
Cybersecurity analyst dashboard with CVE vulnerability records on multiple monitors
What Does CVE Stand for in Cyber Security?
Content
Content
CVE stands for Common Vulnerabilities and Exposures. It's a standardized naming system for publicly known cybersecurity vulnerabilities and exposures in software and hardware. The CVE program provides a universal identifier for each security flaw, making it easier for security professionals, vendors, and organizations worldwide to share information about threats and coordinate their responses.
Think of CVE as a universal catalog number for security weaknesses. Just as ISBN numbers uniquely identify books, CVE IDs uniquely identify vulnerabilities. When a security researcher discovers a flaw in software—whether it's a buffer overflow in a popular web server or an authentication bypass in enterprise software—that vulnerability receives a CVE identifier, creating a common reference point for everyone discussing or addressing the issue.
CVE Definition and Core Meaning
The CVE in cyber security meaning extends beyond just an acronym. It represents a dictionary-style list of publicly disclosed cybersecurity vulnerabilities. Each entry includes an identification number, a description of the vulnerability, and references to related advisories and reports. The system doesn't include technical details about how to exploit vulnerabilities or provide patches—those come from other sources.
The cve in cyber security definition encompasses three key components. First, "Common" indicates the system provides a standardized reference that everyone uses. Second, "Vulnerabilities" refers to weaknesses in software or hardware that could be exploited to compromise security. Third, "Exposures" covers configuration issues or other conditions that, while not direct security holes, still create risk.
MITRE Corporation, a nonprofit organization working in the public interest, maintains the CVE system. Funded by the U.S. Department of Homeland Security's Cybersecurity and Infrastructure Security Agency (CISA), the program launched in 1999 to solve a critical problem: different security tools and databases used different names for the same vulnerabilities, creating confusion and communication breakdowns.
Author: Vanessa Keaton;
Source: williamalmonte.net
A CVE entry doesn't assess severity or provide patches. It simply establishes that a particular vulnerability exists, describes it briefly, and provides references to more detailed information. Organizations like the National Vulnerability Database (NVD) then build upon CVE entries by adding severity scores, affected product configurations, and remediation guidance.
How the CVE System Works
The CVE system operates through a distributed network of CVE Numbering Authorities (CNAs) that reserve and assign CVE IDs. This decentralized approach allows vulnerabilities to be documented quickly by the organizations closest to the affected products.
When a researcher discovers a vulnerability, they typically report it to the software vendor or a coordination center. The CNA for that product area reserves a CVE ID, which the researcher can reference when they publish their findings. The vendor then has time to develop a patch before public disclosure. Once the vulnerability becomes public, the full CVE entry gets published with a description and references.
Understanding CVE ID Format
CVE IDs follow a specific structure: CVE-YEAR-NUMBER. For example, CVE-2025-12345 indicates a vulnerability assigned in 2025 with the sequence number 12345. The year reflects when the CVE ID was assigned, not necessarily when the vulnerability was discovered or disclosed.
The numbering sequence used to increment by ones, but the program now reserves blocks of numbers to different CNAs. You might see gaps in the sequence because some reserved numbers never get used—perhaps a reported issue turned out not to be a vulnerability, or duplicate reports got consolidated.
Starting in 2014, CVE IDs expanded from four digits to at least four digits, allowing for CVE-2025-999999 or higher. This change accommodated the growing volume of vulnerability disclosures, which has increased substantially. In 2025 alone, over 30,000 CVEs were assigned, compared to fewer than 7,000 in 2015.
Who Assigns CVE Numbers
CVE Numbering Authorities are organizations authorized to assign CVE IDs within their specific scopes. As of 2026, more than 300 CNAs operate globally, including major software vendors, security research organizations, and national cybersecurity agencies.
Primary CNAs cover specific products or technologies. For instance, Microsoft acts as a CNA for its own products, while Red Hat covers its Linux distributions. Root CNAs oversee specific regions or industries and can authorize new CNAs within their scope.
The CNA structure creates efficiency. When a vulnerability affects Apache web server, the Apache Software Foundation—as a CNA—can immediately assign a CVE ID without waiting for MITRE to process the request. This distributed model has dramatically reduced the time between vulnerability discovery and CVE assignment, often to within hours.

