Cybersecurity analyst monitoring next-generation endpoint protection dashboard
Next-Generation Endpoint Security Explained
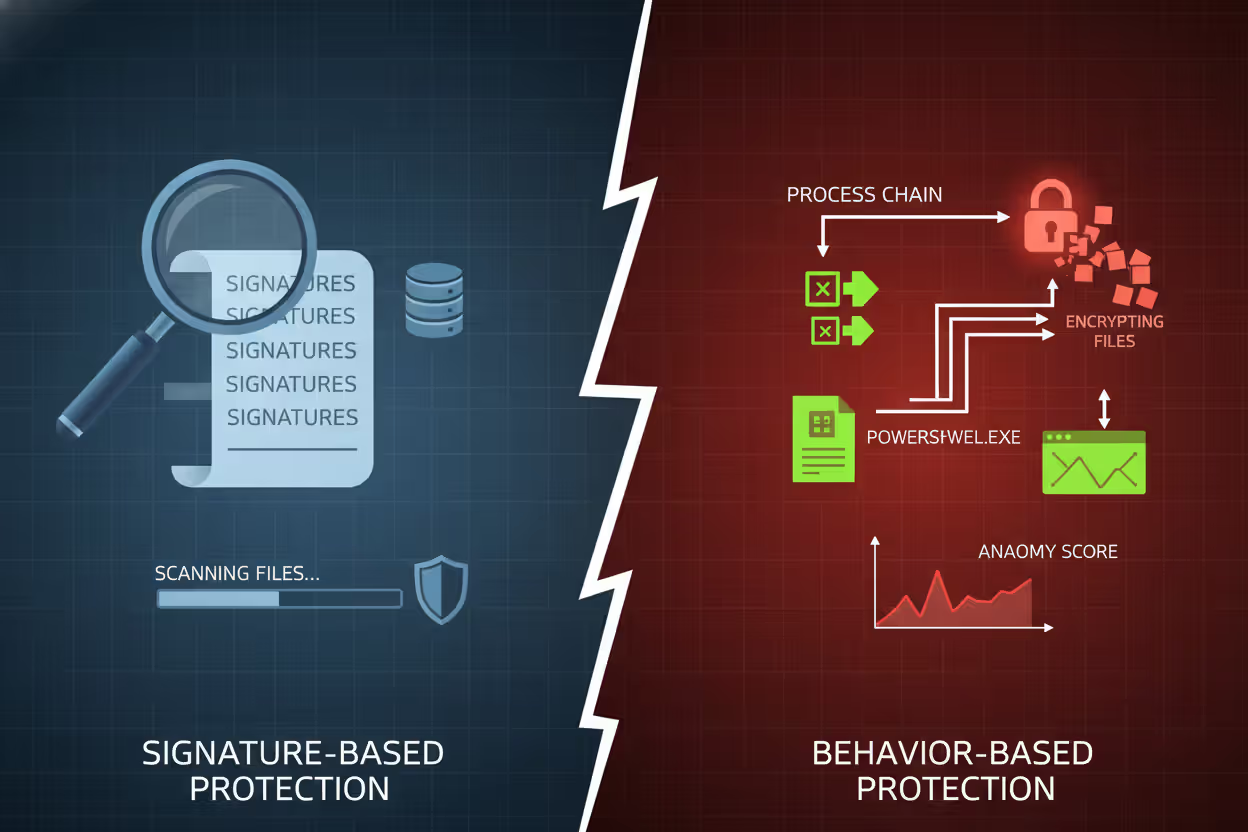
Cyberattacks have evolved far beyond the simple viruses that plagued early computers. Traditional antivirus software, which relies on matching known threat signatures against a database, can no longer keep pace with modern attack methods. Hackers now deploy polymorphic malware, fileless attacks, and zero-day exploits that slip past signature-based defenses before security vendors even know they exist.
Next-generation endpoint security emerged as a response to this reality. Organizations watching ransomware encrypt their files or discovering advanced persistent threats living in their networks for months realized that reactive, signature-dependent tools were fundamentally inadequate. The shift toward proactive, behavior-based protection represents one of the most significant changes in enterprise security over the past decade.
What Is Next-Generation Endpoint Security?
Next-generation endpoint security (often abbreviated as NGAV or NGES) refers to security platforms that protect laptops, desktops, servers, and mobile devices using advanced techniques beyond traditional signature matching. These solutions employ machine learning algorithms, behavioral analysis, threat intelligence feeds, and automated response capabilities to identify and stop threats in real time—including attacks that have never been seen before.
