
Security operations center comparing SIEM and EDR monitoring
SIEM vs EDR Comparison Guide
Cybersecurity teams debate this question constantly: should we invest in SIEM, EDR, or both? By 2026, the answer's gotten more nuanced. Attack methods keep evolving, compliance auditors keep demanding more logs, and security budgets haven't exactly doubled to match.
Here's what happens. A company buys a SIEM because their compliance officer insists. Six months later, ransomware hits an endpoint, and the SIEM missed it entirely. Or they deploy EDR across all workstations, then fail a PCI audit because they can't produce firewall logs from three years ago.
The truth? SIEM and EDR solve fundamentally different problems. One won't replace the other. But figuring out which one your organization needs first—or how to make them work together—requires understanding what each actually does versus what vendors claim they do.
What Are SIEM and EDR?
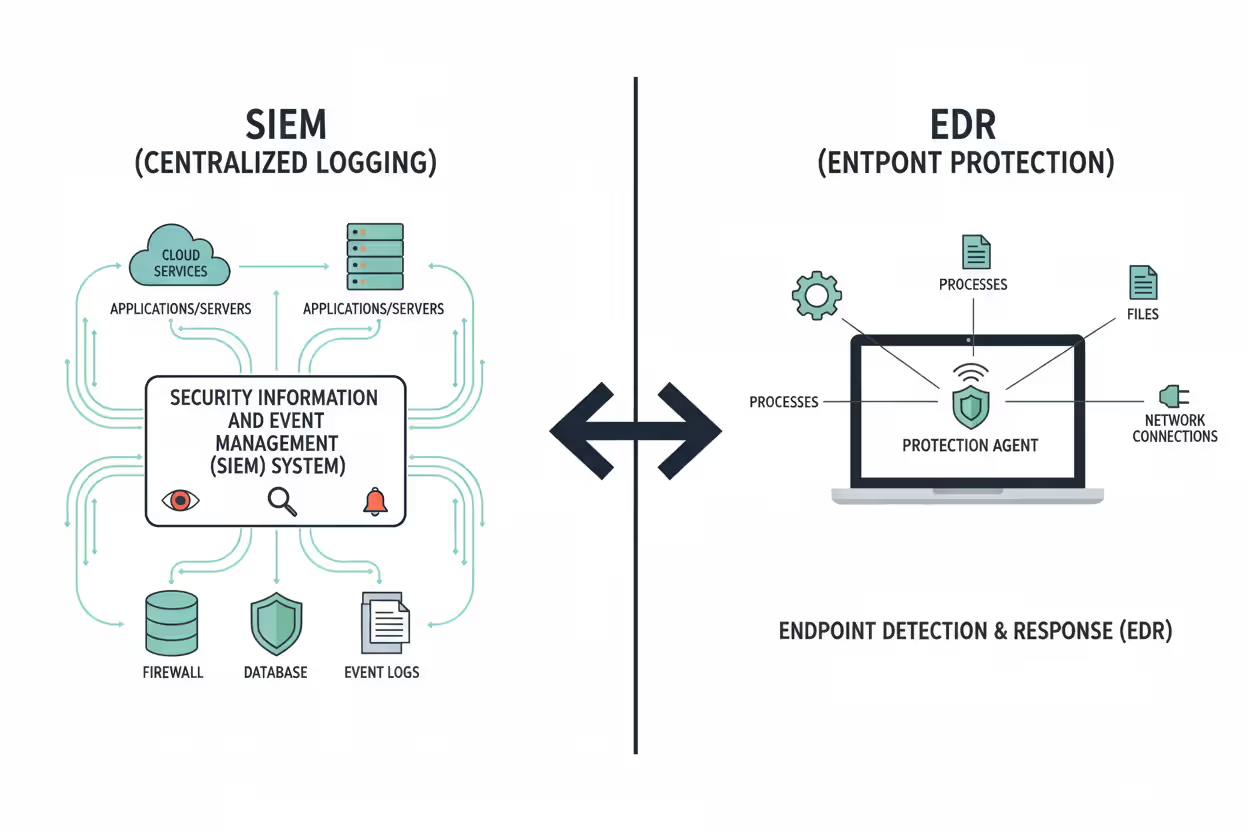
Let's cut through the acronyms. Both technologies protect your infrastructure, but they approach security from opposite directions.
