heuristic analysis examines file characteristics and behaviors to identify suspicious patterns without requiring exact signature matches. For example, a file that attempts to disable antivirus software, encrypt large numbers of files, or establish command-and-control connections exhibits behaviors consistent with malware, even if its specific signature is unknown.
Machine learning models have become central to modern endpoint protection. These models train on millions of samples—both malicious and benign—to identify subtle patterns that indicate threats. They can detect zero-day exploits and novel attack techniques that signature databases haven't cataloged. The trade-off: machine learning requires significant computational resources and can produce false positives when encountering unusual but legitimate software.
Sandboxing executes suspicious files in isolated virtual environments to observe their behavior before allowing them to run on the actual system. If a file attempts malicious actions in the sandbox, it's blocked. Sandboxing provides high accuracy but introduces latency, so it's typically reserved for files that other analysis methods flag as potentially suspicious.
Application control (also called whitelisting) takes a restrictive approach by only allowing approved applications to execute. This prevents unknown malware from running but requires careful management to avoid blocking legitimate new software. Many organizations use hybrid approaches—whitelisting for critical servers, more permissive policies for user workstations.
Real-Time Threat Analysis and Response
The "real-time" aspect of endpoint security threat prevention is what makes it effective against modern attacks. Attackers often move quickly once they gain initial access—establishing persistence, escalating privileges, and exfiltrating data within hours.
Endpoint agents continuously monitor system activity: process creation, file modifications, network connections, registry changes, and user actions. When suspicious activity occurs, the agent can take immediate automated actions: terminating malicious processes, blocking network connections, isolating the device from the network, or reverting unauthorized changes.
Integration with broader security infrastructure amplifies effectiveness. Endpoint agents share threat intelligence with network security tools, SIEM platforms, and threat intelligence feeds. When one endpoint detects a new threat, that information propagates across the organization, protecting other devices. Similarly, threat intelligence from external sources updates endpoint defenses against emerging attack campaigns.

Author: Vanessa Keaton;
Source: williamalmonte.net
Cloud-based management consoles provide centralized visibility and control. Security teams can view the status of thousands of endpoints, deploy policy updates, investigate alerts, and initiate response actions from a single interface. This centralization is crucial for maintaining consistent security across distributed organizations.
Common Endpoint Security Threats and Prevention Methods
Understanding specific threats helps clarify how prevention methods apply in practice. Here are the most prevalent endpoint security threats and corresponding prevention approaches:
| Threat Type | Prevention Method | Example Technology |
| Malware (viruses, trojans, worms) | Signature detection, heuristic analysis, sandboxing | Next-gen antivirus, machine learning classifiers |
| Ransomware | Behavioral monitoring for encryption activity, application control, backup integration | Anti-ransomware modules, controlled folder access |
| Phishing | URL filtering, attachment scanning, user behavior analytics | Email security gateways, browser isolation |
| Zero-day exploits | Exploit prevention, memory protection, patch management | Exploit guard, virtual patching, vulnerability shielding |
| Insider threats | Data loss prevention, privileged access management, user activity monitoring | DLP agents, session recording, anomaly detection |
| Fileless attacks | Memory scanning, script control, process behavior monitoring | PowerShell logging, script execution policies, memory forensics |
| Credential theft | Credential guard, multi-factor authentication enforcement, keylogger detection | Hardware security modules, biometric authentication, anti-keylogging |
Malware encompasses traditional viruses, trojans, and worms. Prevention relies on identifying malicious code before execution using signature databases updated continuously with new threat intelligence. Modern endpoint protection platforms combine signatures with heuristic analysis to catch variants of known malware families.
Ransomware has become one of the most damaging threats, encrypting files and demanding payment for decryption keys. Endpoint security threat prevention examples for ransomware include monitoring for rapid file encryption activity (a behavioral indicator), restricting which applications can modify files in protected folders, and maintaining isolated backups that ransomware can't access. Some solutions can even detect and halt ransomware mid-encryption, then restore affected files from shadow copies.
Phishing attacks trick users into revealing credentials or downloading malware. Endpoint prevention involves scanning email attachments before they reach the user's inbox, blocking access to known phishing URLs, and monitoring for credential entry on suspicious websites. User behavior analytics can flag unusual login patterns that suggest compromised credentials.
Zero-day exploits target vulnerabilities before patches are available. Since signature-based detection can't identify completely novel exploits, prevention relies on exploit mitigation techniques: data execution prevention (DEP), address space layout randomization (ASLR), and monitoring for exploitation behaviors like buffer overflows or privilege escalation attempts.
Insider threats—whether malicious employees or compromised accounts—require different prevention approaches. Data loss prevention (DLP) agents monitor for sensitive information leaving the organization through email, file transfers, or removable media. User activity monitoring establishes baselines for normal behavior and flags anomalies like accessing unusual files or working at odd hours.
