Cybersecurity dashboard comparing EDR and XDR across enterprise infrastructure
EDR vs XDR Security Solutions Guide
Choosing security platforms isn't straightforward anymore. You've probably heard vendors pitching both Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR), each claiming their approach stops threats better. Here's the reality: these technologies solve different problems, and picking the wrong one wastes money and leaves gaps attackers will exploit.
What Are EDR and XDR Security Solutions?
Think of EDR and XDR as two different cameras watching for intruders. EDR gives you a detailed close-up of what's happening at each door and window (your endpoints). XDR gives you a wide-angle view of your entire property, showing how an intruder might sneak through the backyard, climb over the fence, and enter through the basement—connecting dots across multiple entry points. Understanding edr vs xdr explained helps you stop buying security theater and start deploying defenses that actually catch attackers.
Understanding Endpoint Detection and Response (EDR)
EDR puts monitoring software directly on every computer, laptop, server, and mobile device you own. These agents watch everything: what programs start running, which files get modified, when someone changes system settings, and which network connections applications make.
Here's what that looks like in practice. Your marketing director opens an email attachment. The file runs a script that starts encrypting Word documents one after another—classic ransomware behavior. Your EDR sees this pattern instantly: "Why is this random attachment encrypting 87 files in under a minute?" It triggers an alert, cuts that laptop off from your network, and kills the malicious process. The ransomware gets trapped on one machine instead of spreading across 500 computers.
EDR excels at reconstruction. After an incident, security teams can replay exactly what happened on that compromised device. They'll see which browser downloaded the payload at 2:47 PM, how it gained administrative privileges at 2:48 PM, what registry keys it modified at 2:49 PM, and which file server it tried accessing at 2:50 PM. That granular timeline helps you understand attacker techniques and fix the vulnerability they exploited.

Author: Marcus Halbrook;
Source: williamalmonte.net
Manufacturing companies love EDR for production floor computers. Retailers deploy it heavily on point-of-sale terminals. Anywhere you're worried about malware infecting individual machines, EDR delivers focused protection. A construction firm with 200 laptops running AutoCAD can deploy EDR in three weeks and immediately start catching malware that traditional antivirus misses.
Understanding Extended Detection and Response (XDR)
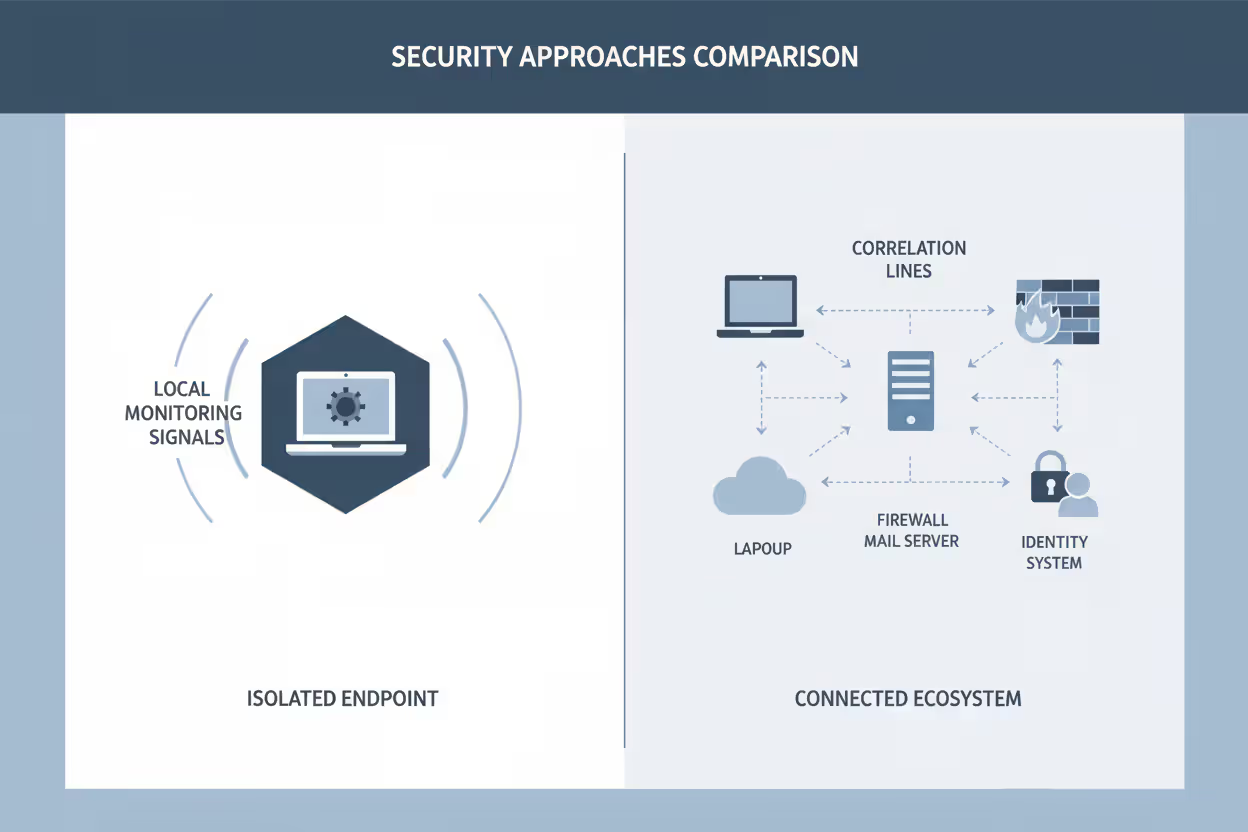
XDR collects security information from everywhere—not just endpoints. It pulls data from your firewall logs, cloud service activities, email gateway records, identity management systems, and network traffic captures, then analyzes everything together looking for attack patterns that span multiple systems.
