Zero trust endpoint security concept with secure devices and remote access
Zero Trust Endpoint Security Guide
Traditional perimeter defenses crumble when laptops leave the office, contractors access sensitive files from home, and cloud applications bypass the corporate firewall entirely. Zero trust endpoint security rebuilds protection from the ground up, treating every device—whether inside or outside your network—as a potential threat until proven otherwise.
What Is Zero Trust Endpoint Security?
Zero trust endpoint security is a framework that requires continuous verification of every device and user attempting to access corporate resources, regardless of location. Unlike perimeter-based models that assume everything inside the network is safe, zero trust operates on the principle: "never trust, always verify."
The shift matters because modern work environments no longer fit neatly inside a corporate perimeter. A sales manager accessing Salesforce from a hotel lobby, a contractor uploading designs from a coffee shop, and a finance director reviewing spreadsheets on a home laptop all represent legitimate business activity—and potential entry points for attackers.
Traditional security models established trust at the network boundary. Once a device connected to the corporate VPN or sat behind the firewall, it enjoyed broad access to internal systems. This approach worked reasonably well when employees worked from desks connected to Ethernet cables. It fails catastrophically when a compromised laptop carries malware directly past perimeter defenses or when stolen credentials grant attackers the same access as legitimate users.
Zero trust endpoint security basics start with eliminating the concept of a trusted network zone. Every access request triggers verification checks: Is this device running current security patches? Does the user's behavior match normal patterns? Does this application need access to this particular data? The system grants the minimum access required to complete the task, then revokes it when finished.
Author: Marcus Halbrook;
Source: williamalmonte.net
The "never trust, always verify" principle extends beyond initial authentication. A laptop that passed all security checks at 9 AM doesn't automatically retain that trust at 3 PM. Continuous monitoring detects when devices fall out of compliance—missing a critical security update, exhibiting suspicious network behavior, or showing signs of compromise. Access adapts in real time based on current risk levels rather than one-time authentication events.
How Zero Trust Endpoint Security Works
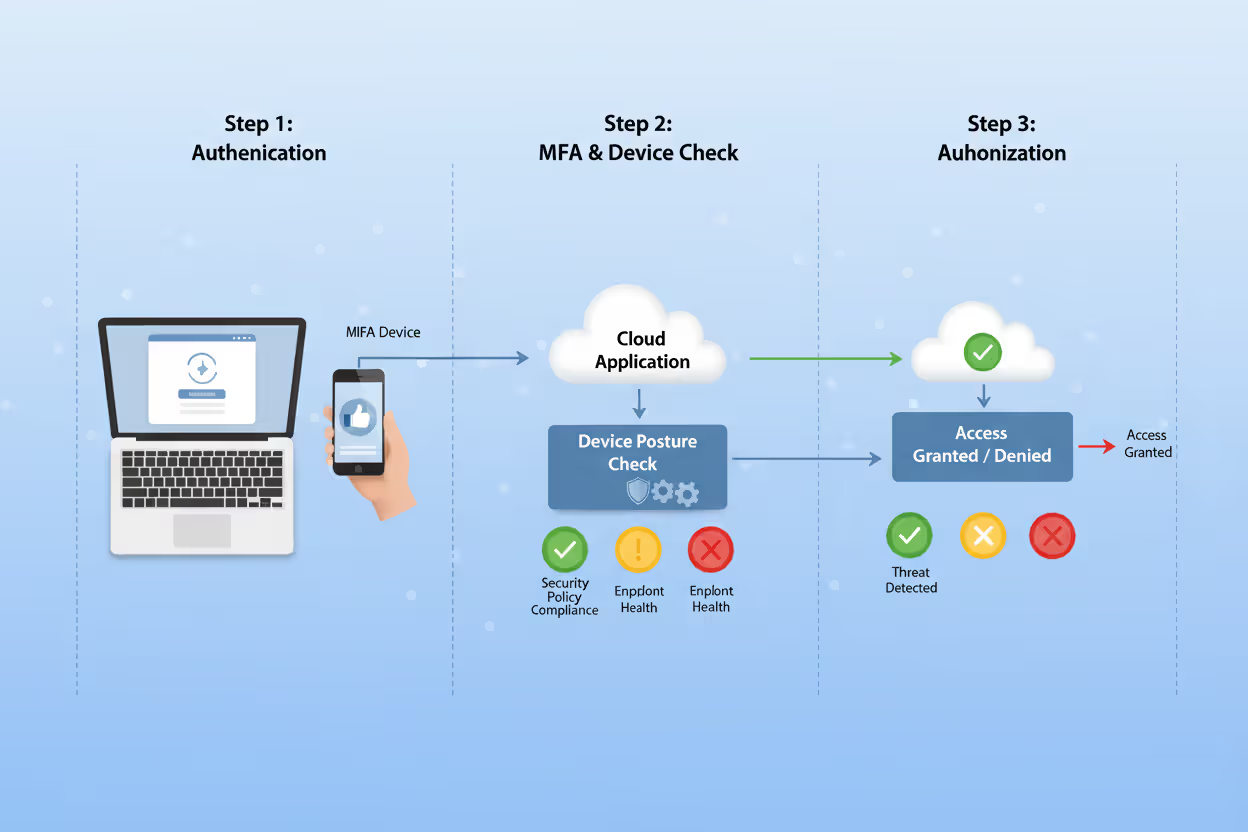
Zero trust endpoint security explained requires understanding three core mechanisms that work together: continuous identity verification, device health assessment, and least-privilege access controls. Each layer adds defense depth without relying on network location as a security proxy.
If you know the enemy and know yourself, you need not fear the result of a hundred battles
— Sun Tzu
Continuous Identity Verification