SIEM Defined
Think of SIEM as the security camera system for your entire digital infrastructure. Security Information and Event Management pulls logs from everywhere—your firewalls spitting out denied connections, Active Directory recording login attempts, databases logging queries, cloud services tracking API calls, even your badge readers noting who entered the server room.
The magic happens in correlation. Imagine an employee badge-swipes into the office in Boston at 2 PM. Fifteen minutes later, that same account logs into your VPN from an IP address in Romania. Separately, these events look normal. Together? That's credential theft. SIEM spots these patterns by comparing events across completely different systems.
Regulations love SIEM. HIPAA auditors want three years of access logs. PCI-DSS demands you track every change to cardholder data environments. SOX requires you prove who accessed financial systems and when. SIEM platforms store these logs, index them for searching, and generate the compliance reports auditors expect.
Today's SIEM platforms go beyond basic correlation. They ingest threat intelligence feeds (known-bad IP addresses, malicious domains), apply machine learning to spot unusual behavior, and automate response workflows. But fundamentally, SIEM remains about centralizing visibility across your entire technology stack.
Author: Ethan Caldwel;
Source: williamalmonte.net
EDR Defined
Endpoint Detection and Response operates exclusively on individual devices. Install an EDR agent on a laptop, and it watches everything happening inside that machine—which processes start, what files they touch, what registry keys change, which network connections open, what gets loaded into memory.
Traditional antivirus compares files against known-bad signatures. EDR watches behavior patterns. When Excel.exe suddenly starts encrypting hundreds of files per second and contacting an external IP address, that's not normal Excel behavior. EDR flags it immediately, even if the malware uses a brand-new signature no antivirus database contains.
The "response" part matters enormously. Security teams can remotely isolate infected machines from the network with one click. Kill malicious processes. Delete dropped files. Capture memory dumps for forensic analysis. Even roll back file encryption if you catch ransomware early enough. No need to physically touch the device or wait for desktop support.
EDR creates forensic timelines showing exactly what happened. You can rewind an incident: the user opened a phishing email attachment at 9:47 AM, which spawned a PowerShell process at 9:48 AM, which downloaded a second-stage payload at 9:49 AM, which began scanning the network at 9:51 AM. This level of endpoint visibility doesn't exist anywhere else.
Key Differences Between SIEM and EDR
Put these technologies side by side, and the contrasts become obvious. They collect different data, detect different threats, and respond in completely different ways.
SIEM vs EDR: Side-by-Side Comparison
| Feature | SIEM | EDR |
| Primary Focus | Infrastructure-wide log aggregation and correlation | Granular endpoint behavior monitoring and threat containment |
| Data Sources | Network devices, servers, cloud platforms, applications, identity providers, physical security systems | Agent-collected endpoint telemetry: processes, file operations, memory activity, network connections |
| Detection Method | Cross-system correlation rules, anomaly detection, threat feed matching, statistical baselines | Real-time behavioral analysis, attack technique recognition, ML-based pattern matching |
| Response Capabilities | Workflow automation, alert routing, ticketing integration, orchestration of other tools | Direct endpoint control: isolation, process termination, file quarantine, forensic collection, system rollback |
| Compliance Support | Purpose-built for audit requirements: long-term retention, compliance dashboards, pre-built reports | Provides endpoint evidence during investigations but lacks comprehensive log retention |
| Deployment Scope | Every log-generating system across the entire organization | Agent must be installed on each protected endpoint |
| Ideal For | Meeting regulatory mandates, detecting distributed attack campaigns, investigating infrastructure-wide incidents | Stopping ransomware, investigating endpoint compromises, rapid threat containment, detailed forensics |
Understanding SIEM vs EDR Key Distinctions
Scope represents the biggest difference. SIEM sees authentication failures from Office 365, unusual queries hitting your SQL servers, configuration changes in AWS, failed VPN connections, and firewall blocks—simultaneously. EDR sees what's happening inside individual Windows laptops and Linux servers, but it's completely blind to your network infrastructure, SaaS applications, or cloud control plane.