Here's why that matters. An attacker sends your CFO a phishing email (your email gateway logs this). She clicks the link and enters credentials on a fake Office 365 login page (your web filter sees this). The attacker uses those stolen credentials to log in from Bulgaria (your identity system flags the unusual location). He accesses SharePoint and downloads your financial projections (cloud security logs this). Then he uploads files to a personal Dropbox account (your DLP system catches this).
EDR would only see two pieces: the initial email click and maybe the Dropbox upload if it happened through an endpoint. XDR connects all five events into one coherent incident: "Credential phishing attack led to unauthorized data exfiltration." You see the complete story, not isolated fragments.
This consolidated perspective transforms how security teams work. Instead of investigating five separate alerts from five different tools—manually figuring out they're related—analysts get one incident showing the entire attack sequence. Response time drops from hours to minutes because you're not puzzling together which alerts actually connect.
Author: Marcus Halbrook;
Source: williamalmonte.net
Core Differences Between EDR and XDR
The edr vs xdr differences change how much you see and what you can do about threats.
What data they collect: EDR watches what happens on devices—period. Every process execution, file modification, network connection, and registry change gets logged, but only if it occurs on a monitored endpoint. XDR vacuums up telemetry from everywhere: endpoints plus network packets, cloud API calls, email metadata, authentication logs, and vulnerability scan results. An attack that stays off endpoints entirely (like cloud account compromise) shows up clearly in XDR but remains invisible to EDR.
How they spot threats: EDR applies behavioral analysis specifically to device activities. It knows normal processes don't usually inject code into other applications' memory space. When PowerShell starts exhibiting that behavior, EDR flags it immediately. XDR identifies multi-stage attack sequences by connecting events across different infrastructure layers. It recognizes that someone logging in from Malaysia at 3 AM, immediately accessing Salesforce despite never using it before, then downloading 50,000 customer records represents a coordinated attack—even though each individual event looks potentially legitimate in isolation.
Integration architecture: EDR connects to other security tools through standard APIs if you need that functionality—it wasn't designed primarily for integration. XDR exists specifically as an integration hub with pre-built connectors for dozens of security products. Those connectors handle complex data normalization so a Palo Alto firewall log and a Microsoft cloud log can be analyzed together meaningfully. Building those integrations yourself takes months; XDR includes them out of the box.
Response capabilities: When EDR detects ransomware, it isolates that specific computer, stops malicious processes, and quarantines infected files. Those response actions target only the compromised device. XDR coordinates responses across your entire security stack simultaneously: blocking the malware distribution server at your firewall, pulling the original phishing email from every employee's inbox, disabling the compromised account in Active Directory, and isolating all devices that communicated with the attacker's infrastructure—one coordinated containment workflow instead of manual actions across five different consoles.