Authentication doesn't stop after the initial login. The system continuously validates identity through behavioral analysis, contextual signals, and multi-factor challenges triggered by risk indicators.
A typical scenario: An employee logs in from Chicago at 8 AM using her company laptop. The system verifies her password and authenticates a push notification to her phone. Two hours later, a login attempt appears from Singapore using the same credentials. Rather than simply blocking access, the zero trust system evaluates risk factors—impossible travel time, new device fingerprint, unusual access patterns—and escalates authentication requirements. It might demand additional verification, restrict access to non-sensitive resources, or alert security teams while allowing limited functionality.
Continuous verification also monitors behavior after authentication. If a marketing coordinator who typically accesses design files suddenly attempts to download customer payment data, the system flags the anomaly. Access might continue under heightened scrutiny, require additional authentication, or trigger automatic restrictions depending on risk thresholds.
Device Health Checks and Posture Assessment
Zero trust systems constantly evaluate endpoint security posture before granting access. A device must meet minimum security requirements—current OS patches, active endpoint protection, encrypted storage, compliant configuration—to access corporate resources.
Posture assessment happens in real time. A laptop that meets all requirements Monday morning might fail checks by Tuesday afternoon if the user disabled antivirus software or skipped a critical security update. The system detects the compliance failure and automatically restricts access until the device returns to acceptable security standards.
Health checks extend beyond basic security software. The system evaluates whether the device shows signs of compromise: unexpected processes, suspicious network connections, unauthorized configuration changes, or malware indicators. A developer's workstation might pass all compliance checks yet trigger restrictions because behavioral analysis detected unusual database queries or abnormal data transfer volumes.
Device trust isn't binary. Rather than simply allowing or blocking access, zero trust frameworks assign risk scores that determine access levels. A fully compliant, corporate-managed device might access all authorized resources. The same user's personal tablet—lacking full endpoint protection—might access email but not customer databases. A device showing potential compromise indicators might retain read-only access to non-sensitive documents while security teams investigate.

Author: Marcus Halbrook;
Source: williamalmonte.net
Least-Privilege Access Controls
Zero trust grants the minimum access required to complete specific tasks, then revokes it. This approach limits blast radius when credentials are compromised or devices become infected.
Traditional networks often grant broad access based on job titles or departments. Everyone in accounting can access all financial systems; all engineers can reach development servers. Zero trust replaces these broad permissions with granular, context-aware access decisions.
