
Cybersecurity analyst monitoring vulnerability management dashboards in a security operations center
What Is Vulnerability Management in Cyber Security?
Picture this: right now, your network probably has dozens of security holes you don't know about. Maybe it's an outdated Java runtime on a marketing server. Could be a misconfigured S3 bucket. Perhaps someone in accounting still uses "Summer2023!" as their admin password.
Here's the uncomfortable truth—attackers scan for these weaknesses 24/7. They don't need sophisticated zero-days. Most breaches exploit vulnerabilities that've had patches available for months, sometimes years.
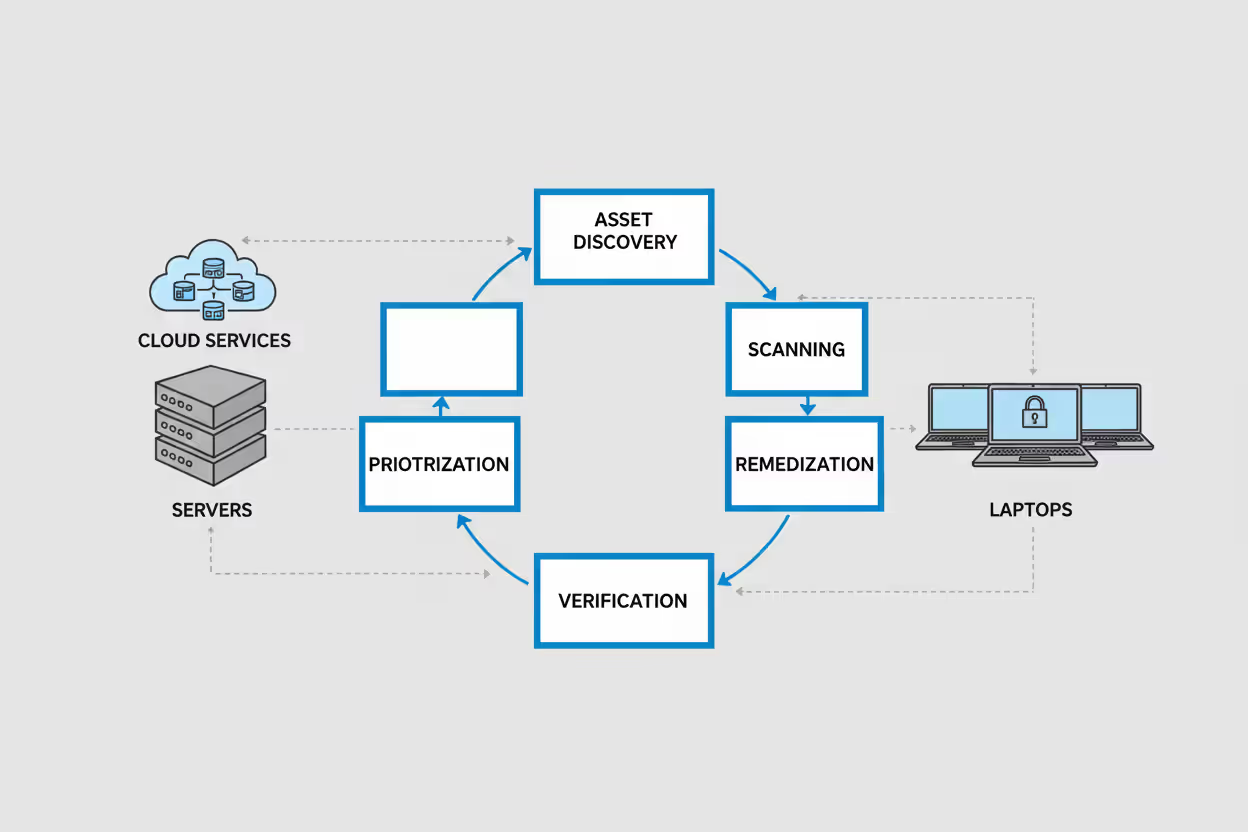
Vulnerability management is how organizations stop playing defense and start getting ahead of attackers. It's a repeating cycle: discover what's vulnerable, figure out what matters most, fix it, then verify the fix actually worked. Miss any step and you're just checking boxes while your attack surface stays wide open.
Vulnerability Management Definition and Core Purpose
So what exactly does vulnerability management in cyber security mean? Think of it as your organization's immune system for digital threats. You're constantly scanning your environment for weaknesses, deciding which ones could actually hurt you, fixing them in order of urgency, and checking back to make sure they stay fixed.