Speed matters differently for each platform. SIEM typically processes logs that arrive with some delay. A firewall might batch logs every 30 seconds. An application might write to log files that get collected every five minutes. EDR agents monitor in real-time—they detect malicious behavior as it's happening. This explains why EDR excels at stopping ransomware: it catches file encryption within seconds, before attackers finish encrypting your file shares.
Response capabilities tilt heavily toward EDR for endpoint threats. SIEM can trigger automated workflows—create tickets, send notifications, call APIs on other systems. But SIEM doesn't directly control your endpoints. EDR agents have kernel-level access to devices, enabling immediate isolation, process termination, and remediation without depending on other systems responding to API calls.
Compliance requirements frequently mandate SIEM. Show up to a PCI audit with only EDR, and auditors will ask where your firewall logs are, how you're tracking database access, what happened to your application audit trails. EDR provides fantastic endpoint forensics but doesn't satisfy regulations demanding comprehensive infrastructure logging.
Author: Ethan Caldwel;
Source: williamalmonte.net
How SIEM and EDR Work
The technical architectures reveal why these platforms excel at different tasks. They process information differently, store data differently, and integrate into security workflows differently.
SIEM Architecture and Data Flow
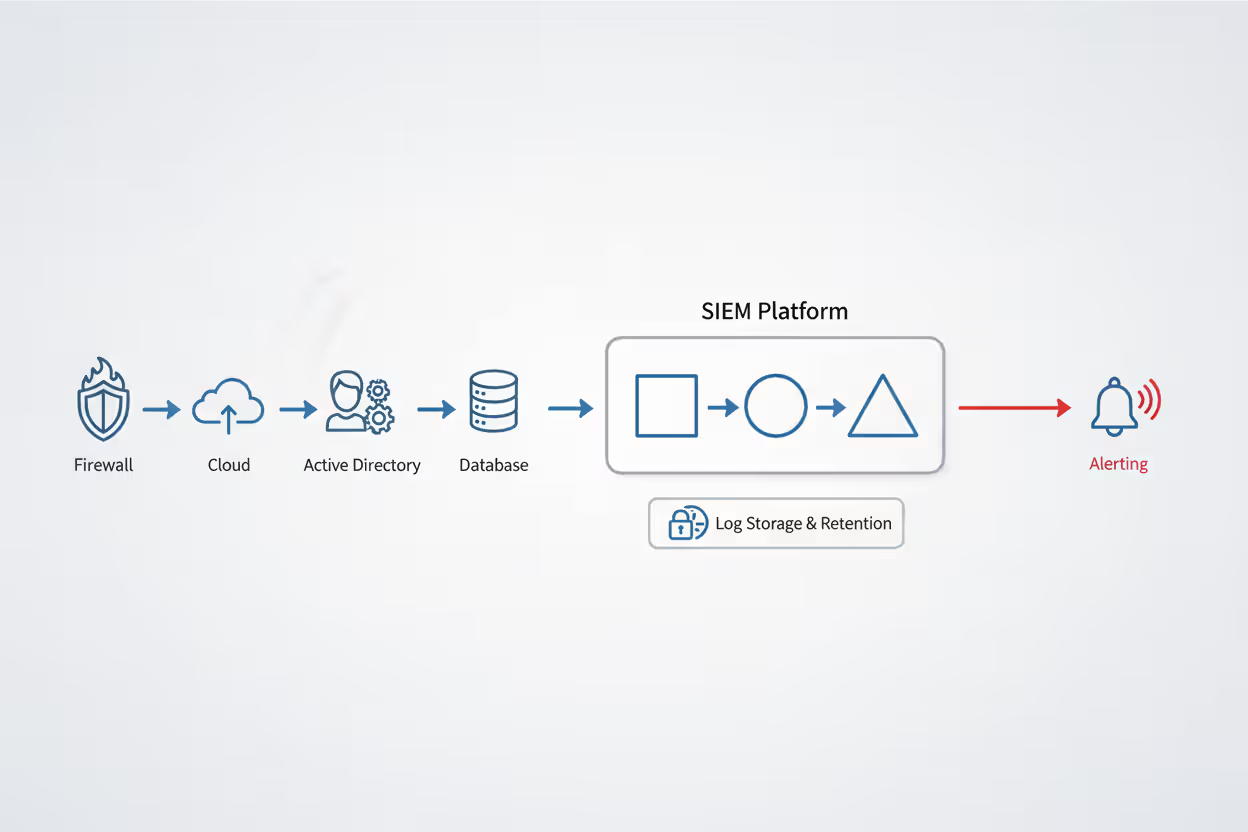
SIEM platforms run a collection-normalization-correlation-alerting pipeline. Log collectors grab events from source systems using whatever method works—syslog from network devices, API integrations with cloud services, Windows Event Forwarding from servers, file monitoring for application logs, database queries for custom systems. Large organizations configure 200+ different data sources.