Fileless attacks execute malicious code in memory without writing files to disk, evading traditional antivirus. Prevention requires memory scanning capabilities, controlling script execution (PowerShell, VBScript, JavaScript), and monitoring process behavior for malicious actions.
A common mistake organizations make is relying on a single prevention method. Attackers routinely combine techniques—using a phishing email to deliver an exploit that downloads fileless malware. Layered defenses that address multiple threat vectors simultaneously provide more robust protection.
Key Components of an Endpoint Security Threat Prevention System
A comprehensive endpoint security threat prevention system integrates several components working in concert:
Next-generation antivirus (NGAV) forms the foundation, replacing signature-only antivirus with machine learning, behavioral analysis, and exploit prevention. NGAV can identify and block threats that traditional antivirus misses, including zero-day malware and fileless attacks. The trade-off: higher resource consumption and occasional false positives requiring tuning.
Endpoint detection and response (EDR) capabilities extend beyond prevention to provide visibility into endpoint activity and forensic data for investigating incidents. While EDR focuses on detection and response, it complements prevention by identifying threats that evade initial blocking and providing context for security decisions. Many modern platforms combine NGAV and EDR in unified agents.
Host-based firewalls control network traffic at the endpoint level, blocking unauthorized connections regardless of network location. This matters particularly for remote devices outside corporate firewall protection. Properly configured endpoint firewalls prevent lateral movement after initial compromise by restricting which systems can communicate with each other.
Application control and whitelisting determine which software can execute on endpoints. Strict whitelisting—only allowing explicitly approved applications—provides strong protection but requires ongoing management as software updates. Many organizations use reputation-based approaches, blocking known-bad applications while allowing most legitimate software.
Device control manages peripheral devices like USB drives, external hard drives, and mobile phones. Preventing unauthorized USB usage blocks a common malware delivery vector and data exfiltration method. Policies can allow specific authorized devices while blocking unknown peripherals.
Patch management ensures endpoints receive security updates promptly. While not strictly "threat prevention," patching eliminates known vulnerabilities that exploits target. Automated patch deployment reduces the window between vulnerability disclosure and remediation.
Encryption protects data on endpoints from physical theft. Full-disk encryption ensures that a stolen laptop doesn't expose sensitive information. File-level encryption protects specific documents. While encryption doesn't prevent malware, it's essential for comprehensive endpoint security.
Data loss prevention (DLP) agents monitor for sensitive information leaving endpoints through unauthorized channels. DLP can block emails containing credit card numbers, prevent copying confidential files to USB drives, or alert when source code is uploaded to personal cloud storage.
Integration between components matters as much as individual capabilities. An endpoint security threat prevention guide should emphasize that isolated tools create management overhead and security gaps. Unified platforms that combine NGAV, EDR, firewall, device control, and DLP in a single agent with centralized management reduce complexity while improving effectiveness.
Endpoint Security Threat Prevention Examples in Practice
Real-world scenarios illustrate how endpoint threat prevention protects different environments:
Remote workforce protection has become critical as distributed work arrangements persist. A marketing manager working from a home coffee shop connects to public Wi-Fi. Her laptop's endpoint agent detects an attempted man-in-the-middle attack on the network and automatically blocks suspicious connections while maintaining her VPN tunnel to corporate resources. When she downloads a client presentation from email, the agent scans it, detects an embedded macro attempting to download additional malware, and quarantines the file before it executes. She receives a notification explaining the threat, and IT receives an alert for follow-up.
Healthcare data security faces stringent compliance requirements and valuable data targets. A hospital deploys endpoint protection across workstations, medical devices, and administrative systems. When a nurse's workstation receives a phishing email with a malicious attachment disguised as a patient referral, the endpoint agent's sandboxing capability executes the file in isolation, observes its ransomware behavior, and blocks it from the actual system. The hospital's security team receives detailed forensic data about the attack, identifies other employees who received similar emails, and proactively blocks the campaign across all endpoints.
Financial services organizations handle sensitive transaction data and face sophisticated attackers. A bank's endpoint security system monitors teller workstations for unusual behavior. When malware attempts to capture screenshots of customer account information, the endpoint agent detects the screen-capture API calls, identifies them as inconsistent with legitimate banking software behavior, and terminates the malicious process. Device control policies prevent tellers from using personal USB drives, blocking a potential data exfiltration vector.
Retail point-of-sale (POS) systems process payment card data, making them attractive targets for financially motivated attackers. A retailer implements application whitelisting on POS terminals, allowing only approved payment processing software to execute. When an attacker compromises the network and attempts to install card-scraping malware on terminals, the endpoint agents block execution because the malware isn't on the approved application list. This prevents a breach that could have exposed millions of card numbers.