The vulnerability management in cyber security definition goes deeper than just running scanners and applying patches. You're building a program that touches every corner of your IT environment—from that forgotten WordPress install in marketing to your production Kubernetes clusters to the third-party vendor who processes payroll.
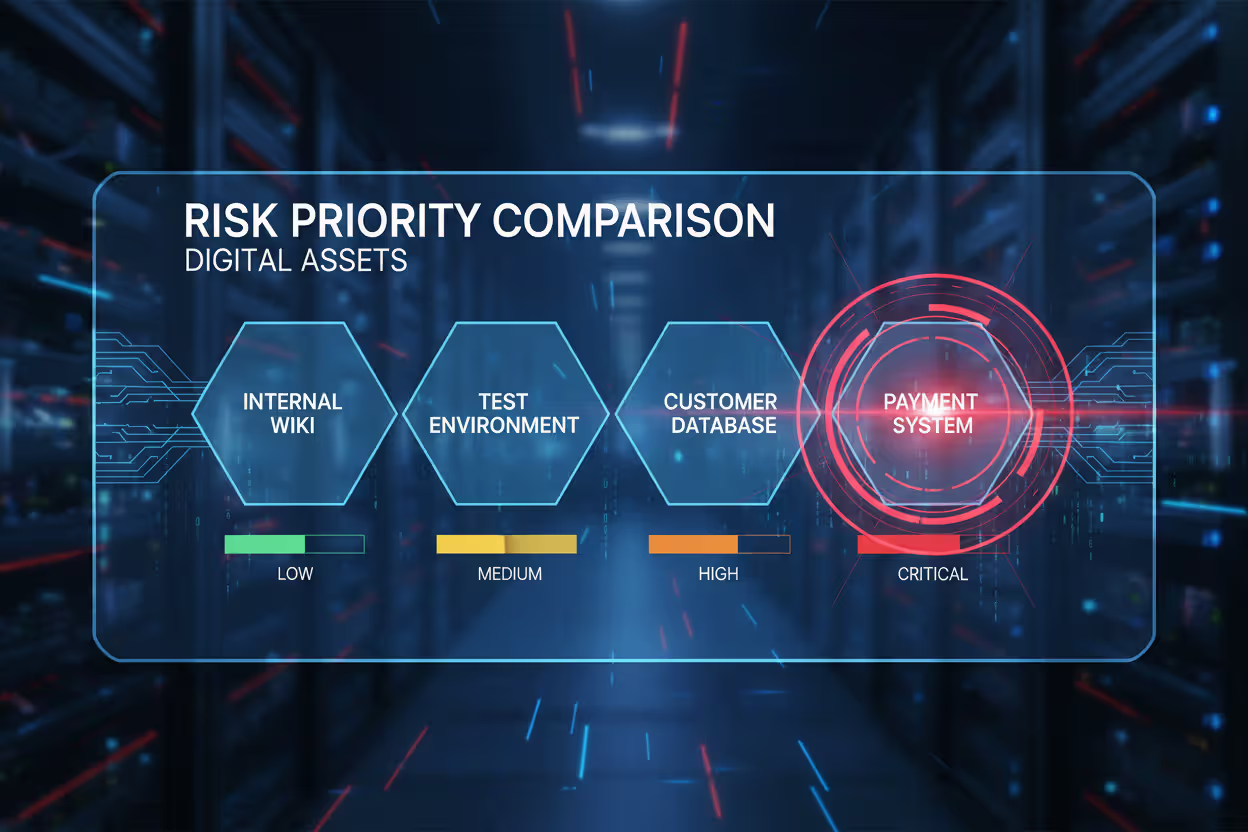
When people ask about vulnerability management in cyber security meaning, they're usually wondering why it matters versus just patching stuff when vendors release updates. Here's why: context. A critical SQL injection flaw in your customer-facing checkout system? Drop everything and fix it. That same vulnerability in an isolated dev sandbox with no real data? Sure, patch it eventually, but maybe not at 2 AM on a Saturday.
Author: Ethan Caldwel;
Source: williamalmonte.net
This differs from related security practices in important ways:
- Patch management just deploys vendor updates. Vulnerability management includes patching but also covers fixing misconfigurations, implementing workarounds when patches don't exist, and sometimes accepting risk when fixes would break critical systems.