Raw logs arrive in wildly inconsistent formats. JSON from AWS, Common Event Format from Palo Alto firewalls, Windows Event XML from domain controllers, plain text syslog from ancient Unix boxes. SIEM parsers normalize everything into a unified schema. A failed login becomes standardized whether it came from Active Directory, an SSH server, or Salesforce.
Correlation engines apply detection rules to normalized events. Simple correlations flag five failed logins from the same account within 60 seconds. Complex correlations spot multi-stage attacks: new account created, added to Domain Admins group, used to access file servers, exfiltrated data to cloud storage—all within a 30-minute window. Each event alone looks innocent; together they scream "compromise."
Storage tiers balance performance against cost. Hot storage keeps the last 30-90 days searchable in seconds using expensive SSD arrays. Warm storage holds 6-12 months on cheaper spinning disks with slower query performance. Cold storage archives years of data on object storage for compliance, retrievable but slow. Organizations commonly spend more on SIEM storage than SIEM licensing.
Today's SIEM platforms use machine learning to establish behavioral baselines. They learn that accounting staff typically access finance applications between 8 AM and 6 PM on weekdays, transferring about 50 MB daily. When someone from accounting starts downloading 10 GB of customer data at 3 AM on Sunday, behavioral analytics flag this deviation even without explicit rules being violated.
EDR Architecture and Data Flow
EDR agents live in kernel space on endpoints, hooking into core operating system functions. They observe every process creation, file read/write, registry modification, network socket, memory allocation, and DLL injection. This privileged access means EDR sees everything happening on that device.

Author: Ethan Caldwel;
Source: williamalmonte.net
Behavioral engines evaluate activities against known attack patterns. The MITRE ATT&CK framework catalogs hundreds of adversary techniques—credential dumping from LSASS memory, persistence via registry run keys, lateral movement through WMI, defense evasion by disabling antivirus. When EDR observes behaviors matching these documented techniques, it generates high-confidence alerts tied to specific attack stages.
Telemetry streams to management consoles running in vendor clouds or on-premises datacenters. Bandwidth optimization matters enormously—you can't send gigabytes of telemetry from thousands of endpoints without crushing your network. Agents send suspicious events immediately, batch routine telemetry periodically, and only transmit full forensic detail (packet captures, memory dumps) when analysts specifically request it.
Threat intelligence enriches EDR detections continuously. When an endpoint reaches out to a domain appearing on threat feeds as a known command-and-control server, EDR flags this communication instantly. File hash matching identifies known-malicious binaries even when attackers use packers, obfuscators, or other evasion techniques to slip past traditional signatures.
Response actions execute through the persistent agent-console connection. Analysts click "isolate," and the agent blocks all network traffic except the management channel—attacker loses access while security teams maintain control. Remediation scripts run locally on endpoints: delete malicious files, remove persistence mechanisms, patch vulnerable applications, reset credentials. This closed-loop workflow—detect, investigate, contain, remediate—happens without IT staff needing physical access to compromised devices.
When to Use SIEM vs EDR
No universal answer exists. What works for a 50-person startup differs completely from what a 5,000-employee financial institution needs.
Company size and security maturity drive practical decisions. Small businesses with 30 employees and basic infrastructure find SIEM overwhelming. You need someone to write correlation rules, tune false positives, integrate data sources, and interpret alerts. Most small businesses lack these resources. Starting with EDR delivers immediate endpoint protection—install agents, enable policies, done. The learning curve stays manageable.
Mid-sized companies between 200 and 2,000 employees typically need both platforms. Compliance requirements kick in at this scale. You're processing credit cards, handling health data, or storing customer information that regulations cover. Simultaneously, your endpoint count justifies EDR investment—ransomware hitting 500 workstations causes catastrophic business disruption. The challenge becomes making these platforms share intelligence instead of operating as isolated tools.