The technology emerged around 2015-2016 when security vendors recognized that signature-based antivirus was failing against sophisticated attacks. Traditional AV works by comparing files against a database of known malware signatures. If a file's signature matches one in the database, it gets blocked. This approach works fine for known threats but fails completely against new variants, obfuscated code, or fileless attacks that never write malicious code to disk.
Next-generation solutions flip this model. Instead of asking "Does this match a known bad signature?" they ask "Is this behavior suspicious or anomalous?" A legitimate system process shouldn't suddenly start encrypting hundreds of files per second. A Word document shouldn't spawn PowerShell commands that download executables from the internet. These behavioral red flags trigger alerts and automated responses even when the specific attack has never been cataloged.
Author: Daniel Prescott;
Source: williamalmonte.net
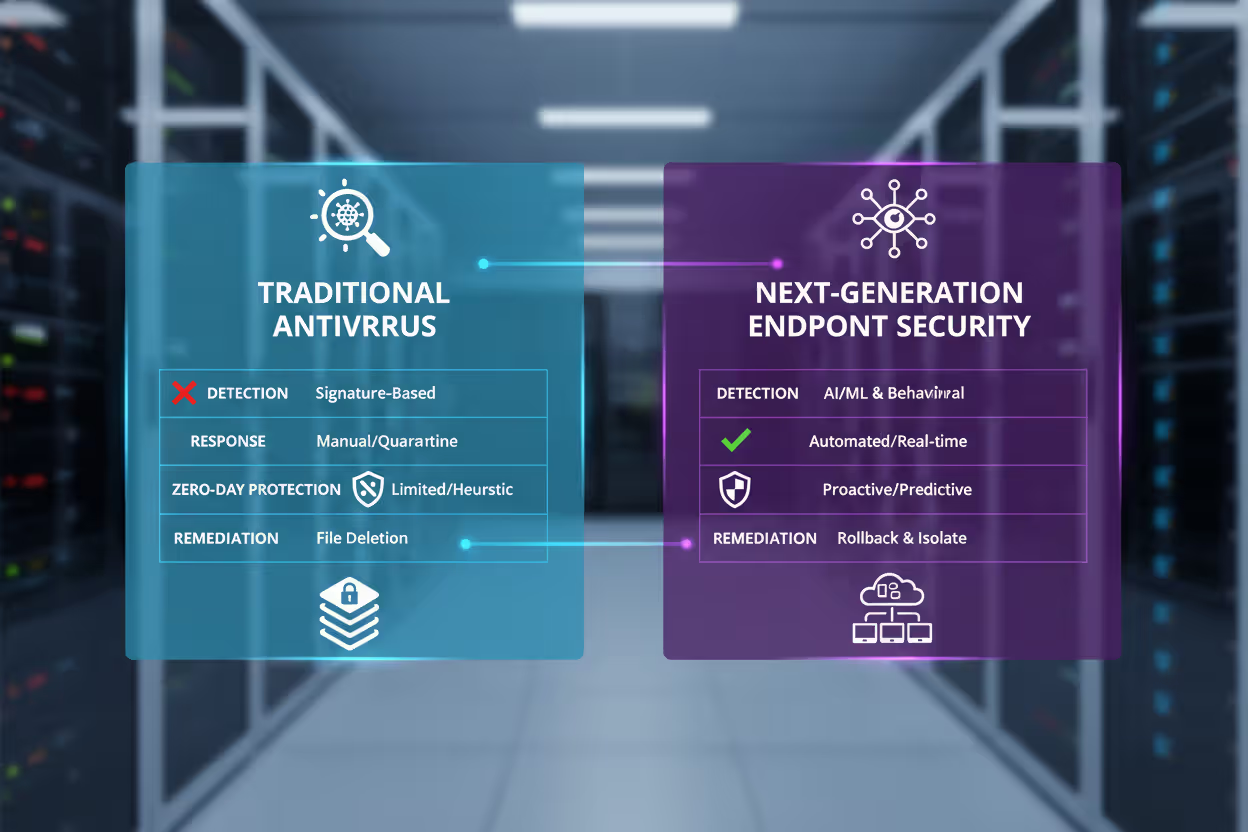
The "next-generation endpoint security basics" revolve around three core principles: prevention through predictive analysis, detection of anomalous behavior, and automated response that contains threats before they spread. Unlike legacy AV that simply quarantines known malware, these platforms can roll back malicious changes, isolate compromised devices from the network, and terminate suspicious processes—all without human intervention.