Author: Vanessa Keaton;
Source: williamalmonte.net
Why CVEs Matter for Cybersecurity
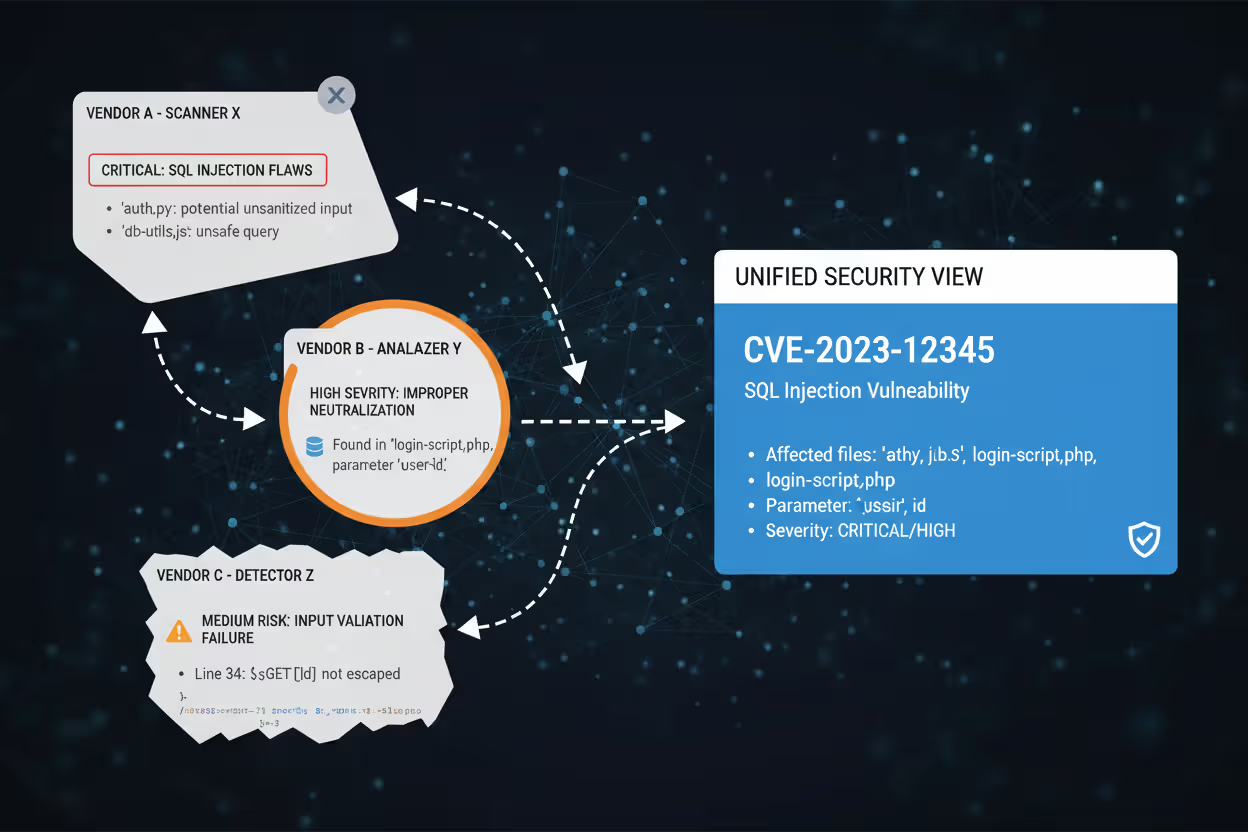
CVEs create a common language for discussing vulnerabilities across organizational boundaries. When a security advisory references CVE-2025-8472, everyone knows exactly which vulnerability is being discussed, regardless of whether they use Tenable, Qualys, Rapid7, or any other security tool.
This standardization transforms vulnerability management from chaos into a coordinated process. Security teams can track which vulnerabilities their scanners detect, verify that patches address specific CVEs, and communicate clearly with vendors and peers about their security posture.
For patch management, CVEs provide the foundation for prioritization. When Microsoft releases a monthly security update addressing fifteen vulnerabilities, each has a CVE ID. Security teams can look up each CVE in the NVD, check the CVSS severity score, determine which systems are affected, and decide which patches to deploy first.
Risk assessment relies heavily on CVE data. Vulnerability scanners report findings by CVE ID, allowing teams to correlate scan results with threat intelligence. If a new ransomware campaign exploits CVE-2025-9876, and your scanners show that vulnerability present on twenty servers, you know exactly where to focus remediation efforts.
Compliance frameworks increasingly reference CVEs. PCI DSS requires organizations to protect against known vulnerabilities, and auditors verify compliance by checking whether systems have been patched for applicable CVEs. Cyber insurance applications often ask about vulnerability management processes and how quickly critical CVEs get remediated.