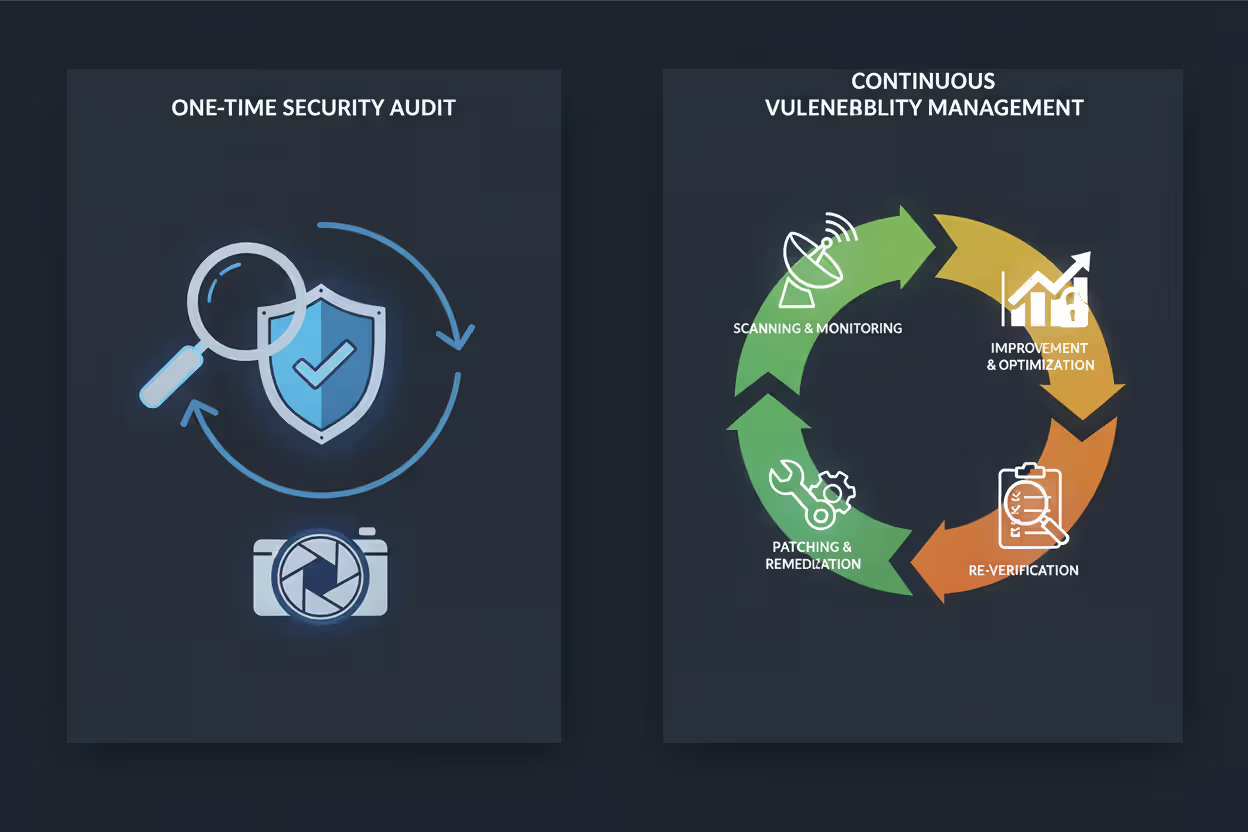
- Penetration testing happens periodically—someone pretends to be an attacker for a week or two. Vulnerability management runs continuously, finding problems whether anyone's actively exploiting them or not.
- Vulnerability assessment gives you a snapshot. "Here's what's broken today." Vulnerability management tracks everything from discovery through remediation to verification, often across months.
Organizations without proper vulnerability management typically discover their security gaps the hard way—when ransomware encrypts their file servers or when they're reading about their own data breach in the news.
How the Vulnerability Management Process Works
Let me walk you through vulnerability management in cyber security explained as an actual workflow. This isn't theory—it's what security teams do every single day.
Asset Discovery and Vulnerability Scanning
You can't protect what you don't know exists. Sounds obvious, but shadow IT is everywhere. That marketing intern who spun up a Heroku instance for a campaign? The engineering team testing a new cloud database? These forgotten assets become attractive targets because nobody's watching them.
Modern asset discovery tools continuously map your network. They find servers, laptops, containers, IoT gadgets, cloud resources—everything with an IP address or API endpoint. Agents installed on critical systems provide authenticated views (logged-in scans that see everything). Unauthenticated scans show what an external attacker would find.