How Next-Generation Endpoint Security Works
Modern endpoint protection platforms combine multiple detection and response technologies into a unified agent installed on each device. This agent continuously monitors system activity, network connections, file operations, registry changes, and process behavior. The collected data feeds into both local and cloud-based analytics engines that apply machine learning models trained on millions of malware samples and benign files.
Next-generation endpoint security changes the logic of defense: instead of waiting for known malware signatures, it identifies suspicious behavior in real time, stops attacks before they spread, and helps organizations respond automatically to threats they have never seen before
— Daniel Miessler
Detection Methods Used in Modern Endpoint Protection
Machine learning classification forms the foundation of next-gen detection. Algorithms analyze file attributes—not just signatures—including file structure, entropy, code patterns, compiler artifacts, and metadata. A file might be completely new, but if its characteristics resemble known ransomware families (high entropy, rapid file system access, cryptographic function calls), the ML model assigns it a high-risk score.
Behavioral analysis tracks what programs actually do after execution. The endpoint agent creates a detailed timeline of every action: files opened, network connections established, registry keys modified, child processes spawned. This execution graph reveals attack patterns. For example, a phishing document that launches cmd.exe, which then runs PowerShell, which downloads an executable from a suspicious domain—this chain of behavior screams "malicious" even if each individual component appears legitimate.
Threat intelligence integration enriches local detection with global context. When the agent encounters a file hash, IP address, domain name, or behavioral pattern, it queries cloud-based threat intelligence databases containing indicators of compromise (IOCs) from attacks worldwide. If that domain was seen in ransomware campaigns targeting other organizations yesterday, your endpoint knows to block it today.
Exploit prevention monitors applications for exploitation techniques rather than specific exploits. Attackers constantly discover new vulnerabilities, but exploitation methods follow predictable patterns: heap spraying, return-oriented programming, DLL injection, privilege escalation. By detecting these techniques at runtime, next-gen solutions stop zero-day exploits without needing patches or signatures.
Sandboxing isolates suspicious files in a controlled virtual environment to observe their behavior before allowing execution on the actual endpoint. If a file exhibits malicious actions in the sandbox—like attempting to disable security tools or encrypt files—it gets blocked. Some platforms perform this sandboxing locally; others send suspicious files to cloud-based detonation chambers.

Author: Daniel Prescott;
Source: williamalmonte.net
Response and Remediation Capabilities
Detection alone doesn't constitute next-generation protection. The "response" component distinguishes modern platforms from legacy AV. When a threat is identified, automated workflows execute immediately:
Process termination kills the malicious process and any child processes it spawned, stopping the attack in progress. Unlike traditional AV that might only quarantine a file, this prevents further damage.
Network isolation disconnects the compromised endpoint from the network while maintaining a connection to the security management console. This containment prevents lateral movement—the attacker can't pivot to other systems—while allowing security teams to investigate remotely.
Rollback and remediation reverses malicious changes. If ransomware encrypted 500 files before being stopped, the platform can restore them from shadow copies or its own backup snapshots. Registry changes get reverted. Scheduled tasks created by the attacker get deleted. The system returns to its pre-attack state without requiring a complete reimaging.

Author: Daniel Prescott;
Source: williamalmonte.net
Forensic data collection captures detailed evidence about the attack: the initial infection vector, every file touched, network connections made, and the complete process execution tree. This information proves invaluable for incident response, threat hunting, and improving future defenses.
Key Differences Between Traditional Antivirus and Next-Gen Solutions
The gap between traditional and next-generation approaches becomes clear when examining their fundamental architectures and capabilities:
| Feature | Traditional Antivirus | Next-Generation Endpoint Security |
| Detection method | Signature-based matching against known malware database | Behavioral analysis, machine learning, threat intelligence, exploit prevention |
| Response time | Hours to days (requires signature updates) | Real-time (identifies unknown threats immediately) |
| Zero-day protection | Minimal; relies on heuristics that generate false positives | Strong; detects malicious behavior regardless of novelty |
| Machine learning | Limited or absent | Core detection engine trained on massive datasets |
| Behavioral analysis | Basic or none | Comprehensive process, file, and network monitoring |
| Remediation | File quarantine only | Automated rollback, network isolation, process termination |
| Resource usage | Frequent signature updates, scheduled scans impact performance | Cloud-based analytics reduce endpoint load; continuous monitoring |
Traditional antivirus operates on a fundamentally reactive model. A new malware variant must be discovered, analyzed by security researchers, and added to signature databases before it can be detected. This process creates a window of vulnerability—often days or weeks—during which the threat spreads undetected. Organizations running traditional AV might have the latest signatures and still get compromised by brand-new malware.
