Endpoint malware protection concept on laptop screen with secured business devices
Endpoint Malware Protection Guide
Corporate networks lose over $6 trillion annually to cybercrime, with most breaches starting at a single device. Your employee's laptop at Starbucks, the warehouse tablet running inventory software, even the conference room's smart display—any connected device can hand attackers the keys to your infrastructure. That's where endpoint malware protection comes in, stopping attacks before they reach your core systems.
What Is Endpoint Malware Protection
Endpoint malware protection is security software installed directly on devices to find, block, and remove malicious programs before damage occurs. Think of it as a security guard stationed at every door rather than just the building entrance.
What counts as an endpoint? Any device that connects to your company network qualifies. Desktop computers and laptops obviously make the list. So do smartphones and tablets your team uses for email. Servers hosting applications count too. Point-of-sale terminals at retail counters. Medical devices in hospitals. Factory floor sensors. That smart thermostat in the breakroom. If it has an IP address and touches your network, it's an endpoint.
Here's the core concept: protect every single access point. Perimeter security—firewalls and intrusion detection at the network boundary—used to be enough when everyone worked in the office. Not anymore. Your sales team connects from hotel rooms. Developers push code from home. Partners access your systems through their own devices. SaaS applications live entirely outside your network perimeter.
The traditional castle-and-moat approach doesn't work when there's no castle.
A single infected laptop can devastate your infrastructure. Attackers establish a foothold there, then move sideways to file servers, databases, and email systems. Verizon's 2025 breach analysis found endpoint compromise triggered 68% of successful attacks—higher than any other entry vector.
Why does endpoint security matter so much? Three reasons stand out. First, these devices store valuable information locally. Cached files, saved passwords, email copies, browser history. Second, compromised endpoints give authenticated access to bigger targets. That infected laptop logs into systems using legitimate credentials. Third, humans introduce chaos. They download attachments, click links, install browser extensions, plug in USB drives. Even well-trained employees make mistakes when rushed or distracted.

Author: Daniel Prescott;
Source: williamalmonte.net
How Endpoint Malware Protection Works
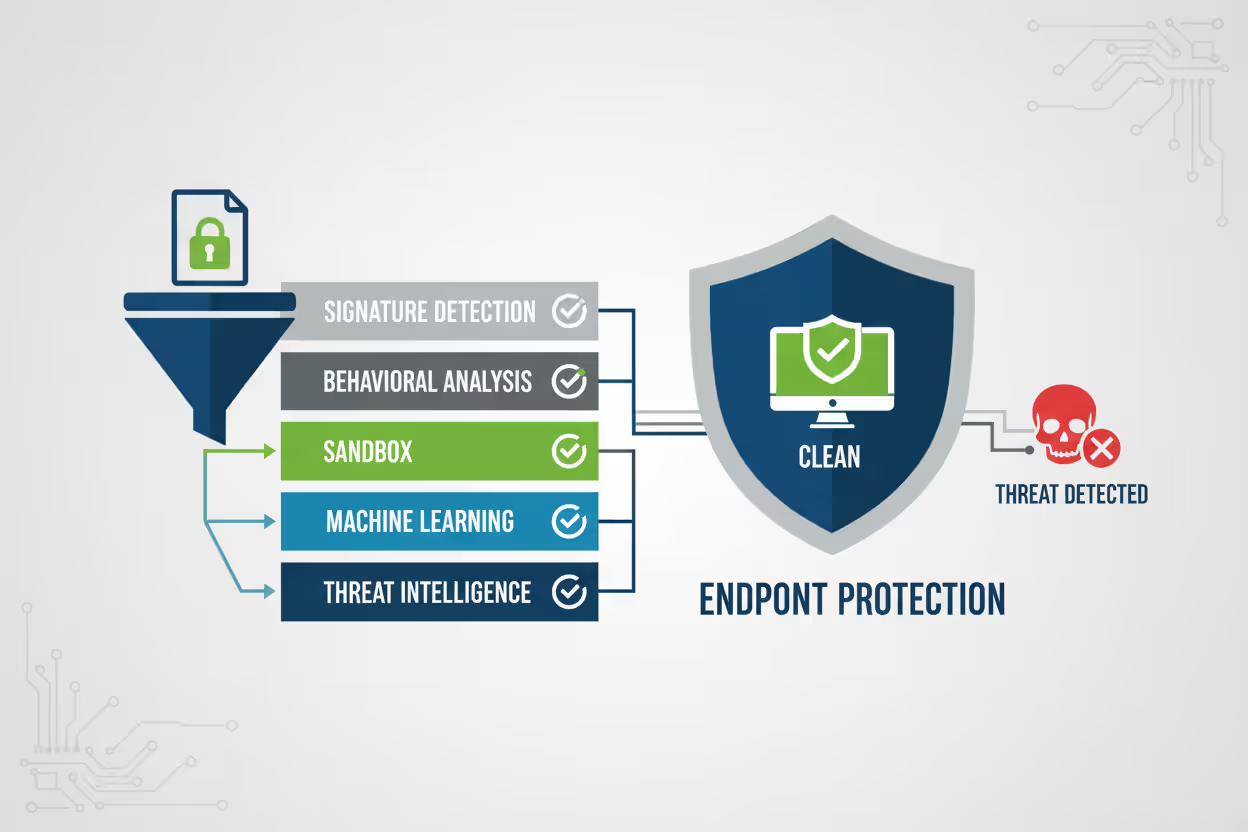
Modern endpoint protection layers multiple detection methods because no single technique catches everything. Understanding how endpoint malware protection works means looking at each layer.
Signature-based detection matches files against a database of known threats. Every malware family leaves distinct code patterns—like fingerprints at a crime scene. When a file matches those patterns, the software quarantines it immediately. This approach works great against established threats like three-year-old ransomware variants still circulating via spam. The weakness? Brand-new malware with no fingerprints on file slips right through. Signature databases need updates constantly, sometimes six times a day during active outbreaks.