Consider an HR coordinator processing new hire paperwork. She needs temporary access to payroll systems to enter salary information, but only during onboarding tasks. Zero trust systems grant access to specific payroll functions required for data entry, restrict access to reports or historical records, and automatically revoke permissions when the task completes. If her account is compromised, attackers gain only narrow access to limited functions rather than carte blanche across all HR systems.
Access decisions incorporate context beyond user identity and device health. Time of day, geographic location, data sensitivity, and current security posture all influence access grants. A CFO might access financial planning systems freely from headquarters during business hours but face additional authentication requirements when accessing the same data from an airport at midnight.
Key Components of a Zero Trust Endpoint Strategy
Implementing zero trust endpoint security requires orchestrating multiple security technologies into a cohesive framework. Four components form the foundation: identity and access management, endpoint detection and response, network segmentation, and encryption.
Identity and access management (IAM) serves as the control plane, making access decisions based on user identity, device posture, and contextual signals. Modern IAM platforms integrate with endpoint agents to evaluate device health before granting access. They enforce multi-factor authentication, manage privileged access, and maintain detailed access logs for compliance and forensic analysis.
Endpoint detection and response (EDR) tools provide continuous monitoring and threat detection on devices. EDR agents report device health status to IAM systems, detect suspicious behavior that might indicate compromise, and enable rapid response when threats are identified. Integration between EDR and access control systems allows automatic restriction of potentially compromised devices before attackers can move laterally.
Network segmentation limits lateral movement even if attackers breach endpoint defenses. Micro-segmentation creates isolated zones around sensitive resources, requiring explicit authentication and authorization for each connection. A compromised laptop might access the specific cloud application the user needs, but segmentation prevents attackers from pivoting to unrelated systems or scanning the network for additional targets.
Encryption protects data both in transit and at rest on endpoints. Full-disk encryption prevents data exposure if devices are lost or stolen. Transport encryption ensures data remains protected as it moves between endpoints and corporate resources. Encryption keys integrate with identity systems, becoming inaccessible when devices fall out of compliance or show compromise indicators.
These components work together rather than operating independently. When EDR detects suspicious behavior, it notifies IAM systems to increase authentication requirements. When a device fails health checks, network segmentation prevents access to sensitive resources. When encryption keys are revoked, data on compromised devices becomes inaccessible even if attackers maintain device control.

Author: Marcus Halbrook;
Source: williamalmonte.net
Zero Trust Endpoint Security in Practice
Zero trust endpoint security examples vary by industry, but common patterns emerge across healthcare, finance, and remote workforce implementations.
Healthcare organizations face unique challenges: medical devices with limited security capabilities, strict HIPAA compliance requirements, and clinicians who need immediate access to patient data during emergencies. A regional hospital system implemented zero trust by segmenting medical devices into isolated network zones, requiring continuous authentication for access to electronic health records, and deploying endpoint protection on all administrative workstations and mobile devices.
The implementation allowed doctors to access patient records from personal smartphones using containerized applications that enforced encryption and prevented data copying. Medical devices—infusion pumps, imaging equipment, patient monitors—operated in isolated segments with strictly controlled access to other network resources. When a ransomware attack compromised a billing department workstation, segmentation prevented lateral movement to systems containing patient data.

Author: Marcus Halbrook;
Source: williamalmonte.net
Financial services firms deal with sophisticated attackers targeting high-value data and stringent regulatory requirements. A wealth management firm serving high-net-worth clients deployed zero trust to protect customer financial data accessed by advisors working remotely and traveling frequently.
The firm implemented risk-based authentication that evaluated device health, location, and behavioral patterns before granting access to client portfolios. Advisors using corporate-managed laptops from home offices experienced seamless access. The same advisors accessing data from hotel business centers faced additional authentication steps and restrictions on downloading client information. Device health checks prevented access from laptops missing security updates, while behavioral monitoring flagged unusual access patterns—an advisor suddenly accessing hundreds of client accounts—for immediate security review.
Remote workforce deployments accelerated dramatically after 2020, forcing organizations to secure employees working from home offices, coffee shops, and coworking spaces. A software company with a fully distributed workforce implemented zero trust to replace its aging VPN infrastructure.