Next-generation platforms operate proactively. They don't need to have seen a specific threat before to recognize it as malicious. A ransomware variant released this morning will exhibit behaviors consistent with encryption malware—rapid file access, cryptographic operations, ransom note creation—that trigger detection algorithms trained on thousands of previous ransomware families.
The shift from "signature matching" to "behavioral understanding" represents the core of what makes endpoint security "next-generation." It's the difference between checking IDs at the door (signature matching) versus watching for suspicious behavior inside the building (behavioral analysis).
Author: Daniel Prescott;
Source: williamalmonte.net
Common Use Cases and Deployment Scenarios
Organizations deploy next-generation endpoint security to address specific threat scenarios where traditional AV consistently fails:
Remote workforce protection has become critical as employees work from home networks, coffee shops, and co-working spaces outside the corporate perimeter. Traditional perimeter defenses—firewalls, intrusion detection systems, web gateways—don't protect these distributed endpoints. Next-gen solutions provide consistent protection regardless of location, with cloud-based management consoles allowing security teams to monitor and respond to threats on any device anywhere.
Ransomware defense represents perhaps the most urgent use case. Ransomware attacks cost organizations millions in ransom payments, downtime, and recovery efforts. Traditional AV struggles because ransomware variants change constantly—attackers modify code to evade signature detection. Next-gen platforms detect the behavioral pattern of mass file encryption and stop it within seconds, often before significant damage occurs. The rollback capabilities then restore affected files without paying ransom.
Fileless malware attacks exploit legitimate system tools like PowerShell, WMI, and Windows Script Host to execute malicious code entirely in memory, never writing files to disk. Since traditional AV scans files, these attacks remain invisible. Next-generation solutions monitor process behavior and detect when legitimate tools are used maliciously—like PowerShell downloading and executing payloads from command-and-control servers.
Zero-day threat protection matters when attackers exploit vulnerabilities before patches exist. A vulnerability disclosed today might not have patches available for weeks, creating a window where traditional defenses offer no protection. Next-gen platforms detect the exploitation techniques used to leverage these vulnerabilities—buffer overflows, privilege escalation, code injection—stopping attacks even when the specific vulnerability is unknown.
Advanced persistent threats (APTs) involve sophisticated attackers establishing long-term footholds in networks, often remaining undetected for months. They use custom malware, living-off-the-land techniques, and careful operational security to avoid traditional detection. Behavioral analysis and threat intelligence integration help identify the subtle anomalies that betray APT presence: unusual lateral movement, strange authentication patterns, or data exfiltration to suspicious destinations.
Compliance requirements increasingly mandate endpoint protection that goes beyond basic antivirus. Frameworks like NIST, PCI-DSS, and HIPAA now emphasize continuous monitoring, incident response capabilities, and forensic data collection—features that traditional AV lacks but next-gen platforms provide natively.
Next-Generation Endpoint Security Examples
Several vendors dominate the next-generation endpoint security market, each offering distinct approaches and capabilities:
CrowdStrike Falcon pioneered the cloud-native endpoint protection model. Its lightweight agent collects endpoint data and sends it to cloud-based analytics engines that apply machine learning and threat intelligence at massive scale. Falcon emphasizes speed and simplicity—the agent installs in minutes, requires no signature updates, and provides immediate protection. The platform includes integrated threat intelligence from CrowdStrike's threat hunting team, which tracks major threat actors and campaigns. Falcon's approach works particularly well for distributed organizations with limited security staff.
SentinelOne takes an autonomous approach, embedding more intelligence directly in the endpoint agent. This allows the platform to detect and respond to threats even when disconnected from the cloud—useful for air-gapped networks or devices with intermittent connectivity. SentinelOne's patented storyline technology creates visual attack narratives showing exactly how an attack unfolded, which files were affected, and what actions the platform took. The solution includes native EDR (Endpoint Detection and Response) capabilities without requiring separate agents or licenses.
Microsoft Defender for Endpoint integrates deeply with Windows, leveraging OS-level visibility that third-party solutions can't match. For organizations already invested in the Microsoft ecosystem, Defender offers seamless integration with Microsoft 365, Azure, and Intune. The platform shares threat intelligence across Microsoft's vast customer base—attacks detected anywhere inform protection everywhere. While historically perceived as less capable than dedicated security vendors, Defender has evolved significantly and now competes effectively in the enterprise market, particularly for Windows-centric environments.