Behavioral analysis watches what programs do rather than what they look like. A document editing application shouldn't encrypt hundreds of files per second. Legitimate software doesn't usually modify system startup settings without user permission. When programs act suspiciously, behavioral engines flag them even without matching any signatures. This catches polymorphic malware that rewrites its own code with each infection, changing its fingerprints every time.
Sandboxing runs suspicious files inside a fake computer environment before allowing them onto the real system. The sandbox looks like Windows to the malware, but it's actually a simulation recording every action. Does the file try calling home to an IP address in Romania? Inject code into memory? Disable security services? If yes, the real endpoint never sees it. If the file behaves normally, it's released from sandbox quarantine.
Machine learning models examine thousands of file characteristics simultaneously—how it was compiled, which APIs it calls, mathematical entropy measurements, metadata patterns. Trained on millions of malware samples, these algorithms spot malicious files nobody has encountered before. They provide zero-day protection without waiting for signature updates to arrive from the vendor.
Real-time scanning intercepts files the moment they're downloaded, opened, or executed. Nothing runs without scrutiny. Scheduled background scans sweep the entire drive periodically, catching threats that landed while the system was offline. Memory scanning finds fileless malware living only in RAM, never writing to disk where traditional scanners look.
Threat intelligence integration connects your endpoints to global threat databases tracking active campaigns. When ransomware hits companies in Japan overnight, your U.S. endpoints know about it by morning. This collective defense dramatically shrinks the window between threat emergence and protection.
Here's the typical flow: Your CFO downloads a PDF invoice attachment. Real-time scanning intercepts it before Acrobat opens. First check—does it match any known malware signatures? No match found. Second check—does its file structure exhibit suspicious characteristics? Machine learning algorithms analyze it in milliseconds. Borderline suspicious score. Third step—sandbox execution. The PDF runs in isolation, attempting to exploit an Acrobat vulnerability to download additional payloads. Behavioral analysis catches the download attempt to an unrecognized domain. Blocked. The CFO sees "Potentially malicious attachment quarantined" and calls IT.
Core Components of Endpoint Malware Protection
Antivirus and Anti-Malware Engines
The detection engine forms the foundation, scanning files, running processes, and active memory for malicious code. Modern engines combine signature matching with heuristic rules—logical patterns identifying suspicious behavior even in unknown files. For instance, a heuristic might trigger on any executable that immediately attempts disabling Windows Update, a common malware tactic.