Scan frequency isn't one-size-fits-all. Your internet-facing web servers? Scan them daily, maybe continuously. Internal file servers might run weekly. That air-gapped SCADA system controlling factory equipment? Monthly, because changes happen slowly and uptime matters more than perfect security.

Author: Ethan Caldwel;
Source: williamalmonte.net
Risk Assessment and Prioritization
Here's where inexperienced teams drown. A typical enterprise scan returns 10,000+ findings. Treat them equally and you'll spend six months fixing informational issues while ignoring actual dangers.
Smart prioritization layers multiple factors:
- CVSS scores give you technical severity (0-10 scale), but a 9.8 vulnerability in a completely isolated test environment might matter less than a 6.5 flaw in your payment gateway.
- Exploit availability changes everything. Theoretical vulnerability versus actively exploited in ransomware campaigns? Totally different urgency.
- Asset criticality matters enormously. Compromising your customer database versus some internal documentation wiki—not remotely comparable risk.
- Existing protections might already mitigate the risk. Strong network segmentation, web application firewalls, or behavioral detection can buy you time.
Some organizations use frameworks like SSVC. Others build custom matrices: critical vulnerabilities patched within 24 hours, high-severity within a week, medium within 30 days. What matters is having a system everyone understands and actually follows.
Remediation and Mitigation Steps
Fixing vulnerabilities isn't always straightforward. Ideal scenario: vendor releases a patch, you test it, deploy it, done. Reality gets messier.
Legacy applications might not have patches. Vendors go out of business. Upgrades break integrations with other critical systems. When you can't patch immediately, you improvise:
- Virtual patching blocks exploitation attempts at the network perimeter using WAFs or IPS rules—doesn't fix the underlying flaw but prevents attackers from reaching it.
- Configuration changes disable unnecessary services, enforce authentication, restrict access to trusted IPs only.
- Network segmentation walls off vulnerable systems so even if attackers compromise them, they can't pivot laterally.
- Decommissioning removes assets that can't be secured economically—sometimes the right answer is "stop using this."
Remediation work flows to whoever owns the asset. Infrastructure team handles server patches. DevOps manages container vulnerabilities. Application developers fix code flaws. Centralized tracking prevents things from slipping through cracks between teams.

Author: Ethan Caldwel;
Source: williamalmonte.net
Verification and Continuous Monitoring
Trust but verify. Just because you deployed a patch doesn't guarantee it worked. Maybe the installation failed silently. Configuration management tools reverted your changes. The patch conflicts with something else.
Verification scans run after remediation, confirming vulnerabilities actually closed. This completes the feedback loop.
Continuous monitoring catches new problems. Software updates introduce fresh vulnerabilities. Infrastructure changes expose new attack surface. Vendors disclose zero-days that affect your entire estate. Automated workflows detect these instantly and kick off new remediation cycles.
Dashboards track program health: mean time to fix critical issues, percentage of high-severity vulnerabilities past their SLA deadline, vulnerability trends by business unit. These metrics let executives see whether security posture is improving or degrading quarter over quarter.
Common Vulnerability Types Organizations Face
Let me give you some vulnerability management in cyber security examples showing what you're actually hunting for.
Software vulnerabilities come from coding mistakes. Buffer overflows let attackers execute arbitrary code. SQL injection flaws expose databases. Cross-site scripting enables session hijacking. Remember Log4Shell in late 2021? That remote code execution bug in a ubiquitous Java logging library forced a global emergency patching frenzy. Attackers started scanning for vulnerable systems within hours of public disclosure. Organizations that didn't patch in the first week got compromised.
Misconfigurations cause more breaches than sophisticated exploits. Someone enables public read access on a cloud storage bucket "temporarily" and forgets to revert it. Default credentials stay unchanged on network appliances. Firewall rules allow access from any IP instead of specific trusted networks. In 2024, a healthcare provider exposed 3.2 million patient records because a junior admin set an S3 bucket to public while troubleshooting an access issue.
Outdated systems accumulate risk over time. Windows Server 2008 hit end-of-life years ago—no more security patches—yet you'll still find it running in factories, hospitals, and government offices. Upgrading risks breaking critical applications or industrial control systems. Each unpatched vulnerability becomes permanent exposure.