Operational complexity: Running EDR requires deploying agents, tuning detection policies, and training analysts on endpoint investigation. Most security teams handle this within their existing capabilities. XDR demands you architect integrations, normalize data from disparate sources, build correlation rules spanning multiple security domains, and design orchestrated response workflows. Organizations with one or two security people often can't operate XDR effectively—there's just too much to configure and maintain.
Here's how they compare across critical factors:
| Factor | EDR | XDR |
| What It Monitors | Only endpoint agents | Endpoints, networks, email, cloud platforms, identity systems |
| Detection View | Individual device behaviors | Attack patterns across infrastructure |
| How It Connects | Standard APIs when needed | Pre-built integration hub |
| Threat Analysis | Events on single devices | Correlated activity across security layers |
| Response Actions | Isolate and contain devices | Coordinate responses across security stack |
| Best Fit Company Size | 50-2,000 employees | 500+ employees |
| Typical Deployment | 3-5 weeks | 3-7 months |
How EDR and XDR Handle Threat Detection
The edr vs xdr comparison guide shows detection methods differ dramatically based on what each platform can actually see.
EDR establishes what's normal for each device, then alerts on deviations. It learns that your accounting computers typically run QuickBooks, Excel, and Outlook—not Python scripts or network scanning tools. When a process starts probing your internal network from an accounting workstation, EDR recognizes that's abnormal behavior for that specific device and investigates. Threat intelligence feeds supplement behavioral detection by identifying known-bad file hashes, malicious domains, and attacker IP addresses observed on endpoints.
Hunting for threats in EDR means querying your endpoint database. You might search for every device that executed a specific PowerShell command, contacted a suspicious domain, or loaded a particular DLL file. EDR provides SQL-like query interfaces for filtering and aggregating across thousands of endpoints. An analyst investigating potential compromise can ask: "Show me every machine that launched cmd.exe as a child process of Microsoft Word in the last 30 days." That unusual parent-child process relationship often indicates attackers exploiting Office macros.
XDR recognizes attack progressions that span multiple security tools. Consider business email compromise: attackers send a convincing invoice change request appearing to come from your CEO (email security logs the message). An accounts payable clerk clicks the link (web filtering records the click). The page harvests her credentials (authentication system logs a failed login from Romania). The attacker uses those credentials successfully after solving the MFA prompt through a proxy service (identity logs show access from a TOR exit node). He changes the bank account information for your largest vendor (application logs capture the modification). He sends an updated invoice (email gateway logs outbound message).
Each event looks potentially benign independently. Emails go out constantly. Failed logins happen daily when people mistype passwords. Vendor information gets updated regularly. But XDR identifies this specific sequence matches business email compromise tactics: initial phishing, credential harvesting, authentication from suspicious geography, rapid privilege use, and financial system modification. The correlation algorithm connects these six events from five different security tools into one high-confidence incident.
Cloud-native attacks highlight XDR's advantage clearly. An attacker compromises your AWS credentials through a phishing attack. He logs into your AWS console exclusively through a web browser—no software touches endpoints. He spins up cryptocurrency mining instances, costing you $14,000 in two days. EDR detects the initial phishing click but completely misses the AWS abuse because it happens entirely in the cloud. XDR correlates the phishing email, suspicious authentication patterns (login from a country your organization never operates in), unusual AWS API calls (launching 50 instances simultaneously), and abnormal cloud spending alerts into one incident showing credential compromise leading to resource abuse.

Author: Marcus Halbrook;
Source: williamalmonte.net
Alert correlation saves massive analyst time. EDR generates separate alerts for each suspicious device event. Your team sees 150 alerts in a shift: 50 from endpoints, 40 from network security, 35 from email gateway, 25 from cloud security. Analysts manually investigate which alerts represent one sophisticated attack versus 150 unrelated minor issues. That manual correlation takes 4-6 hours for experienced analysts.
XDR automatically groups related alerts into incidents. Those same 150 security events get consolidated into 12 actual incidents—some containing 20 correlated alerts showing one attack's complete progression, others containing single alerts for isolated issues. Your team investigates 12 incidents instead of 150 individual alerts. Analyst productivity roughly quadruples because they're not spending hours manually connecting dots.