These engines run at the kernel level, inserting themselves between applications and the operating system. When ransomware tries encrypting your Documents folder, the engine sees that system call before it executes and can block it. Quarantine zones safely store suspicious files for analysis without risking infection. Performance tuning ensures scans don't consume all CPU cycles—security teams constantly balance thoroughness against usability complaints.
Author: Daniel Prescott;
Source: williamalmonte.net
Firewall and Network Controls
Host-based firewalls control traffic directly on each device, separate from network firewalls. They enforce which applications can communicate externally and which network ports stay open. When malware attempts calling its command server in Bulgaria, network controls cut the connection.
Advanced versions include DNS filtering, blocking lookup requests for known malicious domains. Deep packet inspection examines traffic content, not just addresses. If ransomware tries contacting a Bitcoin wallet tied to previous campaigns, network controls see it and block the transaction. These controls also prevent lateral movement—stopping infected Endpoint A from attacking Endpoint B across your internal network.
Endpoint Detection and Response (EDR)
EDR assumes prevention sometimes fails and focuses on rapid detection plus response. Traditional antivirus tries stopping threats at the gate. EDR prepares for enemies who break through.
EDR agents continuously record endpoint activity, creating detailed forensic timelines. Process creation events. File modifications. Network connections. Registry changes. When something suspicious occurs, analysts see exactly what happened—which process spawned malicious activity, what files it touched, where it tried communicating. This investigation capability transforms vague alerts into actionable intelligence.
Threat hunting becomes possible—security teams proactively search for compromise indicators across thousands of endpoints simultaneously. Automated response capabilities isolate infected devices from the network instantly, kill malicious processes, or roll back file encryption using volume shadow copies.
Application Whitelisting and Control
Whitelisting inverts the security model. Instead of identifying bad software, you specify good software. Only approved applications execute. Everything else gets blocked automatically. This proves highly effective in stable environments—point-of-sale systems running the same three applications for years, or industrial controllers where unauthorized software could cause physical damage.
Application control offers more flexibility, allowing broad software categories while restricting dangerous behaviors. Users can run Microsoft Office but cannot execute PowerShell scripts from email attachments. Word processors work normally but cannot launch CMD.exe with hidden windows—a fileless malware technique. This balanced approach accommodates legitimate work without opening common attack vectors.
Author: Daniel Prescott;
Source: williamalmonte.net
Types of Endpoint Malware Protection Solutions
Real-world endpoint malware protection examples help match solutions to organizational needs.
Traditional antivirus uses signature databases and basic heuristics. These products update definitions regularly and scan files on access or schedule. They handle known threats well but miss sophisticated attacks. Traditional AV fits small businesses with straightforward needs and limited budgets. Windows Defender provides baseline protection built into the operating system at no additional licensing cost.
Next-generation antivirus (NGAV) adds machine learning, behavioral analysis, and cloud threat intelligence to the signature foundation. NGAV catches zero-day exploits and fileless attacks that evade signature detection. Updates matter less because algorithms adapt to threat patterns rather than specific signatures. CrowdStrike Falcon and SentinelOne represent leading NGAV platforms, using lightweight agents that process data in the cloud rather than consuming endpoint resources.
Endpoint Detection and Response (EDR) builds investigation and response capabilities on top of NGAV detection. EDR platforms like Carbon Black and Microsoft Defender for Endpoint deliver forensic timelines, threat hunting interfaces, and automated remediation actions. Security operations centers rely on EDR to investigate alerts, map attack chains, and contain breaches mid-incident. EDR makes sense for organizations with dedicated security personnel who need visibility beyond simple "threat blocked" notifications.
Extended Detection and Response (XDR) correlates endpoint data with network traffic, cloud workloads, email security logs, and identity systems into unified analysis. XDR platforms connect dots across security domains to reveal complex attacks spanning multiple vectors. For example, XDR might link a phishing email to subsequent endpoint compromise, then to lateral movement attempts visible in network logs. Palo Alto Cortex and Trend Micro Vision One offer XDR functionality, targeting enterprises with diverse security infrastructure requiring centralized visibility.