The alternative to CVEs would be vendor-specific vulnerability identifiers that don't translate across products or tools. Imagine trying to determine whether "Microsoft Security Advisory 2025-001" is the same issue as "RHEL Bug #98765" and whether your Cisco firewall is vulnerable to the same flaw. CVEs eliminate this confusion.

Author: Vanessa Keaton;
Source: williamalmonte.net
Real-World CVE Examples and What They Tell Us
CVE-2021-44228 (Log4Shell): This vulnerability in the Apache Log4j logging library became one of the most critical security issues in recent history. The flaw allowed remote code execution through specially crafted log messages, affecting countless Java applications worldwide. With a CVSS score of 10.0, it represented maximum severity. Organizations spent months hunting down every instance of Log4j in their environments, including in third-party software where the library was embedded. The Log4Shell incident demonstrated how a vulnerability in a widely-used component can create cascading risk across the entire technology ecosystem.
CVE-2023-23397 (Microsoft Outlook Elevation of Privilege): This critical vulnerability in Microsoft Outlook allowed attackers to steal NTLM hashes simply by sending a specially crafted email. The victim didn't need to open the email or click anything—just receiving it in Outlook triggered the vulnerability. With a CVSS score of 9.8, this CVE illustrated how seemingly innocuous features (in this case, calendar reminders pointing to network shares) can create serious security risks. Microsoft's patch addressed the issue, but organizations needed to actively update Outlook clients across their entire user base.
CVE-2025-3094 (Hypothetical IoT Camera Authentication Bypass): A fictional but representative example of vulnerabilities affecting Internet of Things devices. This type of CVE typically describes a flaw where default credentials or missing authentication allows unauthorized access to device management interfaces. The CVSS score might be 7.5, reflecting high impact but requiring network access. These CVEs highlight the security challenges in IoT deployments, where devices often lack automatic update mechanisms and remain vulnerable long after patches become available.
CVE-2024-21410 (Microsoft Exchange Server Privilege Escalation): This vulnerability in Exchange Server allowed authenticated attackers to elevate privileges and potentially compromise email servers. With organizations heavily dependent on Exchange for email infrastructure, this CVE received immediate attention despite requiring the attacker to already have some level of access. The example shows how not all critical CVEs involve remote unauthenticated exploitation—privilege escalation and lateral movement vulnerabilities also pose significant risks.
Each of these examples demonstrates different aspects of the threat landscape: widely-used libraries with massive blast radius, client-side applications that users interact with daily, IoT devices with limited security controls, and enterprise infrastructure that attackers specifically target.

Author: Vanessa Keaton;
Source: williamalmonte.net
How to Look Up and Research CVEs
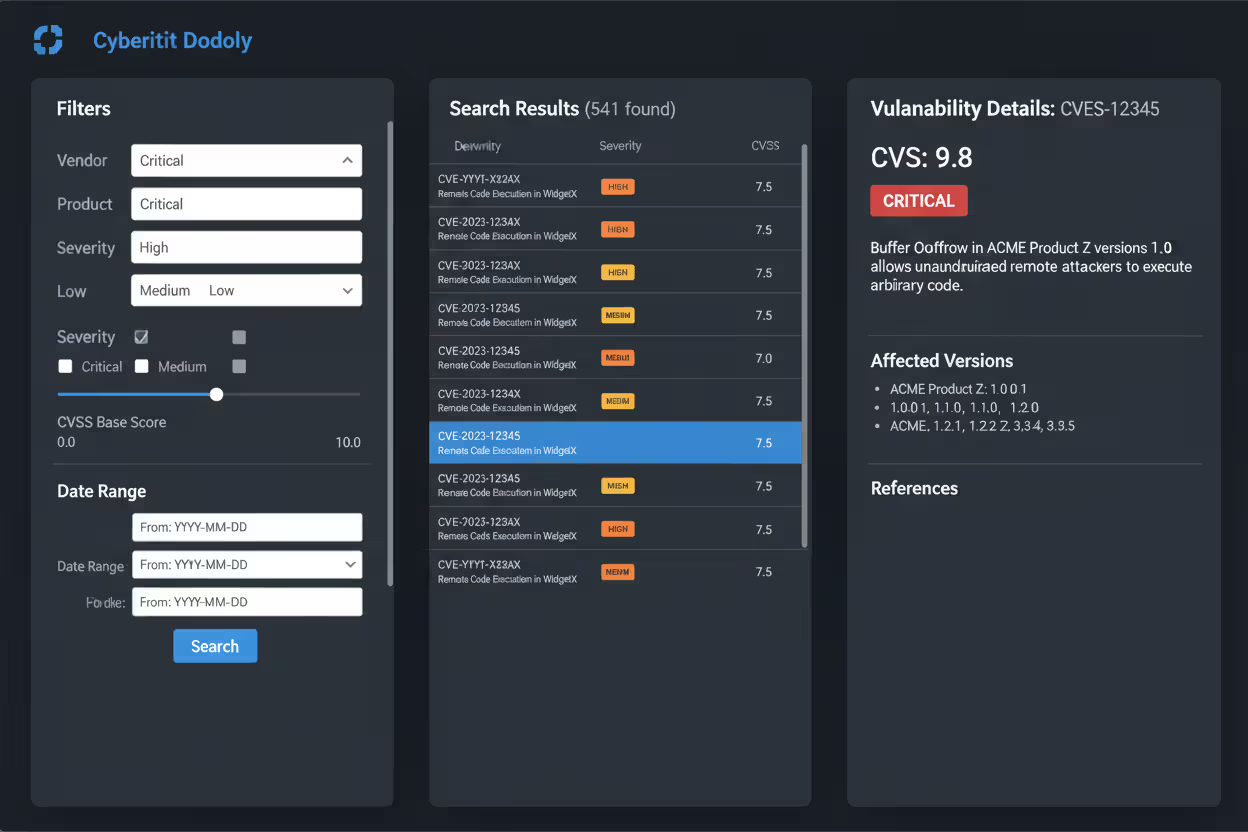