Compliance mandates force SIEM adoption. Healthcare organizations handling protected health information can't satisfy HIPAA audits without centralized logging and multi-year retention. Payment processors need PCI-DSS compliance, which explicitly requires log aggregation, correlation, and monitoring across the cardholder data environment. Government contractors face NIST 800-171 or CMMC requirements demanding audit trails. EDR doesn't fulfill these mandates because auditors want logs from network devices, applications, databases, and infrastructure—not just endpoints.
Your threat landscape shapes tool prioritization. Facing nation-state adversaries conducting long-term espionage campaigns? You need both platforms. SIEM detects reconnaissance activities, lateral movement between network segments, and data exfiltration disguised as normal business traffic. EDR catches initial compromises, privilege escalation on endpoints, and attacker tooling. Advanced persistent threats move across both domains; defending against them requires comprehensive coverage.
Worried primarily about ransomware? Prioritize EDR. Ransomware gangs target endpoints—phishing emails, drive-by downloads, vulnerable RDP servers. They escalate privileges locally, disable security tools, encrypt files, and demand payment. EDR's behavioral monitoring catches these attack chains as they unfold. The platform can isolate infected machines within seconds, before encryption spreads to network shares. SIEM helps during post-incident investigation but lacks the response speed to stop ransomware mid-attack.
Existing infrastructure affects deployment effort. Already collecting logs for IT operations—troubleshooting application issues, monitoring server performance, tracking capacity utilization? You've built half the SIEM infrastructure already. Adding security correlation becomes incrementally cheaper. Conversely, starting from zero means deploying log collectors, configuring hundreds of integrations, and building storage infrastructure before you get security value.
Budget constraints demand hard choices. EDR typically runs $40-80 per endpoint annually for mid-tier products. A company with 500 endpoints spends $20,000-40,000 yearly. SIEM costs vary wildly based on data volume but easily reach $150,000-300,000 annually for organizations ingesting 1 TB daily once you factor in storage, professional services, and ongoing tuning. Budget-limited organizations often deploy EDR first for immediate protection, adding SIEM later when compliance demands or budget allows.
Using SIEM and EDR Together
Security leaders increasingly reject the "or" question. Mature organizations deploy both platforms in integrated architectures, creating capabilities neither achieves alone.
Integration transforms these tools from separate point solutions into unified detection and response workflows. Feed EDR telemetry into SIEM as another data source. When SIEM correlation detects suspicious patterns—maybe unusual database queries combined with VPN access from a new country—analysts pivot to EDR for detailed endpoint forensics. This workflow combines SIEM's infrastructure-wide visibility with EDR's deep endpoint investigation capabilities.
Walk through a realistic incident. Your SIEM correlates several concerning events: a service account that normally runs automated reports suddenly authenticated from an unusual subnet, accessed sensitive HR databases outside business hours, and queried employee salary tables. Correlation rules flag this as potential insider threat. Analysts query EDR to examine the server where this service account executed. EDR forensics reveal credential-dumping malware ran 45 minutes before the suspicious database access. The timeline snaps into focus—credential theft enabled database compromise. You couldn't reconstruct this attack sequence with either tool alone.
Automated response workflows leverage both platforms simultaneously. SIEM correlation rules trigger EDR containment actions automatically. When SIEM detects ransomware indicators—perhaps unusual authentication patterns combined with mass file modifications on network shares—it instructs EDR to immediately isolate potentially compromised endpoints. This automated containment executes in under 10 seconds, limiting damage before human analysts even review alerts.
Organizations integrating SIEM and EDR reduce mean time to respond by roughly 40% compared to running these platforms separately. The integration enables closed-loop security operations where broad detection feeds precise response actions seamlessly
— Allie Mellen
Threat hunting benefits enormously from combined platforms. Hunters develop hypotheses about adversary behavior based on recent threat intelligence—"maybe attackers are exploiting this new Windows vulnerability." Use SIEM to search across the entire environment for indicators: unusual PowerShell execution, suspicious network connections, abnormal authentication patterns. SIEM narrows 10,000 endpoints down to 20 candidates. Then pivot to EDR for deep forensic investigation on those 20 systems. This iterative process—broad search narrowing to focused investigation—plays to each platform's strengths.