Response orchestration scope reflects visibility boundaries. EDR responds to ransomware by isolating infected devices, killing malicious processes, and potentially restoring files from shadow copies. Those actions contain the threat locally but don't address network-level indicators or email-based distribution. XDR coordinates simultaneous containment across every relevant security control: blocking the ransomware command-and-control server at your firewall, quarantining the distribution email from every mailbox, disabling the initially compromised account, isolating all devices showing ransomware indicators, and blocking the Bitcoin wallet address in your proxy. One coordinated response workflow addresses every attack vector immediately.
When to Choose EDR Over XDR
EDR makes more sense than XDR for specific situations—knowing when helps you avoid overspending on capabilities you can't effectively use. Here's when to use edr and xdr becomes clear based on practical constraints.
Budget limitations: XDR costs 50-80% more than comparable EDR platforms before you factor integration engineering, storage expansion, and operational overhead. Organizations with $75,000 security budgets achieve better risk reduction buying excellent EDR coverage for 500 endpoints than partial XDR implementation that only integrates two data sources due to budget constraints. Comprehensive protection at one layer beats incomplete visibility across multiple layers.
Simple IT infrastructure: XDR delivers value by correlating data from advanced network detection, sophisticated cloud security platforms, enterprise email gateways, and identity threat detection. Smaller organizations often lack these security investments. A dental practice with 15 computers, basic Microsoft 365, and a standard firewall gains minimal advantage from XDR's correlation features because there aren't multiple sophisticated security tools generating telemetry to correlate. That dental practice's primary risks—malware infections from malicious email attachments and compromised workstations—are threats EDR addresses directly.
Endpoint-focused threats: Manufacturing companies worried about production line computer infections, healthcare clinics protecting medical device workstations from ransomware, and retail stores securing point-of-sale terminals face predominantly endpoint-centric threats. EDR's deep device visibility and rapid containment capabilities address these risk scenarios without requiring XDR's additional complexity. A regional hospital network with 800 Windows workstations running electronic health record software might effectively manage its ransomware risk with comprehensive EDR deployment alone.
Small security teams: XDR requires diverse expertise spanning network forensics, cloud architecture, identity security, and endpoint protection. Organizations with one to three security staff typically lack this breadth of knowledge. A regional bank with two security analysts probably can't configure XDR integrations across ten security tools, develop meaningful correlation rules, tune detection algorithms across multiple domains, and maintain response playbooks effectively. EDR's narrower operational scope matches small team capabilities—they can develop strong endpoint investigation skills and operate the platform competently without requiring expertise across six security disciplines.
Fast deployment requirements: Regulators gave you 90 days to implement endpoint protection after your assessment revealed gaps. You need coverage operational quickly. EDR deploys in 3-4 weeks: distribute agents to devices, configure baseline policies, conduct initial tuning, and train analysts. XDR requires 4-7 months: design integration architecture, deploy platform, integrate data sources sequentially, develop correlation rules, configure orchestrated responses, conduct extensive tuning, and train staff across multiple domains. When time pressure matters, EDR's rapid deployment timeline often makes it the only realistic option.
Compliance mandates: HIPAA requires malware protection on systems containing protected health information. PCI-DSS mandates antivirus and endpoint logging for payment card data environments. Various regulations specify endpoint security controls that EDR satisfies directly without requiring XDR's broader correlation capabilities. A medical billing company primarily concerned with meeting compliance requirements might fulfill those obligations through EDR without justifying XDR's substantially higher investment.
When to Choose XDR Over EDR
XDR becomes the right choice when infrastructure complexity, threat sophistication, or operational challenges exceed what EDR can handle effectively. Knowing when to use edr and xdr depends on recognizing scenarios where correlation across security domains becomes critical.
Complex hybrid environments: Organizations running on-premises VMware alongside AWS, Azure, and Google Cloud, plus 30 SaaS applications and remote workforce infrastructure spanning home networks and coffee shops, face attacks that deliberately exploit boundaries between security domains. Attackers know EDR watches endpoints closely, so they minimize device-level footprints by abusing cloud services, stolen credentials, and legitimate administrative tools. XDR correlates subtle indicators across network, cloud, identity, and endpoint layers that EDR operating alone simply cannot see. A financial services firm with 2,000 employees across 12 offices, three cloud providers, and 40 SaaS applications probably needs XDR's cross-infrastructure visibility to detect sophisticated threats.