The National Vulnerability Database at nvd.nist.gov serves as the primary resource for researching CVEs. Maintained by NIST, the NVD enhances basic CVE entries with severity scores, impact analysis, and affected product configurations. When you search for a CVE ID, the NVD provides comprehensive information including CVSS scores, weakness types, affected software versions, and references to vendor advisories.
The official CVE website at cve.org offers the authoritative CVE list. While less detailed than the NVD, it provides the canonical CVE descriptions and confirms whether a particular CVE ID has been assigned. The site also offers tools for CNAs and information about the CVE program structure.
Understanding CVSS (Common Vulnerability Scoring System) scores helps interpret CVE severity. CVSS provides a numerical score from 0.0 to 10.0 based on factors like attack complexity, privileges required, and potential impact. The score breaks down into three metric groups: Base (intrinsic vulnerability characteristics), Temporal (time-dependent factors like exploit availability), and Environmental (organization-specific factors).
Author: Vanessa Keaton;
Source: williamalmonte.net
When researching a CVE, check multiple sources. The NVD provides official NIST analysis, but vendor security advisories often include additional context specific to their products. Security research blogs and threat intelligence feeds may document active exploitation or proof-of-concept code availability. Cross-referencing these sources builds a complete picture of the risk.
For ongoing monitoring, RSS feeds and email alerts from the NVD allow teams to stay informed about new CVEs relevant to their environment. Many vulnerability management platforms automatically correlate new CVE publications with asset inventories, alerting teams when a new CVE affects their infrastructure.
The NVD's search capabilities let you filter by product, vendor, severity, or date range. Searching for "vendor:microsoft product:windows_server" returns all CVEs affecting Windows Server. Adding severity filters focuses results on critical and high-severity issues requiring immediate attention.
Common Misconceptions About CVEs
The CVE Program's mission is to identify, define, and catalog publicly disclosed cybersecurity vulnerabilities. There is one CVE Record for each vulnerability in the catalog. The vulnerabilities are discovered then assigned and published by organizations from around the world that have partnered with the CVE Program. Partners publish CVE Records to communicate consistent descriptions of vulnerabilities. Information technology and cybersecurity professionals use CVE Records to ensure they are discussing the same issue, and to coordinate their efforts to prioritize and address the vulnerabilities
— CVE Program Mission Statement
A CVE means the vulnerability is actively exploited. Many people assume that if something has a CVE, attackers are already using it. In reality, CVE assignment simply means the vulnerability is publicly known. Some CVEs never see active exploitation, while others get exploited heavily. The CVE system doesn't track exploitation status, though threat intelligence sources often provide that information separately.
All CVEs are critical and require immediate patching. CVE severity varies dramatically. Some represent theoretical weaknesses with minimal real-world risk, while others enable complete system compromise. Organizations must assess each CVE's severity, applicability to their environment, and available compensating controls before deciding on remediation timelines.