VMware Carbon Black (formerly Carbon Black Response) emphasizes forensic investigation and threat hunting alongside prevention. The platform records every endpoint event—every process execution, file modification, network connection—creating a comprehensive audit trail. Security analysts can query this data to hunt for threats proactively, investigate suspicious activity, or conduct post-incident forensics. This approach generates substantial data volumes but provides unmatched visibility for organizations facing sophisticated threats.
Palo Alto Networks Cortex XDR extends endpoint protection into a broader extended detection and response platform. Rather than focusing solely on endpoints, Cortex XDR correlates data from endpoints, networks, cloud workloads, and identity systems to detect attacks that span multiple vectors. An attacker might compromise a cloud workload, move laterally through the network, and establish persistence on endpoints—Cortex XDR connects these events into a unified attack story that might be invisible when examining each data source separately.
Each platform offers free trials or proof-of-concept deployments, allowing organizations to test detection capabilities against their specific environments and threat profiles before committing.

Author: Daniel Prescott;
Source: williamalmonte.net
Choosing the Right Solution for Your Organization
Selecting next-generation endpoint security requires balancing multiple factors specific to your environment:
Organization size and complexity influences deployment and management requirements. Small businesses with limited IT staff benefit from cloud-native solutions that require minimal maintenance and offer managed service options. Large enterprises with dedicated security teams might prefer platforms with extensive customization, advanced threat hunting tools, and on-premises deployment options. Mid-market organizations often need a balance—robust protection without overwhelming complexity.
Existing security infrastructure matters significantly. If you've already invested in a SIEM, firewall vendor, or cloud platform, choosing endpoint security from the same vendor often provides better integration and unified management. However, best-of-breed approaches—selecting the strongest solution in each category—sometimes deliver superior protection despite integration challenges.
Threat landscape and risk profile should drive capability requirements. Organizations in targeted industries (finance, healthcare, critical infrastructure) facing advanced persistent threats need comprehensive EDR, threat hunting, and forensic capabilities. Companies facing primarily commodity threats might prioritize prevention and automated response over deep investigation tools.
Performance requirements vary by endpoint type. Servers running business-critical applications can't tolerate security agents that consume excessive CPU or memory. Legacy systems might lack resources to run modern security software. Test candidate solutions under realistic workloads to verify acceptable performance impact.
Budget constraints extend beyond licensing costs. Consider deployment effort, training requirements, staffing for alert triage and investigation, and potential managed service fees. Some vendors charge per endpoint; others base pricing on feature tiers. Cloud-based solutions typically use subscription models; on-premises platforms might involve larger upfront costs but lower ongoing expenses.
Managed versus self-managed represents a critical decision. Managed detection and response (MDR) services provide 24/7 monitoring, investigation, and response by vendor security teams—essentially outsourcing your security operations center. This works well for organizations lacking security expertise but requires trusting external parties with sensitive data and response authority. Self-managed deployments give you complete control but demand skilled staff and round-the-clock coverage.
Deployment and compatibility considerations include operating system support (Windows, macOS, Linux, mobile), virtualized environment compatibility, support for legacy systems, and deployment methods (cloud-managed, on-premises console, hybrid). Verify that your chosen solution supports all endpoint types in your environment.
A common mistake involves selecting based solely on feature checklists. Every vendor claims machine learning, behavioral analysis, and automated response. What matters is how effectively these capabilities detect real threats in your environment. Request proof-of-concept deployments with realistic testing against malware samples, attack simulations, and red team exercises.
Frequently Asked Questions About Next-Generation Endpoint Security
The evolution from signature-based antivirus to next-generation endpoint security reflects the fundamental shift in how cyberattacks work. Threats that change daily can't be stopped by defenses updated weekly. Attackers using legitimate tools to execute fileless attacks won't be caught by file scanners. Zero-day exploits by definition have no signatures to match.
Next-generation platforms address these realities through behavioral analysis, machine learning, threat intelligence, and automated response. They detect malicious intent rather than matching known patterns. They stop attacks in real time rather than waiting for signature updates. They remediate damage automatically rather than simply quarantining files.
Organizations still relying on traditional antivirus face a straightforward question: How long can you afford to remain vulnerable to threats your current defenses can't see? The technology exists to dramatically improve endpoint protection. The remaining barrier is organizational inertia—the assumption that "antivirus" means the same thing it meant a decade ago.
It doesn't. The endpoint security landscape has fundamentally changed, and organizations that fail to adapt accept risks that are no longer necessary. Evaluating next-generation solutions, testing them against your actual environment, and deploying modern protection represents one of the highest-return security investments available. The attacks aren't waiting for you to catch up.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.