Advanced persistent threats: Nation-state attackers and organized criminal groups increasingly use "living off the land" techniques—legitimate Windows administration tools, valid stolen credentials, and cloud-native attack methods generating minimal endpoint telemetry. They specifically study what EDR detects and adjust tactics to evade device-level behavioral analytics. Attacks might involve compromising credentials through social engineering, authenticating legitimately to cloud services, abusing API access to exfiltrate data—all while barely touching endpoints. XDR detecting these attacks correlates authentication anomalies (logins from unusual locations), cloud behavior changes (first-time access to data repositories), and subtle network patterns (unusual data transfer volumes) that individually seem benign but collectively indicate compromise.
Alert fatigue: Your security team receives 3,000 daily alerts from separate endpoint, network, cloud, email, and identity tools. Analysts spend 70% of their time determining which alerts matter and which represent false positives or isolated low-severity events. They're burned out from alert triage and missing genuine threats buried in noise. XDR reduces alert volume 65-80% by automatically correlating related events into unified incidents. Those 3,000 alerts become 400 incidents, many containing multiple correlated alerts showing complete attack progressions. Analyst productivity improves dramatically because they investigate coherent incidents instead of isolated alert fragments.
Existing security investments: You've already deployed network traffic analysis, cloud security posture management, advanced email security, and user behavior analytics—spending $400,000 annually across these tools. They each generate valuable security telemetry, but operate independently. Your analysts manually correlate alerts across five different consoles, missing connections between events detected by different tools. XDR multiplies the value of existing investments by correlating their collective telemetry, giving you unified visibility you paid for but aren't currently achieving. Adding XDR creates synergy across tools rather than replacing them wholesale.
Cross-domain compliance requirements: Financial regulations require detecting coordinated attacks targeting trading systems, customer portals, and internal networks simultaneously. Healthcare standards mandate monitoring threats spanning electronic health records, billing systems, and telehealth platforms. Payment card requirements demand visibility into point-of-sale terminals, payment gateways, and administrative networks collectively. These regulatory frameworks increasingly recognize sophisticated attacks don't conveniently limit themselves to one security domain. XDR's unified detection architecture addresses cross-domain compliance requirements that managing separate security tools independently struggles to satisfy.
Security operations efficiency: Your organization wants to improve analyst effectiveness, reduce investigation time, and decrease burnout rates. XDR presents correlated incidents with enriched context rather than isolated alerts requiring manual investigation. It automates investigation workflows by querying multiple security tools simultaneously and consolidating findings. It enables coordinated response actions that would otherwise require manually logging into six different consoles and executing actions individually. Organizations implementing XDR report 50-70% reduction in time spent on alert triage and 40-60% improvement in mean time to respond—substantial operational benefits justifying the platform investment.
Too many security leaders treat the EDR versus XDR decision as purely technical—which platform has better features? That's backwards. Start by honestly assessing your infrastructure complexity, team capabilities, and operational maturity. I've watched mid-sized companies waste millions buying XDR they couldn't properly implement because their security team lacked the diverse skills required for effective operation. EDR remains the correct answer for many organizations if it matches their actual operational reality rather than aspirational vendor presentations
— Sarah Chen
EDR to XDR Migration Considerations
Moving from EDR to XDR isn't a straightforward upgrade—treat it as a security architecture transformation requiring careful planning, not a vendor swap you complete in one weekend.
Security tool inventory: Document every security product currently deployed before evaluating XDR platforms. List your network traffic analysis tools, cloud workload protection, email security gateway, identity threat detection, data loss prevention, and vulnerability management solutions. Then evaluate integration compatibility with candidate XDR platforms. Some XDR vendors build native integrations with specific products (Palo Alto Networks' XDR integrates deeply with Palo Alto firewalls and Prisma Cloud). Others support broader integration through standard APIs but with less rich data correlation. Organizations whose security tools lack compatible integration options face difficult choices: accept reduced correlation capabilities that undermine XDR's value, replace incompatible tools (expensive and disruptive), or reconsider whether XDR makes sense given current infrastructure.