Implementation challenges absolutely exist. Integration requires API connections, data format mapping, and workflow automation that doesn't happen automatically. Security teams need analysts skilled in both platforms—SIEM correlation logic AND endpoint forensics. Alert correlation between systems can create noise if tuning isn't careful. Successful implementations treat integration as a first-class deployment requirement, not an afterthought.
Common Mistakes When Choosing Between SIEM and EDR
Organizations repeatedly make the same errors during evaluation and deployment. Learning from others' mistakes beats learning from your own.
Mistake: Assuming EDR satisfies compliance requirements. Technical teams sometimes deploy EDR thinking it checks the "security monitoring" box for compliance. Then auditors arrive asking for three years of firewall logs, database access records, and application audit trails. EDR provides none of these. This mistake happens when security teams make purchasing decisions without involving compliance stakeholders. PCI audits, HIPAA assessments, and SOX reviews expect specific log types EDR doesn't collect.
Mistake: Deploying SIEM without defined use cases. Some companies buy SIEM because "enterprises run SIEM" without articulating what threats they'll detect or which compliance requirements they'll satisfy. They ingest logs, configure vendor-provided rules, then wonder why alerts seem meaningless. SIEM platforms demand investment—custom correlation rules aligned to your environment, integration with incident response processes, continuous tuning. Without this effort, you've bought an expensive log storage system that generates false positives.
Mistake: Underestimating staffing requirements. Both platforms need skilled operators. SIEM demands analysts who understand diverse log formats, correlation logic, and how attacks manifest across different systems. EDR requires endpoint forensics expertise, malware analysis skills, and deep operating system knowledge. Organizations deploying these tools without adequate staffing see terrible detection rates, slow response times, and alert fatigue. The technology only works if competent people operate it.

Author: Ethan Caldwel;
Source: williamalmonte.net
Mistake: Ignoring integration during vendor selection. Buying best-of-breed SIEM from one vendor and best-of-breed EDR from another sounds smart until you realize their APIs barely communicate. Analysts manually copy indicators between platforms, maintain duplicate workflows, and waste time context-switching. This operational friction destroys the complementary value integrated platforms deliver. Evaluate integration quality during proof-of-concept testing, not after purchase orders are signed.
Mistake: Overlooking SIEM data volume costs. SIEM vendors often price based on daily data ingestion—maybe $X per GB per day. Organizations enable verbose debug logging from every source because "more data equals better security," then face sticker shock when monthly bills arrive. Smart deployment involves prioritizing high-signal data sources (authentication logs, security tool alerts, EDR telemetry) over low-signal noise (verbose application debugging, routine info-level messages). Not every log needs centralized collection and multi-year retention.
Mistake: Choosing based on feature checklists. Vendor presentations showcase impressive feature matrices showing hundreds of capabilities. But operational success depends on usability, documentation quality, community support, and vendor responsiveness when things break. Organizations prioritizing checkbox features over operational fit struggle with unintuitive interfaces, incomplete documentation, and frustrating support experiences. Evaluate what using the platform daily actually feels like, not what the feature list claims it can do.
Frequently Asked Questions About SIEM and EDR
Choosing between SIEM and EDR demands understanding your organizational context, compliance obligations, primary threats, and operational capabilities. These platforms serve complementary roles: SIEM delivers infrastructure-wide visibility with robust compliance features, while EDR provides deep endpoint investigation capabilities with rapid containment actions.
Organizations with adequate resources benefit from deploying both platforms in integrated architectures. This combination leverages SIEM's correlation capabilities alongside EDR's response speed, creating comprehensive detection and response workflows. Smaller organizations or those with limited security staffing might start with EDR for immediate threat protection, adding SIEM later as compliance needs or maturity increases.
Successful deployment depends less on vendor feature claims than operational fit, integration quality, and staffing capabilities. Define specific use cases before purchasing. Evaluate how platforms integrate during proof-of-concept testing. Ensure you have skilled analysts before deploying enterprise security tools. The security landscape in 2026 rewards thoughtful tool selection aligned with actual risks over checkbox compliance with vendor marketing.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.