Author: Vanessa Keaton;
Source: williamalmonte.net
These endpoint security threat prevention examples demonstrate how the same core technologies apply differently across industries based on specific threat models, compliance requirements, and operational constraints. The common thread: preventing threats at the device level provides protection that network-based security can't deliver.
How to Choose an Endpoint Security Threat Prevention Solution
Selecting an appropriate solution requires evaluating several factors against your organization's specific needs:
Scalability determines whether a solution can grow with your organization. A platform suitable for 50 endpoints may lack the management capabilities, performance, or licensing structure for 5,000 endpoints. Consider both current needs and projected growth. Cloud-based management typically scales more easily than on-premise infrastructure.
Compatibility with your existing environment is essential. Verify support for your operating systems (Windows, macOS, Linux, mobile platforms), applications, and infrastructure. Some solutions perform better in specific environments—for example, offering deeper integration with Microsoft or VMware ecosystems. Test thoroughly before full deployment to identify compatibility issues.
Automation capabilities reduce the security team's workload. Look for automated threat response (isolating infected devices, terminating malicious processes), policy enforcement, and remediation. Manual intervention for every alert doesn't scale. The best solutions handle routine threats automatically while escalating genuine incidents requiring human judgment.
Vendor support and threat intelligence quality varies significantly. Evaluate the vendor's threat research capabilities, update frequency, and support responsiveness. During an active incident, vendor support quality becomes critical. Review service level agreements and support options (24/7 availability, dedicated support contacts for enterprise customers).
Compliance requirements may dictate specific capabilities. Healthcare organizations need HIPAA compliance features; financial services require controls for PCI-DSS or SOX. Verify that solutions provide necessary audit logging, data protection, and reporting capabilities. Some vendors offer compliance-specific packages that simplify meeting regulatory requirements.
Performance impact on endpoints affects user productivity. Endpoint agents consume CPU, memory, and disk resources. Excessive resource consumption slows systems and frustrates users, potentially leading to workarounds that bypass security. Test solutions under realistic workloads to assess performance impact. Cloud-connected agents that offload analysis to cloud infrastructure typically have lower endpoint resource requirements.

Author: Vanessa Keaton;
Source: williamalmonte.net
Total cost of ownership extends beyond licensing. Consider deployment effort, ongoing management time, training requirements, and infrastructure costs. A less expensive solution that requires extensive manual management may cost more over time than a pricier platform with better automation. Factor in costs for additional infrastructure like management servers or cloud subscriptions.
Integration with existing security tools amplifies effectiveness. Evaluate how well endpoint solutions integrate with your SIEM, network security tools, identity management systems, and security orchestration platforms. Open APIs and pre-built integrations reduce implementation effort and enable better threat correlation across security layers.
A practical approach: identify your top three threat concerns (ransomware, data loss, zero-day exploits, etc.), then evaluate how well each solution addresses those specific threats. Generic "best endpoint security" rankings matter less than which solution best fits your environment, threats, and constraints.
Endpoint security has shifted from a reactive, detection-focused approach to proactive threat prevention that stops attacks before they execute. Organizations that embrace this shift—deploying behavioral analysis, machine learning, and real-time response capabilities—significantly reduce their attack surface and incident response burden. The endpoints are where users work and where data lives; that's where security must be strongest.
— Dr. Sarah Chen, Chief Security Strategist
Frequently Asked Questions About Endpoint Security Threat Prevention
Endpoint security threat prevention represents a fundamental shift from reactive detection to proactive blocking of cyber threats at the device level. As attack surfaces expand with remote work, mobile devices, and cloud services, protecting endpoints has become central to organizational security strategies.
Effective endpoint protection combines multiple technologies—signature detection, behavioral analysis, machine learning, exploit prevention, and application control—working together to stop threats before they execute. Understanding common threats like malware, ransomware, and zero-day exploits helps organizations implement appropriate prevention methods tailored to their specific risk profile.
Choosing the right solution requires evaluating scalability, compatibility, automation, vendor support, and total cost of ownership against your organization's needs. Small businesses need endpoint security as much as enterprises, though their solutions may emphasize simplicity and cost-effectiveness. Cloud users still need endpoint protection because devices accessing cloud services remain vulnerable to compromise.
No security solution provides perfect protection. Endpoint threat prevention reduces risk significantly but should be part of a layered security strategy that includes network security, user training, incident response planning, and regular backups. The goal is making successful attacks difficult enough that most threat actors move to easier targets while ensuring that breaches that do occur are detected and contained quickly.
Organizations that implement comprehensive endpoint security threat prevention gain visibility into device activity, reduce incident response workload through automation, and protect data regardless of where endpoints connect. In a threat landscape where attacks grow more sophisticated daily, strong endpoint security is no longer optional—it's essential for protecting the devices where work happens and data lives.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.