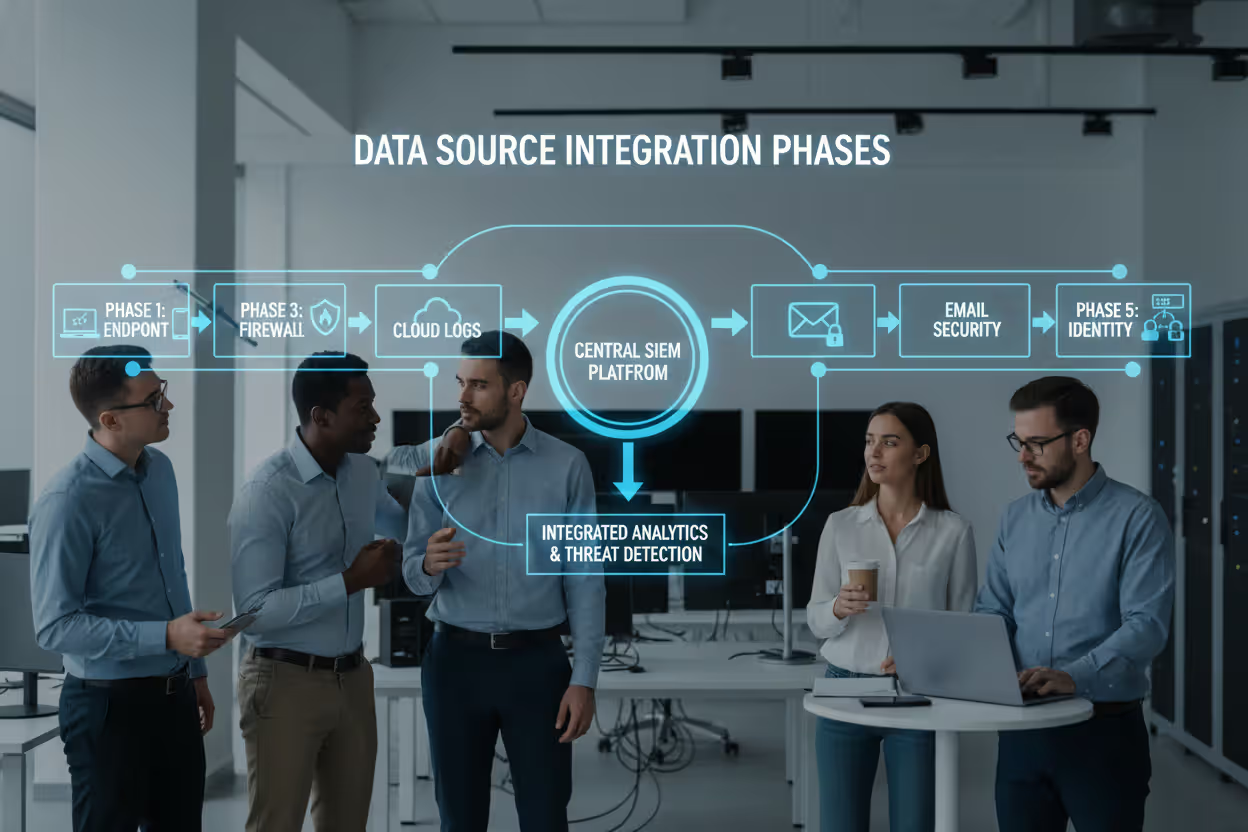
Phased data source integration: Don't attempt integrating all security tools simultaneously—that's a recipe for failed implementation. Prioritize data sources based on threat intelligence and risk assessments. Most organizations benefit starting with endpoint and network integration (catching the majority of common attacks), then progressively adding cloud security, email gateway, and identity management as operational confidence develops. A software company might integrate EDR and firewall first (month 1-2), add AWS CloudTrail and Azure logs next (month 3-4), then incorporate Office 365 Advanced Threat Protection (month 5-6). This staged approach delivers incremental value while keeping implementation complexity manageable.