Managed Detection and Response (MDR) delivers EDR or XDR technology as a fully-managed service. Third-party security experts monitor your endpoints around the clock, investigate every alert, and respond to confirmed threats on your behalf. Organizations without internal security teams benefit enormously from MDR. Arctic Wolf and Rapid7 provide MDR services, essentially operating as outsourced security operations centers for companies that can't justify hiring full-time analysts.
Choosing depends on threat exposure, available budget, and staff capabilities. A dental practice might need NGAV with HIPAA compliance features. Investment firms likely require EDR with dedicated analysts investigating suspicious activity. A 50-person software company might choose MDR to access enterprise-grade protection without building a security department from scratch.
Common Threats Endpoint Protection Defends Against
Ransomware encrypts files and demands payment for decryption keys. Modern variants steal data before encrypting, threatening to publish customer records or trade secrets if victims refuse payment. Endpoint protection catches ransomware through behavioral analysis—massive file encryption triggers immediate alerts and automated device isolation. LockBit and BlackCat dominated 2025 attack campaigns, targeting healthcare and manufacturing sectors.
Author: Daniel Prescott;
Source: williamalmonte.net
Trojans masquerade as legitimate software while executing malicious code in the background. They log keystrokes, harvest credentials, or provide remote access to attackers. Banking trojans like Emotet specifically target financial data and payment systems. Endpoint protection identifies trojans through signature matching and behavioral monitoring that spots unexpected network connections or credential theft attempts.
Spyware monitors user activity without consent, recording passwords, browsing habits, and confidential documents. Corporate espionage campaigns deploy spyware on executive devices to steal strategic plans and acquisition targets. Endpoint solutions detect spyware via memory scanning and monitoring for suspicious data collection behaviors like screenshot capture or keylogging.
Rootkits modify operating system code to hide malware presence and maintain persistent access even after reboots. They run at privileged levels below normal security software visibility. Advanced endpoint protection uses integrity checking to identify unauthorized system modifications and employs specialized removal tools that boot into protected modes to excise rootkit components.
Zero-day exploits attack previously unknown vulnerabilities before software vendors release patches. Signature-based detection completely fails here—there's no signature for unknown threats. Endpoint protection defends through behavioral analysis, exploit mitigation that blocks common exploitation techniques, and virtual patching that monitors vulnerable applications for attack attempts while you wait for official updates.
Fileless malware executes entirely in memory or through legitimate system tools like PowerShell and WMI, leaving no files for scanners to detect. Attackers favor this technique for stealth—traditional antivirus literally has nothing to scan. Endpoint protection counters fileless attacks through memory scanning, script execution monitoring, and behavioral analysis tracking abnormal usage of system administration tools.
Protection effectiveness varies dramatically by solution sophistication. Traditional signature-only antivirus might catch 60-70% of threats in independent testing. NGAV with machine learning reaches 95-98% detection rates. EDR doesn't prevent every infection, but it ensures rapid detection and containment—limiting damage even when prevention fails.
Choosing the Right Endpoint Malware Protection
We've moved past the idea that perfect prevention is achievable. The question isn't whether an endpoint gets compromised—it's how quickly you detect and contain it. Organizations need forensic visibility into device activity, not just alerts about blocked files. Speed matters more than perfection. The gap between detection and containment often determines whether you face a minor incident or a catastrophic breach
— Maria Chen
Business size drives requirements significantly. Small businesses need simple deployment, minimal ongoing management, and affordable per-device pricing. Cloud-based NGAV with centralized web consoles fits this profile perfectly. Enterprises need granular policy controls across departments, integration with existing SIEM and SOAR platforms, and the ability to scale across 10,000+ endpoints in dozens of locations worldwide.
Deployment model affects operational fit profoundly. Cloud-based solutions update automatically without internal infrastructure, making them perfect for remote workforces scattered across different regions. On-premise deployments offer tighter control over data and policy management but require dedicated servers and IT staff to maintain them. Hybrid approaches balance control with cloud convenience—management console in the cloud, agents reporting to local collectors in each office.
Integration capabilities determine whether endpoint protection fits your security ecosystem or creates information silos. Does it feed threat intelligence to your SIEM for correlation with firewall logs? Can it trigger automated responses through your SOAR playbooks? Does it support your identity provider for conditional access policies based on device health? Poor integration creates visibility gaps and manual copy-paste work between consoles.