Rather than tunneling all traffic through centralized VPN concentrators, the company deployed identity-aware proxy services that authenticated users and devices before granting access to specific applications. Developers accessed code repositories and development environments through secure channels that verified device health and enforced least-privilege access. Customer support staff accessed helpdesk systems and customer databases with appropriate restrictions based on role and device security posture. When a support representative's laptop showed signs of malware infection, the system automatically restricted access while allowing continued work on non-sensitive tasks.
Common Deployment Mistakes and How to Avoid Them
Organizations implementing zero trust endpoint security frequently stumble over predictable obstacles. Recognizing these patterns helps avoid expensive delays and security gaps.
Rushing implementation creates security holes and user frustration. A manufacturing company attempted to deploy zero trust across all endpoints in 30 days, believing speed would minimize disruption. Instead, incomplete device inventories left industrial control systems unprotected, inadequate testing broke critical applications, and frustrated employees found workarounds that bypassed security controls entirely.
Better approach: Phase deployment across manageable groups. Start with non-critical systems to identify issues, then expand to broader populations. A three-to-six-month rollout for mid-sized organizations allows time for testing, user training, and adjustment based on real-world feedback.
Ignoring user experience drives employees toward shadow IT and security workarounds. An insurance company deployed endpoint security that required multi-factor authentication for every application access, generated frequent prompts to verify device health, and blocked access when laptops needed routine updates. Claims adjusters began using personal devices and consumer file-sharing services to avoid security friction.
Better approach: Design security that adapts to risk rather than applying maximum restrictions universally. Implement single sign-on to reduce authentication friction, schedule device health checks during off-hours when possible, and provide clear guidance when access is restricted. Security that interferes with legitimate work gets bypassed; security that operates transparently gets adopted.

Author: Marcus Halbrook;
Source: williamalmonte.net
Incomplete asset inventory leaves gaps in coverage. A retail chain deployed zero trust across corporate laptops and smartphones but overlooked point-of-sale systems, inventory scanners, and warehouse management devices. Attackers compromised an unprotected inventory scanner and used it as a foothold to access payment systems.
Better approach: Discover all devices before deploying controls. Include IoT devices, operational technology, contractor equipment, and legacy systems in your inventory. Accept that some devices can't support full endpoint agents and plan alternative controls—network segmentation, isolated VLANs, or replacement with more secure alternatives.
Lack of visibility prevents effective security decisions. A consulting firm deployed endpoint agents but failed to centralize logging or establish monitoring processes. When a client reported suspicious emails originating from the firm, security teams lacked data to identify compromised devices or assess breach scope.
Better approach: Establish centralized visibility before deploying controls. Implement security information and event management (SIEM) systems or extended detection and response (XDR) platforms that correlate endpoint data with network and application logs. Define clear escalation procedures when devices show compromise indicators.
Comparing Zero Trust to Traditional Endpoint Security
Understanding the fundamental differences between zero trust and traditional approaches clarifies why organizations are making the transition.
| Security Model | Trust Assumption | Access Method | Threat Response | Best For |
| Traditional Perimeter | Devices inside the network are trusted | Broad access after initial authentication | Reactive; detect and remediate breaches | Static environments with clear network boundaries |
| Zero Trust Endpoint | No device is trusted by default | Least-privilege access verified continuously | Proactive; prevent unauthorized access before it occurs | Distributed workforces, cloud applications, BYOD |
Traditional perimeter security assumes the network edge separates trusted internal resources from untrusted external threats. Once a device authenticates and joins the internal network, it enjoys broad access to resources. This model worked when employees worked from offices and applications ran in corporate data centers.
Zero trust endpoint security explained in contrast assumes breach is inevitable and trust must be continuously earned. Every access request requires verification regardless of network location. A device on the corporate LAN receives the same scrutiny as one connecting from a hotel. Access grants are specific, time-limited, and revoked when no longer needed.
Traditional models respond to threats reactively. Security teams deploy antivirus software, monitor for known attack signatures, and investigate alerts after suspicious activity occurs. The goal is detecting breaches quickly and minimizing damage.
Zero trust takes a proactive stance. Rather than assuming devices are secure until proven compromised, it requires proof of security before granting access. Continuous verification catches security posture degradation before attackers exploit it. Least-privilege access limits blast radius even when prevention fails.