Author: Marcus Halbrook;
Source: williamalmonte.net
Skills assessment: XDR requires working knowledge across multiple security disciplines that most endpoint-focused teams lack. Evaluate whether current security personnel can analyze network packet captures, understand cloud security architectures, investigate identity-based attacks, and configure security orchestration workflows. Many organizations discover their security team excels at endpoint forensics but lacks practical network analysis experience. Address skills gaps through training programs (expect 6-12 months for meaningful skill development) or hiring specialists with complementary expertise (cloud security analyst, network forensics specialist). Organizations frequently underestimate XDR's operational expertise requirements and struggle after deployment when their team can't effectively use the platform.
Total cost modeling: Budget comprehensively beyond platform licensing. XDR implementations involve platform licenses (typically $120-180 per user annually vs. $70-100 for EDR), professional services for integration engineering ($80,000-200,000 depending on complexity), additional storage infrastructure (XDR ingests 6-12× more data than EDR—plan for substantial storage expansion), and ongoing operational costs (analyst training, detection tuning specialists, playbook development). Model 24 months of total costs for accurate financial comparison. A 1,000-employee organization moving from EDR to XDR should budget $350,000-500,000 total investment over two years, not just the $120,000 license cost.
Incremental deployment approach: Maintain existing EDR while deploying XDR alongside it initially. Validate XDR detection capabilities against known attack scenarios. Train security staff through hands-on experience. Gradually transition operational reliance from EDR to XDR as confidence grows. This parallel operation maintains security effectiveness throughout transition. Avoid the temptation to rip out EDR immediately after XDR deployment—you need operational validation before depending entirely on the new platform. Organizations typically run both platforms 3-6 months before fully transitioning operational workflows.
Platform selection criteria: Prioritize integration breadth and operational usability over feature checklists. Demand proof-of-concept deployments testing detection of attack scenarios relevant to your specific environment: business email compromise if that's your primary concern, cloud account takeover if you're heavily cloud-native, or ransomware campaigns if that's your biggest risk. Evaluate investigation workflow efficiency—how many clicks does it take to investigate a correlated incident? Test response automation flexibility—can you configure coordinated responses matching your specific tools? Ask for customer references from organizations with similar infrastructure complexity and threat profiles, not generic reference lists.
Realistic timeline expectations: Complete EDR-to-XDR migrations require 9-15 months for organizations with 500-2,000 employees and 18-36 months for large enterprises with complex infrastructure. This timeline includes platform deployment (month 1-2), progressive data source integration (month 2-8), detection rule development and tuning (month 3-12), response workflow configuration and testing (month 4-10), comprehensive analyst training (month 2-9), and operational validation (month 6-15). Organizations expecting rapid migration frequently encounter operational disruptions, reduced security effectiveness during problematic transitions, and analyst frustration from inadequate training. Be realistic about timeline—rushing XDR implementation typically fails.
Common Questions About EDR and XDR
Selecting between EDR and XDR depends entirely on your specific operational context, not abstract feature comparisons or vendor marketing claims. EDR provides focused, cost-effective device protection that's appropriate for organizations with straightforward infrastructure, constrained budgets, or predominantly endpoint-centric threats. XDR delivers cross-infrastructure correlation and unified incident response valuable for complex environments, sophisticated threat exposure, and mature security programs with existing tool investments to leverage through integration.
Start by honestly assessing your current security maturity, infrastructure complexity, threat profile, and team capabilities. Companies with 50-500 employees, straightforward IT environments, and small security teams typically achieve superior ROI through robust EDR implementation across all devices. Larger organizations with hybrid cloud infrastructure, diverse security tool portfolios, and advanced persistent threat exposure benefit from XDR's correlation and automation—but only if they possess the operational maturity and staff expertise to implement it successfully.
Organizations considering advancement from EDR to XDR should adopt incremental approaches that reduce implementation risk and maintain security effectiveness throughout transition. Thoroughly assess existing security tools for integration compatibility, prioritize data source integration based on threat intelligence, address skills gaps through training or hiring, and model total costs realistically including often-overlooked operational expenses. Most importantly, recognize XDR success depends equally on technology deployment, operational maturity, staff expertise development, and organizational commitment to cross-domain security visibility—buying the platform doesn't automatically deliver its benefits without substantial implementation effort.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.