Cost structure includes more than license fees. Calculate implementation costs—will you need consultants? Training expenses for IT staff? Ongoing management time? Per-endpoint licensing suits organizations with predictable device counts. Per-user licensing accommodates employees with multiple devices—laptop, tablet, phone. Watch for hidden costs like expensive false positive alerts that waste security team hours chasing ghosts.

Author: Daniel Prescott;
Source: williamalmonte.net
Scalability ensures the solution accommodates growth. Can it handle your projected endpoint count three years from now? Does management console performance degrade at 5,000+ devices? Does vendor support transition from helpful to nonexistent as you grow? Cloud platforms generally scale more smoothly than on-premise systems requiring hardware upgrades at capacity milestones.
Compliance requirements mandate specific capabilities. HIPAA demands encryption at rest and access audit trails. PCI-DSS requires file integrity monitoring on systems touching cardholder data. GDPR influences data residency and privacy controls around threat telemetry. Verify endpoint protection includes necessary compliance reporting and audit log retention before committing.
Performance impact affects user satisfaction and productivity. Lightweight agents offloading processing to cloud infrastructure minimize endpoint resource consumption. Heavy agents running constant full-disk scans cripple older hardware. Test solutions under realistic workloads before deployment—security software slowing workstations by 30% will face user rebellion and shadow IT workarounds.
Request proof-of-concept trials testing against your actual environment and threat samples. Evaluate management console usability—your team interacts with it daily. Review vendor support quality, especially incident response assistance during active breaches. Check independent test results from AV-TEST, AV-Comparatives, or MITRE ATT&CK evaluations for objective performance comparisons.
| Solution Type | Detection Method | Response Capabilities | Deployment Complexity | Ideal Use Case |
| Traditional Antivirus | Signature matching, basic heuristics | Quarantine and removal only | Simple setup | Small businesses needing basic protection |
| NGAV | Machine learning, behavioral analysis, cloud intelligence | Automated blocking and device isolation | Moderate setup | Organizations defending against modern threats |
| EDR | NGAV plus continuous activity recording | Investigation tools, threat hunting, automated remediation | Complex configuration | Enterprises with security operations teams |
| XDR | Cross-domain correlation with network and cloud data | Unified response across entire security stack | High complexity | Large enterprises with diverse infrastructure |
Frequently Asked Questions About Endpoint Malware Protection
Endpoint malware protection forms the cornerstone of practical cybersecurity. Work environments continue fragmenting—remote employees, contractor access, cloud applications, IoT devices. Threat actors grow more sophisticated with each passing year. Securing every device touching your network isn't optional anymore.
Effective endpoint security requires matching solution capabilities to your specific risk profile, technical environment, and operational capacity. Small businesses gain substantial protection from cloud-based NGAV requiring minimal management. Enterprises need EDR visibility and response capabilities to defend against targeted attacks. Companies without dedicated security staff should strongly consider MDR services rather than struggling with complex tools nobody fully understands.
Implementation determines whether security tools actually protect or just create compliance checkboxes. Deploy endpoint protection across every device without exception—that single unprotected laptop in accounting can compromise your entire infrastructure. Configure policies appropriately, balancing security requirements against usability to prevent user workarounds. Train employees to recognize phishing attempts and report suspicious activity. Test your response procedures quarterly through tabletop exercises and simulated breach scenarios.
This market keeps advancing rapidly. Machine learning models improve accuracy while reducing false positives that waste analyst time. XDR platforms unify visibility across previously siloed security domains. Automated response handles routine threats without human intervention, freeing security teams for complex investigations requiring judgment and creativity. Stay informed about emerging capabilities. Reassess your endpoint strategy annually as threats evolve and your organization grows.
Malware continues targeting endpoints because that's where work happens and data lives. Attacks won't decrease—they'll accelerate. Your defense must evolve alongside threats, moving beyond reactive signature updates toward proactive threat hunting and rapid incident response. Organizations that weather tomorrow's attacks invested in comprehensive endpoint protection today, before they needed it desperately during an active breach.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.