Neither model is universally superior. Traditional perimeter security works well for isolated networks with minimal external connectivity—industrial control systems, air-gapped research environments, or legacy infrastructure that can't support modern endpoint agents. Zero trust excels in distributed environments where users, devices, and applications span multiple locations and cloud platforms.
Getting Started with Zero Trust Endpoint Security
Transitioning to zero trust endpoint security requires methodical planning rather than wholesale replacement of existing infrastructure. A phased approach minimizes disruption while building toward comprehensive coverage.
Assessment steps establish your current security posture and identify gaps:
Start with a complete asset inventory. Document every device accessing corporate resources: employee laptops, smartphones, tablets, contractor equipment, IoT devices, and operational technology. Include device ownership (corporate vs. personal), operating systems, installed security software, and current access privileges.
Map data flows and access patterns. Identify sensitive data repositories, document which users and applications need access, and understand how data moves between systems. This mapping reveals where to prioritize security controls and identifies overly broad access that needs restriction.
Evaluate existing security tools for zero trust compatibility. Many organizations already have components of a zero trust architecture—multi-factor authentication, endpoint protection, SIEM platforms—that can be integrated rather than replaced. Identify gaps where new tools are required and redundancies where consolidation makes sense.
Phased rollout approach builds momentum while managing risk:
Phase one focuses on visibility and identity. Deploy endpoint agents to collect device health data, implement centralized logging to establish baseline behavior, and strengthen identity controls with multi-factor authentication. This phase establishes the foundation without disrupting existing access patterns.
Phase two introduces access restrictions for new applications or high-risk resources. Rather than changing access to existing systems, apply zero trust principles to new cloud application deployments, recently identified sensitive data repositories, or user groups with elevated risk profiles. This approach demonstrates value without overwhelming security teams or users.
Phase three expands zero trust controls to broader populations and additional resources. Use lessons learned from earlier phases to refine policies, improve user experience, and address technical challenges. Continue expanding coverage until all devices and resources operate under zero trust principles.
Vendor selection considerations significantly impact implementation success:
Prioritize integration capabilities over point solutions. Zero trust requires orchestration across identity management, endpoint protection, network security, and application access controls. Vendors whose products integrate smoothly reduce complexity and improve security effectiveness. Evaluate whether vendors support open standards and APIs that enable integration with your existing infrastructure.
Assess vendor commitment to the zero trust model. Some vendors rebrand existing products as "zero trust" without fundamental architectural changes. Look for vendors who support continuous verification, least-privilege access, and granular policy enforcement rather than simply adding multi-factor authentication to legacy products.
Consider operational requirements beyond initial deployment. Zero trust generates substantial security telemetry that requires analysis, policy enforcement that needs ongoing tuning, and user support for access issues. Evaluate whether vendors provide adequate management tools, documentation, and support to operate the solution effectively.
Test with pilot groups before broad deployment. Select a pilot population that represents diverse use cases—remote workers, office-based employees, contractors, executive users—and deploy zero trust controls in a limited scope. Use pilot results to refine policies, identify training needs, and build internal expertise before expanding deployment.
Frequently Asked Questions
Zero trust endpoint security represents a fundamental shift from perimeter-based defenses to continuous verification and least-privilege access. The model aligns security with modern work patterns—distributed workforces, cloud applications, contractor access, and personal devices—that render traditional network boundaries obsolete.
Implementation requires orchestrating identity management, endpoint protection, network segmentation, and encryption into a cohesive framework. Success depends on phased rollouts that build visibility before enforcing restrictions, user experience design that minimizes friction for legitimate access, and comprehensive asset inventory that leaves no security gaps.
Organizations that rush deployment, ignore user needs, or attempt wholesale replacement of existing infrastructure typically struggle. Those that take a methodical approach—assessing current posture, piloting with limited groups, refining based on feedback, and expanding systematically—build robust security that adapts to evolving threats without disrupting business operations.
The transition from perimeter security to zero trust isn't optional for organizations serious about protecting sensitive data in distributed environments. The question isn't whether to adopt zero trust principles, but how quickly you can implement them before attackers exploit the gaps in traditional defenses.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.