Zero-day vulnerabilities exist but remain unknown to vendors and defenders. No patch available because nobody knew the flaw existed. Nation-state attackers and sophisticated cybercrime groups stockpile zero-days for high-value targets. Vulnerability management can't prevent zero-days, but good programs limit damage through defense-in-depth: segmentation reduces lateral movement, least-privilege access constrains what compromised accounts can reach, behavioral detection spots anomalous exploitation.
Third-party component risks hide in dependencies. Your web application might directly use 15 libraries, but those libraries depend on 50 others, which depend on 200 more. A vulnerability anywhere in that dependency tree compromises your application. Software composition analysis tools track these nested dependencies and flag known CVEs.
Vulnerability Management vs. Vulnerability Assessment
People constantly confuse these terms. They're related but fundamentally different:
| Aspect | Vulnerability Management | Vulnerability Assessment |
| Definition | Continuous program spanning discovery, risk evaluation, remediation, and verification across all organizational assets | Point-in-time scan identifying vulnerabilities present at a specific moment |
| Frequency | Ongoing or regularly scheduled (daily/weekly/monthly depending on asset criticality) | Periodic intervals (quarterly/annually) or event-driven |
| Scope | Enterprise-wide with persistent tracking, ownership assignment, and accountability | Targeted scan of particular systems, applications, or network segments |
| Output | Living remediation queue with SLAs, owner assignments, trend analysis, and executive dashboards | Static report listing discovered vulnerabilities with severity scores and descriptions |
| Purpose | Systematically reduce organizational risk through sustained vulnerability elimination | Provide security posture snapshot for audits, compliance documentation, or project gates |
Think of assessments as inputs feeding your management program. You run a quarterly compliance assessment—that's a snapshot. The program that tracks those findings, assigns them to system owners, enforces remediation deadlines, verifies fixes, and rescans—that's management.
Real-World Vulnerability Management Examples
Let me show you vulnerability management in cyber security examples from actual implementations.
Scenario 1: Retail Chain Patch Coordination
National retailer with 8,000 point-of-sale terminals across 500 stores. Microsoft releases Patch Tuesday updates on the second Tuesday each month. Here's their workflow:
By Wednesday morning, their vulnerability management platform has scanned the entire environment identifying which systems need which patches. Critical vulnerabilities affecting internet-facing payment systems get emergency change approval—patches deploy by Friday. Medium-severity issues in back-office systems wait for the next scheduled maintenance window (typically Sunday nights). Low-severity findings batch into quarterly updates.
Patch deployment happens overnight when stores close. Automated systems push updates to terminals, servers reboot during off-hours. Verification scans run Wednesday morning. Any system still showing vulnerabilities triggers investigation—maybe it was offline during the patch window, or a configuration conflict prevented installation. Those exceptions get manual attention.
Author: Ethan Caldwel;
Source: williamalmonte.net
Scenario 2: SaaS Company Container Security
Startup running microservices architecture spins up hundreds of containers daily. Traditional monthly scanning would miss ephemeral workloads that exist for hours then disappear.
They integrated vulnerability scanning into their CI/CD pipeline. Every container image gets scanned before deployment. Images with high or critical CVEs fail the build—they literally cannot reach production. Developers see vulnerability reports alongside their code review feedback.
Runtime scanning monitors live containers for configuration drift and emerging threats. When a new CVE affecting their base OS image gets published, automated scans identify every affected container within minutes. DevOps rebuilds images with patched base layers and redeploys, often completing the cycle in under two hours.
Scenario 3: Financial Services Vendor Risk
Bank partners with a payroll processor who needs network access to employee systems. Before granting access, the vendor must complete security questionnaires and submit to external vulnerability scanning of systems handling bank data.
Initial scan reveals outdated TLS implementations (still using TLS 1.0), an Apache web server three versions behind, and exposed administrative interfaces. Bank's vendor risk team blocks access until remediation. Vendor fixes issues, rescanning confirms closure. Post-onboarding, quarterly scans verify the vendor maintains adequate security. This extends the bank's vulnerability management beyond its own perimeter, addressing supply chain risk.
Tools and Technologies Used in Vulnerability Management
This vulnerability management in cyber security guide wouldn't be complete without covering the tools that make it practical.
Network scanners probe IP ranges for open ports, running services, and known vulnerabilities. They're agentless—just point them at your network—which makes them great for discovering rogue devices but limits depth of inspection.
Agent-based scanners install lightweight software on endpoints, providing authenticated views of patch levels, installed applications, and configuration details. Agents phone home continuously, enabling near-real-time detection of new vulnerabilities without waiting for scheduled scans.