Getting a CVE assigned means the vendor has released a patch. CVE assignment and patch availability are independent processes. Sometimes CVEs are published before patches exist, particularly when researchers disclose vulnerabilities after vendors fail to respond. Other times, vendors release patches without requesting CVEs until later. The CVE entry itself doesn't indicate patch availability—you need to check vendor advisories.
CVE and CVSS are the same thing. CVE is the identifier; CVSS is the severity scoring system. A CVE might have multiple CVSS scores from different analyzing organizations. MITRE assigns CVEs but doesn't score them—that's done by the NVD and other vulnerability databases.
Only software vulnerabilities get CVEs. Hardware vulnerabilities also receive CVE identifiers. Processor flaws like Spectre and Meltdown had CVEs. Firmware vulnerabilities in network equipment, BMCs, and UEFI implementations all receive CVEs. The key criterion is that the vulnerability is publicly disclosed, not what type of product is affected.
A product without recent CVEs must be secure. Absence of CVEs doesn't prove security. The product might not receive sufficient security research attention, or vulnerabilities might exist but haven't been discovered or disclosed yet. Conversely, products with many CVEs might simply be popular targets that receive extensive security scrutiny.
CVE Severity Levels and Response Priority
| Severity Level | CVSS Score Range | Typical Characteristics | Response Priority |
| Critical | 9.0 – 10.0 | Remote code execution without authentication; complete system compromise; wormable vulnerabilities | Immediate action required; patch within 24-48 hours; consider emergency change procedures |
| High | 7.0 – 8.9 | Remote code execution requiring user interaction; privilege escalation to admin; significant data exposure | Patch within 7 days; prioritize internet-facing systems; implement compensating controls if patching delayed |
| Medium | 4.0 – 6.9 | Information disclosure; denial of service; privilege escalation requiring existing access | Patch within 30 days; include in regular maintenance windows; assess risk based on asset criticality |
| Low | 0.1 – 3.9 | Minor information leaks; limited denial of service; requires significant preconditions to exploit | Patch during next regular update cycle; acceptable to defer if compensating controls exist |
This table provides general guidance, but organizations should adjust response timelines based on their specific risk tolerance, asset criticality, and whether active exploitation is occurring. A medium-severity CVE being actively exploited in the wild warrants faster response than a critical CVE affecting a non-critical system with no public exploits.
Frequently Asked Questions About CVEs
Understanding what CVE stands for in cyber security provides the foundation for effective vulnerability management. The Common Vulnerabilities and Exposures system transforms vulnerability tracking from a fragmented mess of vendor-specific identifiers into a coordinated global effort to document and address security weaknesses.
Security professionals should incorporate CVE identifiers into their daily workflows. When evaluating security advisories, prioritize understanding the specific CVEs involved and their severity scores. Configure vulnerability scanners to report findings by CVE ID, enabling clear communication with vendors and colleagues. Build processes that track CVE remediation timelines and ensure critical vulnerabilities receive appropriate attention.
Organizations benefit from establishing CVE-based metrics for their security programs. Tracking mean time to remediate CVEs by severity level provides measurable indicators of vulnerability management effectiveness. Monitoring which CVEs affect your environment and how quickly patches get deployed helps identify process gaps and resource constraints.
The CVE system continues evolving to meet changing needs. The expansion of CNA networks accelerates CVE assignment, while ongoing improvements to CVE entry quality enhance their usefulness. Integration between CVE data and threat intelligence platforms provides richer context about exploitation activity and remediation urgency.
For anyone working in cybersecurity, vulnerability management, IT operations, or risk management, CVEs represent essential vocabulary. They enable precise communication about security issues, facilitate coordinated responses to emerging threats, and provide the foundation for measuring and improving security posture. Mastering CVE concepts and resources transforms vulnerability management from reactive chaos into proactive risk reduction.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes only. It is intended to explain concepts related to endpoint security, cybersecurity practices, threat prevention, and security technologies.
All information on this website, including articles, guides, and examples, is presented for general educational purposes. Cybersecurity requirements and implementations may vary depending on organizational needs, infrastructure, regulatory requirements, and threat environments.
This website does not provide professional cybersecurity, legal, or compliance advice, and the information presented should not be used as a substitute for consultation with qualified cybersecurity professionals.
The website and its authors are not responsible for any errors or omissions, or for any outcomes resulting from decisions made based on the information provided on this website.