Web application scanners crawl sites and APIs testing for injection vulnerabilities, authentication flaws, and configuration weaknesses. They simulate attack techniques (fuzzing inputs, testing boundary conditions) without actually exploiting vulnerabilities destructively.
Author: Ethan Caldwel;
Source: williamalmonte.net
Container and cloud-native scanners inspect Docker images, Kubernetes manifests, and cloud infrastructure-as-code. They integrate with registries and orchestration platforms, blocking vulnerable deployments before they reach production.
Software composition analysis tools parse application code and dependency manifests, mapping every third-party library and flagging known CVEs. Developers get alerts when libraries they're using appear in vulnerability databases.
SIEM and SOAR platforms connect vulnerability data with security operations. When a high-priority vulnerability appears on an asset that's also triggering behavioral alerts, analysts investigate potential active exploitation. Automated playbooks can isolate affected systems or trigger emergency patching workflows.
Manual penetration testing complements automation. Skilled testers discover logic flaws, business process vulnerabilities, and complex attack chains that scanners miss. Annual or biannual manual assessments validate automated findings and uncover blind spots.
Common Mistakes That Weaken Vulnerability Programs
This vulnerability management in cyber security guide section covers pitfalls I see organizations hit repeatedly.
Letting low-severity findings accumulate indefinitely creates massive technical debt. Sure, individually they're low risk. But attackers chain multiple "low" vulnerabilities together. Privilege escalation often combines three or four minor flaws into system compromise. Set maximum ages even for low-severity items—maybe six months—before someone must address them.
Operating without prioritization frameworks leads to paralysis. Teams stare at 5,000 findings and have no idea where to start. Document your methodology: CVSS score + exploit availability + asset criticality = priority tier. Publish SLAs so everyone knows critical means 24 hours, not "whenever we get around to it."
Siloed teams create organizational dysfunction. Security identifies vulnerabilities but can't patch systems. IT operations controls infrastructure but doesn't understand risk context. Application teams prioritize features and view security as obstructionist. Successful programs embed security people inside ops and dev teams, fostering collaboration instead of antagonism.
Infrequent scanning creates exposure windows. Monthly scans mean vulnerabilities disclosed mid-cycle sit undetected for weeks. Critical internet-facing assets need daily or continuous scanning. Balance frequency against network impact and system load.
Treating vulnerability management as pure compliance theater defeats the purpose. Scanning once before your annual audit then ignoring results for 11 months leaves you exposed most of the year. Compliance should be a side effect of good security hygiene, not the primary driver.
Ignoring asset inventory accuracy guarantees blind spots. Scanners can't find vulnerabilities on systems they don't know exist. Regularly reconcile asset databases against network discovery to catch shadow IT and orphaned systems.
Organizations remediating critical vulnerabilities within 72 hours experienced 68% fewer successful intrusions compared to those taking over two weeks. Speed matters, but what enables speed is process maturity—automated discovery, clear prioritization criteria, cross-functional collaboration, and executive support for disrupting business-as-usual when critical risks emerge
— Vulnerability Management Maturity Study
Frequently Asked Questions About Vulnerability Management
Vulnerability management transforms security from reactive chaos into disciplined practice. Instead of discovering your weaknesses when attackers exploit them, you find problems first, fix what matters most, and verify your fixes actually worked.
Effective programs demand collaboration across organizational boundaries. Security teams discover and contextualize risks. Infrastructure and development teams implement fixes. Executives provide resources and enforce accountability. When these groups align around shared metrics and clear SLAs, vulnerability management amplifies your entire security program's effectiveness.
Nobody achieves zero vulnerabilities. Developers ship new code daily. Vendors disclose flaws weekly. Infrastructure evolves constantly, introducing fresh attack surface. The goal isn't perfection—it's shrinking exposure windows. Find critical issues in hours instead of months. Patch in days instead of quarters. Maintain visibility across every asset, from on-premises servers to multi-cloud deployments to third-party SaaS integrations.
Organizations just starting should begin with accurate asset inventory and baseline scanning. Establish simple prioritization: patch anything with public exploits immediately, then work down by severity and asset criticality. Automate repetitive tasks but preserve human judgment about business context and acceptable risk.
Mature programs never reach "done." They adapt continuously as threats evolve, new asset types emerge, and the business landscape shifts. Vulnerability management isn't a project you complete and move on from—it's perpetual security hygiene that keeps your infrastructure resilient against adversaries who never stop probing for weaknesses to exploit.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.




